All posts tagged "hacking news"
-

 400Malware
400MalwareBlind Eagle Cyber Espionage Group Strikes Again: New Attack Chain Uncovered
The cyber espionage actor tracked as Blind Eagle has been linked to a new multi-stage attack chain that leads to the deployment...
-

 4.8KCyber Attack
4.8KCyber AttackPakistani Hackers Use Linux Malware Poseidon to Target Indian Government Agencies
The Pakistan-based advanced persistent threat (APT) actor known as Transparent Tribe used a two-factor authentication (2FA) tool used by Indian government agencies...
-

 768Cyber Attack
768Cyber AttackU.S. and U.K. Warn of Russian Hackers Exploiting Cisco Router Flaws for Espionage
U.K. and U.S. cybersecurity and intelligence agencies have warned of Russian nation-state actors exploiting now-patched flaws in networking equipment from Cisco to...
-

 1.2KCyber Attack
1.2KCyber AttackIranian Government-Backed Hackers Targeting U.S. Energy and Transit Systems
An Iranian government-backed actor known as Mint Sandstorm has been linked to attacks aimed at critical infrastructure in the U.S. between late...
-
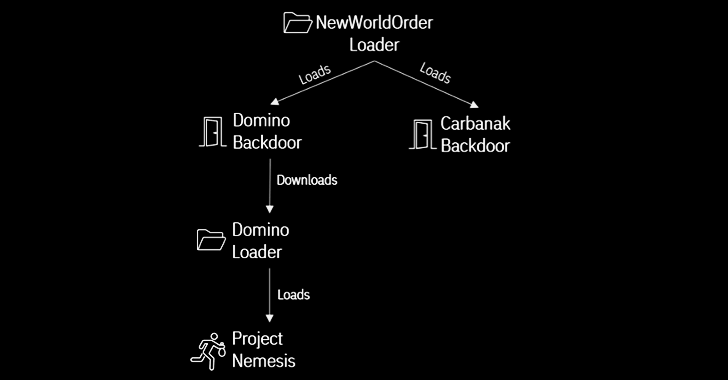
 2.6KMalware
2.6KMalwareFIN7 and Ex-Conti Cybercrime Gangs Join Forces in Domino Malware Attacks
A new strain of malware developed by threat actors likely affiliated with the FIN7 cybercrime group has been put to use by...
-
 645Malware
645MalwareNew Zaraza Bot Credential-Stealer Sold on Telegram Targeting 38 Web Browsers
A novel credential-stealing malware called Zaraza bot is being offered for sale on Telegram while also using the popular messaging service as...
-

