All posts tagged "Hacks"
-

 1.2KGeek
1.2KGeekHere are 5 MacBook Hacks that You Must Know
MacBook hacks and shortcuts are endless. There is AirDrop, there is iMessage—the options are limitless. Here are 5 quick hacks to make...
-

 519Data Breach
519Data BreachClick2mail Hacked – Hackers Starts Sending Spam Emails To Stolen Email Address of Users
Famous Email service provider Click2mail suffering from a massive data breach that leaked their customer sensitive personal information, and the attackers used...
-

 247Malware
247MalwareATM Robber Malware Turns ATM into Slot Machine to Dispense Cash Automatically
ATM hijacking malware dubbed WinPot turns the ATMs into a slot machine, which starts dispensing the cash based on SPIN button. Security...
-

 200Incidents
200Incidents19-year-old youngster hacks local police systems
Officers say the young man wanted to belong to the police department Jared Joslin really wanted to belong to a law enforcement...
-

 257News
257NewsHackers Are Using These 6 Tools To Steal Your Cryptocurrency
In the early July, suspicious action around 2.3 million Bitcoin wallets was discovered, all of which appeared to be full-blown hacks in...
-

 278Data Security
278Data SecurityQuick look your right eyes and ears while using public WiFi network
Research has revealed that public WiFi networks are more dangerous than one might realize. They can be like ripe fruit for hackers....
-
 218Incidents
218IncidentsReport: Chinese government is behind a decade of hacks on software companies
Though sloppy at times, Winnti Umbrella remain advanced and extremely prolific. Researchers said Chinese intelligence officers are behind almost a decade’s worth...
-

 268News
268NewsSome Basic Tech Security Hacks That Everyone Should Use
Almost everyone today knows that the internet is full of viruses, all kinds of malware (simple as well as sophisticated ones) and...
-

 231Vulnerabilities
231VulnerabilitiesNew Tool Automatically Finds and Hacks Vulnerable Internet-Connected Devices
Hacking just got fully automated for script kiddies. Hacking isn’t always hard. Some lower-tier hackers use programs to automatically churn through breached login details...
-

 342News
342NewsNintendo Switch Hacked to Run Pirated Games
There is no doubt about the fact that Nintendo Switch is currently the most sought-after device. However, the device is also prone...
-

 237Geek
237GeekPS4 Jailbreak possible with newly identified exploit
PS4 Jailbreak is now possible – Thanks to a new exploit identified by researchers. We have always believed gaming consoles to be...
-

 235Vulnerabilities
235VulnerabilitiesDEVELOPERS TARGETED IN ‘PARSEDROID’ POC ATTACK
Researchers have developed a proof of concept attack that could impact the millions of users of integrated development environments such as Intellij,...
-

 338Geek
338GeekHackers Can Remotely Access Wireless Syringe Infusion Pump
Another day, another set of critical vulnerabilities in wireless medical devices – This time; high severity flaws identified in Smiths Medical Syringe...
-
 181Incidents
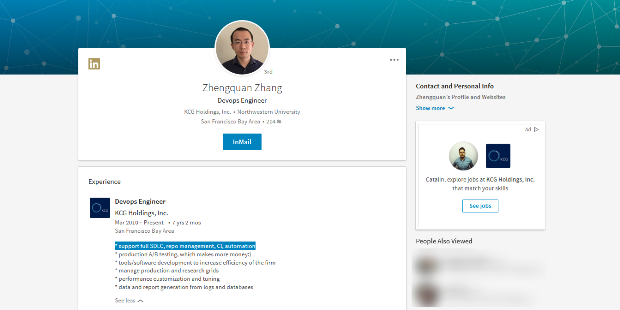
181IncidentsWall Street IT Engineer Hacks Employer to See If He Will Be Let Go
On Friday, April 7, the FBI arrested Zhengquan Zhang, a 31-year-old IT engineer, who now stands accused of installing malware on his...
-
 360Geek
360GeekSecurity Flaws in MAC Address Randomization Technique makes iOS, Android Devices Vulnerable to Tracking
Tracking mobile phones has become relatively easier since the advent of smartphones and wireless connectivity as these devices become traceable when they...
-

 217Vulnerabilities
217VulnerabilitiesHacks all the time. Engineers recently found Yahoo systems remained compromised
Company knocks $350 million off its purchase price. Some five months after Yahoo disclosed a security breach that exposed sensitive data for...
-
 192Vulnerabilities
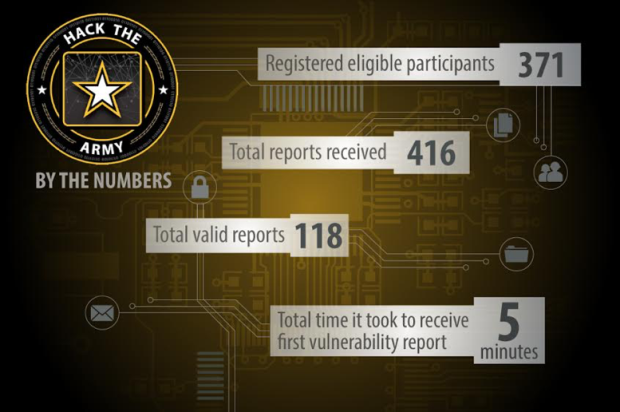
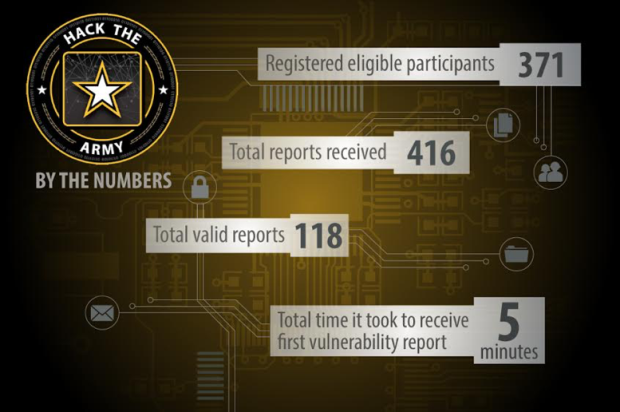
192VulnerabilitiesExpert Hacks Internal DoD Network via Army Website
The Defense Digital Services (DDS) group is tasked with pioneering private sector solutions to solve some of the Department of Defense’s most...
-
 294Data Breach
294Data BreachThese were the biggest Cyber Attacks of the year 2016
This was the year when many historical hacks came back to bite millions just as they were least expecting it.This year many...
-
 334How To
334How ToHOW TO CLONE A SIM CARD
Clone A SIM Card The Ultimate Tool to spy on somebody is his phone. People mostly do their confidential talks over a...
-

 242Cyber Attack
242Cyber AttackLearn SQL Injection with Practical example!!
What is a SQL Injection? Full form of SQL is Structured Query Language. It is used to retrieve and manipulate data in...
-

 277News
277NewsTurkish Hacker Defaces Arizona State Representatives and Legislature Sites
A football loving Turkish hacker defaced high-profile US government websites belonging to the State of Arizona, Arizona House of Representatives and Arizona Legislature! A...






