All posts tagged "https"
-

 2.4KData Security
2.4KData Security5 WordPress Security Solutions with Free SSL Certificates
Security vulnerabilities are inevitable but one can avoid them by securing applications. In this article, we are listing 5 popular WordPress security...
-

 4.1KData Security
4.1KData SecurityGoogle issues patches for Chrome flaw for Windows, Mac and Linux
Along with a patch for a zero-day bug in the Chrome browser, Google has addressed seven other flaws in its recent update....
-

 347Data Security
347Data SecurityWill other countries follow Kazakhstan in forcing users to install certificates for HTTPS interception?
Experts from multiple digital forensics firms report that the Kazakhstan government has begun intercepting all HTTPS traffic detected within its territory. Internet...
-

 231News
231NewsYour Netflix Bandersnatch Choices Can Be Tracked By Hackers
Netflix took the video streaming industry by storm when it debuted Black Mirror: Bandersnatch last year. The “choose your own adventure” themed...
-

 308News
308News150 Million Xiaomi Devices Vulnerable To A Major Security Flaw
The purpose of security apps is to protect devices and user data. However, Xiaomi’s pre-installed security app did just the opposite and...
-

 242News
242NewsGoogle Chrome Lite Pages Are Now More Secure And Faster
Google Chrome’s Data Saver feature helps load pages faster when there is low network connectivity on Android devices. In addition to this,...
-

 225Vulnerability Analysis
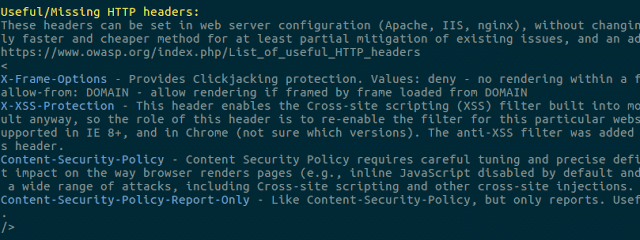
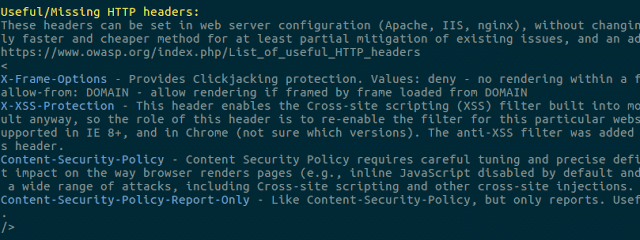
225Vulnerability Analysistestssl.sh – Testing TLS/SSL Encryption Anywhere On Any Port
testssl.sh is a free command line tool which checks a server’s service on any port for the support of TLS/SSL ciphers, protocols...
-
 256Vulnerability Analysis
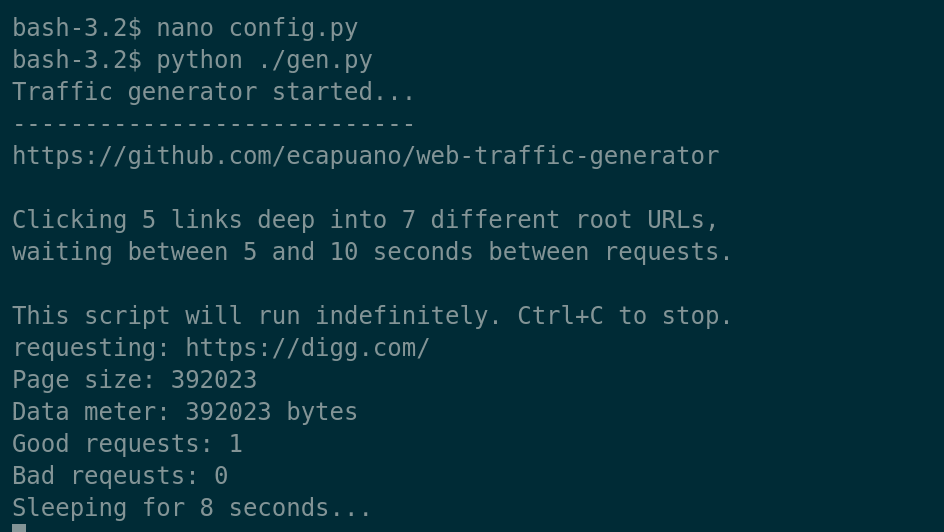
256Vulnerability AnalysisWeb-Traffic-Generator – A Quick And Dirty HTTP/S “Organic” Traffic Generator
Just a simple (poorly written) Python script that aimlessly “browses” the internet by starting at pre-defined rootURLs and randomly “clicking” links on...
-
 410News
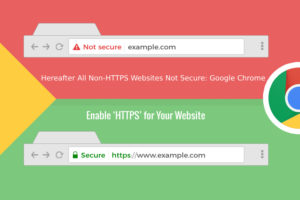
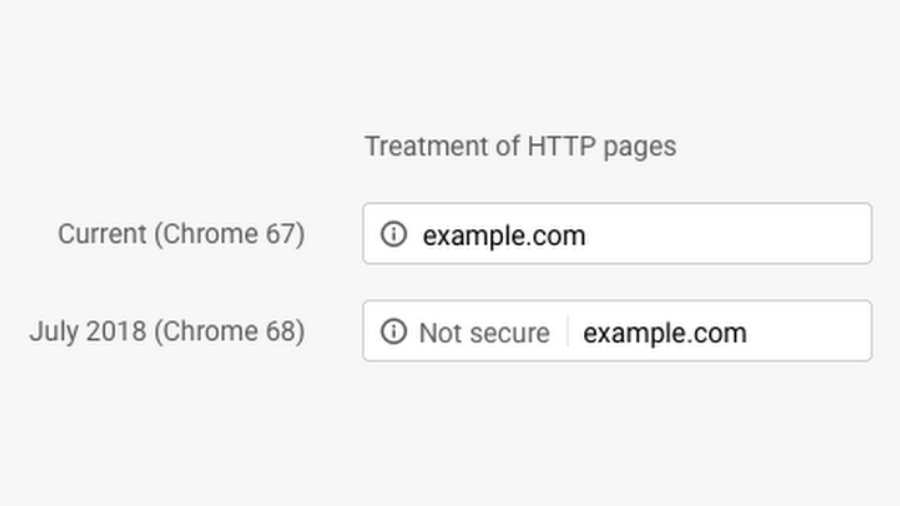
410NewsGoogle Chrome Warns It’s Now Time To Ban Websites With No Https
Google’s Chrome Browser is now labeling all non-https website as explicitly “not secure.” With the release of Chrome 68 yesterday, all http...
-
 249Hacked
249HackedHere’s Why Chrome Is Now Showing Millions of Websites As “Not Secure”
Google is taking the privacy quite seriously, and the new Chrome security update will undoubtedly put a significant toll on all your...
-

