All posts tagged "hacking tool"
-
 525Malware
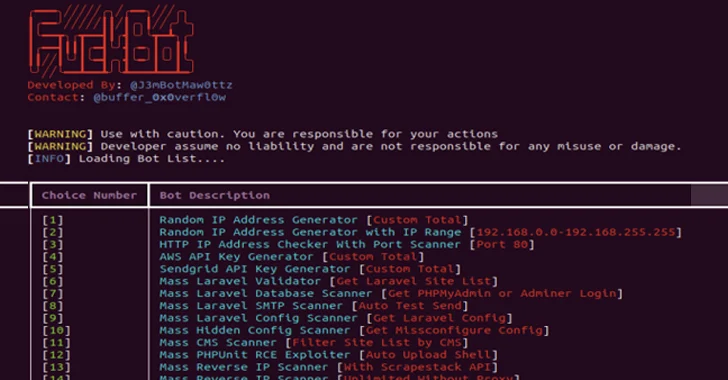
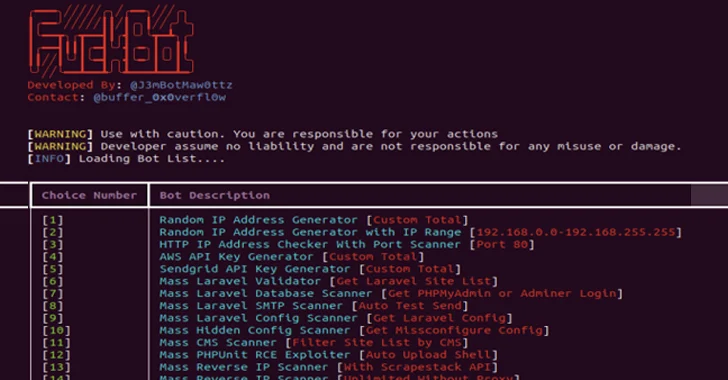
525MalwareNew Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms
A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud services, content management systems (CMS), and SaaS platforms...
-
 4.5KMalware
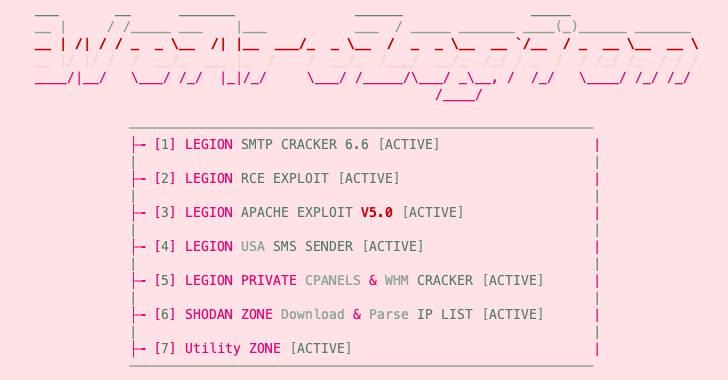
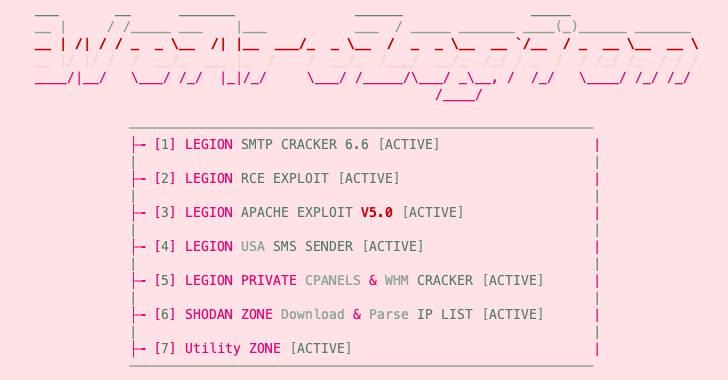
4.5KMalwareNew Python-Based “Legion” Hacking Tool Emerges on Telegram
An emerging Python-based credential harvester and a hacking tool named Legion is being marketed via Telegram as a way for threat actors...
-
 1.3KMalware
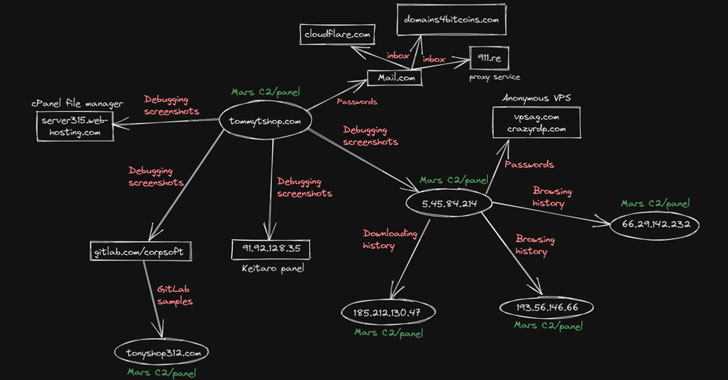
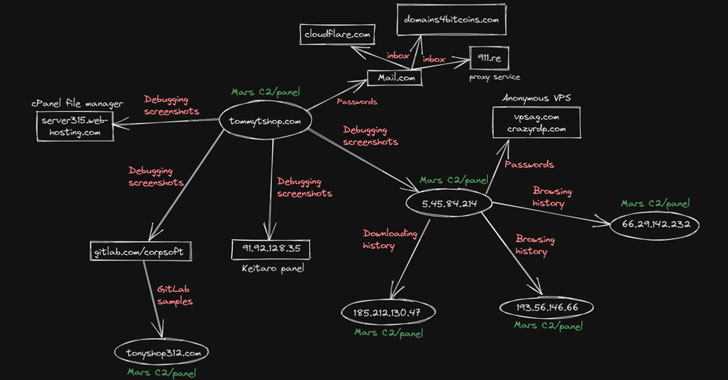
1.3KMalwareResearchers Expose Mars Stealer Malware Campaign Using Google Ads to Spread
A nascent information stealer called Mars has been observed in campaigns that take advantage of cracked versions of the malware to steal...
-
 4.4KMalware
4.4KMalwareLive Cybersecurity Webinar — Deconstructing Cobalt Strike
Organizations’ cybersecurity capabilities have improved over the past decade, mostly out of necessity. As their defenses get better, so do the methods,...
-

