All posts tagged "hack"
-
 190Hacked
190HackedLynda.com Hacked, Passwords Of 55,000 Users Leaked
Short Bytes: Online learning company Lynda is the latest victim of hacking attacks. The company has sent precautious emails to its 9.5...
-
 210Hacked
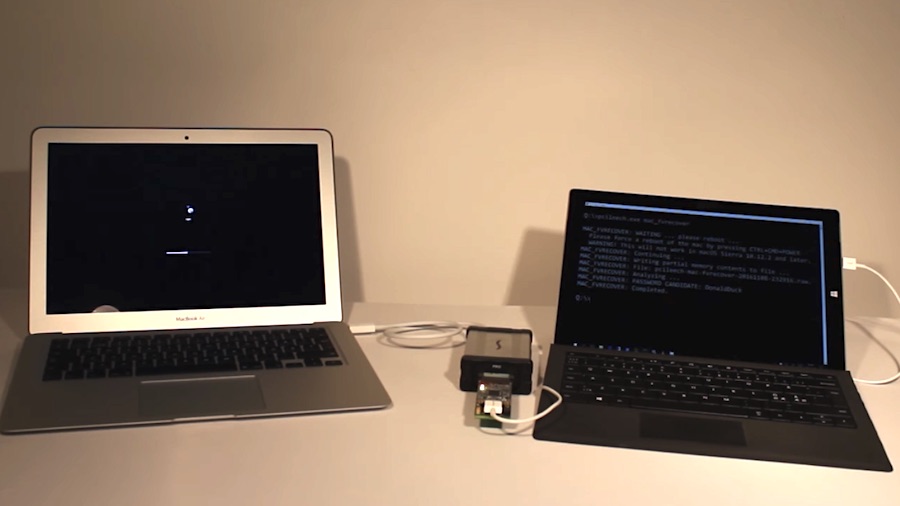
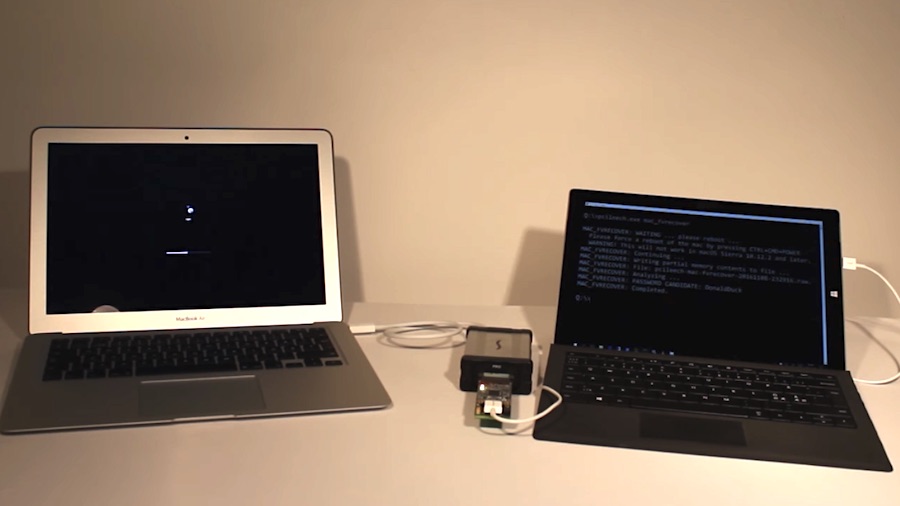
210HackedHere’s How Your Sleeping Mac Can Be Hacked In 30 Seconds
Short Bytes: A security researcher has exploited a flaw in macOS and used his $300 device and open source software to hack a...
-

 230Cyber Attack
230Cyber AttackHacker Launched A DDOS Competition to lay down Political Websites
A Turkish hacker who is known on-line as Mehmet has released a DDoS opposition that invitations members to take down political websites...
-

 190News
190News10 Search Engines Where You Can Surf Anonymously
EhPrivate surfing using the non-public or incognito modes furnished in your browser does no longer come up with the level of privacy...
-

 113News
113NewsLinux Based Red Star OS of North Korea can be Hacked by just a Link
North Korea’s personal homegrown PC operating device redstar, it’s presupposed to be completely hacker proof and extra comfortable than foreign OS, like...
-

 181News
181NewsFBI gets Expanded Power to Hack any Computer in the World through Rule 41
Hacking a couple of computer systems the world over simply were given less difficult for america intelligence and law enforcement businesses from...
-

 303Data Security
303Data SecurityWindows 10 Upgrade Vulnerability Makes Any PC Super Easy to Hack
Security expert discovers flaw in Windows 10 in-place upgrade system that gives hackers admin rights. Getting administrator privileges on a Windows 10...
-

