All posts tagged "endpoint security"
-

 2.8KMalware
2.8KMalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
The threat actor tracked as TA558 has been observed leveraging steganography as an obfuscation technique to deliver a wide range of malware...
-

 2.6KMalware
2.6KMalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
A threat actor tracked as TA547 has targeted dozens of German organizations with an information stealer called Rhadamanthys as part of an...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesMicrosoft Fixes 149 Flaws in Huge April Patch Release, Zero-Days Included
Microsoft has released security updates for the month of April 2024 to remediate a record 149 flaws, two of which have come...
-
 3.1KMalware
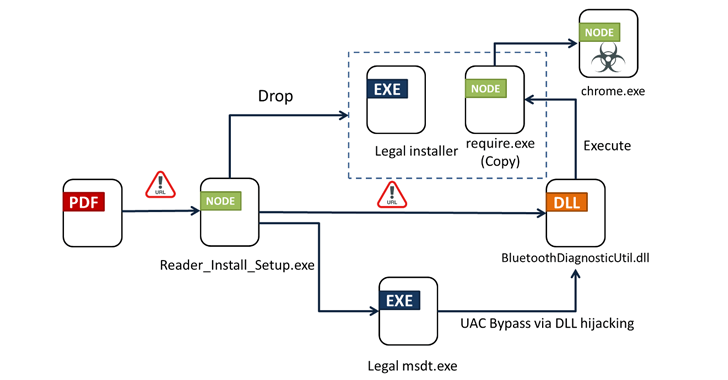
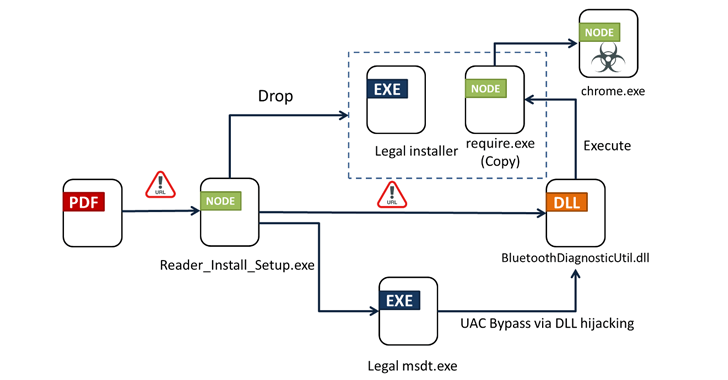
3.1KMalwareFrom PDFs to Payload: Bogus Adobe Acrobat Reader Installers Distribute Byakugan Malware
Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the...
-

 4.9KMalware
4.9KMalwareDetecting Windows-based Malware Through Better Visibility
Despite a plethora of available security solutions, more and more organizations fall victim to Ransomware and other threats. These continued threats aren’t...
-
 345Vulnerabilities
345VulnerabilitiesMagnet Goblin Hacker Group Leveraging 1-Day Exploits to Deploy Nerbian RAT
A financially motivated threat actor called Magnet Goblin is swiftly adopting one-day security vulnerabilities into its arsenal in order to opportunistically breach...
-
 654Cyber Attack
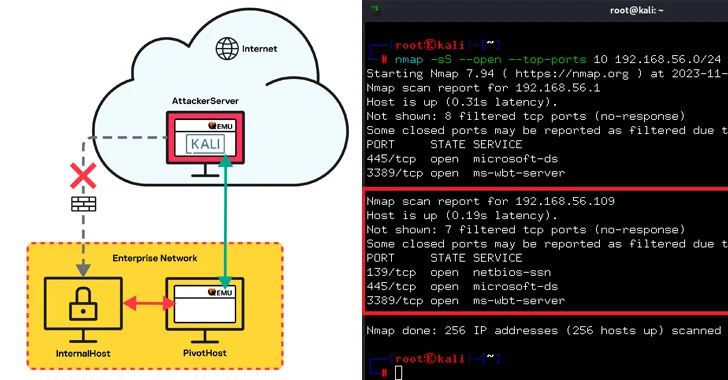
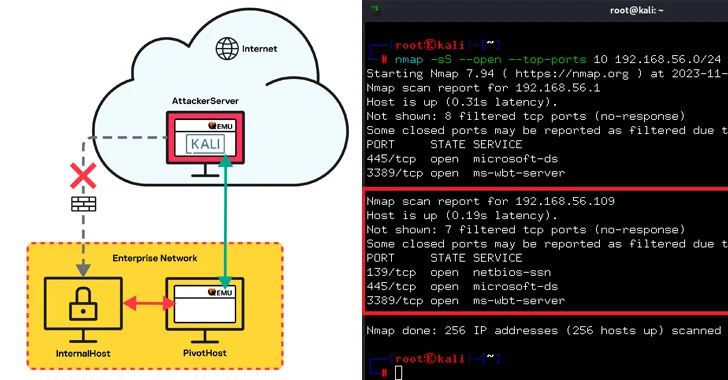
654Cyber AttackQEMU Emulator Exploited as Tunneling Tool to Breach Company Network
Threat actors have been observed leveraging the QEMU open-source hardware emulator as tunneling software during a cyber attack targeting an unnamed “large...
