All posts tagged "hacking news"
-

 4.7KCyber Attack
4.7KCyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
Threat actors have been exploiting the newly disclosed zero-day flaw in Palo Alto Networks PAN-OS software dating back to March 26, 2024,...
-
 3.4KVulnerabilities
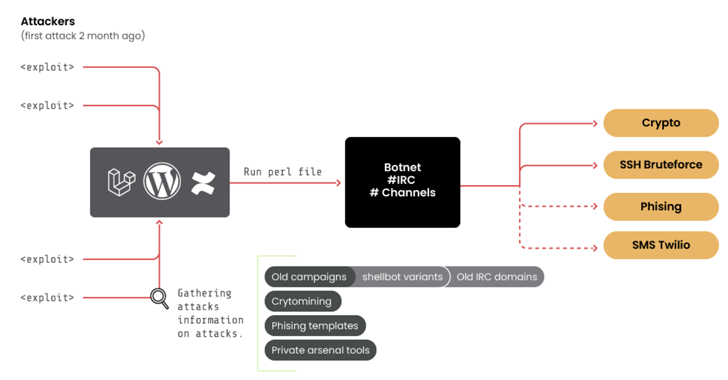
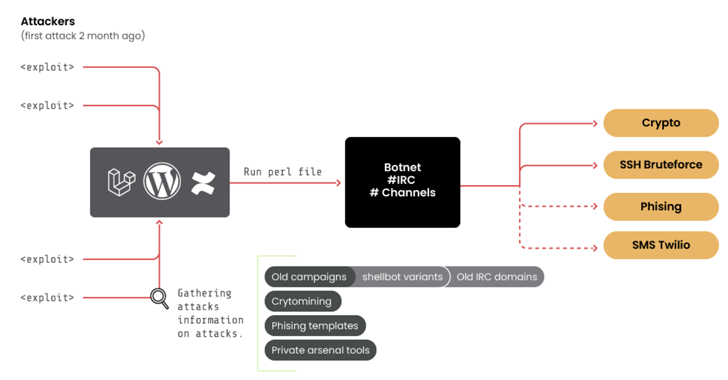
3.4KVulnerabilities10-Year-Old ‘RUBYCARP’ Romanian Hacker Group Surfaces with Botnet
A threat group of suspected Romanian origin called RUBYCARP has been observed maintaining a long-running botnet for carrying out crypto mining, distributed...
-
 3.9KMalware
3.9KMalwareNew APT Group ‘Lotus Bane’ Behind Recent Attacks on Vietnam’s Financial Entities
A financial entity in Vietnam was the target of a previously undocumented threat actor called Lotus Bane as part of a cyber...
-

 784Malware
784MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-

 4.1KMalware
4.1KMalwareAnatsa Android Trojan Bypasses Google Play Security, Expands Reach to New Countries
The Android banking trojan known as Anatsa has expanded its focus to include Slovakia, Slovenia, and Czechia as part of a new...
-

 2.8KMalware
2.8KMalwareMoqHao Android Malware Evolves with Auto-Execution Capability
Threat hunters have identified a new variant of Android malware called MoqHao that automatically executes on infected devices without requiring any user...
-

 3.5KData Breach
3.5KData BreachHands-On Review: SASE-based XDR from Cato Networks
Companies are engaged in a seemingly endless cat-and-mouse game when it comes to cybersecurity and cyber threats. As organizations put up one...
-

 2.1KMalware
2.1KMalwarePegasus Spyware Targeted iPhones of Journalists and Activists in Jordan
The iPhones belonging to nearly three dozen journalists, activists, human rights lawyers, and civil society members in Jordan have been targeted with...
-

 2.5KCyber Attack
2.5KCyber AttackAnyDesk Hacked: Popular Remote Desktop Software Mandates Password Reset
Remote desktop software maker AnyDesk disclosed on Friday that it suffered a cyber attack that led to a compromise of its production...
-

