All posts tagged "hacker"
-
 428News
428NewsHacker Adrian Lamo who tipped off FBI about Chelsea Manning dies at 37
Adrian Lamo, a hacker who was once in the news for informing the FBI about Chelsea Manning, the WikiLeaks whistleblower, has passed away...
-
 472Video Tutorials
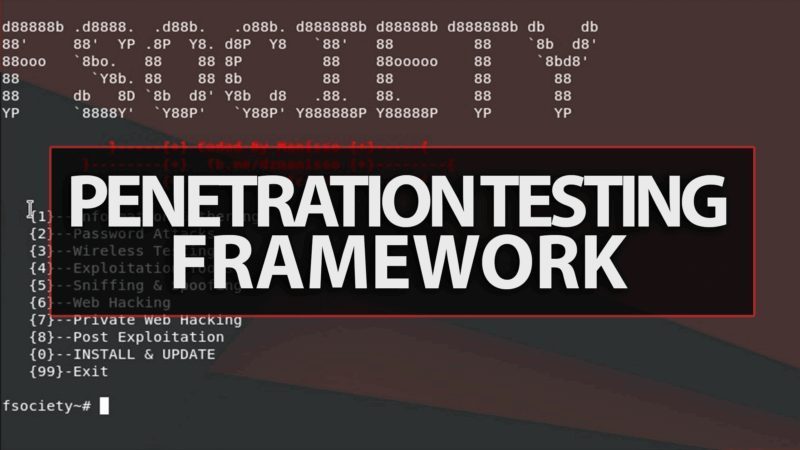
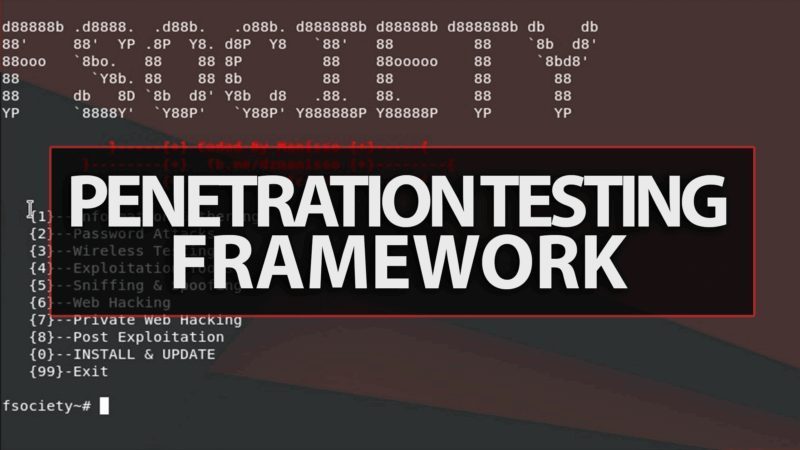
472Video TutorialsFsociety Hacking Tools Pack – A Penetration Testing Framework – Kali Linux 2017.3
A Penetration Testing Framework, you will have every script that a hacker needs Fsociety: https://github.com/Manisso/fsociety Menu Information Gathering Password Attacks Wireless Testing...
-
 242Articles
242ArticlesCo-Founder of Lizard Squad And PoodleCorp Caught For Operating ‘Hacker For Hire’ Services
Zachary Buchta, a 20 year old hacker, who is the co-founder of famous hacking groups called Lizard Squad And Poodlecorp was recently...
-

 90Articles
90ArticlesHacker Proves It Is Possible To Hack Gift Cards
Christmas is the time of the year where gift cards are on the rise. As per The National Retail Federation, people in...
-

 236Lists
236Lists10 Best Hacking Movies You Need To Watch In 2018
In this age of smartphones and computers, the electronic devices have become our true companions. For technology enthusiasts and geeks, this is...
-
 131Information Gathering
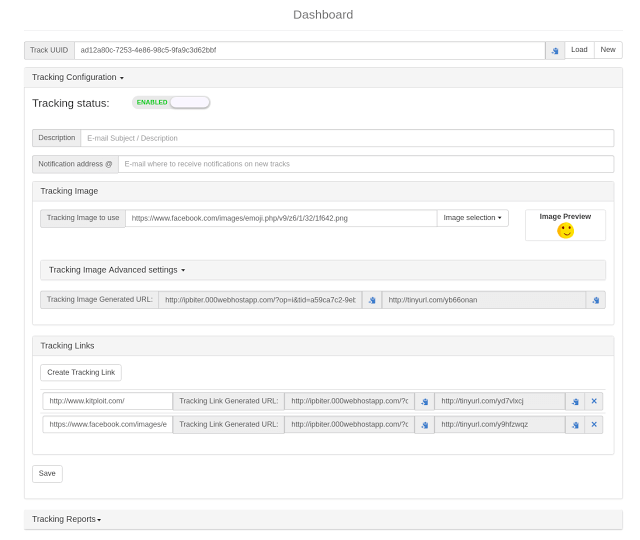
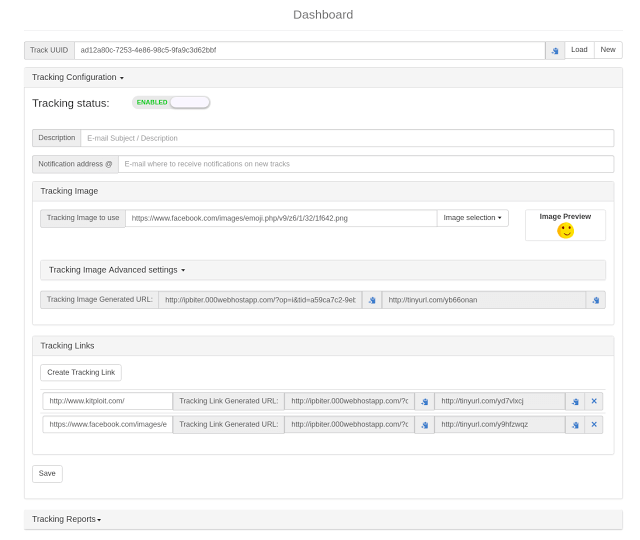
131Information GatheringIP-Biter – The Hacker-friendly E-Mail Tracking Framework
IP-Biter is an open source, easy to deploy, tracking framework that generate high configurables and uniques tracking images and links to embed...
-

