All posts tagged "fingerprinting"
-
 634Security Tools
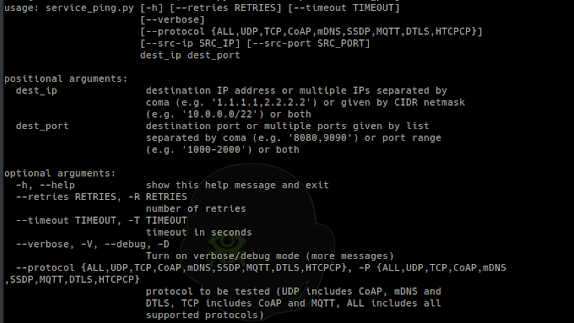
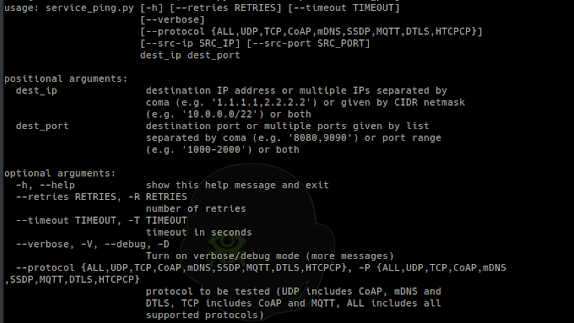
634Security ToolsCotopaxi – Tools For Security Testing Of Internet Of Things Devices
Set of tools for security testing of Internet of Things devices using protocols like: CoAP, DTLS, HTCPCP, mDNS, MQTT, SSDP. Installation: Simply clone...
-

 430Network Tools
430Network ToolsFATT – Extracting Network Metadata And Fingerprints From Pcap Files
FATT is a script for extracting network metadata and fingerprints such as JA3 and HASSH from packet capture files (pcap) or...
-

 516Data Breach
516Data BreachBiometric Security Platform Data Breach Leaked Millions of Users Facial Recognition & Fingerprinting Data
Security researchers discovered the biggest data breach in Biometric Security Platform BioStar 2 that leaks millions of users facial recognition records, fingerprints,...
-

 260Hacked
260HackedYour Smartphone’s Sensors Can Be Used To Track You
In a world where companies are hungry for user data and are adopting different mechanisms to legally or illegally get hold of...
-

 337Mobile Security
337Mobile SecurityOnePlus 7 Pro Fingerprint Scanner Hacked In a Minutes Using a Fake Fingerprint
OnePlus 7 Pro Fingerprint Scanner hacked within minutes using Fake Fingerprint that can be created using hot-glue due to inadequate security that...
-

 284Data Security
284Data SecurityIs Flawless Anonymity Possible?
The condition of being anonymous is called anonymity – Let’s suppose you want to post the most anonymous comment on a social...
-

