All posts tagged "Hacking WiFi"
-
 298Data Security
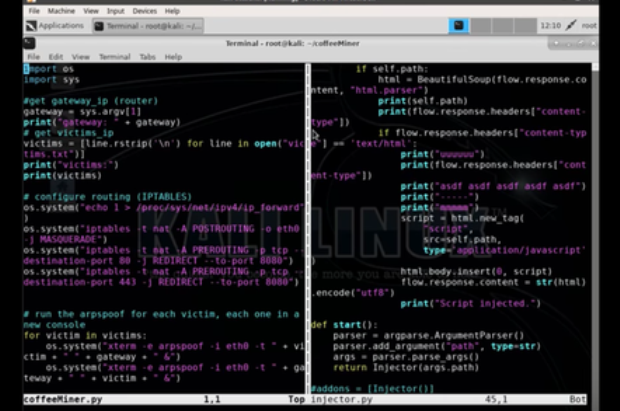
298Data SecurityCoffeeMiner: Hacking WiFi to inject cryptocurrency miner to HTML requests
Some weeks ago I read about this Starbucks case where hackers hijacked laptops on the WiFi network to use the devices computing power to...
-
 283Articles
283ArticlesProof of Concept Code for WPA2 Krack Attack has been released
Security researchers have discovered several key management vulnerabilities in the core of Wi-Fi Protected Access II (WPA2) protocol that could allow an...
-

 274Wifi Hacking
274Wifi HackingHacking WiFi – Selecting the best strategy
Not every hack will work under every circumstance, so choosing the right strategy is more likely to lead to success and less...