 305Cyber Crime
305Cyber CrimeHire a Hacker is the latest in Cyber Crime Service
Guess, what it must be when you see a guy a user on the dark web claims that he can track any...
-
 132Incidents
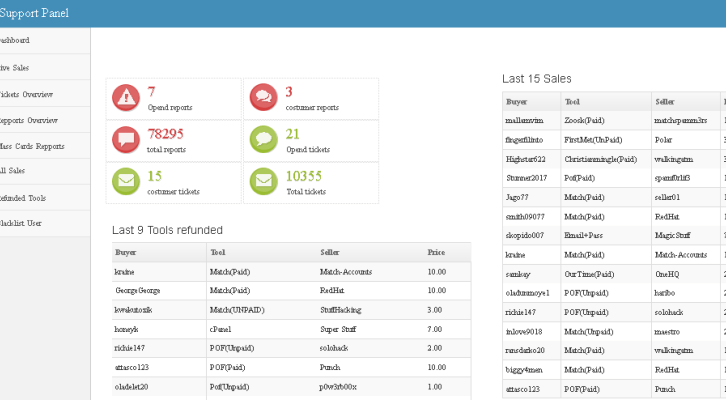
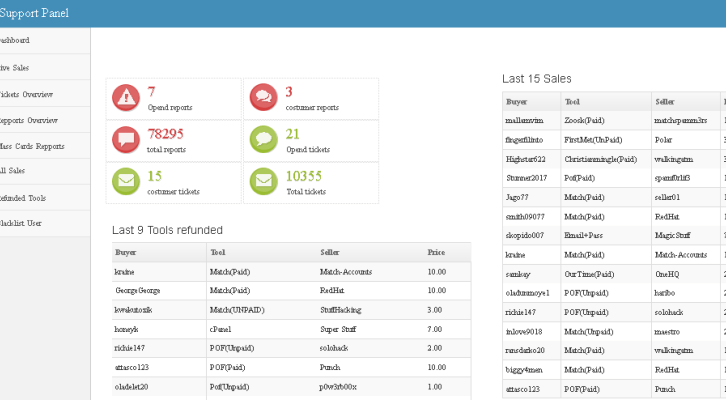
132IncidentsBasetools underground hacking forum breached, hacker demands $50K ransom
Basetools underground hacking forum was breached, hackers demand a $50K ransom to avoid sharing stolen data, including admin identity, with law enforcement....
-

 390How To
390How To40 Powerful Hacking Tools To Become A Powerful Hacker
Here are the next 40 Powerful hacking tools that will make you a powerful hacker. Creating packages to exploit Firewall weaknesses hping...
-
 173News
173NewsApache Tomcat Patched Most Of The Remote Code Execution Flaw
The Apache Tomcat team recently patched several security vulnerabilities in Apache Tomcat, one of which could allow an unauthorized attacker to execute...
-

 230How To
230How ToUnofficial Anonymous Hacker Guide For Security Enthusiasts
CHAPTER 1: INTRODUCTION TO HACKER GUIDE | HACKER GUIDE 1.1 Hacking 1.2 Hacker 1.3 Classifications of Hacker 1.4 Famous Hackers of All...
-
 316News
316NewsIn Upcoming Months UK Police Force Will Be Learning Hacktivism
Twenty years ago, it was not necessary for the authorities to have the skills of piracy. In fact, there were (and still...
-

