All posts tagged "ethical hacking"
-

 426Lists
426Lists12 Best Operating Systems For Ethical Hacking And Penetration Testing | 2018 Edition
Wondering which is the best operating system for ethical hacking and pen testing purposes? Trying to solve this problem, Fossbytes has prepared...
-
 383Video Tutorials
383Video TutorialsHow to Change / Spoof your Mac Address using Macchanger on Kali Linux 2018.1
MAC Changer is an utility that makes the maniputation of MAC addresses of network interfaces easier. A media access control (Mac) address...
-
 202Articles
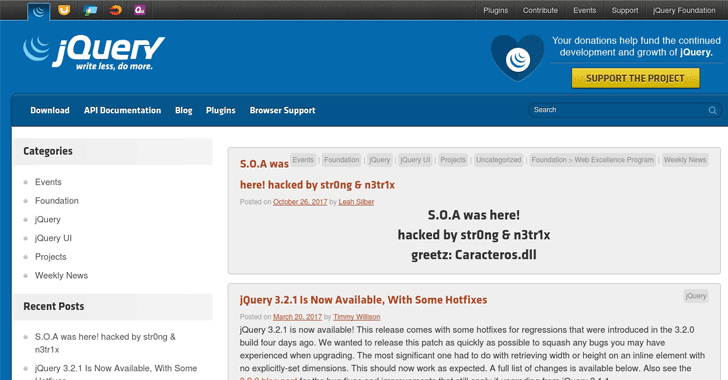
202ArticlesjQuery hacked: Site was hit, but not the library
The official blog of jQuery—most popular JavaScript library used by millions of websites—has been hacked by some unknown hackers, using the pseudonym...
-
Vulnerability Analysis
MIDA-Multitool – Bash Script Purposed For System Enumeration, Vulnerability Identification And Privilege Escalation
Bash script purposed for system enumeration, vulnerability identification and privilege escalation. MIDA Multitool draws functionality from several of my previous scripts namely...
-

 201Vulnerability Analysis
201Vulnerability AnalysisDorkNet – Selenium Powered Python Script To Automate Searching For Vulnerable Web Apps
Selenium powered Python script to automate searching the web for vulnerable applications. DorkNet can take a single dork or a list of...
-
Network Tools
Shadow – Unique Discrete Event Network Simulator
Shadow is a unique discrete-event network simulator that runs real applications like Tor and Bitcoin, and distributed systems of thousands of nodes...
-
Vulnerability Analysis
CyberScan – Tool To Analyse Packets, Decoding , Scanning Ports, And Geolocation
CyberScan is an open source penetration testing tool that can analyse packets , decoding , scanning ports, pinging and geolocation of an...
-
 266Exploitation Tools
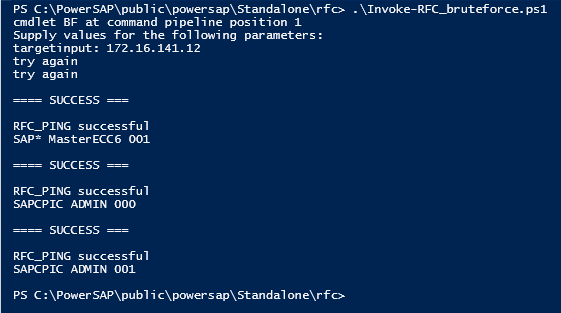
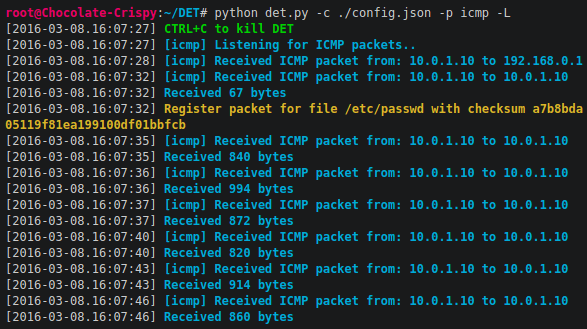
266Exploitation ToolsPowerSAP – Powershell SAP Assessment Tool
PowerSAP is a simple powershell re-implementation of popular & effective techniques of all public tools such as Bizploit, Metasploit auxiliary modules, or...
-
 208Information Gathering
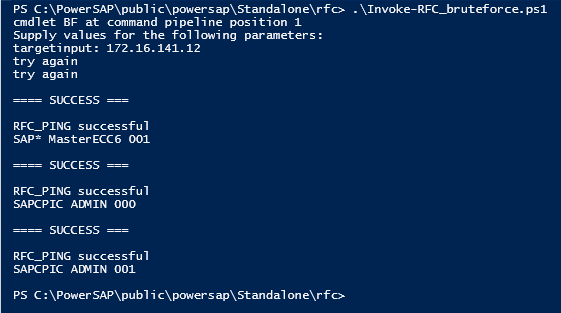
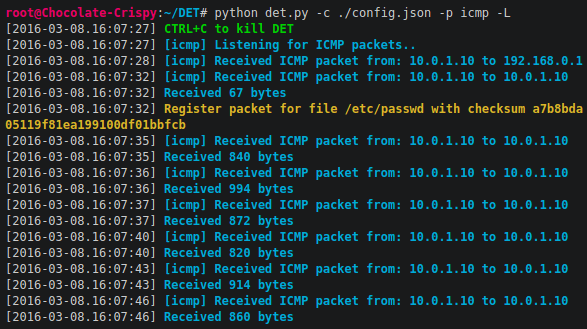
208Information GatheringDET – (extensible) Data Exfiltration Toolkit
DET (is provided AS IS), is a proof of concept to perform Data Exfiltration using either single or multiple channel(s) at the...
-
Vulnerability Analysis
VHostScan – Virtual Host Scanner
A virtual host scanner that can be used with pivot tools, detect catch-all scenarios, aliases and dynamic default pages. First presented at...
-
Stress Testing
drinkme – Shellcode Testing Harness
drinkme is a shellcode test harness. It reads shellcode from stdin and executes it. This allows pentesters to quickly test their payloads...
-

