All posts tagged "GitHub"
-

 176How To
176How Topassfault – OWASP Passfault Evaluates Passwords & Enforces Password Policy In A Different Way
OWASP Passfault evaluates passwords and enforces password policy in a completely different way. Running the Command-line Interface Step 1: install javaStep 2:...
-

 294How To
294How Tochisel – Fast TCP tunnel over HTTP
Chisel is a fast TCP tunnel, transported over HTTP. Single executable including both client and server. Written in Go (Golang). Chisel is...
-

 241How To
241How ToLUNAR – Lockdown UNix Auditing and Reporting
It can perform a lockdown. Unlike some other scripts it has the capability to backout changes. Files are backed up using cpio...
-

 170How To
170How TorePy2exe – Reverse Engineering Tool For py2exe Applications
rePy2exe, a Reverse Engineering Tool for py2exe applications. cmake git python 2.7 Enter the following command to download rePy2exe file git...
-

 170How To
170How ToOperative – The Fingerprint Framework
This is a framework based on fingerprint action, this tool is used for get information on website or enterprise target pip...
-

 171How To
171How ToKickThemOut – Tool To Kick Devices Off Your Network
A tool to kick devices out of your network and enjoy all the bandwidth for yourself. It allows you to select specific...
-
 294Geek
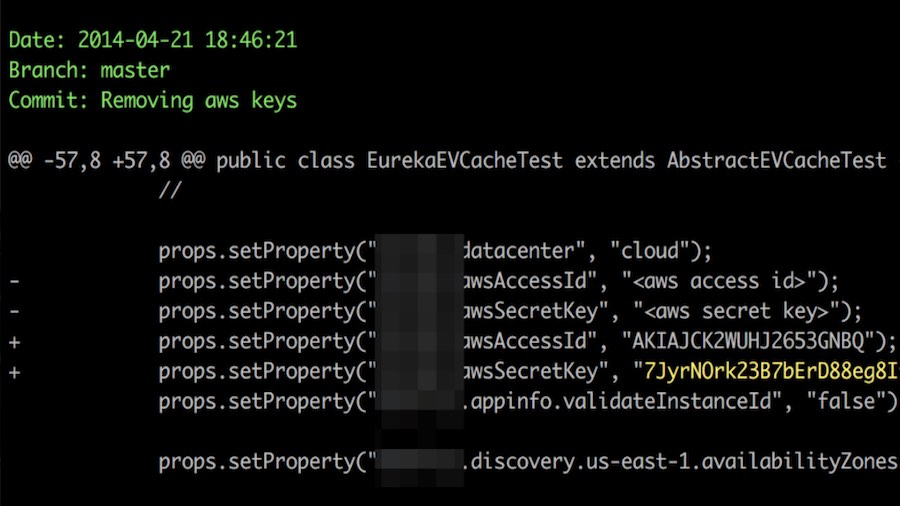
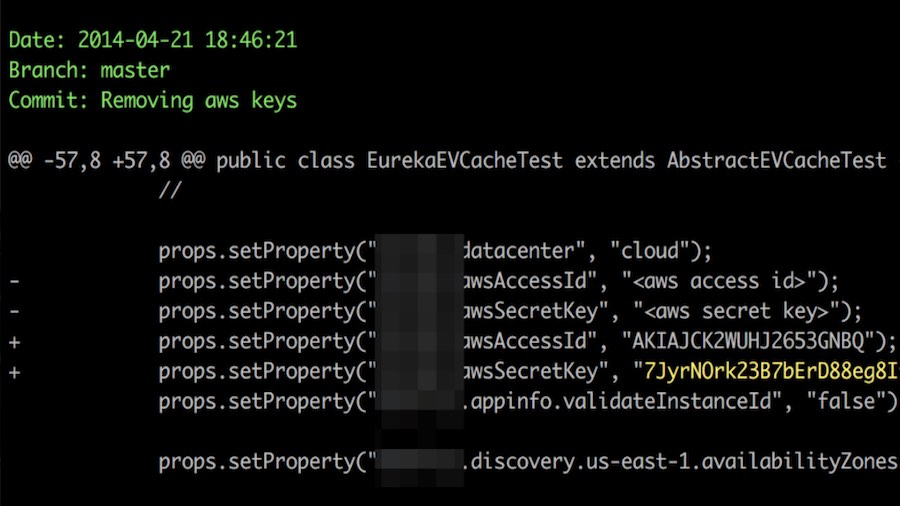
294GeekHacker Publishes Open Source Tool For Finding Secret Keys On GitHub
Short Bytes: A hacker has published an open source tool for helping administrators strengthen the security of their networks. Dubbed TruffleHog, this tool...
-
 235How To
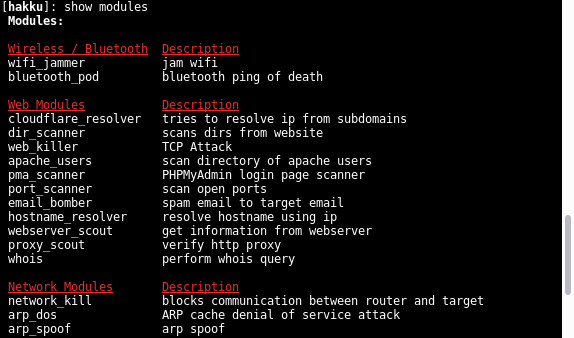
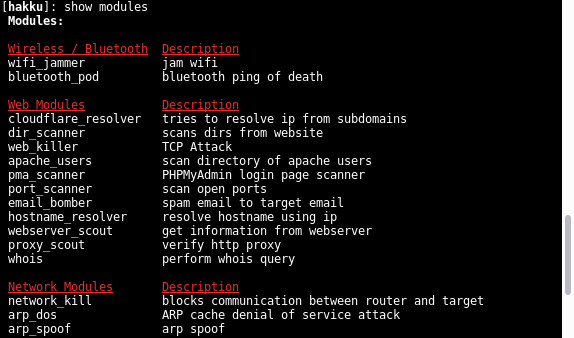
235How ToHakku Framework – Simple Penetration Testing Framework
Hakku Framework is been made for penetration testing. It offers simple structure, basic CLI, and useful features for penetration testing tools developing. Hakku is...
-

