All posts tagged "forensics"
-
 237Forensics Tools
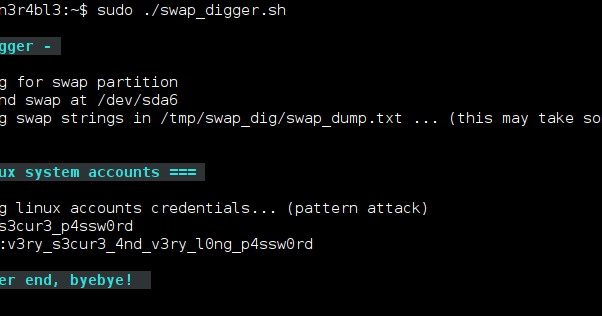
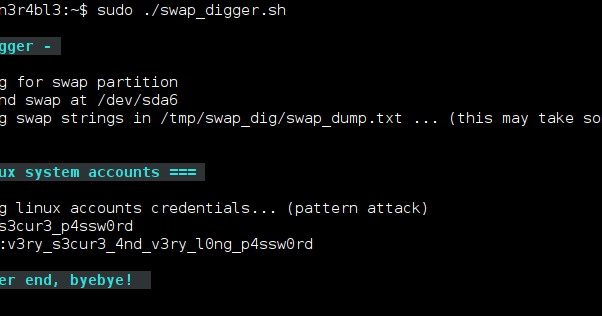
237Forensics ToolsSwap Digger – Tool That Automates Swap Extraction And Searches For User Credentials, Web Forms Credentials, Emails, Http Authentication, Wifi SSID And Keys, Etc
swap_digger is a bash script used to automate Linux swap analysis for post-exploitation or forensics purpose. It automates swap extraction and searches...
-
 285Forensics Tools
285Forensics ToolsHindsight – Internet History Forensics For Google Chrome/Chromium
Hindsight is a free tool for analyzing web artifacts. It started with the browsing history of the Google Chrome web browser and...
-
 197Data Security
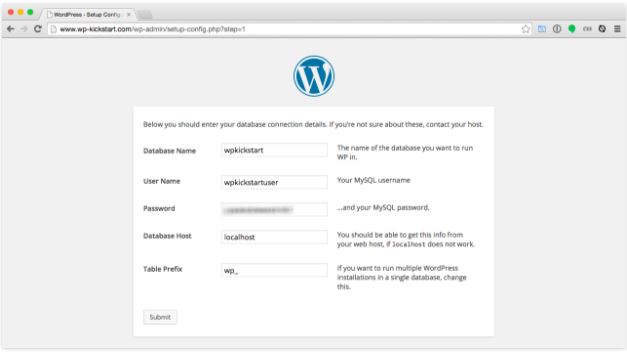
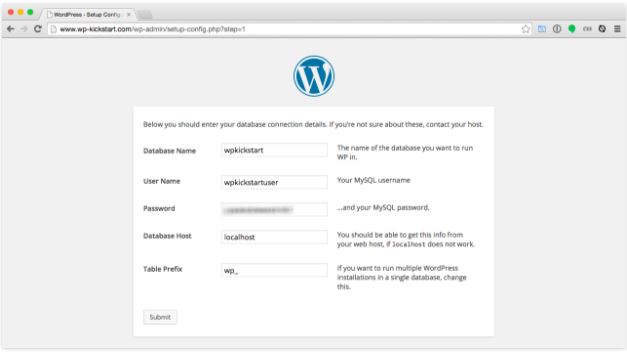
197Data SecurityForensics report of WordPress hacked site
This post details the forensics performed by Information security trainingprofessional during the clean-up operation. The expert also note specific WordPress security recommendations based...
