All posts tagged "Fileless Malware"
-

 3.6KMalware
3.6KMalwareHeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since...
-
 3.5KMalware
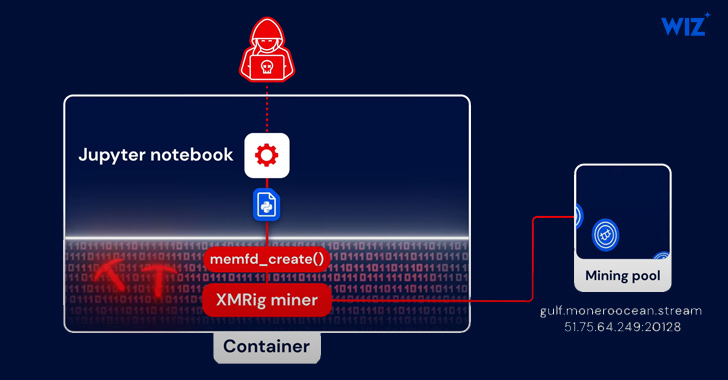
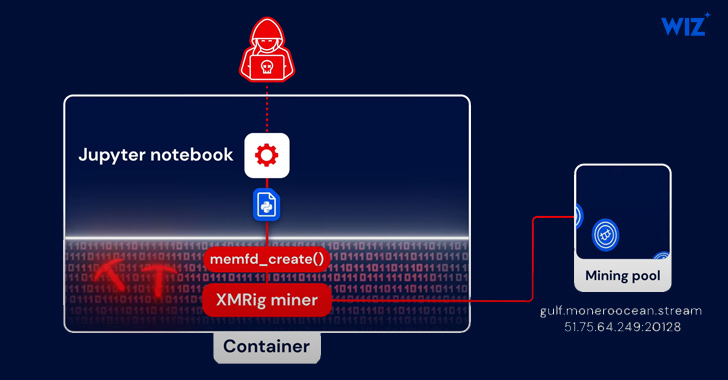
3.5KMalwarePython-Based PyLoose Fileless Attack Targets Cloud Workloads for Cryptocurrency Mining
A new fileless attack dubbed PyLoose has been observed striking cloud workloads with the goal of delivering a cryptocurrency miner, new findings...
-
 1.7KCyber Attack
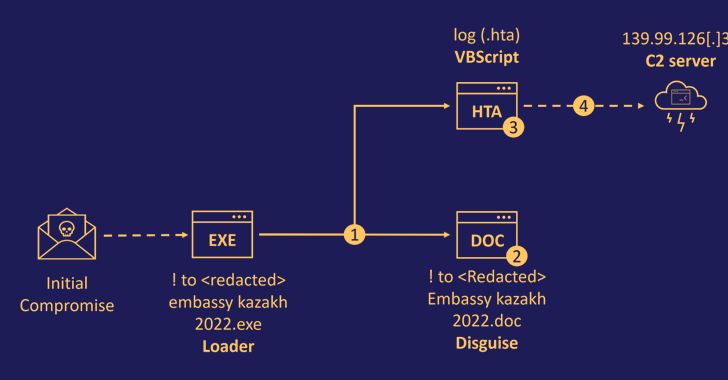
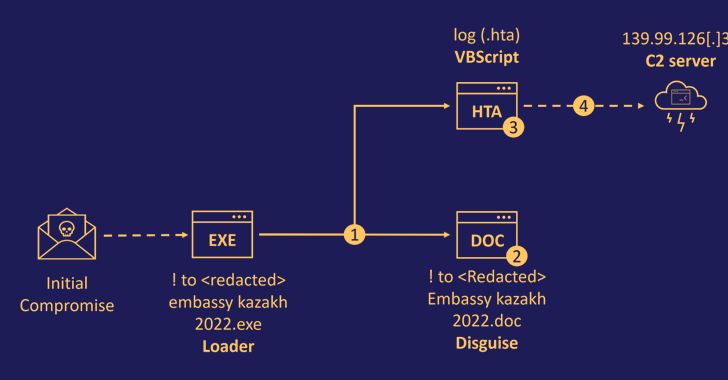
1.7KCyber AttackSophisticated DownEx Malware Campaign Targeting Central Asian Governments
Government organizations in Central Asia are the target of a sophisticated espionage campaign that leverages a previously undocumented strain of malware dubbed...
-