 242How To
242How ToWifijammer – Blocks All WiFi Clients/Routers
Wifijammer, is a tool that blocks all wifi clients and access points within range. The effectiveness of this script is constrained by your...
-

 281How To
281How ToSteghide – Tool To Find Hidden Information And Password In A File
Steghide, is a tool that executes a brute force attack to file with hide information and password established. Linux operating system Steghide Python...
-

 296How To
296How ToCommix – Automated All-In-One OS Command Injection And Exploitation Tool
Commix, other wise known as [ comm ]and [ i ]njection e[ x ]ploiter is an automated tool written by that can...
-

 207How To
207How ToLobotomy – Android Reverse Engineering Tool
Lobotomy is a command line based Android reverse engineering tool. Components: Permission Strings Attack Surface Surgical Interact UI De-compile De-buggable Dextra...
-

 227How To
227How ToRaptor WAF – Web Application Firewall Using DFA
Raptor WAF is a simple web application firewall made in C, using KISS principle, to make poll use select() function, is not...
-

 285How To
285How ToHijacker – Graphical User Interface For Wireless Auditing Tools In Android
Hijacker is a Graphical User Interface for the wireless auditing tools airodump-ng, aireplay-ng and mdk3. It offers a simple and easy UI...
-

 245How To
245How ToMSF-Remote-Console – Tool To Connect To The Msfrcpd Server Of Metasploit
A remote msfconsole written in Python 2.7 to connect to the msfrcpd server of metasploit. This tool gives you the ability to...
-