-
 3.8KMalware
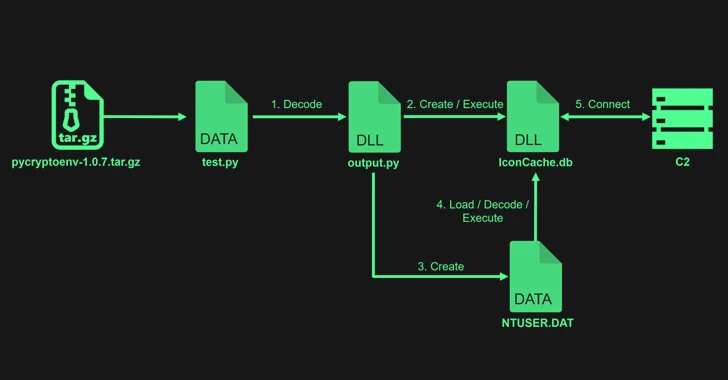
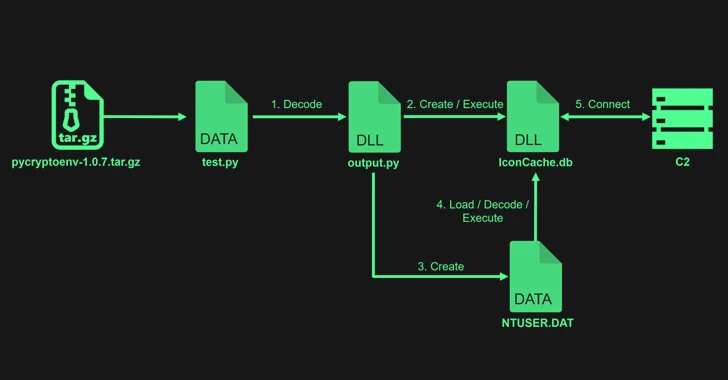
3.8KMalwareLazarus Exploits Typos to Sneak PyPI Malware into Dev Systems
The notorious North Korean state-backed hacking group Lazarus uploaded four packages to the Python Package Index (PyPI) repository with the goal of...
-

 709Data Breach
709Data BreachCybersecurity for Healthcare—Diagnosing the Threat Landscape and Prescribing Solutions for Recovery
On Thanksgiving Day 2023, while many Americans were celebrating, hospitals across the U.S. were doing quite the opposite. Systems were failing. Ambulances...
-

 1.4KMalware
1.4KMalwareIvanti Pulse Secure Found Using 11-Year-Old Linux Version and Outdated Libraries
A reverse engineering of the firmware running on Ivanti Pulse Secure appliances has revealed numerous weaknesses, once again underscoring the challenge of...
-

 3.6KVulnerabilities
3.6KVulnerabilitiesFortinet Warns of Critical FortiOS SSL VPN Flaw Likely Under Active Exploitation
Fortinet has disclosed a new critical security flaw in FortiOS SSL VPN that it said is likely being exploited in the wild....