 96Incidents
96IncidentsUS Navy Waits Till Thanksgiving Eve to Disclose Hack of 130,000 Sailors
On Oct. 27 of this year, a contractor told the US Navy that one of its employee’s laptops was “compromised,” resulting in...
-

 148Incidents
148IncidentsThree to appear in court over TalkTalk hack
Part of broader investigation into alleged data theft. Three men are due to appear at the Old Bailey charged with various offences...
-
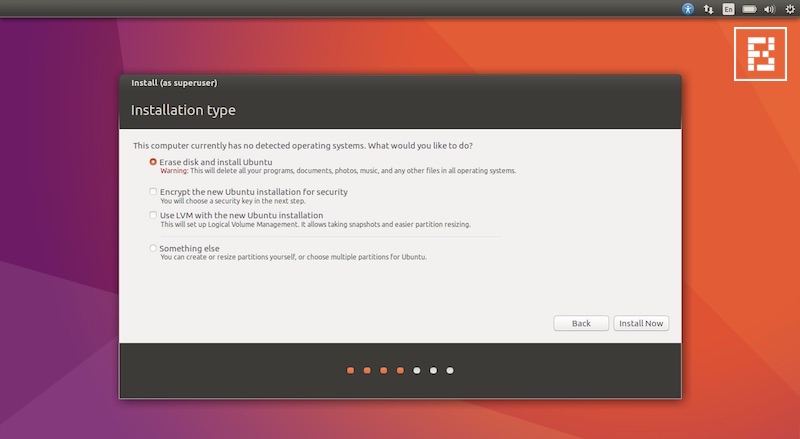
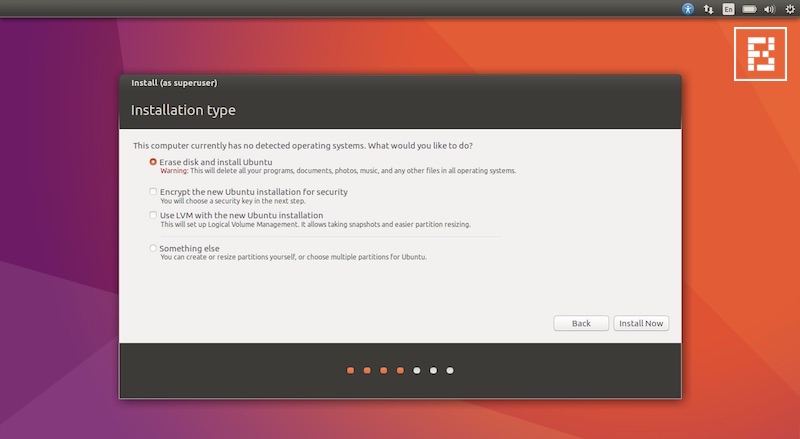 336Hacked
336HackedYou Can Own A Linux System By Holding Down Enter Key For 70 Seconds, Here’s The Fix
Short Bytes: Due to a flaw in the Cryptsetup encryption utility, a hacker can get access to the root shell by holding down the Enter key for...
-

 208Hacked
208HackedHow Your Own Fingers Can Leak Passwords By “Talking” To Wi-Fi Signal
Short Bytes: A group of researchers has revealed a new method to steal sensitive information from a user’s computer or phone. Named WindTalker,...
-
 184Data Security
184Data SecurityDefusing The Virus – Hack The Hacker
VIRUS a piece of malicious coded file can turn your life into hell , Worlds first PC virus was created in Pakistan...
-

 95Data Security
95Data SecurityHacker Discovered A Vulnerability In Gmail That Allows Anyone To Hack Any Email Account
Introduction Gmail allows its users from all over the world to use multiple email addresses and associate or link them with Gmail also...
-