 3.3KMalware
3.3KMalwareHackers Sneak ‘More_Eggs’ Malware Into Resumes Sent to Corporate Hiring Managers
A new set of phishing attacks delivering the more_eggs malware has been observed striking corporate hiring managers with bogus resumes as an...
-
 3.9KCyber Attack
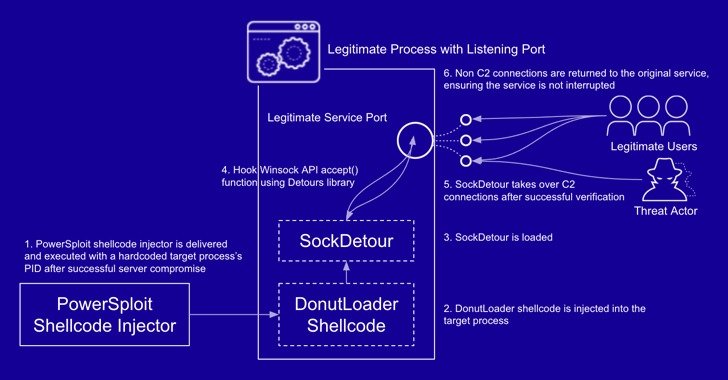
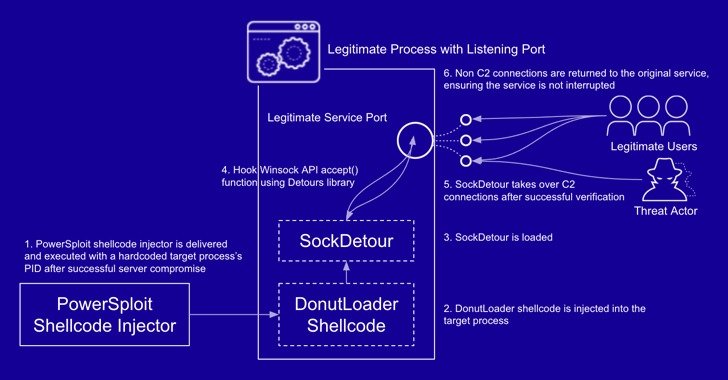
3.9KCyber AttackNew “SockDetour” Fileless, Socketless Backdoor Targets U.S. Defense Contractors
Cybersecurity researchers have taken the wraps off a previously undocumented and stealthy custom malware called SockDetour that targeted U.S.-based defense contractors with...
-

 2.4KMalware
2.4KMalwareChinese Hackers Spotted Using New UEFI Firmware Implant in Targeted Attacks
A previously undocumented firmware implant deployed to maintain stealthy persistence as part of a targeted espionage campaign has been linked to the...
-
 2.7KMalware
2.7KMalwareNew Fileless Malware Uses Windows Registry as Storage to Evade Detection
A new JavaScript-based remote access Trojan (RAT) propagated via a social engineering campaign has been observed employing sneaky “fileless” techniques as part...
-
 359Malware
359MalwareBeware!! New “Nodersok” Fileless Malware Hack Windows PC and Change into Zombie Proxies
Microsoft issued a serious warning about the new form of stealthy fileless Malware campaign “Nodersok” that attacks windows computers using living-off-the-land techniques....
-
 359Malware
359MalwareMicrosoft Warns of a New Rare Fileless Malware Hijacking Windows Computers
Watch out Windows users! There’s a new strain of malware making rounds on the Internet that has already infected thousands of computers...
-
 308Malware
308MalwareTurla APT Hackers Upgraded Its Arsenal with New Hacking Tool “Topinambour” to Attack Government Networks
Infamous Turla APT Hackers group renew its arsenal with a new hacking tool named “Topinambour ” also called as aka Sunchoke that...
-
 387Cyber Attack
387Cyber AttackWatch Out! Microsoft Spotted Spike in Astaroth Fileless Malware Attacks
Security researchers at Microsoft have released details of a new widespread campaign distributing an infamous piece of fileless malware that was primarily...
-
 354Malware
354MalwareMicrosoft Spotted New Fileless Malware “Astaroth” that Abusing Legitimate Tools To Hack Your Windows
A widespread fileless malware campaign called Astaroth spotted with the “lived off the land” method to attack Windows users with advanced persistent...
-

 364Malware
364MalwareHackers using steganography to Drop the Powload Malware & Hide Their Malvertising Traffic
Cyber criminals now approaching a unique way to spread Powload malware with the help of steganography to infect the targeted system. Powload...
-