 356Reverse Engineering
356Reverse EngineeringdnSpy – NET Debugger & Assembly Editor
Reverse Engineer .NET Assemblies dnSpy is a tool to reverse engineer .NET assemblies. It includes a decompiler, a debugger and an assembly...
-
Forensics Tools
Meta Twin – File Resource Cloner
The project is designed as a file resource cloner. Metadata, including digital signature, is extracted from one file and injected into another....
-
Post Exploitation
portia – Automated Privilege Escalation
Portia aims to automate a number of techniques commonly performed on internal network penetration tests after a low privileged account has been...
-
Security Tools
TorWall – Transparent Tor for Windows
Tallow is a small program that redirects all outbound traffic from a Windows machine via the Tor anonymity network. Any traffic that...
-
Exploitation Tools
LFiFreak – An automated LFi Exploiter with Bind/Reverse Shells
LFiFreak is a tool for exploiting local file inclusions using PHP Input, PHP Filter and Data URI methods. Features Works with Windows,...
-

 324Pentest Linux Distributions
324Pentest Linux DistributionsTails 3.2 – Live System to Preserve Your Privacy and Anonymity
Tails is a live system that aims to preserve your privacy and anonymity. It helps you to use the Internet anonymously and...
-
Video Tutorials
How to Scan Websites for SQL Injection – DSSS – Damn Small SQLi Scanner – Kali Linux 2017.1
Hey Guys, In this video i show you a fast and small SQL Injection Scanner. Damn Small SQLi Scanner (DSSS) is a...
-
Exploitation Tools
PytheM – Python Pentesting Framework
pythem is a multi-purpose pentest framework written in Python. It has been developed to be used by security researchers and security professionals....
-

 229Man-In-The-Middle
229Man-In-The-MiddlemitmAP – Create a Fake AP and Sniff Data
A python program to create a fake AP and sniff data new in 2.0: SSLstrip2 for HSTS bypass Image capture with Driftnet...
-
Man-In-The-Middle
Xerosploit – Advanced Man In The Middle Framework
Xerosploit is a penetration testing toolkit whose goal is to perform man in the middle attacks for penetration testing purposes. It brings...