-
 1.8KMalware
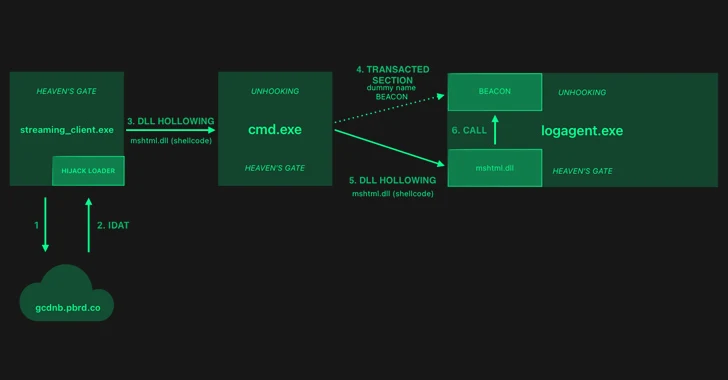
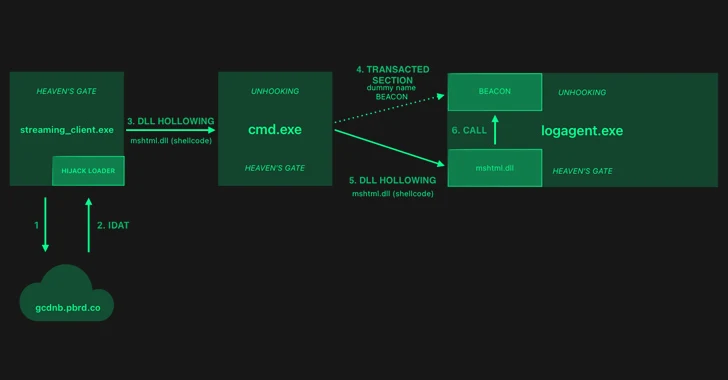
1.8KMalwareHijackLoader Evolves: Researchers Decode the Latest Evasion Methods
The threat actors behind a loader malware called HijackLoader have added new techniques for defense evasion, as the malware continues to be...
-
 300Vulnerabilities
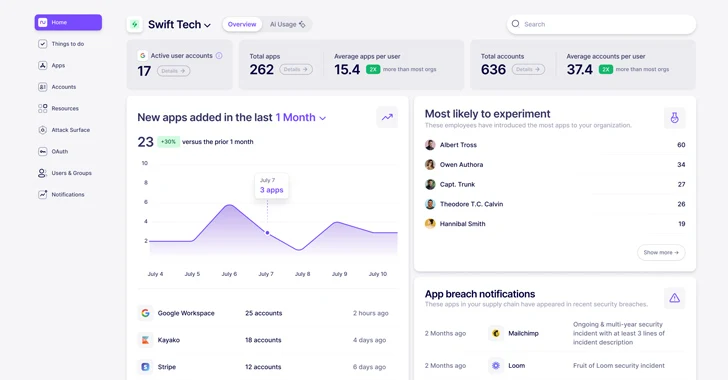
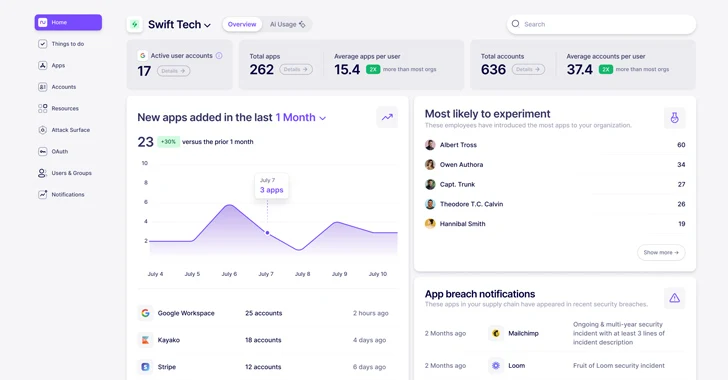
300VulnerabilitiesWhat is Nudge Security and How Does it Work?
In today’s highly distributed workplace, every employee has the ability to act as their own CIO, adopting new cloud and SaaS technologies...
