All posts tagged "Google Cloud"
-

 1.7KVulnerabilities
1.7KVulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
New cybersecurity research has found that command-line interface (CLI) tools from Amazon Web Services (AWS) and Google Cloud can expose sensitive credentials...
-
 4.8KCyber Attack
4.8KCyber AttackBanking Trojans Target Latin America and Europe Through Google Cloud Run
Cybersecurity researchers are warning about a spike in email phishing campaigns that are weaponizing the Google Cloud Run service to deliver various...
-
 1.7KVulnerabilities
1.7KVulnerabilitiesReptar: New Intel CPU Vulnerability Impacts Multi-Tenant Virtualized Environments
Intel has released fixes to close out a high-severity flaw codenamed Reptar that impacts its desktop, mobile, and server CPUs. Tracked as...
-
 1.3KMalware
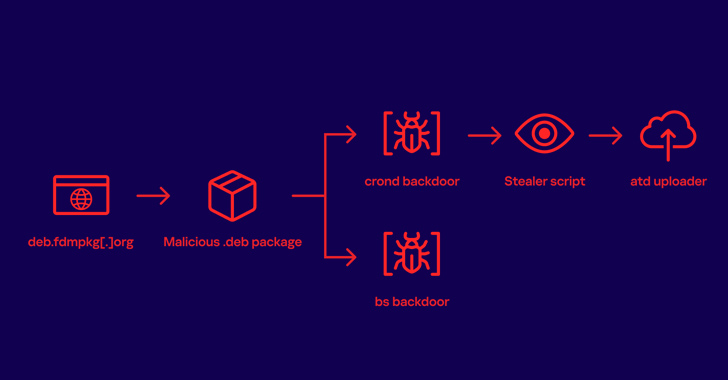
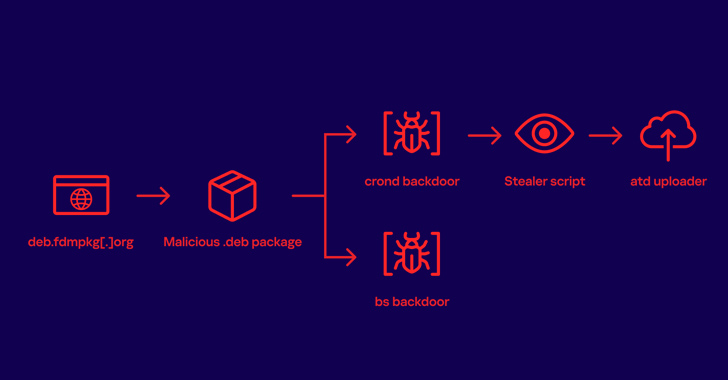
1.3KMalwareFree Download Manager Site Compromised to Distribute Linux Malware to Users for 3+ Years
A download manager site served Linux users malware that stealthily stole passwords and other sensitive information for more than three years as...
-

 760Malware
760MalwareHackers Using Compromised Google Cloud Accounts to Mine Cryptocurrency
Threat actors are exploiting improperly-secured Google Cloud Platform (GCP) instances to download cryptocurrency mining software to the compromised systems as well as...
-

 3.4KMalware
3.4KMalwareMalware Attack Using Google Cloud Computing Platform
Hackers have unleashed a global malware campaign using the Google cloud computing platform via weaponized PDF. Security researchers at the Netskope Threat...
-

 443Malware
443MalwareHackers Using Google Cloud Computing Platform To Deliver Targeted Malware Attacks via Weaponized PDF
Threat actors using Google computing platform (GCP) to deliver the malware through malicious PDF files. The attack targeting governments and financial firms...






