All posts tagged "Exploitation"
-
 397Information Gathering
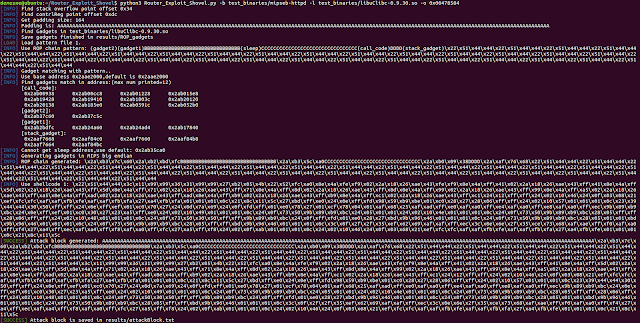
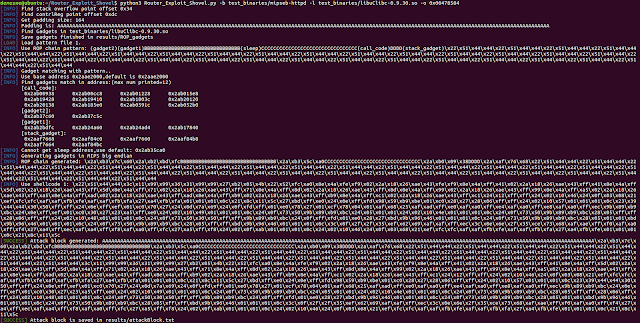
397Information GatheringRouter Exploit Shovel – Generation For Stack Overflow Routers Types
Automated Application Generation for Stack Overflow Types on Wireless Routers. Router exploits shovel is an automated application generation tool for stack...
-
 348Post Exploitation
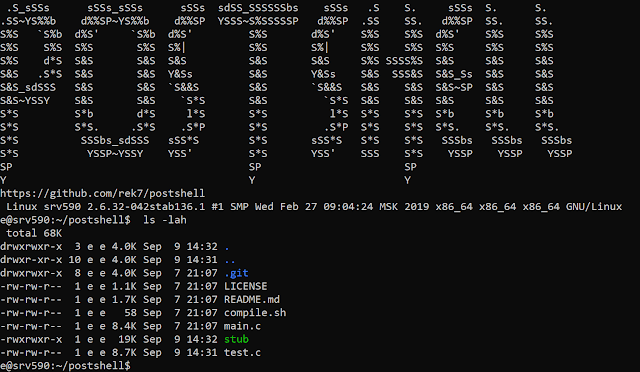
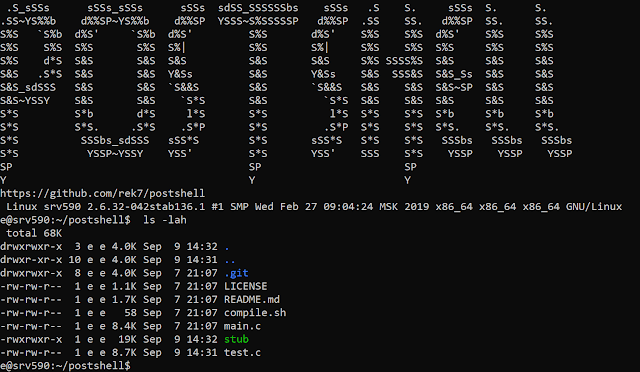
348Post ExploitationPostShell – Post Exploitation Bind/Backconnect Shell
PostShell is a post-exploitation shell that includes both a bind and a back connect shell. It creates a fully interactive TTY...
-
 253Exploitation Tools
253Exploitation ToolsBashark – Bash Post Exploitation Toolkit
Bashark aids pentesters and security researchers during the post-exploitation phase of security audits. Usage To launch Bashark on compromised host, simply source...
-

 287Malware
287MalwareFBI Uncovered North Korean Malware Attack KEYMARBLE on U.S Government Entities to Stealing Sensitive Data
DHS and FBI identified North Korean malware KEYMARBLE that related to HIDDEN COBRA to attack U.S government entities to capture screenshots, stealing...
-
 353Video Tutorials
353Video TutorialsHow to Generate a PHP Backdoor using Weevely – Kali Linux
Weevely is a web shell designed for post-exploitation purposes that can be extended over the network at runtime. Upload weevely PHP agent...
-
 267Exploitation Tools
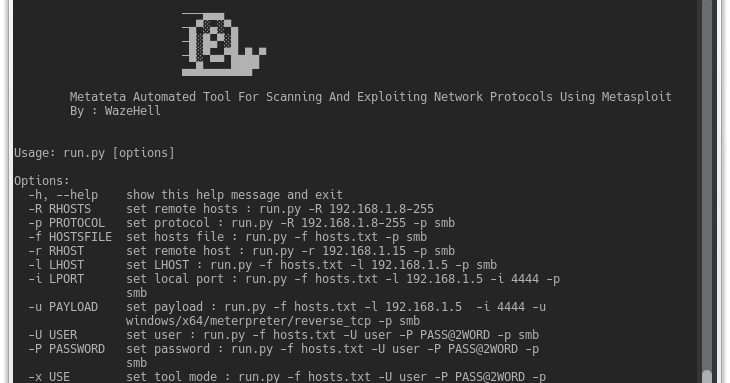
267Exploitation ToolsMetateta – Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit
Metateta Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit For faster pen testing for large networks What You Can Do...
-