 573Cyber Attack
573Cyber AttackSevere Android and Novi Survey Vulnerabilities Under Active Exploitation
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence...
-
 4.5KMalware
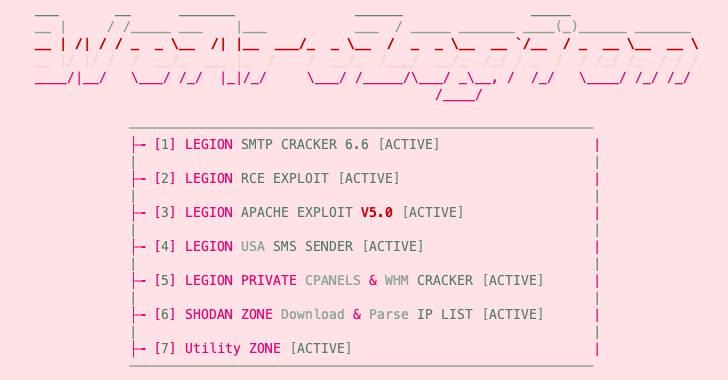
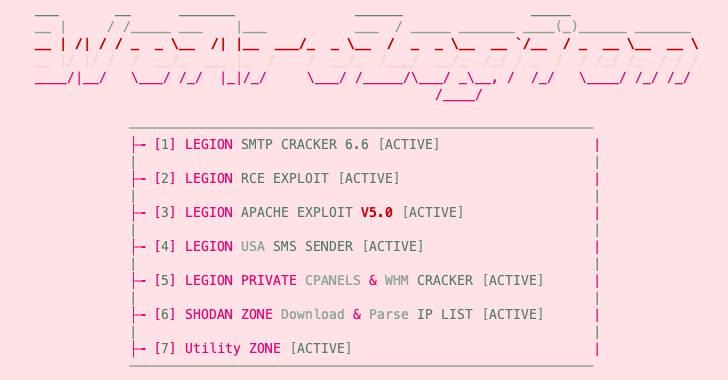
4.5KMalwareNew Python-Based “Legion” Hacking Tool Emerges on Telegram
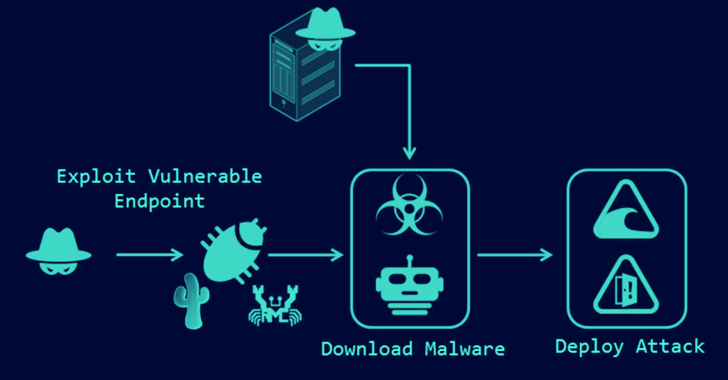
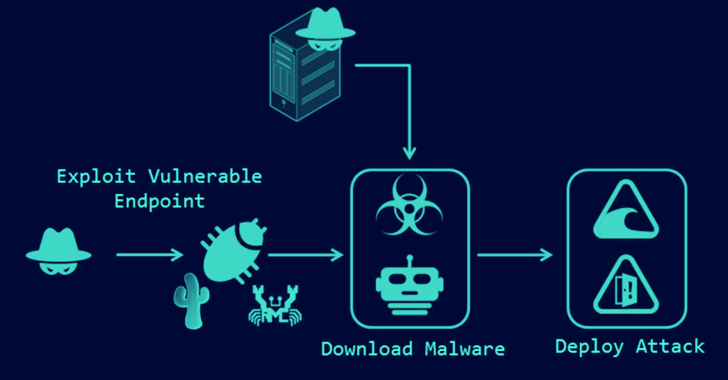
An emerging Python-based credential harvester and a hacking tool named Legion is being marketed via Telegram as a way for threat actors...
-
 4.6KCyber Attack
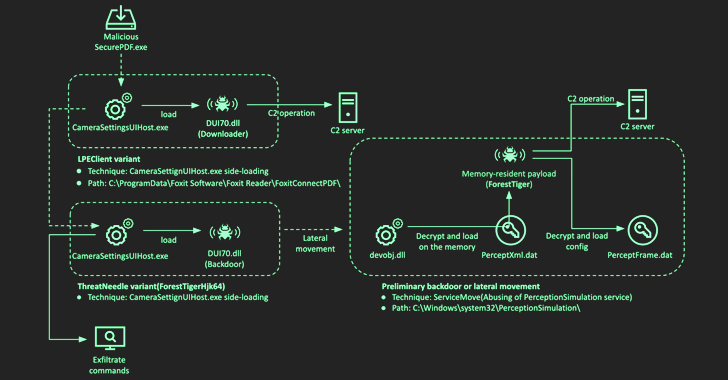
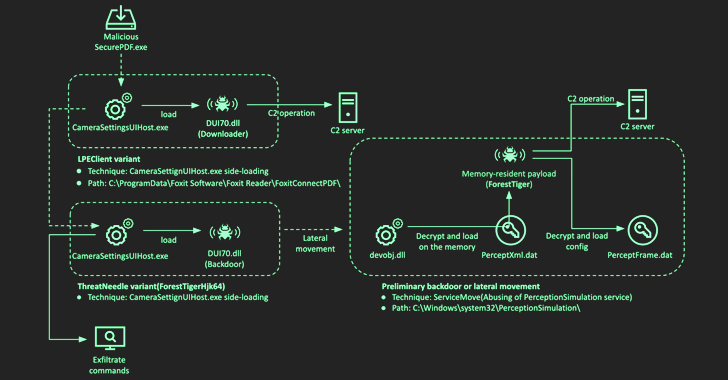
4.6KCyber AttackLazarus Hacker Group Evolves Tactics, Tools, and Targets in DeathNote Campaign
The North Korean threat actor known as the Lazarus Group has been observed shifting its focus and rapidly evolving its tools and...
-

 455Cyber Attack
455Cyber AttackUrgent: Microsoft Issues Patches for 97 Flaws, Including Active Ransomware Exploit
It’s the second Tuesday of the month, and Microsoft has released another set of security updates to fix a total of 97...
-

 1.4KMalware
1.4KMalwareCybercriminals Turn to Android Loaders on Dark Web to Evade Google Play Security
Malicious loader programs capable of trojanizing Android applications are being traded on the criminal underground for up to $20,000 as a way...
-
 1.9KMalware
1.9KMalwareEstonian National Charged in U.S. for Acquiring Electronics and Metasploit Pro for Russian Military
An Estonian national has been charged in the U.S. for purchasing U.S.-made electronics on behalf of the Russian government and military. The...
-

 3.9KMalware
3.9KMalwareCISA Warns of 5 Actively Exploited Security Flaws: Urgent Action Required
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added five security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing...
-

 348Malware
348MalwareTaiwanese PC Company MSI Falls Victim to Ransomware Attack
Taiwanese PC company MSI (short for Micro-Star International) officially confirmed it was the victim of a cyber attack on its systems. The...
-