-
 291Forensics Tools
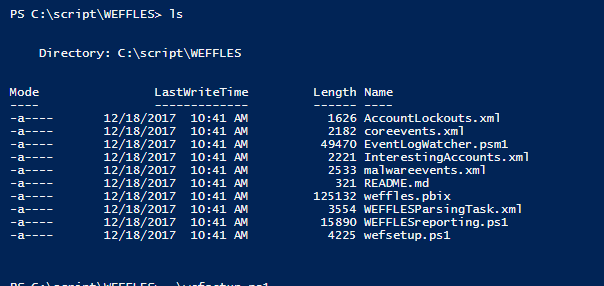
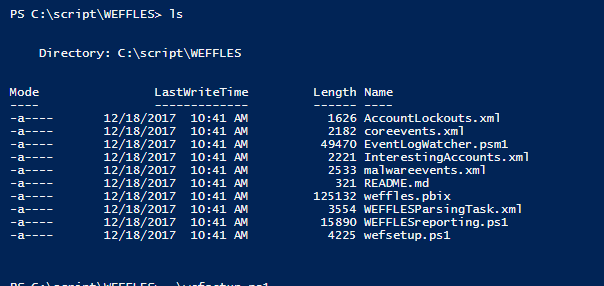
291Forensics Toolsweffles – Threat Hunting/Incident Response Console with Windows Event Forwarding and PowerBI.
WEFFLES is designed to be small and lightweight, both for speed of getting something deployed during an Incident Response and also for...
-
 301Forensics Tools
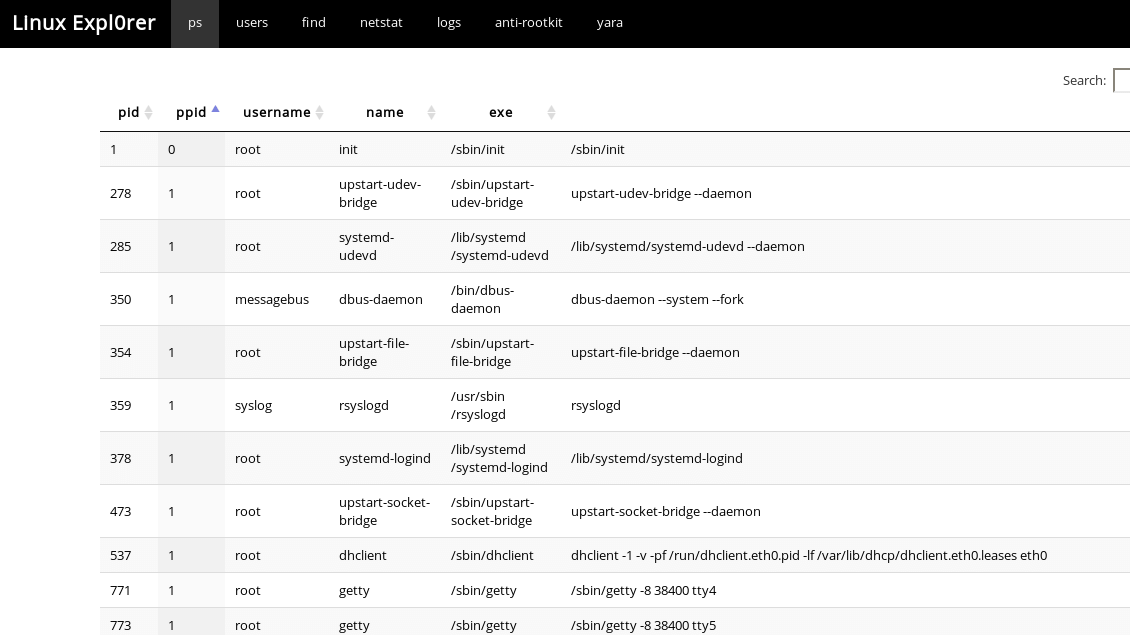
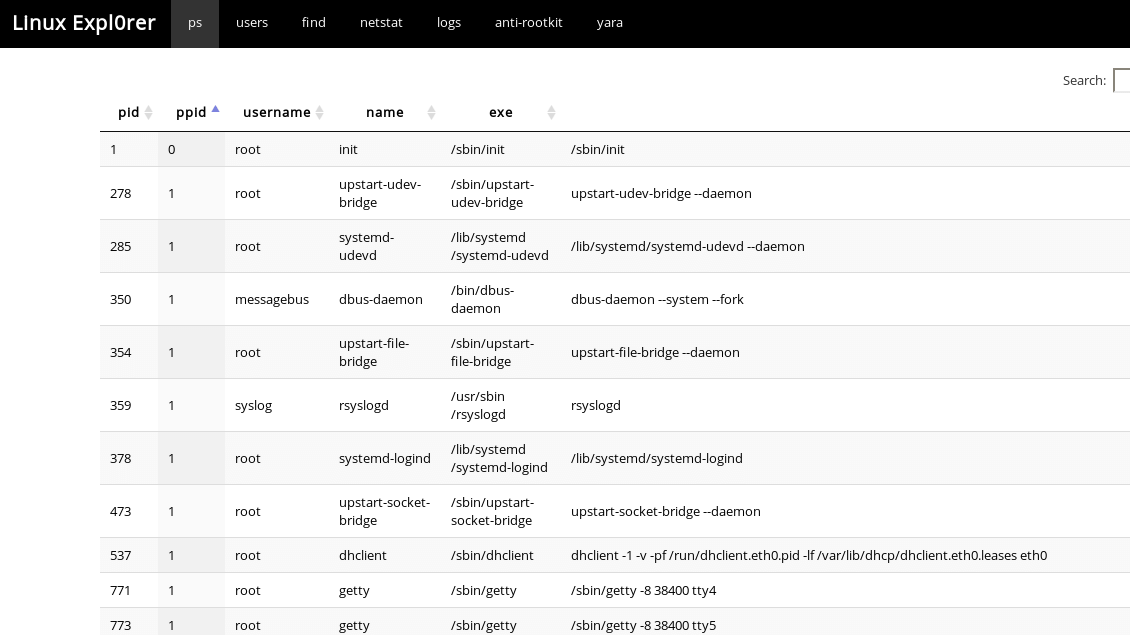
301Forensics ToolsLinux Expl0rer – Easy-To-Use Live Forensics Toolbox For Linux Endpoints
Easy-to-use live forensics toolbox for Linux endpoints written in Python & Flask. Capabilities ps View full process list Inspect process memory map...
-
Forensics Tools
srum-dump – A Forensics Tool to Convert the Data in the Windows srum
srum-dump This program will create an excel spreadsheet containing forensics artifacts contained the SRUM (System Resource Utilization Manager) database. The program can...
-
Network Tools
Shadow – Unique Discrete Event Network Simulator
Shadow is a unique discrete-event network simulator that runs real applications like Tor and Bitcoin, and distributed systems of thousands of nodes...
-
Articles
Your Facebook Account Can be Hacked through new Phishing Scam
Security researchers from AccessNow have discovered a new Facebook phishing scam that can also fool a professional technical user into falling victim...
-
 246Network Tools
246Network Toolspsad – Intrusion Detection and Log Analysis with iptables
The Port Scan Attack Detector psad is a lightweight system daemon written in is designed to work with Linux iptables/ip6tables/firewalld firewalling code...