 210Hacked
210HackedWannaMine: Another Cryptojacking Malware Fueled By Leaked NSA Exploit Is Rising
You might be able to recall the NSA exploit called EternalBlue which was leaked by the hacker group in April last year....
-
 320Malware
320MalwareUsing n1n3 to Simulate an Evasive Fileless Malware – Proof Of Concept
Fileless malware are types of malicious code used in cyber attacks that don’t use files to launch the attack and carry on...
-
 289Malware
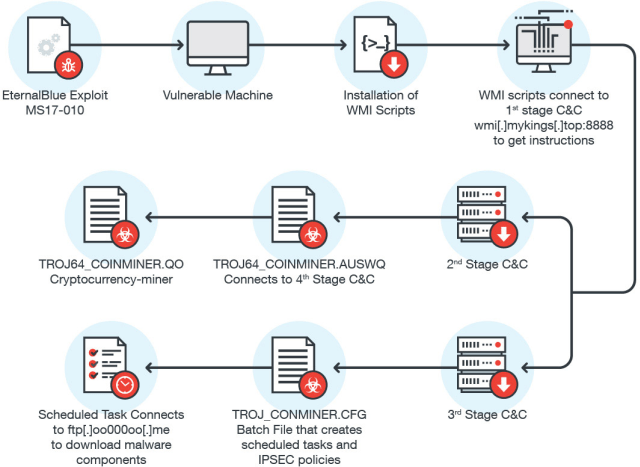
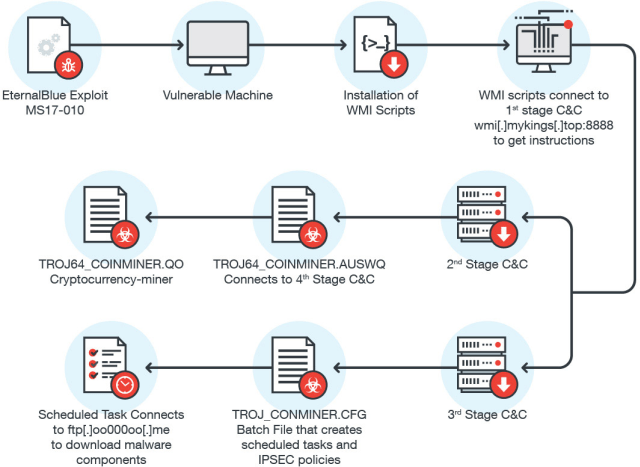
289MalwareFileless Cryptocurrency Miner that affects Windows Machine Through WMI and EternalBlue
Nowadays Hackers Distributing Advanced Fileless Malware with Evasion capabilities which are very Difficult to Detect. Security experts from Trend Micro Identified a...
-

 302Malware
302MalwareFileless malware that uses PowerShell scripts from Window’s registry leading to Click Fraud Malware Campaign
Nowadays Hackers Distributing Advanced Fileless Malware with Evasion capabilities which are very Difficult to Detect. These types of malware sit in the...
-
 310Malware
310MalwareA Complete Fileless Malware “JS_POWMET” with Highly Sophisticated Evasion Technique
Hackers are Distributing Advanced Fileless Malware with Evasion capabilities that lead very Difficult to Detect With a different kind of Advance Attacking...
-
 362Malware
362MalwareMachine learning system to create invisible malwares – gym-malware
In the recent DEF CON Meet, technical director of security shop Endgame Hyrum Anderson disclosed a research paper on adapting API frameworks...
-
 378Ransomware
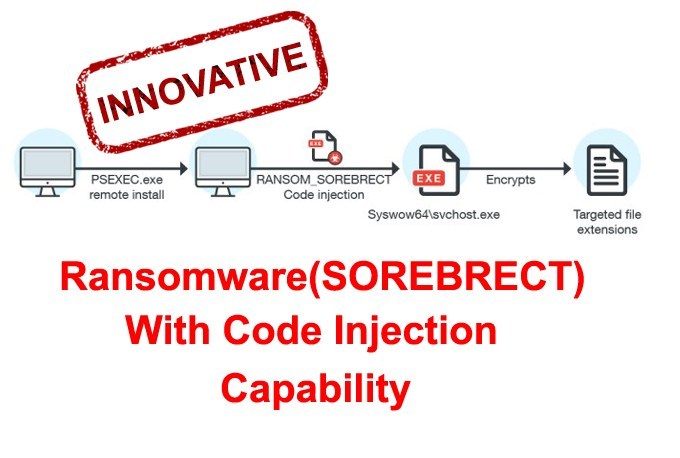
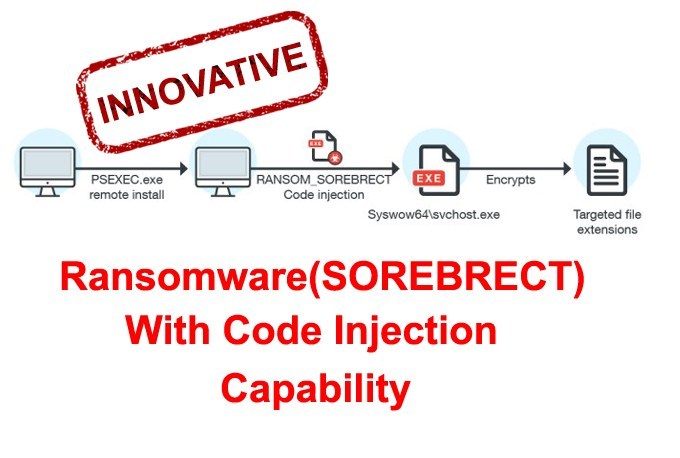
378RansomwareA Fileless Ransomware Called “SOREBRECT” Discovered with Code Injection Capability that Encrypts local and Network Share Files
A Fileless Ransomware “SOREBRECT” Discovered that have the capability to inject the Malicious code into the target and Encrypt the victim’s data....
-

 232Cyber Attack
232Cyber AttackUsing Fileless Malware Hackers Stole More Than $800,000 from ATMs
Hackers centered at the least eight ATMs in Russia and stole $800,000 using fileless malware in a single night, however, the technique...






