All posts tagged "Hack Android"
-
 4.6KHack Tools
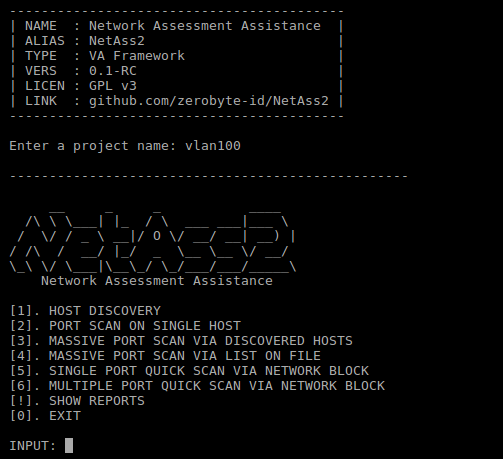
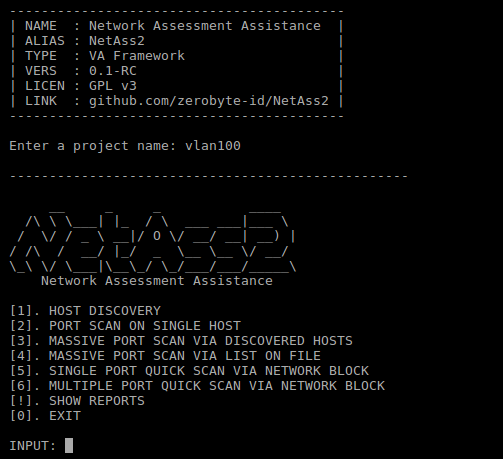
4.6KHack ToolsNetAss2 – Network Assessment Assistance Framework
Easier network scanning with NetAss2 (Network Assessment Assistance Framework). Make it easy for Pentester to do penetration testing on network. Dependencies nmap...
-

 3.1KHack Tools
3.1KHack ToolsRsdl – Subdomain Scan With Ping Method
Subdomain Scan With Ping Method. Flags Value Description –hostname example.com Domain for scan. –output Records the output with the domain name. –list...
-
 1.5KHack Tools
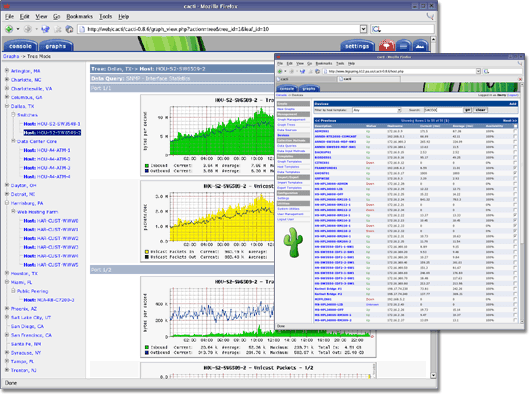
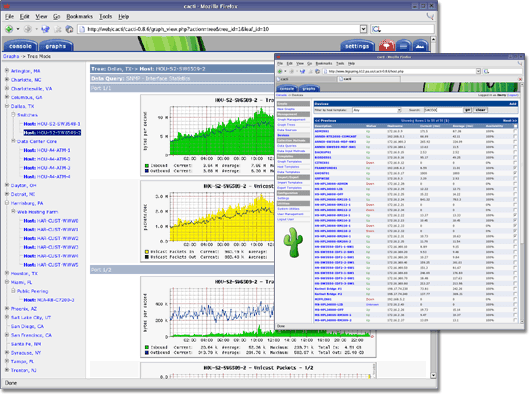
1.5KHack ToolsCacti – Complete Network Graphing Solution
IMPORTANTWhen using source or by downloading the code directly from the repository, it is important to run the database upgrade script if...
-

 929Hack Tools
929Hack ToolsGCPBucketBrute – A Script To Enumerate Google Storage Buckets, Determine What Access You Have To Them, And Determine If They Can Be Privilege Escalated
A script to enumerate Google Storage buckets, determine what access you have to them, and determine if they can be privilege escalated....
-
 3.0KHack Tools
3.0KHack Toolsthreat_note – DPS’ Lightweight Investigation Notebook
threat_note is a web application built by Defense Point Security to allow security researchers the ability to add and retrieve indicators related...