 228How To
228How ToMorpheus – Automated Ettercap TCP/IP Hijacking Tool
Morpheus is a framework tool which automates TCP/UDP packet manipulation tasks by using etter filters to manipulate target requests/responses under MitM attacks...
-

 244How To
244How ToWiFiPhisher – Automated Phishing Attacks Against Wi-Fi Clients
Wifiphisher is a security tool that mounts automated victim-customized phishing attacks against WiFi clients in order to obtain credentials or infect the...
-
 265How To
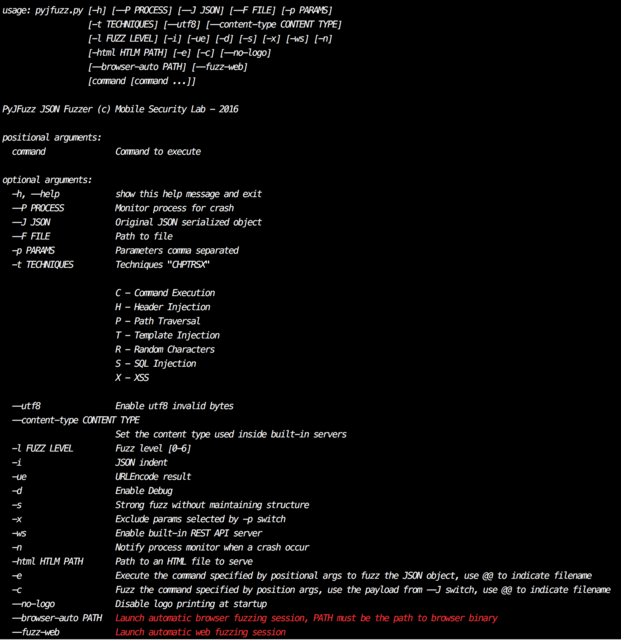
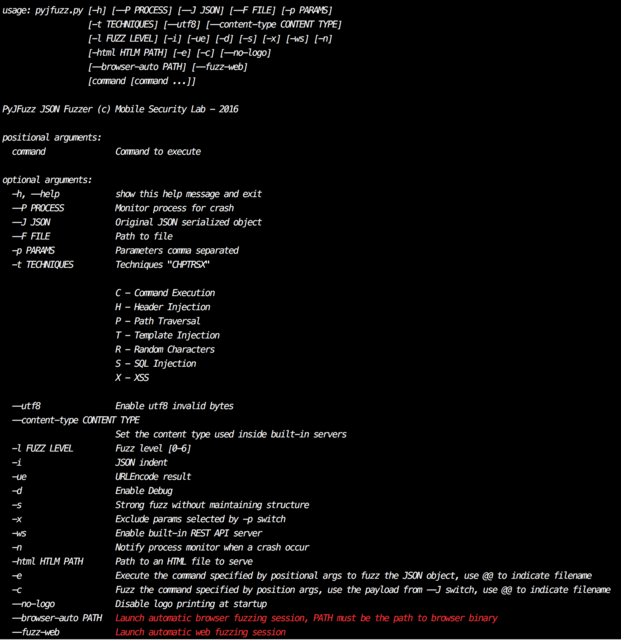
265How ToPyJFuzz – Python JSON Fuzzer
PyJFuzz is a small, extensible and ready-to-use framework used to fuzz JSON inputs , such as mobile endpoint REST API, JSON implementation,...
-

 200How To
200How ToFileBuster – Fast And Flexible Web Fuzzer
FileBuster, a free tool to fuzz a website faster & flexible based on a dictionary using regex patterns. FileBuster was built based...
-
 248How To
248How Todedsploit – Framework For Attacking Network Protocols
dedsploit is an open source software use for attacking network protocols and network exploitation. This framework aims to exploit and attack some common...
-

 212How To
212How ToPhishLulz – Ruby Toolset To Automate Phishing Activities
The VM comes with various open source tools that have been glued together. The two main components are: PhishingFrenzy (https://github.com/pentestgeek/phishing-frenzy) BeEF (https://github.com/beefproject/beef)...