 406Malware
406MalwareINTERPOL Arrests 31 in Global Operation, Identifies 1,900+ Ransomware-Linked IPs
An INTERPOL-led collaborative operation targeting phishing, banking malware, and ransomware attacks has led to the identification of 1,300 suspicious IP addresses and...
-
 3.7KMalware
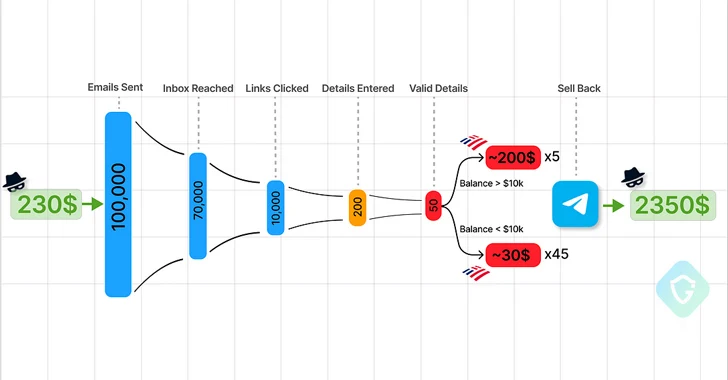
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 1.0KCyber Attack
1.0KCyber AttackMicrosoft Warns of Widening APT29 Espionage Attacks Targeting Global Orgs
Microsoft on Thursday said the Russian state-sponsored threat actors responsible for a cyber attack on its systems in late November 2023 have...
-

 2.9KMalware
2.9KMalwareKasseika Ransomware Using BYOVD Trick to Disarm Security Pre-Encryption
The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to disarm...
-
 2.8KMalware
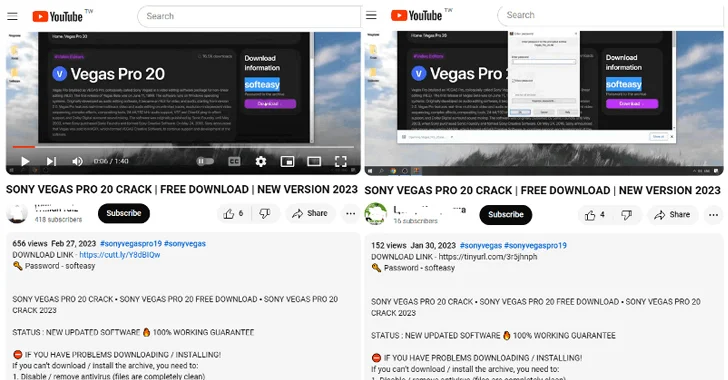
2.8KMalwareBeware! YouTube Videos Promoting Cracked Software Distribute Lumma Stealer
Threat actors are resorting to YouTube videos featuring content related to cracked software in order to entice users into downloading an information...
-

 4.8KCyber Attack
4.8KCyber AttackIranian Hackers Exploit PLCs in Attack on Water Authority in U.S.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) revealed that it’s responding to a cyber attack that involved the active exploitation of...
-

 5.0KCyber Attack
5.0KCyber AttackStealthy Kamran Spyware Targeting Urdu-speaking Users in Gilgit-Baltistan
Urdu-speaking readers of a regional news website that caters to the Gilgit-Baltistan region have likely emerged as a target of a watering...
-
 4.5KMalware
4.5KMalwareResearchers Find 34 Windows Drivers Vulnerable to Full Device Takeover
As many as 34 unique vulnerable Windows Driver Model (WDM) and Windows Driver Frameworks (WDF) drivers could be exploited by non-privileged threat...
-