-
 247Forensics Tools
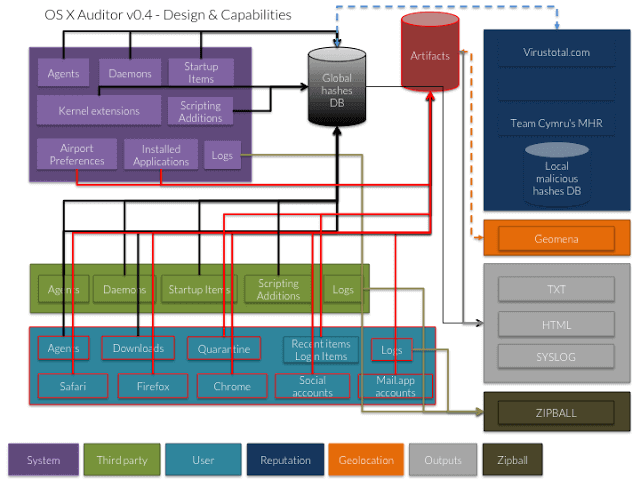
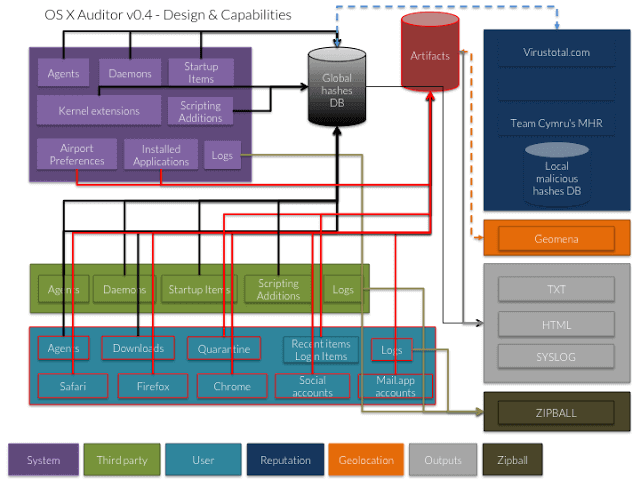
247Forensics ToolsOSXAuditor – Free Mac OS X Computer Forensics Tool
OS X Auditor is a free Mac OS X computer forensics tool. OS X Auditor parses and hashes the following artifacts on...
-
 258Reverse Engineering
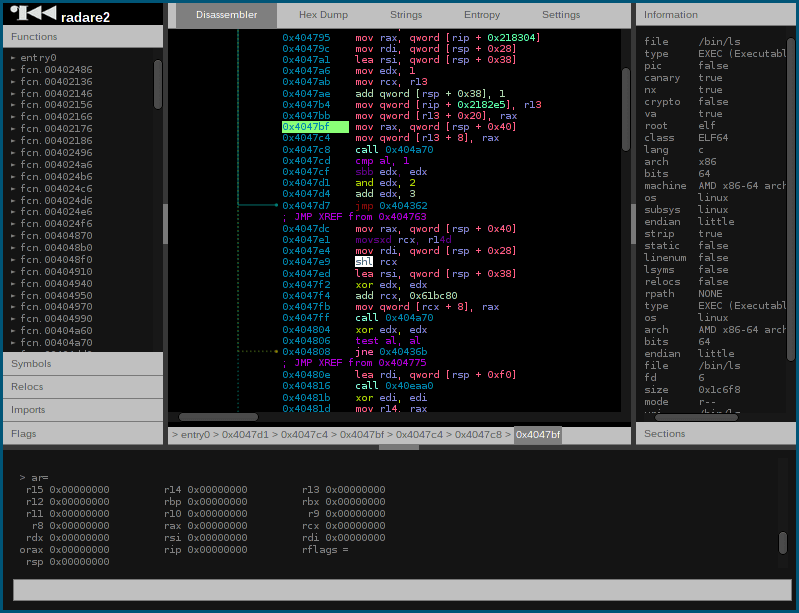
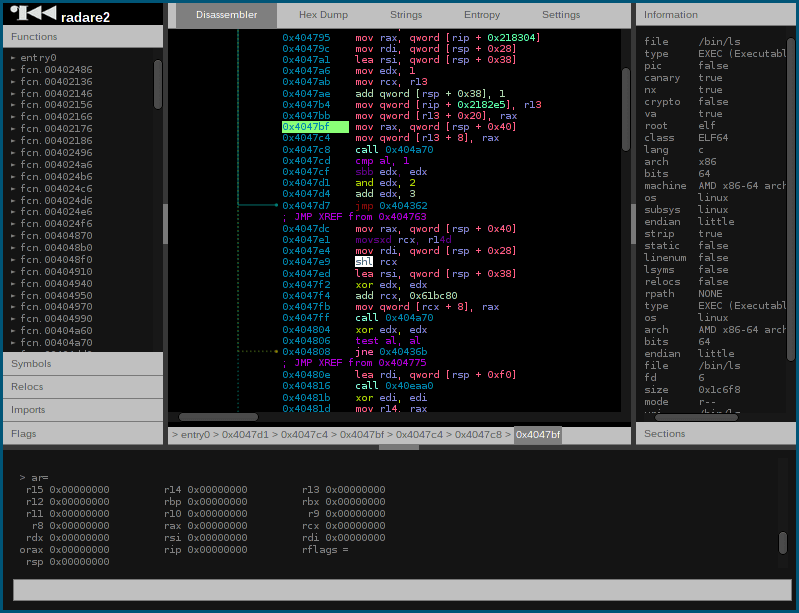
258Reverse Engineeringradare2 – Unix-Like Reverse Engineering Framework And Commandline Tools
r2 is a rewrite from scratch of radare in order to provide a set of libraries and tools to work with binary...