 305News
305NewsGoogle to mark all non HTTP pages as not secure
As we hit the browser day in and day out we have seen how the web security has taken to new heights....
-

 206News
206NewsGoogle Axes Green Padlock Sign from HTTPS Sites
Google in 2016 won the desktop browser war, toppling the erstwhile king Microsoft’s Internet Explorer and as of this writing, its minimalist...
-

 253Hacked
253HackedAndroid P Will Block Apps From Sending Internet Traffic That Anyone Can See
Android P will prevent apps from using unencrypted connections by default while establishing connections over the internet, according to a blog post...
-

 306News
306NewsEither HTTPS or Get Booted out
In the coming July 2018, Chrome will come down heavily on websites that have not implemented Secure-socket Layer/Transport Security, which will be...
-
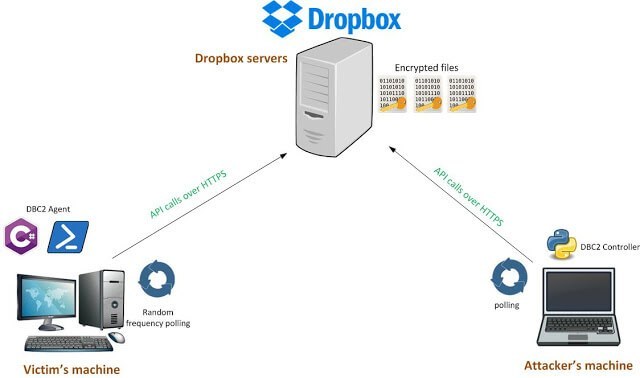
 281Post Exploitation
281Post ExploitationDBC2 (DropboxC2) – A Modular Post-Exploitation Tool, Composed Of An Agent Running On The Victim’S Machine
DBC2 (DropboxC2) is a modular post-exploitation tool, composed of an agent running on the victim’s machine, a controler, running on any machine,...
-
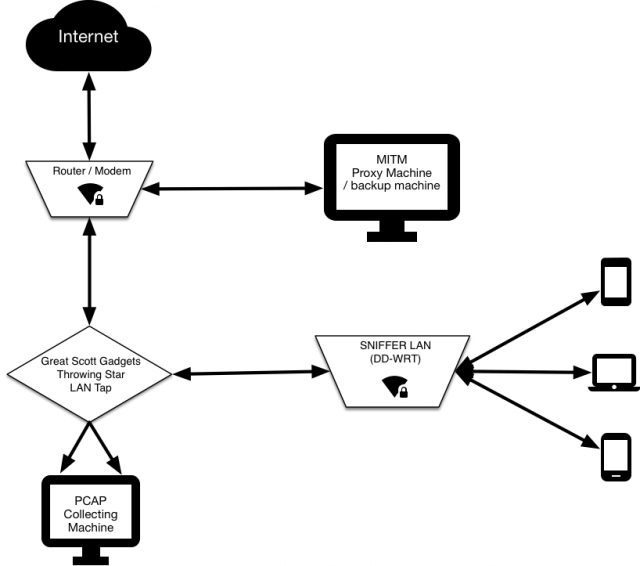
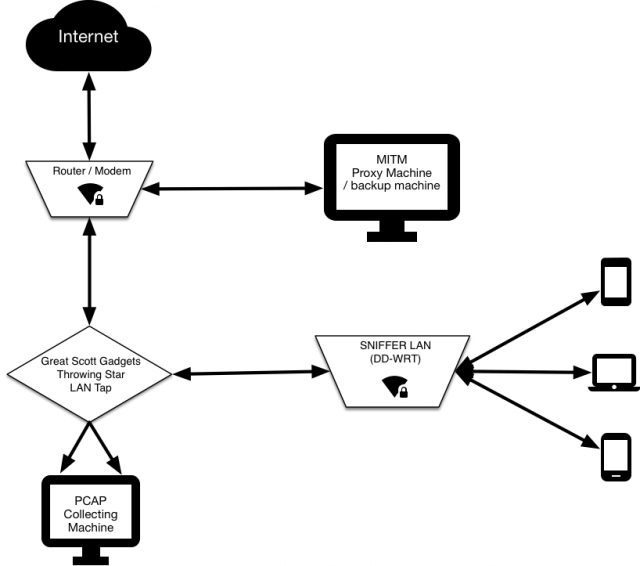 272Man-In-The-Middle
272Man-In-The-MiddleSNIFFlab – Create Your Own MITM Test Environment
Essentially it’s a WiFi hotspot that is continually collecting all the packets transmitted across it. All connected clients’ HTTPS communications are subjected...
-
 232Exploitation Tools
232Exploitation ToolsCrunchRAT – HTTPS-based Remote Administration Tool (RAT)
CrunchRAT currently supports the following features: File upload File download Command execution It is currently single-threaded (only one task at a time),...
-
 243Information Gathering
243Information GatheringEllaScanner – Passive Web Scanner
Passive web scanner. EllaScanner is a simple passive web scanner. Using this tool you can simply check your site’s security state. Usage:...
-

 266Malware
266MalwareRunning OSX relatively safe? New Malware strains targeting all versions of MacOSX clients
People regularly anticipate that in case you’re strolling OSX, you’re highly secure from malware. But that is turning into much less and...
-

 233Hacked
233HackedWorld’s Biggest Porn Site Is Now HTTPS Protected And Fully Encrypted
Short Bytes: Pornhub, a talked about name in the adult entertainment industry has rolled HTTPS encryption across the whole website. This is...
-

 297How To
297How ToBinProxy – A Proxy Tool For TCP Connections
BinProxy is a proxy tool for arbitrary TCP connections. It gives you a TCP proxy and an interface to write protocol-specific parsers...






