All posts tagged "Encryption"
-

 3.3KMalware
3.3KMalwareNew ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility
Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two years after the botnet’s infrastructure was dismantled...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSystemBC Malware’s C2 Server Analysis Exposes Payload Delivery Tricks
Cybersecurity researchers have shed light on the command-and-control (C2) server workings of a known malware family called SystemBC. “SystemBC can be purchased...
-

 1.6KData Breach
1.6KData BreachU.S., U.K., Australia Sanction Russian REvil Hacker Behind Medibank Breach
Governments from Australia, the U.K., and the U.S. have imposed financial sanctions on a Russian national for his alleged role in the...
-
 1.8KVulnerabilities
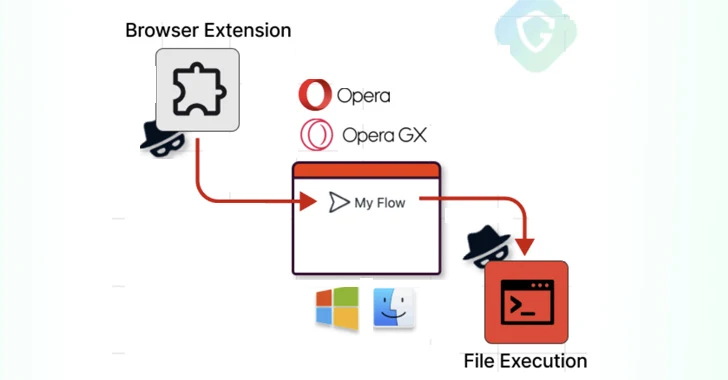
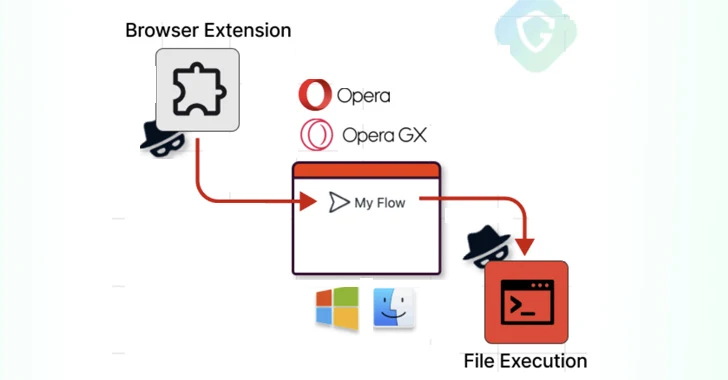
1.8KVulnerabilitiesOpera MyFlaw Bug Could Let Hackers Run ANY File on Your Mac or Windows
Cybersecurity researchers have disclosed a now-patched security flaw in the Opera web browser for Microsoft Windows and Apple macOS that could be...
-
 4.1KMalware
4.1KMalwareAtomic Stealer Gets an Upgrade – Targeting Mac Users with Encrypted Payload
Cybersecurity researchers have identified an updated version of a macOS information stealer called Atomic (or AMOS), indicating that the threat actors behind...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesNew Terrapin Flaw Could Let Attackers Downgrade SSH Protocol Security
Security researchers from Ruhr University Bochum have discovered a vulnerability in the Secure Shell (SSH) cryptographic network protocol that could allow an...
-

 1.1KData Breach
1.1KData BreachRemote Encryption Attacks Surge: How One Vulnerable Device Can Spell Disaster
Ransomware groups are increasingly switching to remote encryption in their attacks, marking a new escalation in tactics adopted by financially motivated actors...
-

 4.0KCyber Attack
4.0KCyber AttackMajor Cyber Attack Paralyzes Kyivstar – Ukraine’s Largest Telecom Operator
Ukraine’s biggest telecom operator Kyivstar has become the victim of a “powerful hacker attack,” disrupting customer access to mobile and internet services....
-

 3.0KVulnerabilities
3.0KVulnerabilitiesLockBit Ransomware Exploiting Critical Citrix Bleed Vulnerability to Break In
Multiple threat actors, including LockBit ransomware affiliates, are actively exploiting a recently disclosed critical security flaw in Citrix NetScaler application delivery control...
-

 2.0KCyber Attack
2.0KCyber AttackMustang Panda Hackers Targets Philippines Government Amid South China Sea Tensions
The China-linked Mustang Panda actor has been linked to a cyber attack targeting a Philippines government entity amid rising tensions between the...
-

 2.9KMalware
2.9KMalware8Base Group Deploying New Phobos Ransomware Variant via SmokeLoader
The threat actors behind the 8Base ransomware are leveraging a variant of the Phobos ransomware to conduct their financially motivated attacks. The...
-

 2.8KData Breach
2.8KData BreachHelloKitty Ransomware Group Exploiting Apache ActiveMQ Vulnerability
Cybersecurity researchers are warning of suspected exploitation of a recently disclosed critical security flaw in the Apache ActiveMQ open-source message broker service...
-

 2.1KMalware
2.1KMalwareTurla Updates Kazuar Backdoor with Advanced Anti-Analysis to Evade Detection
The Russia-linked hacking crew known as Turla has been observed using an updated version of a known second-stage backdoor referred to as...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesAct Now: VMware Releases Patch for Critical vCenter Server RCE Vulnerability
VMware has released security updates to address a critical flaw in the vCenter Server that could result in remote code execution on...
-
 750Malware
750MalwareRorschach Ransomware Emerges: Experts Warn of Advanced Evasion Strategies
Cybersecurity researchers have taken the wraps off a previously undocumented ransomware strain called Rorschach that’s both sophisticated and fast. “What makes Rorschach...
-