-

 5.0KHack Tools
5.0KHack ToolsAdaudit – Powershell Script To Do Domain Auditing Automation
PowerShell Script to perform a quick AD audit _____ ____ _____ _ _ _| _ | | _ |_ _ _| |_|...
-
 5.5KHack Tools
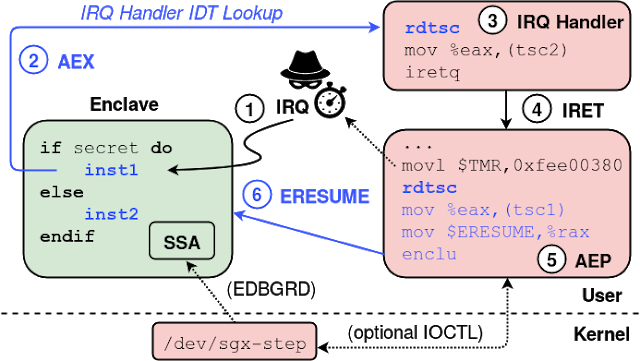
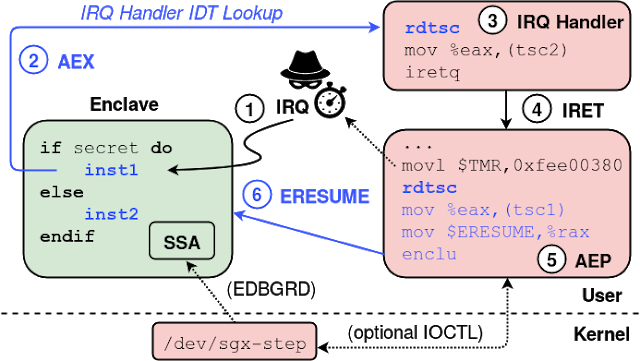
5.5KHack ToolsSgx-Step – A Practical Attack Framework For Precise Enclave Execution Control
SGX-Step is an open-source framework to facilitate side-channel attack research on Intel SGX platforms. SGX-Step consists of an adversarial Linux kernel driver...
-
 2.4KHack Tools
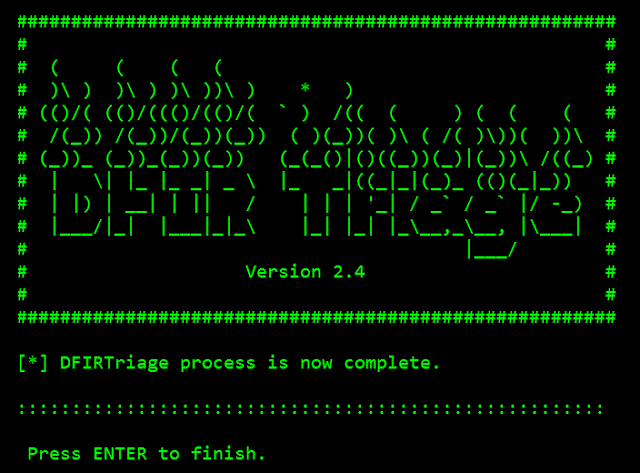
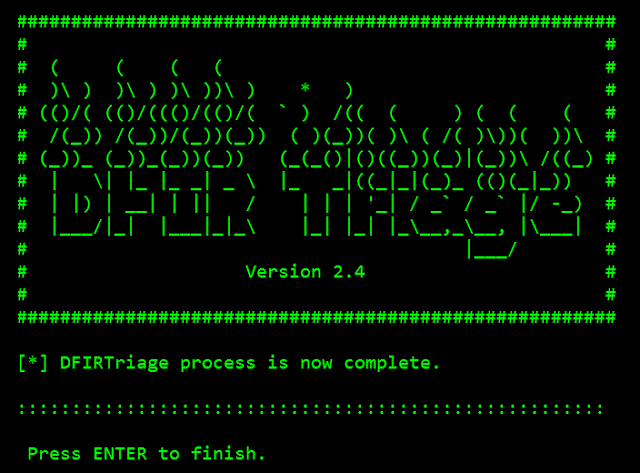
2.4KHack ToolsDFIRtriage – Digital Forensic Acquisition Tool For Windows Based Incident Response
DFIRtriage is a tool intended to provide Incident Responders with rapid host data. Written in Python, the code has been compiled to...