-
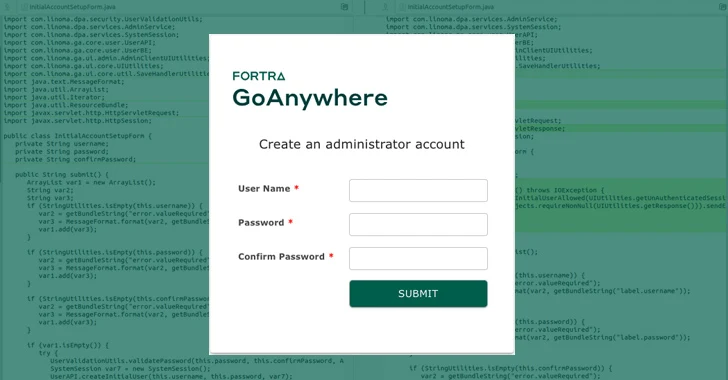
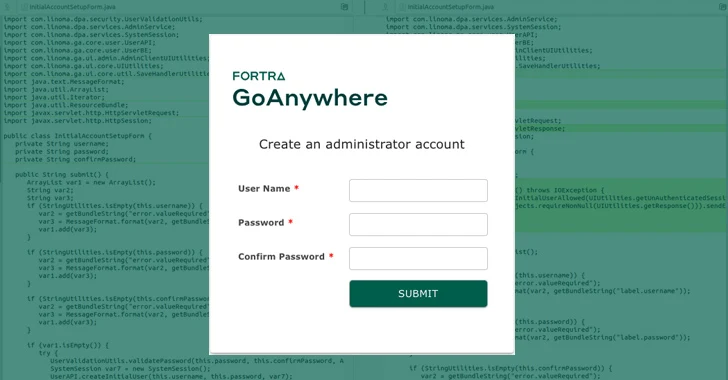 4.1KVulnerabilities
4.1KVulnerabilitiesPatch Your GoAnywhere MFT Immediately – Critical Flaw Lets Anyone Be Admin
A critical security flaw has been disclosed in Fortra’s GoAnywhere Managed File Transfer (MFT) software that could be abused to create a...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesSpectralBlur: New macOS Backdoor Threat from North Korean Hackers
Cybersecurity researchers have discovered a new Apple macOS backdoor called SpectralBlur that overlaps with a known malware family that has been attributed...
-
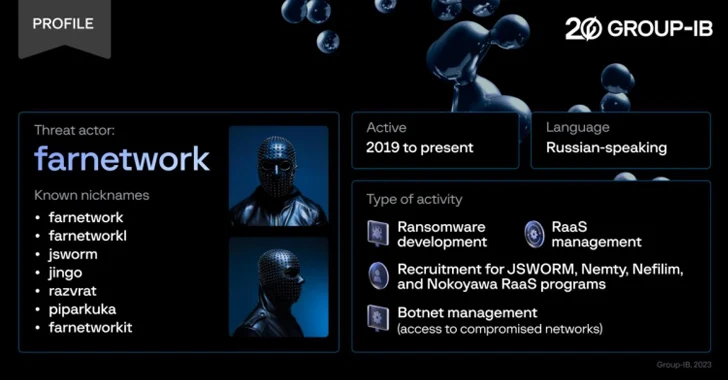
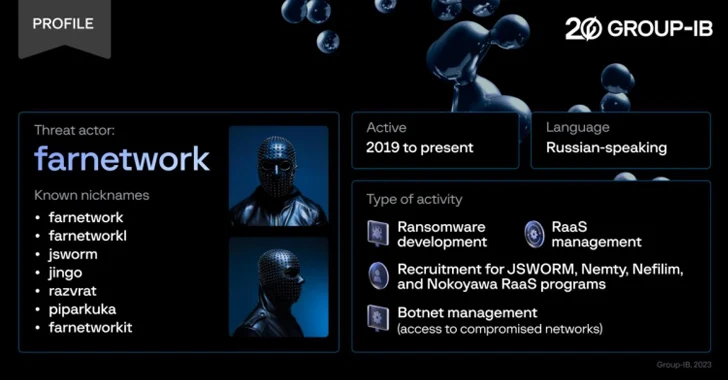 4.9KMalware
4.9KMalwareExperts Expose Farnetwork’s Ransomware-as-a-Service Business Model
Cybersecurity researchers have unmasked a prolific threat actor known as farnetwork, who has been linked to five different ransomware-as-a-service (RaaS) programs over...