 5.1KCyber Attack
5.1KCyber AttackCryptoClippy: New Clipper Malware Targeting Portuguese Cryptocurrency Users
Portuguese users are being targeted by a new malware codenamed CryptoClippy that’s capable of stealing cryptocurrency as part of a malvertising campaign....
-
 3.6KMalware
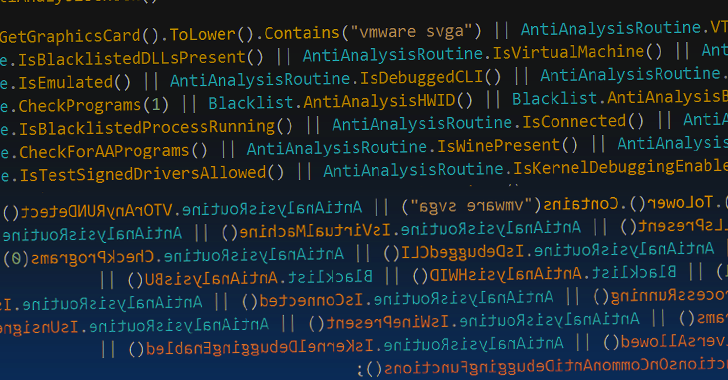
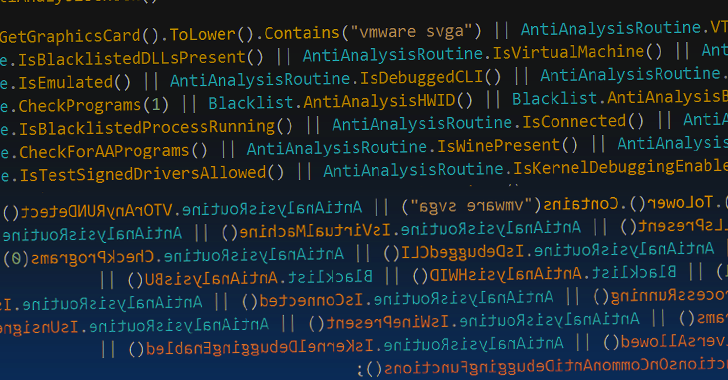
3.6KMalwareTyphon Reborn Stealer Malware Resurfaces with Advanced Evasion Techniques
The threat actor behind the information-stealing malware known as Typhon Reborn has resurfaced with an updated version (V2) that packs in improved...
-

 2.1KMalware
2.1KMalwareCryptocurrency Companies Targeted in Sophisticated 3CX Supply Chain Attack
The adversary behind the supply chain attack targeting 3CX deployed a second-stage implant specifically singling out a small number of cryptocurrency companies....
-
 4.3KVulnerabilities
4.3KVulnerabilitiesCacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active Exploitation
Critical security flaws in Cacti, Realtek, and IBM Aspera Faspex are being exploited by various threat actors in hacks targeting unpatched systems....
-

 2.7KVulnerabilities
2.7KVulnerabilitiesSpyware Vendors Caught Exploiting Zero-Day Vulnerabilities on Android and iOS Devices
A number of zero-day vulnerabilities that were addressed last year were exploited by commercial spyware vendors to target Android and iOS devices,...
-
 2.3KMalware
2.3KMalwareMélofée: Researchers Uncover New Linux Malware Linked to Chinese APT Groups
An unknown Chinese state-sponsored hacking group has been linked to a novel piece of malware aimed at Linux servers. French cybersecurity firm...
-
 2.9KMalware
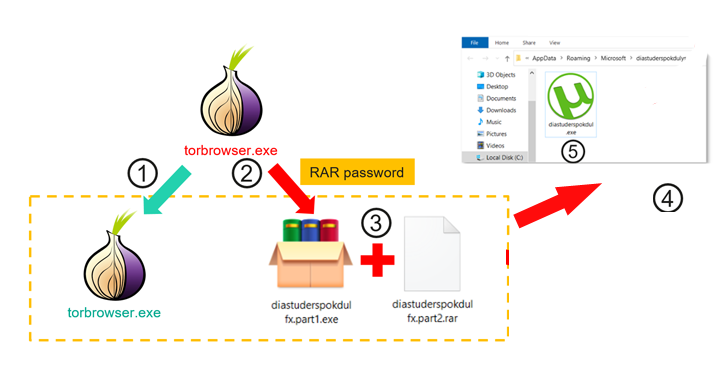
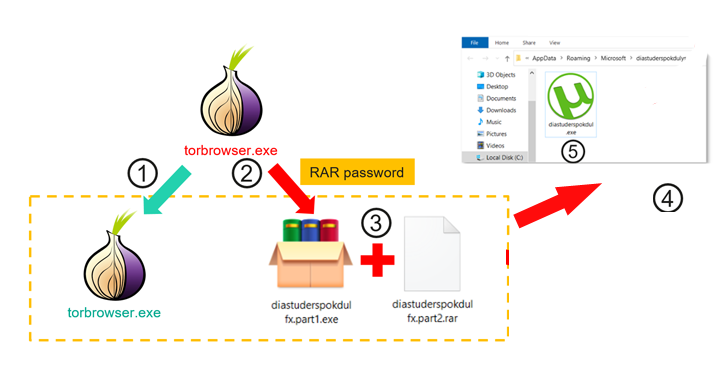
2.9KMalwareTrojanized TOR Browser Installers Spreading Crypto-Stealing Clipper Malware
Trojanized installers for the TOR anonymity browser are being used to target users in Russia and Eastern Europe with clipper malware designed...