 226How To
226How ToAirtel Free Internet Trick 2016 Released
Airtel free internet trick by simply using VPN First of all before going to the trick. Let’s take some knowledge about VPN...
-
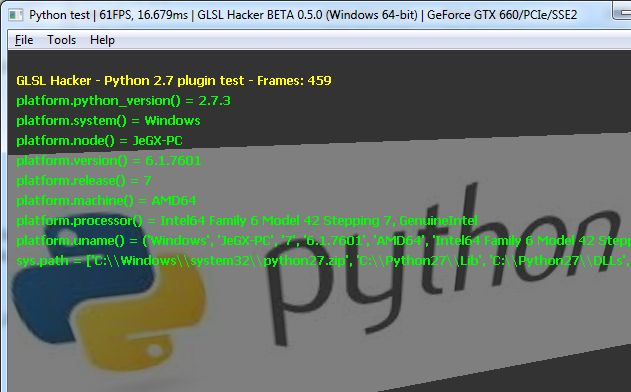
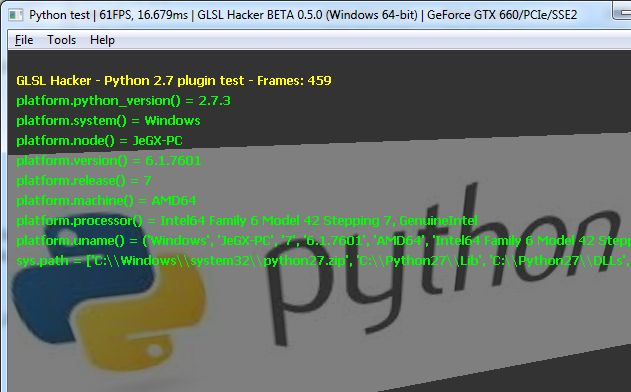 82Data Security
82Data SecurityHack This: An Overdue Python Primer
In writing the most recent Hack This (“Scrape the Web with Beautiful Soup”) I again found myself trapped between the competing causes...
-
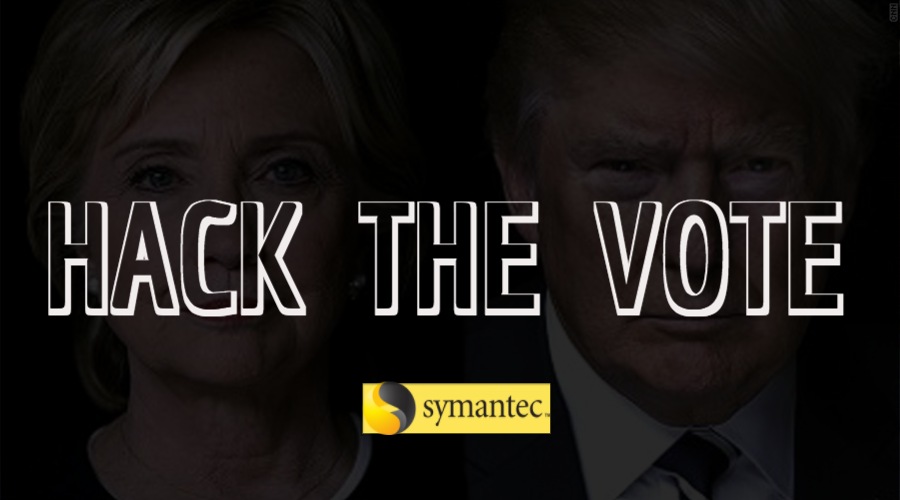
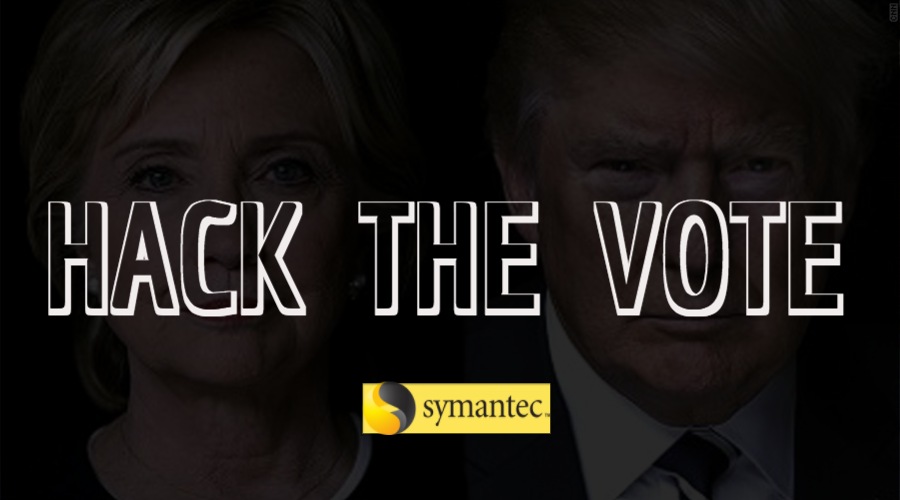 271Hacked
271HackedSymantec Shows How A $15 Device Can Be Used To Hack The U.S. Presidential Election
Short Bytes: Can some group of notorious hackers influence the U.S. Presidential Election? To study the same, the cybersecurity firm Symantec simulated the election...
-
 276Hacked
276HackedHackers Successfully Attacked A Nuclear Power Plant — Is Anything Safe Anymore?
Short Bytes: The International Atomic Energy Agency Director, Yukiya Amano, has revealed that a nuclear power plant was attacked by the hackers...
-