 249Exploitation Tools
249Exploitation Toolsp0wnedShell- PowerShell Runspace Post Exploitation Toolkit
p0wnedShell is an offensive PowerShell host application written in C# that does not rely on powershell.exe but runs powershell commands and functions...
-
 306Post Exploitation
306Post ExploitationNishang – PowerShell Penetration Testing Framework
Nishang is an open source framework and collection of powerful PowerShell scripts and payloads that you can use during penetration testing audit,...
-
 317Post Exploitation
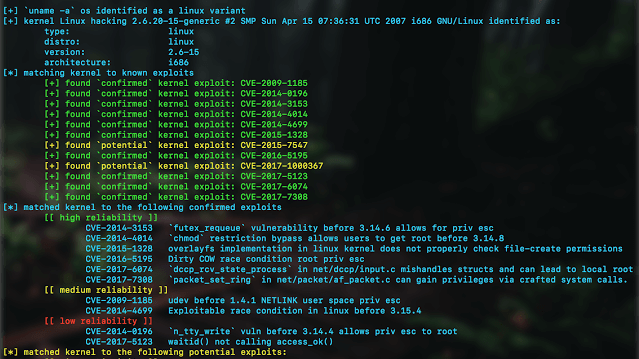
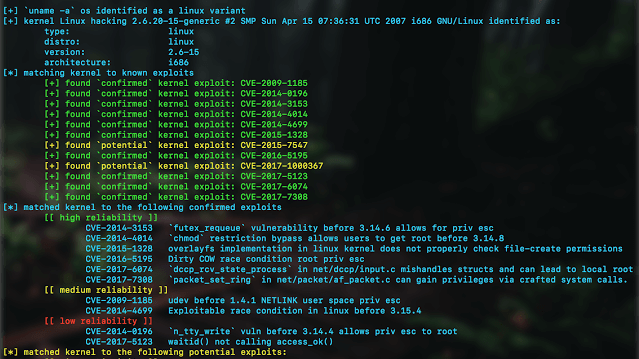
317Post ExploitationKernelpop – Kernel Privilege Escalation Enumeration And Exploitation Framework
kernelpop is a framework for performing automated kernel exploit enumeration on Linux, Mac, and Windows hosts. Requirementspython3 Currently supported CVE’s: *CVE-2017-1000367 *CVE-2017-1000112...
-
 249Vulnerability Analysis
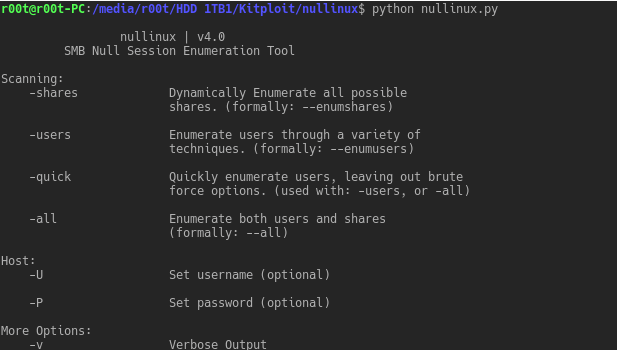
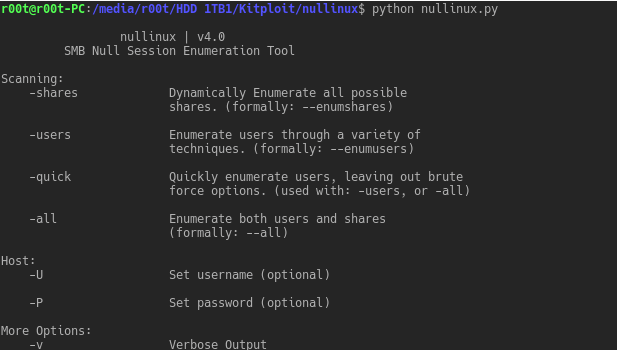
249Vulnerability Analysisnullinux – SMB null Session Identification and Enumeration Tool
nullinux is an internal penetration testing tool for Linux that can be used to enumerate OS information, domain information, shares, directories, and...
-
Vulnerability Analysis
MIDA-Multitool – Bash Script Purposed For System Enumeration, Vulnerability Identification And Privilege Escalation
Bash script purposed for system enumeration, vulnerability identification and privilege escalation. MIDA Multitool draws functionality from several of my previous scripts namely...
-

 190Vulnerabilities
190VulnerabilitiesOnePlus OTAs: Analysis & Exploitation
In this blog post we present new trivial vulnerabilities found on OnePlus One/X/2/3/3T OxygenOS & HydrogenOS. They affect the latest versions (4.1.3/3.0)...






