All posts tagged "Hack The Virtual Memory"
-
 135Vulnerabilities
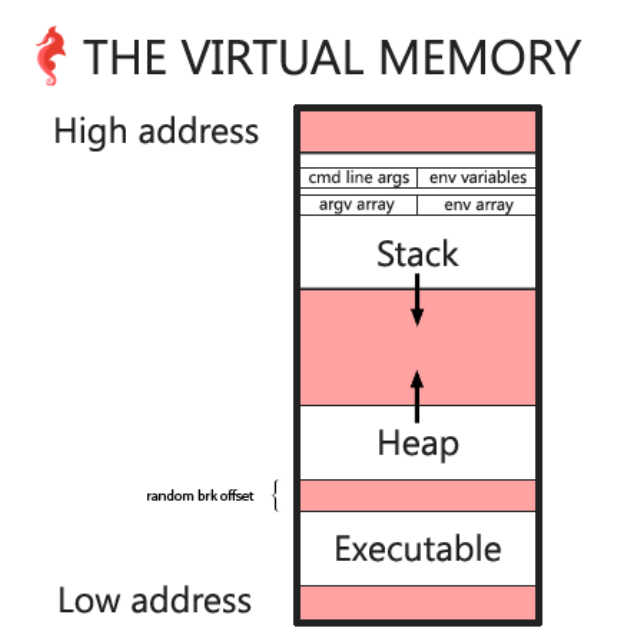
135VulnerabilitiesHack the Virtual Memory: malloc, the heap & the program break
The heap In this chapter we will look at the heap and malloc in order to answer some of the questions we...
-

 138Incidents
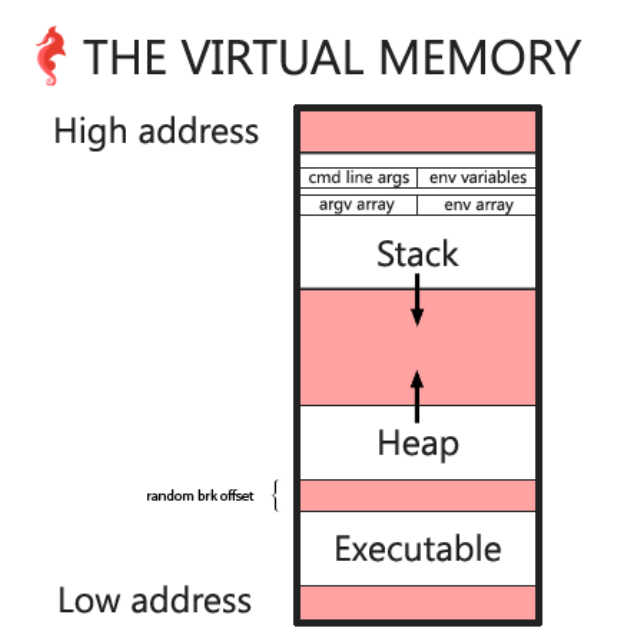
138IncidentsHack The Virtual Memory: Python bytes
For this second chapter, we’ll do almost the same thing as for chapter 0: C strings & /proc, but instead we’ll access...