 214Data Security
214Data SecurityHow to hack a security CCTV camera
Watch how simple it really is to hack a security camera. CCTV cameras are thought to be the final frontier in protecting physical...
-
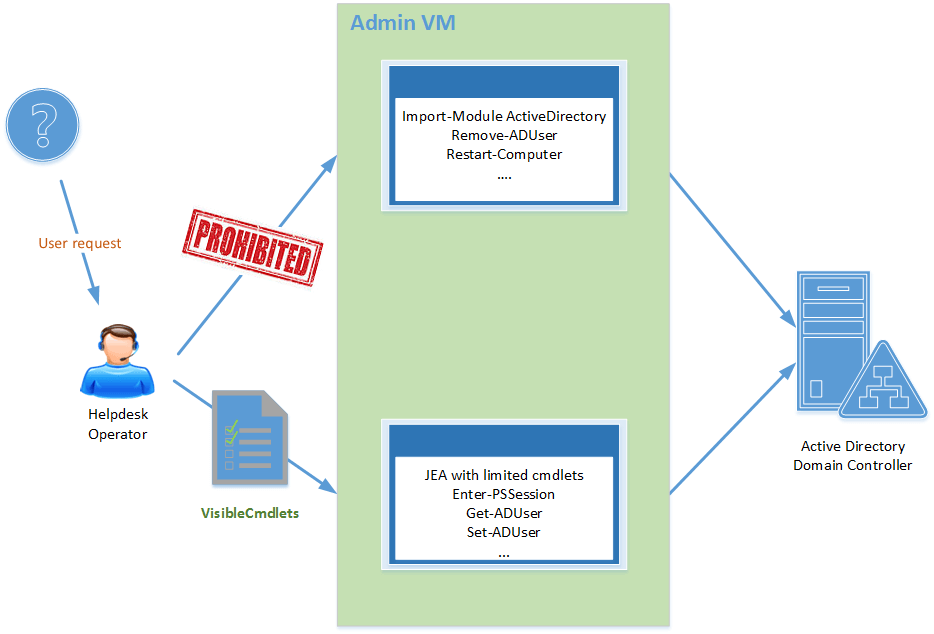
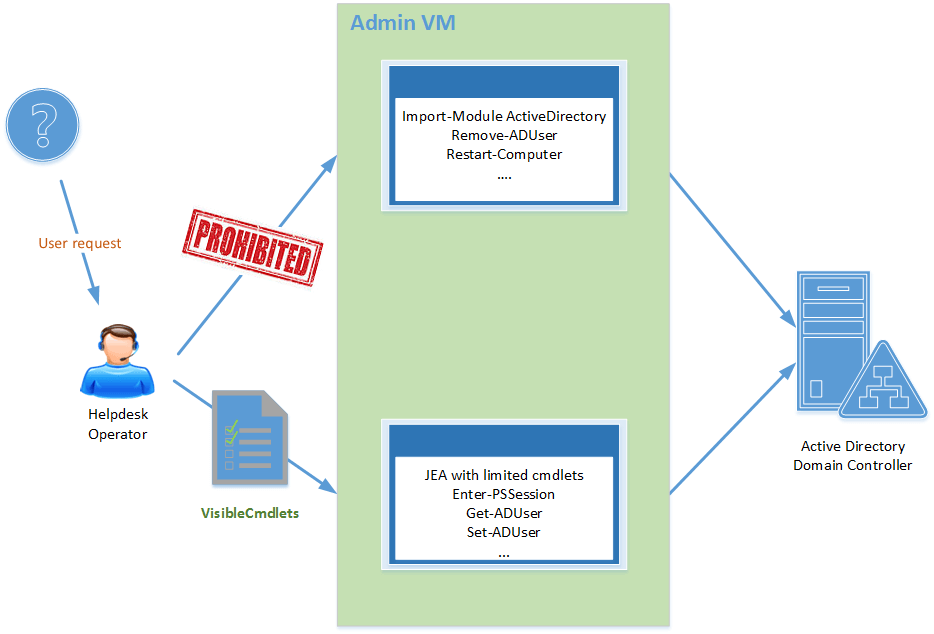 101Incidents
101IncidentsBreaking the Microsoft JEA technology to hack a system
The security researcher Matt Weeks discovered a way to abuse the Microsoft Just Enough Administration (JEA) technology to escalate user profiles. Just...
-

 107Incidents
107IncidentsHACK CRASHES LINUX DISTROS WITH 48 CHARACTERS OF CODE
With just a mere 48 characters of code, Linux admin and SSLMate founder Andrew Ayer has figured out how to crash major Linux distributions...
-

 83Data Security
83Data SecuritySpace Wars Will Be Fought With Hacks, Not Missiles
On Monday morning, a number of professionals in the aerospace industry received a rather mundane email containing a PDF ostensibly about the...