-

 5.3KHack Tools
5.3KHack ToolsVscan – Vulnerability Scanner Tool Using Nmap And Nse Scripts
vulnerability scanner tool is using nmap and nse scripts to find vulnerabilitiesThis tool puts an additional value into vulnerability scanning with nmap....
-
 3.1KHack Tools
3.1KHack ToolsSojobo – A Binary Analysis Framework
Sojobo is an emulator for the B2R2 framework. It was created to easier the analysis of potentially malicious files. It is totally...
-
 1.8KHack Tools
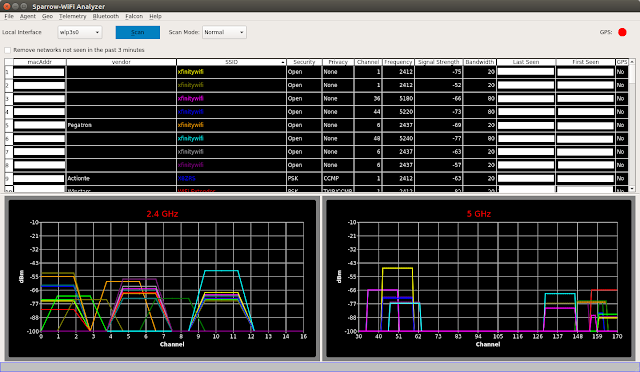
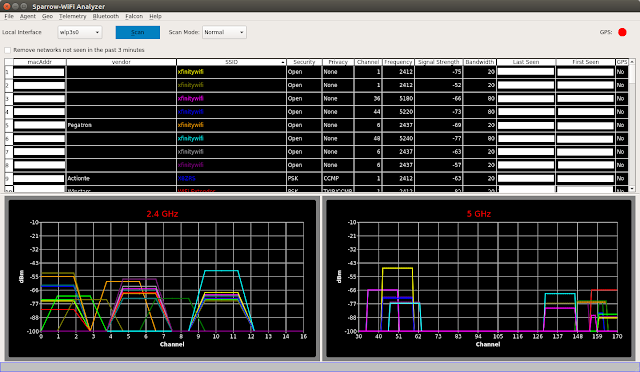
1.8KHack ToolsSparrow-Wifi – Next-Gen GUI-based WiFi And Bluetooth Analyzer For Linux
Sparrow-wifi has been built from the ground up to be the next generation 2.4 GHz and 5 GHz Wifi spectral awareness tool....
-
 3.4KHack Tools
3.4KHack ToolsDonut – Generates X86, X64, Or AMD64+x86 Position-Independent Shellcode That Loads .NET Assemblies, PE Files, And Other Windows Payloads From Memory
Donut generates x86 or x64 shellcode from VBScript, JScript, EXE, DLL (including .NET Assemblies) files. This shellcode can be injected into an...
-
 992Hack Tools
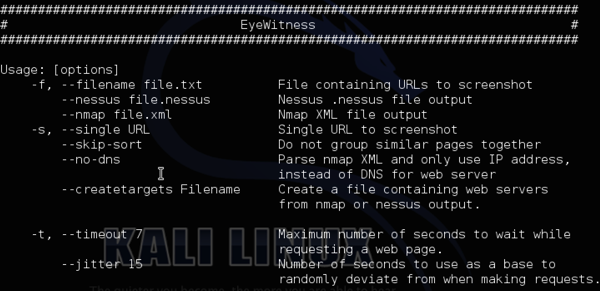
992Hack ToolsEyeWitness – Tool To Take Screenshots Of Websites, Provide Some Server Header Info, And Identify Default Credentials If Possible
EyeWitness is designed to take screenshots of websites provide some server header info, and identify default credentials if known.EyeWitness is designed to...