 449Cyber Attack
449Cyber AttackA Look Into Continuous Efforts By Chinese Hackers to Target Foreign Governments
Phishing is still one of the widely used strategies by cybercriminals and espionage groups to gain an initial foothold on the targeted...
-
 401Exploitation Tools
401Exploitation ToolsPixload – Image Payload Creating/Injecting Tools
Set of tools for creating/injecting payload into images. Useful references for better understanding of pixload and its use-cases: Bypassing CSP using polyglot JPEGs...
-
 309Malware
309MalwareTurla APT Hackers Upgraded Its Arsenal with New Hacking Tool “Topinambour” to Attack Government Networks
Infamous Turla APT Hackers group renew its arsenal with a new hacking tool named “Topinambour ” also called as aka Sunchoke that...
-
 253Malware
253MalwareHackers using weaponized TeamViewer to Attack & Gain Full Control of the Government Networks
Researchers spotted a new wave of cyber attack from Russian speaking hacker who uses the weaponized TeamViewer to compromise and gain the...
-

 489Hacked
489Hacked13 Best Hacking Tools Of 2019 For Windows, Linux, macOS
We have compiled a list of top hacking software and tools of 2019 with their best features and download links. This list...
-
 230News
230NewsWireshark 3.0.0 Open-source Network Analyzer Released: Download It Here
If analyzing data traffic and network protocols are something you are interested in, Wireshark is the go-to tool. It’s the world’s leading...
-

 249Exploitation Tools
249Exploitation ToolsPasteJacker – Add PasteJacking To Web-Delivery Attacks
The main purpose of the tool is automating (PasteJacking/Clipboard poisoning/whatever you name it) attack with collecting all the known tricks used in...
-

 293Hacking Tools
293Hacking ToolsSingularity – Open Source DNS Rebinding Attack Tool
Security company NCC Group have released an open source tool for penetration testing named Singularity, the tool allows security researchers to test...
-
 329Hacked
329HackedSocial Mapper: This Open Source Tool Lets “Good” Hackers Track People On Social Media
There are tons of automated tools and services that any shady hacker can employ to grab the public data on Facebook, Twitter,...
-
 235Data Breach
235Data BreachU.S Identified the Suspect Who Behind the major CIA Hacking Tools Leak and Provide to WikiLeaks
The U.S Finally identified the suspect who involved the CIA Vault 7 Hacking Tool leaks that contains the Powerful cyber weapons that...
-

 383Data Breach
383Data BreachVault 7 Leaks: CIA Conducts Secret Cyber Operation “ExpressLane” Against Their Intelligence Partners -WikiLeaks
WikiLeaks Revealed a new document of CIA Secret operations called “ExpressLane” that conducts against CIA’s information sharing Service Partners (liaison services) like NSA,DHS ,and FBI....
-
 314Malware
314MalwareCIA Hacking Tool “Brutal Kangaroo” Revealed to Hack Air-Gapped Networks by using USB Thumb Drives -WikiLeaks
Wikileaks Revealed Next CIA Hacking Tool called “Brutal Kangaroo” under Vault 7 Projects that Consists of 4 Powerful Malware Components which targets...
-

 287Hacked
287HackedVault 7: Wikileaks Uncovers Top Secret CIA Virus Control System “Hive”
Short Bytes: The non-profit whistleblower Wikileaks has published 6 new documents disclosing information about Hive, a back-end infrastructure used to manage CIA...
-

 271Hacked
271HackedKali Alternative: BackBox Linux 4.7 Arrives With Updated Hacking Tools
Short Bytes: The BackBox developers have released the latest version of their ethical hacking Linux distro, i.e., BackBox Linux 4.7. It comes with...
-

 224Hacked
224HackedAnother Facebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...