 79Hacked
79HackedRussian Computer Programmer Suspected In US Election Hacking Arrested
Short Bytes: A Russian programmer named Pyotr Levashov has been arrested in Spain. The arrest was made based on an international warrant issued by...
-
 123Vulnerabilities
123VulnerabilitiesAnonymous Hacker Who Exposed Steubenville Rape Case Gets Two Years in Prison
One of the Anonymous hackers who exposed the Steubenville High School rape case in 2012, was sentenced yesterday to two years in...
-
 195Vulnerabilities
195VulnerabilitiesDOCKER PATCHES CONTAINER ESCAPE VULNERABILITY
Docker has patched a privilege escalation vulnerability (CVE-2016-9962) that could lead to container escapes, allowing a hacker to affect operations of a...
-

 88Vulnerabilities
88VulnerabilitiesHacker Steals 900 GB of Cellebrite Data
The hackers have been hacked. Motherboard has obtained 900 GB of data related to Cellebrite, one of the most popular companies in...
-
 294Geek
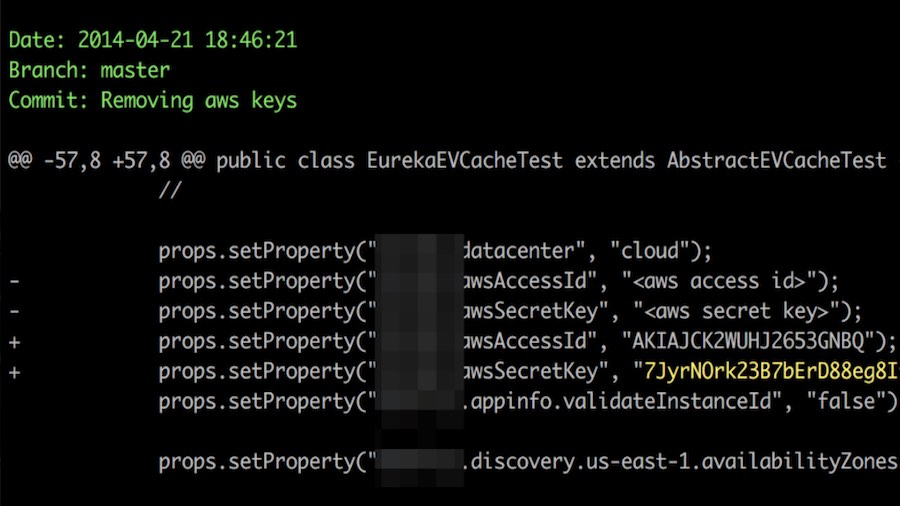
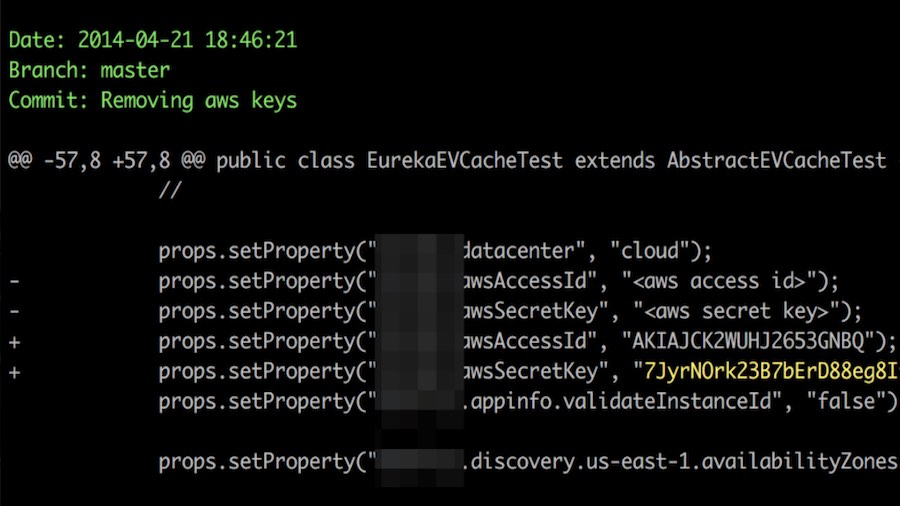
294GeekHacker Publishes Open Source Tool For Finding Secret Keys On GitHub
Short Bytes: A hacker has published an open source tool for helping administrators strengthen the security of their networks. Dubbed TruffleHog, this tool...
-

 250Lists
250Lists10 Highest Paying Jobs That Don’t Want Your College Degree
Short Bytes: It’s the 21st century, you can find a number of jobs that don’t require any professional degree. These career streams include...
-

 170Incidents
170IncidentsHacker claims army of 3.2M home routers seized via malicious firmware update
One of the hackers who amassed a new massive army of zombie internet-connected devices that can launch disruptive cyberattacks—even by mistake—now claims...
-

 111News
111NewsLinux Based Red Star OS of North Korea can be Hacked by just a Link
North Korea’s personal homegrown PC operating device redstar, it’s presupposed to be completely hacker proof and extra comfortable than foreign OS, like...
-
 88Incidents
88IncidentsPowerful Greek Army Hacker Breaches High Commission Websites in India
They promised they’d fix the issues and they didn’t, hacker says, so this latest breach shows better security is needed. India is...