 366News
366NewsTor’s Anti-Fingerprinting Technique ‘Letterboxing’ Coming To Firefox 67
Once again, Mozilla has taken a leaf out of Tor browser’s handbook with the introduction of user anti-fingerprinting technique in Firefox 67...
-
 231Information Gathering
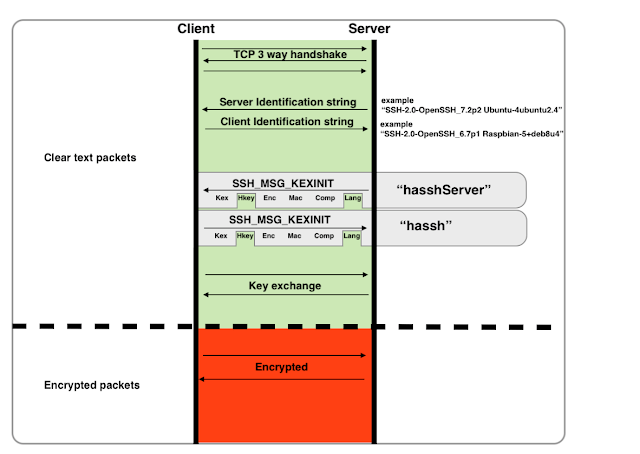
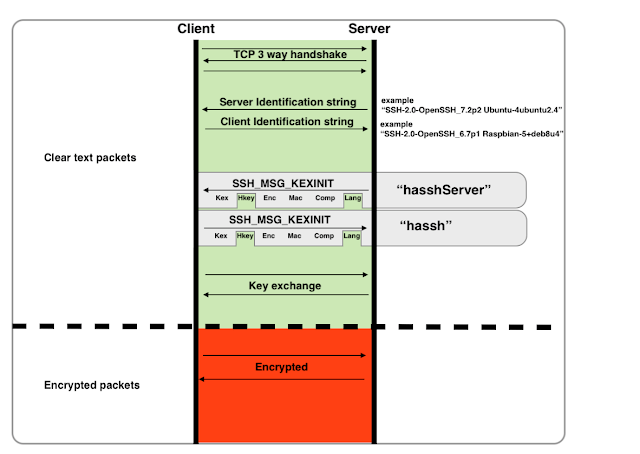
231Information GatheringHASSH – A Network Fingerprinting Standard Which Can Be Used To Identify Specific Client And Server SSH Implementations
“HASSH” is a network fingerprinting standard which can be used to identify specific Client and Server SSH implementations. The fingerprints can be...
-
 187Security Tools
187Security ToolsWPHardening v1.6 – Fortify the security of any WordPress installation
Fortify the security of any WordPress installation. This tool releases new versions on a regular basis. Make sure to update your dependencies...
-
 238Vulnerability Analysis
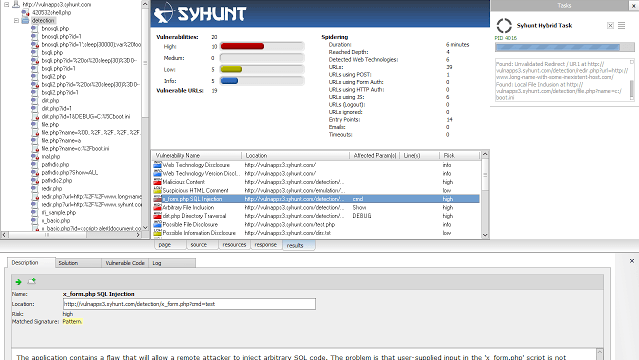
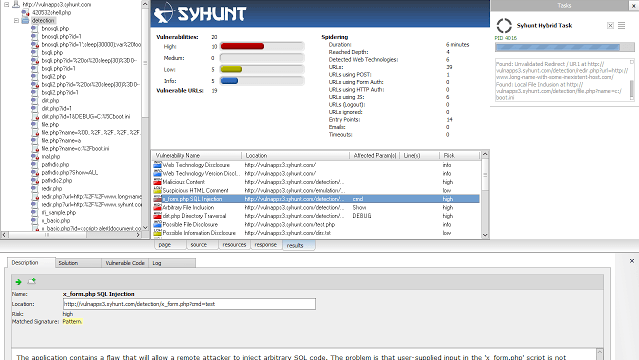
238Vulnerability AnalysisSyhunt ScanTools 6.0 – Console Web Vulnerability Scan Tools
Syhunt ScanTools 6.0 adds advanced fingerprinting capabilities, enhanced spidering, injection and code scan capabilities, and a large number of improved checks. Adds...
-
Articles
Websites need to ask permission to extract fingerprints from the user in Firefox 58
Canvas fingerprinting relies on websites meaning able to receive data from HTML canvas details calmly. In future, Firefox users will be required...
-
 248Network Tools
248Network Toolspsad – Intrusion Detection and Log Analysis with iptables
The Port Scan Attack Detector psad is a lightweight system daemon written in is designed to work with Linux iptables/ip6tables/firewalld firewalling code...
-
 253Information Gathering
253Information GatheringScannerl – Modular Distributed Fingerprinting Engine
Scannerl is a modular distributed fingerprinting engine implemented by Kudelski Security. Scannerl can fingerprint thousands of targets on a single host, but can...
-

 186Hacked
186HackedWebsites Can Now Track 36 Features Of Your Computer, Identify You Even If You Use Multiple Browsers
Short Bytes: A new research conducted at the Lehigh University has taken the browser fingerprinting to a whole new level. They have...
-
 258Data Security
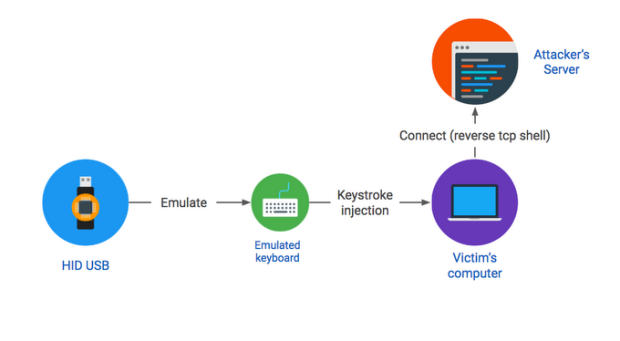
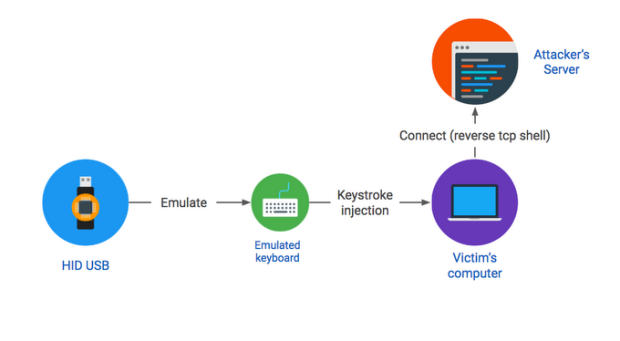
258Data Security#BHUSA2016 – Researcher explained how to hack any PC with a found USB drive
Dropping a malicious USB key in a parking lot is an effective attack vector, as demonstrated by our recent large-scale study. This...
-

 205Data Security
205Data SecurityHow JavaScript Functions And Mouse Movements Can Reveal TOR Users’ True Identity
Short Bytes: While TOR software suite promises enhanced privacy and security, researchers have found new ways like TOR user fingerprinting to unmask...






