All posts tagged "Exploiting"
-
 340Vulnerabilities
340VulnerabilitiesActive campaign exploiting Apache Struts 2 vulnerability
A Monero mining script is spreading using remote command execution vulnerability It seemed a matter of time before attacks like these happened...
-
 228Articles
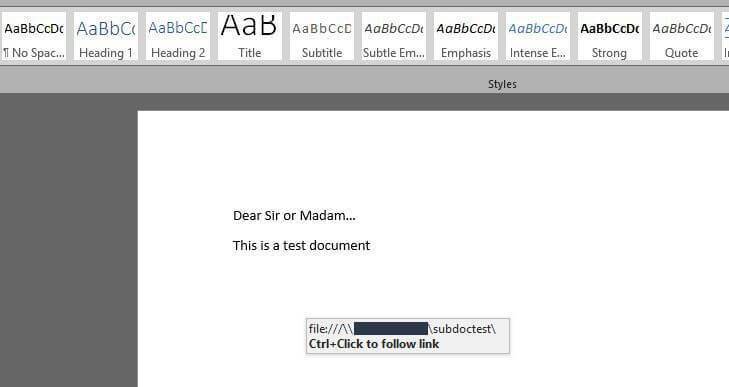
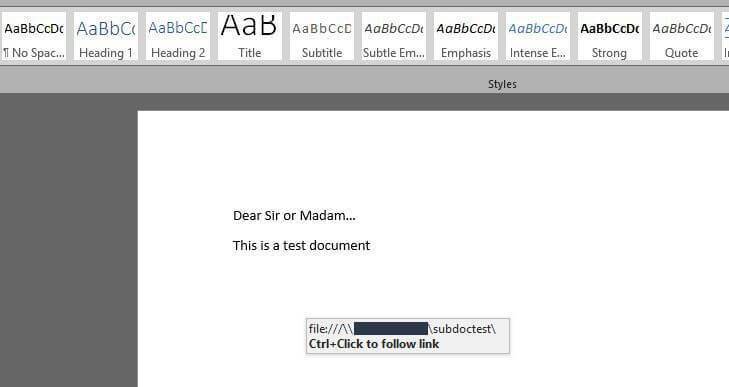
228ArticlesAttackers Can Steal Windows Credentials By Exploiting The subDoc Feature In Microsoft Word
Security researchers from Rhino Labs (a US-based cyber-security firm) have found that cyber criminals can use a Microsoft Word feature dubbed subDoc to fool...
-
 190Vulnerabilities
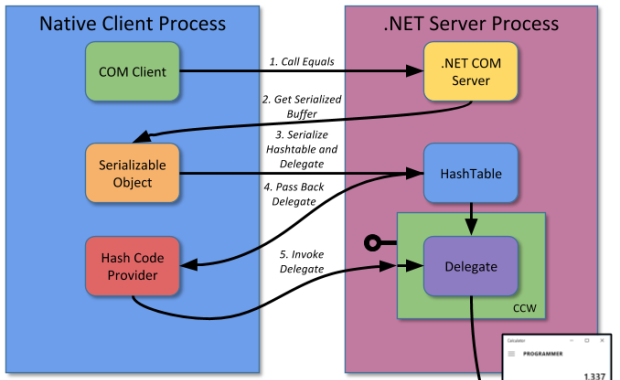
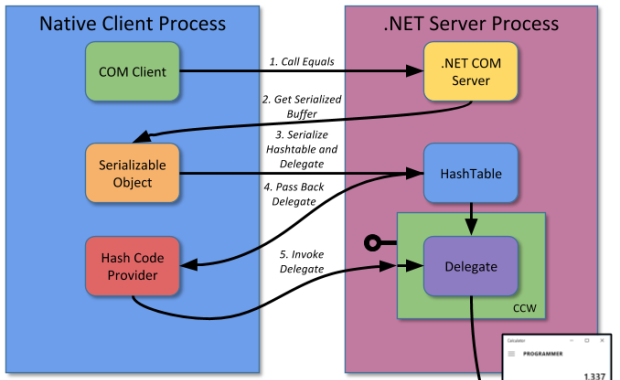
190VulnerabilitiesExploiting .NET Managed DCOM
One of the more interesting classes of security vulnerabilities are those affecting interoperability technology. This is because these vulnerabilities typically affect any...