-
 4.5KHack Tools
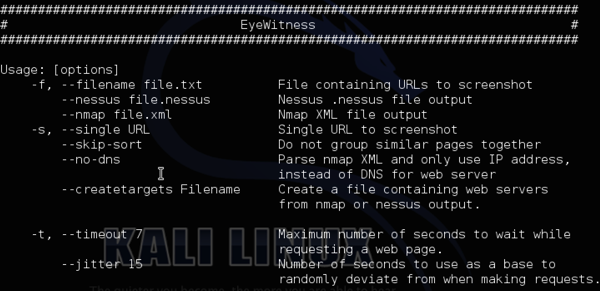
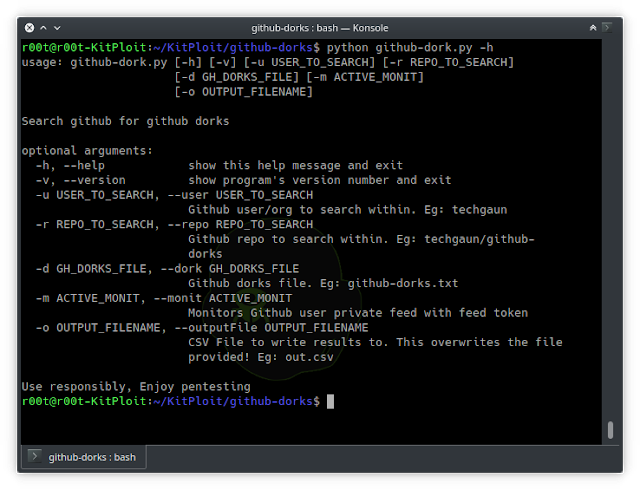
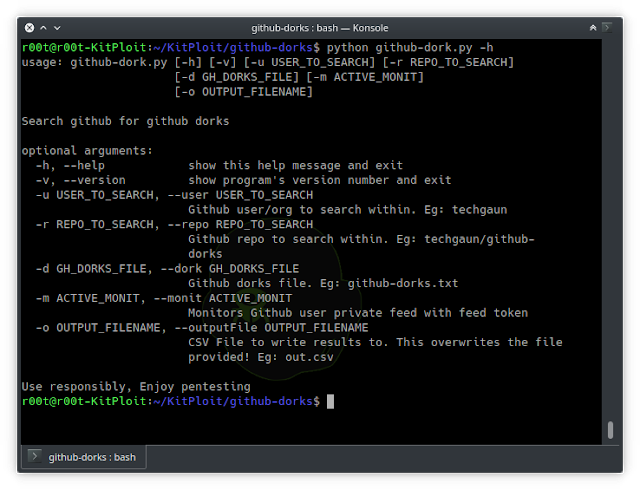
4.5KHack ToolsGithub-Dorks – Collection Of Github Dorks And Helper Tool To Automate The Process Of Checking Dorks
Github search is quite powerful and useful feature and can be used to search sensitive data on the repositories. Collection of github...
-
 4.1KHack Tools
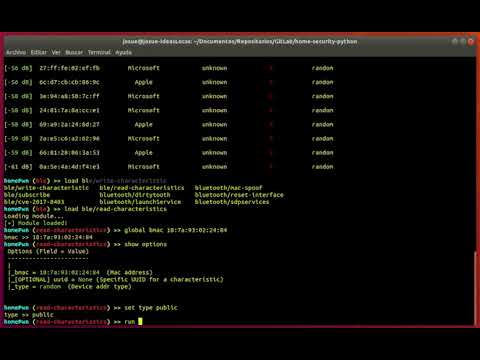
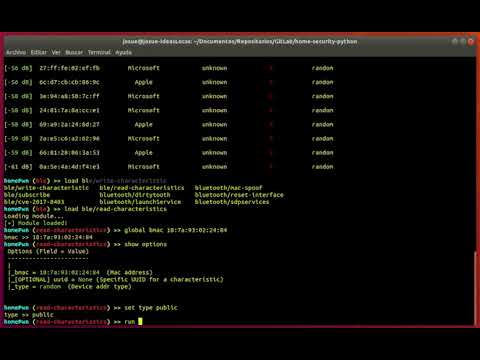
4.1KHack ToolsHomePwn – Swiss Army Knife for Pentesting of IoT Devices
HomePwn is a framework that provides features to audit and pentesting devices that company employees can use in their day-to-day work and...
-

 4.6KHack Tools
4.6KHack ToolsXray – A Tool For Recon, Mapping And OSINT Gathering From Public Networks
XRay is a tool for network OSINT gathering, its goal is to make some of the initial tasks of information gathering and...