 3.4KMalware
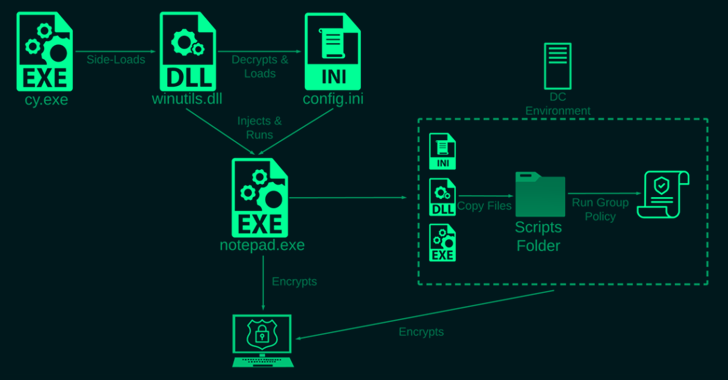
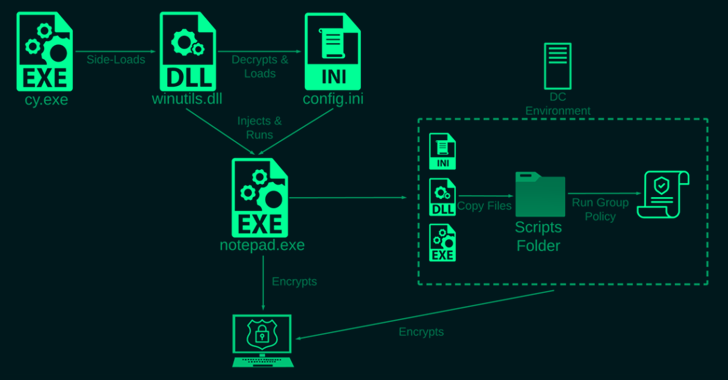
3.4KMalwareLockBit 3.0 Ransomware: Inside the Cyberthreat That’s Costing Millions
U.S. government agencies have released a joint cybersecurity advisory detailing the indicators of compromise (IoCs) and tactics, techniques, and procedures (TTPs) associated...
-

 4.0KMalware
4.0KMalwareU.S. Cybersecurity Agency Raises Alarm Over Royal Ransomware’s Deadly Capabilities
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released a new advisory about Royal ransomware, which emerged in the threat landscape...
-

 1.6KMalware
1.6KMalwareHive Ransomware Infrastructure Seized in Joint International Law Enforcement Effort
In what’s a case of hacking the hackers, the darknet infrastructure associated with the Hive ransomware-as-a-service (RaaS) operation has been seized as...
-
 1.7KMalware
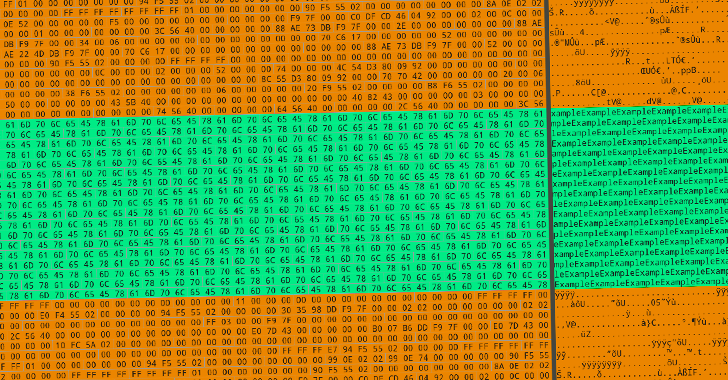
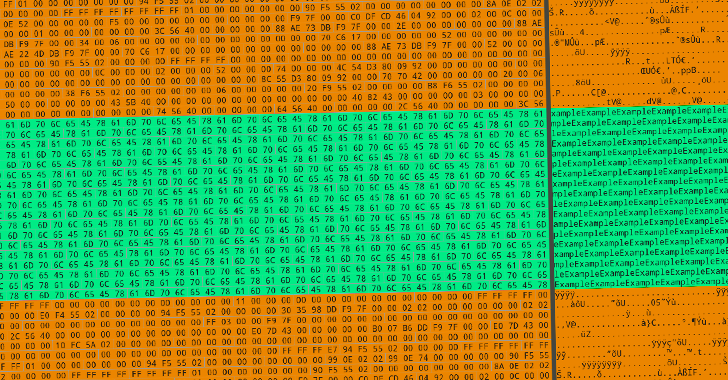
1.7KMalwareCybersecurity Experts Uncover Inner Workings of Destructive Azov Ransomware
Cybersecurity researchers have published the inner workings of a new wiper called Azov Ransomware that’s deliberately designed to corrupt data and “inflict...
-
 1.3KVulnerabilities
1.3KVulnerabilitiesResearchers Say Microsoft Office 365 Uses Broken Email Encryption to Secure Messages
New research has disclosed what’s being called a security vulnerability in Microsoft 365 that could be exploited to infer message contents due...
-
 2.6KMalware
2.6KMalwareNew XLoader Botnet Version Using Probability Theory to Hide its C&C Servers
An enhanced version of the XLoader malware has been spotted adopting a probability-based approach to camouflage its command-and-control (C&C) infrastructure, according to...






