All posts tagged "HIJACKING"
-
 344Exploitation Tools
344Exploitation ToolsThreadBoat – Uses Thread Execution Hijacking To Inject Shellcode
Program uses Thread Hijacking to Inject Native Shellcode into a Standard Win32 Application. With Thread Hijacking, it allows the hijacker.exe program...
-

 293News
293News17-Yr-Old Finds Dell Laptops And PCs Are Vulnerable To Remote Attack
Dell laptop and computer owners beware! Your machine is vulnerable to an attack that can be executed remotely to hijack your system —...
-

 272Mobile Security
272Mobile SecurityHack the Car in Real Time – Car Alarm Flaw let Hackers Remotely Hijack 3 Million Vehicles Globally
Researchers discovered a serious Vulnerability in famous vendors car alarm system that allows attackers to hijack the car remotely and kill the...
-

 354Vulnerabilities
354VulnerabilitiesCombination of bugs in WordPress and WooCommerce allows website hijacking
A flaw in how WordPress handles privileges can be exploited to take control of a domain A flaw in the WordPress process to...
-
 245Vulnerability Analysis
245Vulnerability AnalysisScan your exposure to domain and subdomain hijacking over 10’s of cloud providers
Domain Hijacking is a well-known security issue that can be carried in many different ways. In addition to social engineering or unauthorized...
-

 293News
293NewsCrypto-Mining Malware is Catching Up
According to Check Point’s latest Global Threat Impact index, nearly 23 percent of organizations across the world is affected by the Coinhive...
-

 298Malware
298MalwareEMOTET Malware Hijacking the Windows API & Evade the Sandbox Analysis
A wide Spread EMOTET malware emerging again with new stealthy capabilities to hijack the Windows API and evade the sandbox detection which also gives...
-
 251Data Security
251Data SecurityNumber of Hijacked MongoDB Databases Is Going Up as More Hackers Are Flocking In
MongoDB administrators are about to be tought a hard lesson in database management practices, as the number of hackers that are now...
-
 183Data Security
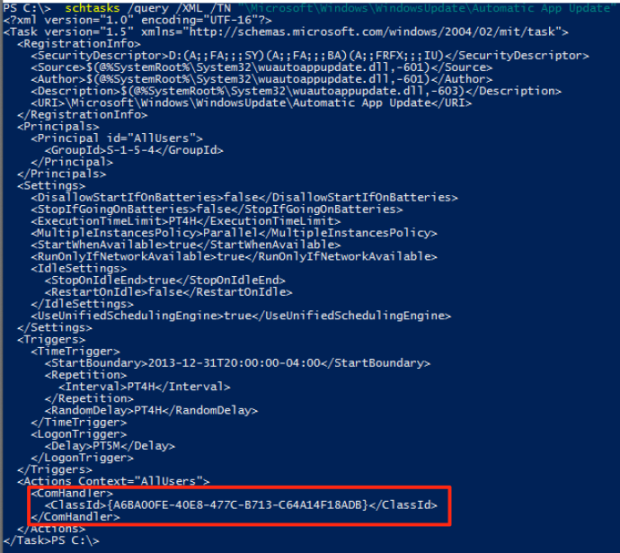
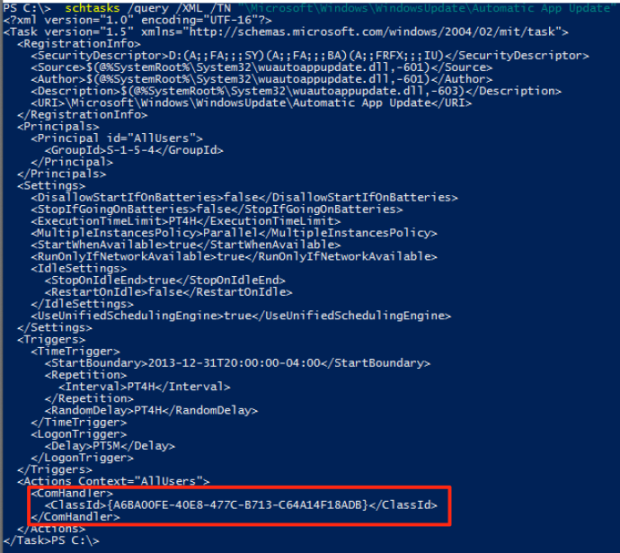
183Data SecurityUSERLAND PERSISTENCE WITH SCHEDULED TASKS AND COM HANDLER HIJACKING
A while back I was exploring userland COM and stumbled across some 2011 research by Jon Larimer explaining the dangers of per-user...
-

 249News
249NewsEuropean Trains at risk of being Hacked: Hackers
A trio of Russian hackers revealed numerous bugs in the train systems of many of Europe’s railway companies, saying that hackers and...
-

 195News
195NewsHacked Website of Connecticut University Caught Spreading Malware
Simple DNS hijacking enables attackers to distribute Fake Infected Flash Player at UConn website. On Sunday, the official web portal of the...
-
 351Data Security
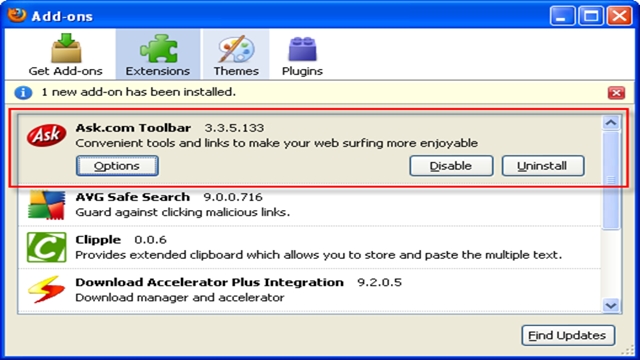
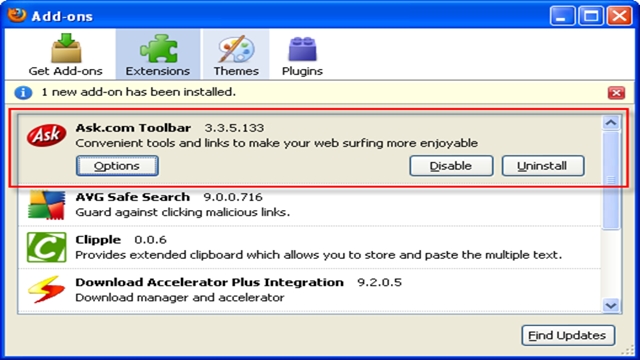
351Data SecurityAsk.com Toolbar Can Hijack Your Computer Through Java Updates
The Ask.com toolbar is not a handy tool — it’s a Curse because it never goes away. Apparently, Ask.com toolbar hijacks your...