 1.9KCyber Attack
1.9KCyber AttackAlert: F5 Warns of Active Attacks Exploiting BIG-IP Vulnerability
F5 is warning of active abuse of a critical security flaw in BIG-IP less than a week after its public disclosure, resulting...
-
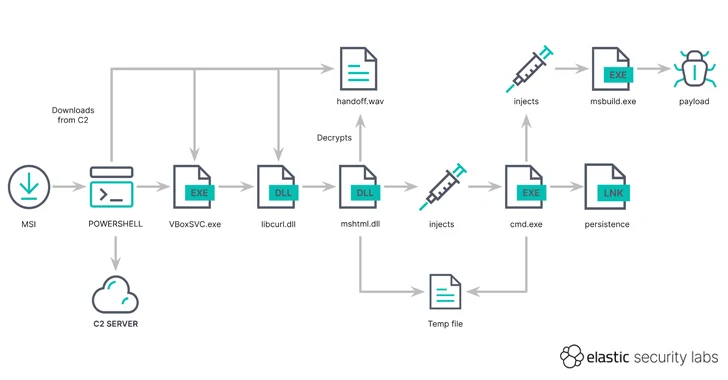
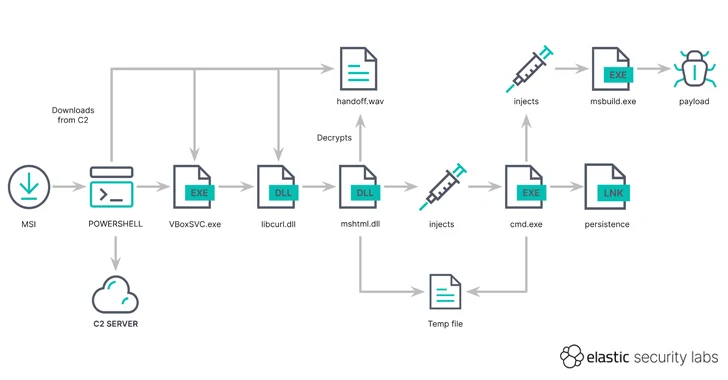 937Cyber Attack
937Cyber AttackHackers Using MSIX App Packages to Infect Windows PCs with GHOSTPULSE Malware
A new cyber attack campaign has been observed using spurious MSIX Windows app package files for popular software such as Google Chrome,...
-
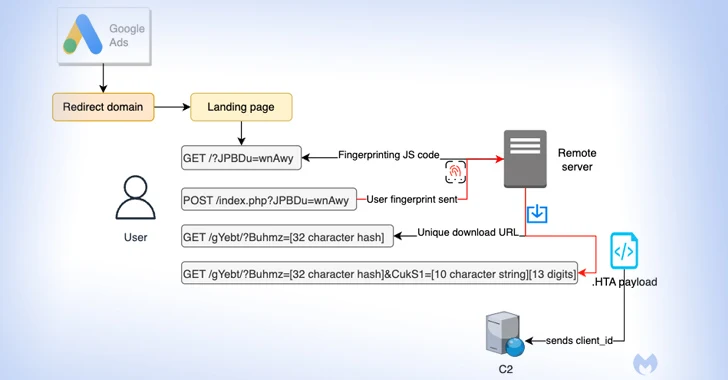
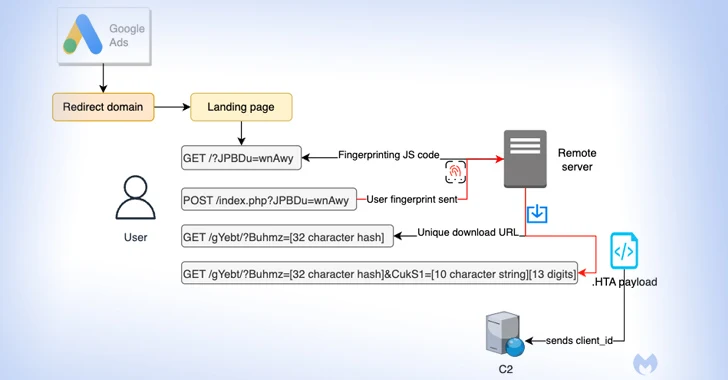 596Cyber Attack
596Cyber AttackMalvertisers Using Google Ads to Target Users Searching for Popular Software
Details have emerged about a malvertising campaign that leverages Google Ads to direct users searching for popular software to fictitious landing pages...
-
 4.9KCyber Attack
4.9KCyber AttackExelaStealer: A New Low-Cost Cybercrime Weapon Emerges
A new information stealer named ExelaStealer has become the latest entrant to an already crowded landscape filled with various off-the-shelf malware designed...