-

 231Incidents
231IncidentsCellebrite digital forensics tools leaked online by a reseller
The firmware used by the Israeli mobile forensic firm Cellebrite was leaked online by one of its resellers, the McSira Professional Solutions....
-
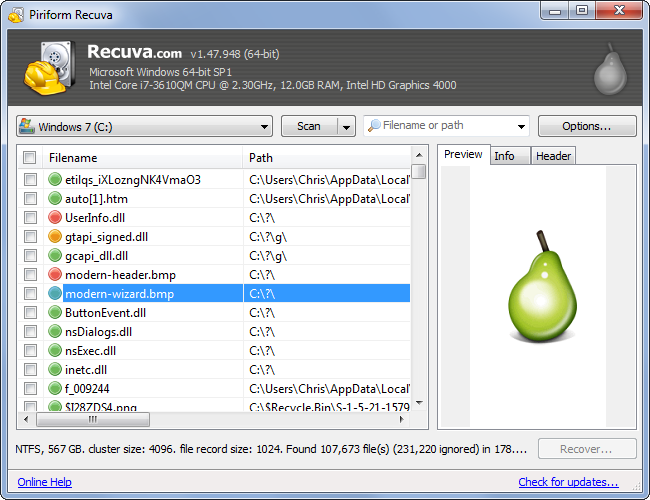
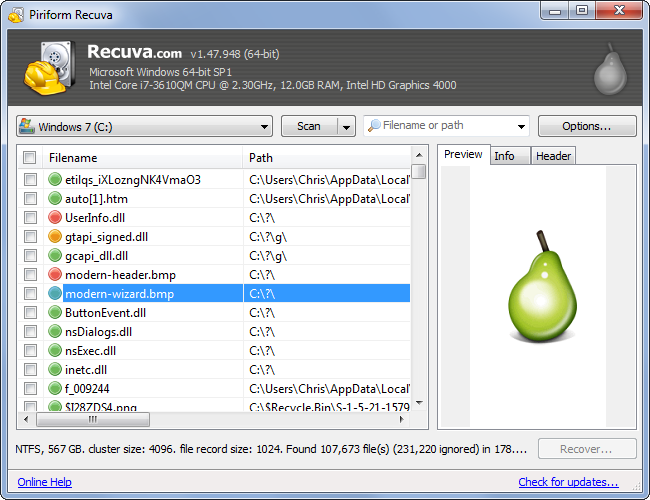 213Computer Forensics
213Computer ForensicsRecovering your Deleted Files
It has happened to most of us. You deleted a file and realize you need it back. But is it really deleted?...
-

 319Hacking Tutorials
319Hacking TutorialsBacktracing a RAT / Find the IP of the Hacker’s RAT
Welcome to my tutorial, today i will be showing you how to get someone’s ip once you have the person’s RAT. In...