-
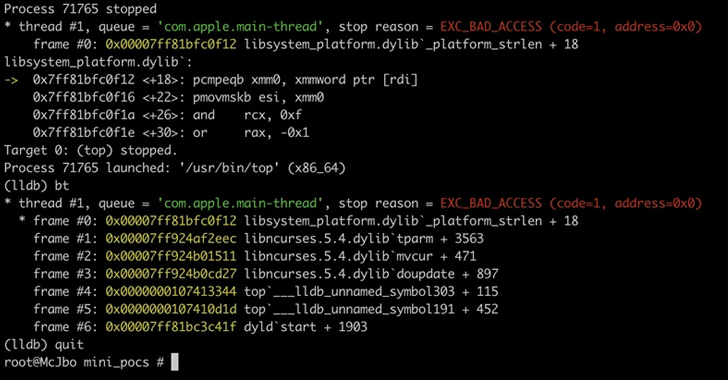
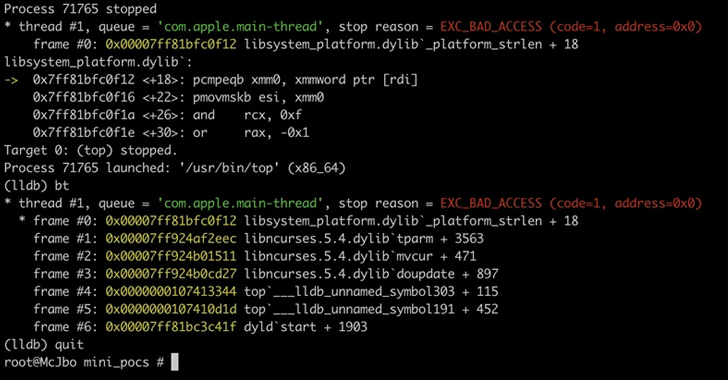 4.1KVulnerabilities
4.1KVulnerabilitiesMicrosoft Uncovers Flaws in ncurses Library Affecting Linux and macOS Systems
A set of memory corruption flaws have been discovered in the ncurses (short for new curses) programming library that could be exploited...
-

 5.0KMalware
5.0KMalwareCybercriminals Using PowerShell to Steal NTLMv2 Hashes from Compromised Windows
A new cyber attack campaign is leveraging the PowerShell script associated with a legitimate red teaming tool to plunder NTLMv2 hashes from...
-

 4.7KMalware
4.7KMalwareHackers Can Exploit Windows Container Isolation Framework to Bypass Endpoint Security
New findings show that malicious actors could leverage a sneaky malware detection evasion technique and bypass endpoint security solutions by manipulating the...
-
 4.8KVulnerabilities
4.8KVulnerabilitiesNew Ransomware Strain ‘CACTUS’ Exploits VPN Flaws to Infiltrate Networks
Cybersecurity researchers have shed light on a new ransomware strain called CACTUS that has been found to leverage known flaws in VPN...
-
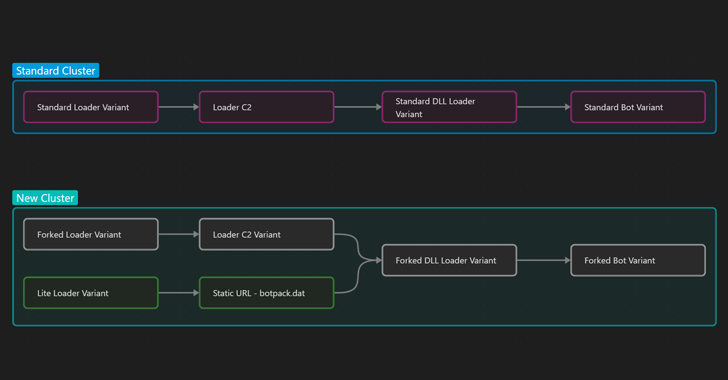
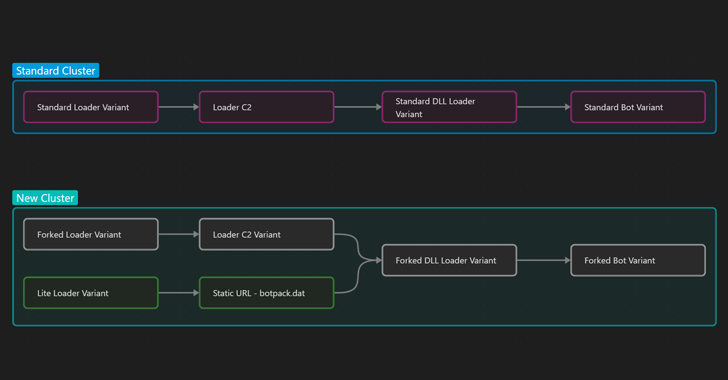 4.5KMalware
4.5KMalwareIcedID Malware Shifts Focus from Banking Fraud to Ransomware Delivery
Multiple threat actors have been observed using two new variants of the IcedID malware in the wild with more limited functionality that...