-
 221Hack Tools
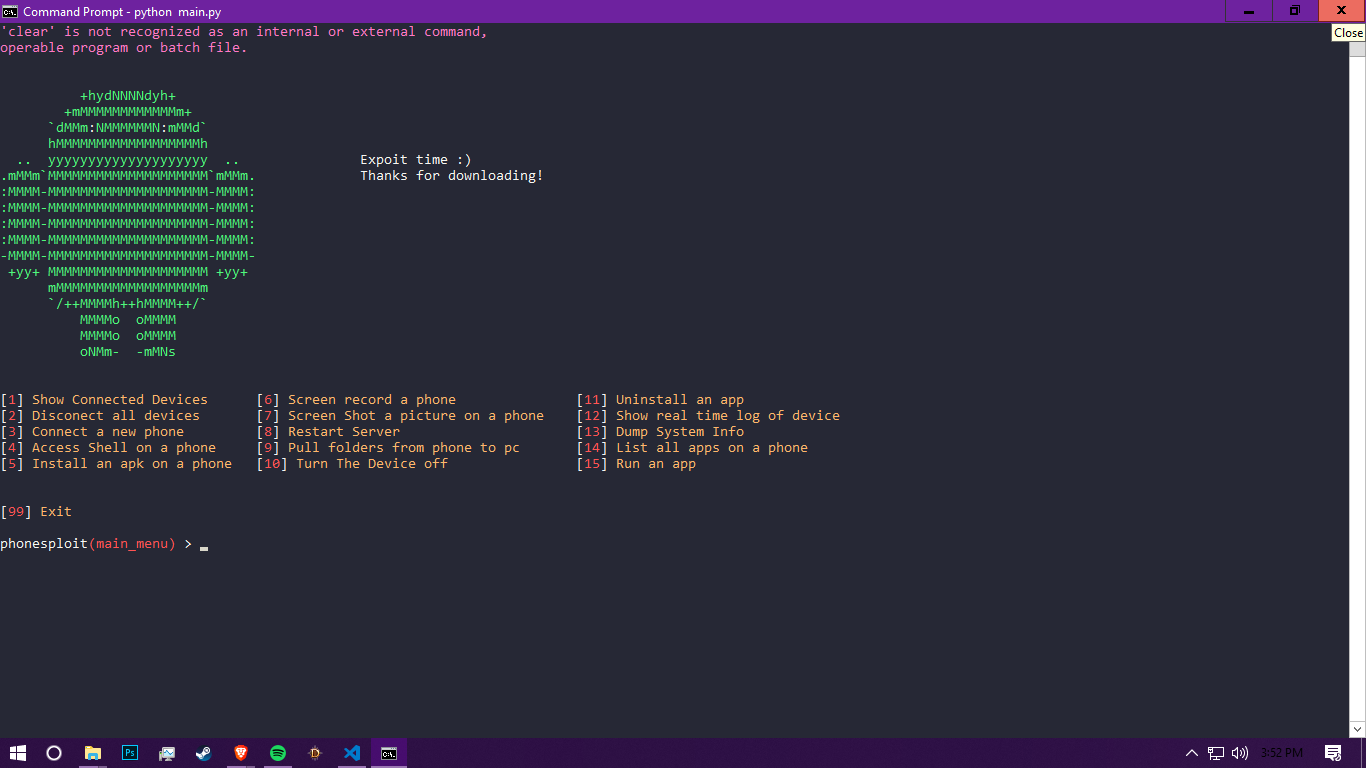
221Hack ToolsPhoneSploit – Using Open Adb Ports We Can Exploit A Devive
Using open Adb ports we can exploit a device you can find open ports here https://www.shodan.io/search?query=android+debug+bridge+product%3A”Android+Debug+Bridge” To find out how to access...
-
 407Data Security
407Data SecurityHack Windows, Android, Mac using TheFatRat (Step by Step tutorial)
Using Metasploit is not an difficult thing anymore. Because there are many resources that are available over the internet. Which tells usage...
-

 328Malware
328MalwareNew “Roaming Mantis” Malware uses DNS Hijacking Attack to Hack Android Smartphones
Newly discovered Malware called “Roaming Mantis” infiltrate the Android smartphones using a technique known as DNS hijacking and steal the sensitive information...






