All posts tagged "IBM"
-
 1.3KMalware
1.3KMalwareNew Evidence Links Raspberry Robin Malware to Dridex and Russian Evil Corp Hackers
Researchers have identified functional similarities between a malicious component used in the Raspberry Robin infection chain and a Dridex malware loader, further...
-

 277News
277NewsIBM Completes The $34 Billion Red Hat Acquisition
International Business Machines Corporation (IBM) has completed its acquisition of Red Hat for $34 billion, thus making it the world’s second-biggest technology...
-

 298Incidents
298IncidentsTech companies IBM, HP, Fujitsu, TCS, NTT Data, Dimension Data and CSC were hacked to access client networks & data
Network security specialists claim that a hacker group working for China’s Ministry of State Security hacked the networks of eight of the...
-

 267News
267News“Red Hat Will Remain Independent; I’m Not Buying Them To Destroy Them,” Says IBM CEO
Ever since IBM announced that it’s going to acquire the open source giant Red Hat, Linux and open source enthusiasts have been...
-
 274News
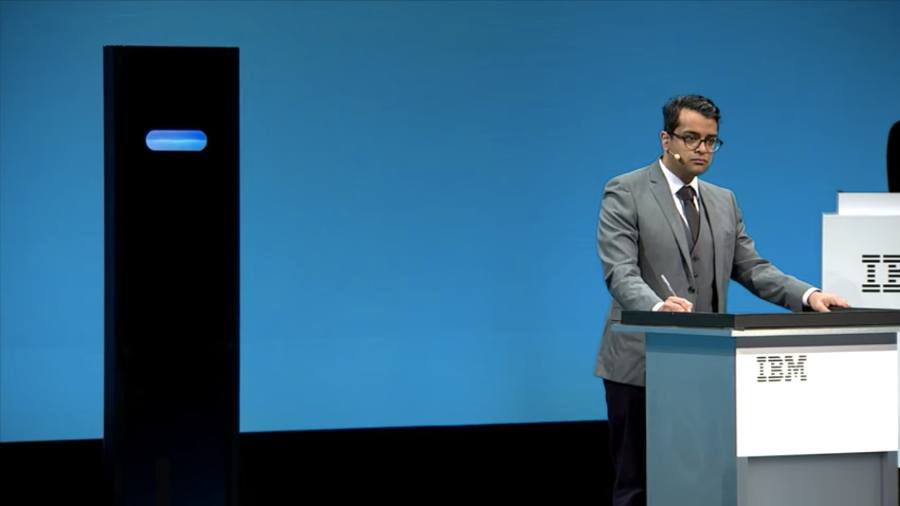
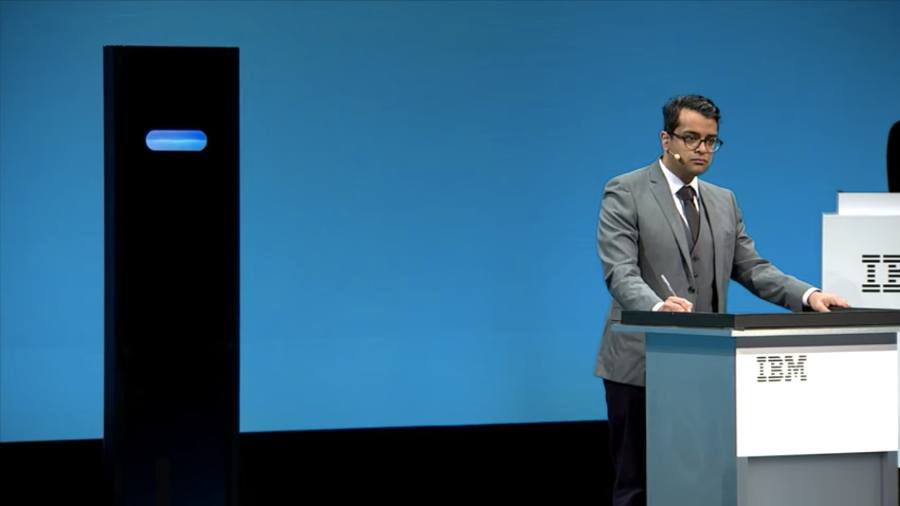
274NewsIBM’s AI Computer Loses To Human In A Debate
People are usually good at arguing, and the ability to comprehend and put forward arguments is one of our greatest capabilities. But...
-

 311News
311NewsFirst Commercial Quantum Computer From IBM Features An Awe Inspiring Design
With CES 2019 underway, IBM has unveiled the world’s first commercial quantum computing system Q System One. Visually, it’s nothing less than a...
-

 298Data Security
298Data SecurityWeather Channel & Weather app are selling user’s location data
A lawsuit against the app developers was filed in a Los Angeles court by allegedly extracting the location data from the users...
-

 298Incidents
298IncidentsCybercriminals attack Hewlett Packard and IBM networks and servers
Accusations against Chinese intelligence agencies continue According to cybersecurity and ethical hacking experts from the International Institute of Cyber Security, alleged Chinese...
-

 257Geek
257GeekIBM acquiring Red Hat for a whopping $34 billion
IBM (International Business Machine) is acquiring the world-renowned provider of open source cloud software Red Hat, Inc., for a whopping $34 billion, the...
-
 323Geek
323GeekIBM Buys Linux & Open Source Software Distributor Red Hat For $34 Billion
IBM and Red Hat have announced an agreement that IBM has struck a deal to acquire the Linux and open source software distributor...
-

 267Data Security
267Data SecurityCamuBot Malware Camouflaged as Bank Security App to Steal Credentials
A new banking malware has been discovered that is targeting bank customers in Brazil. Dubbed as CamuBot, it is identified to be...
-

 243Hacked
243HackedDeepLocker: Here’s How AI Could ‘Help’ Malware To Attack Stealthily
By this time, we have realized how artificial intelligence is a boon and a bane at the same time. Computers have become...
-

 287Vulnerabilities
287VulnerabilitiesSecurity flaw that allows hackers to replace serverless codes at IBM is fixed
This is the first vulnerability in a serverless platform being publicly disclosed International Business Machines Corporation (IBM) researchers have solved a critical vulnerability...
-

 235Geek
235GeekProgramming Meets Blockchain: IBM’s New Patent Ensures That You Get Rewarded For Your Code
When several coders work on a large project, it can become quite a task to keep track of their accomplishments and determine...
-

 323Vulnerabilities
323VulnerabilitiesMultiple Vulnerabilities in IBM QRadar SIEM Allows Attackers to Escalate Privileges and to Execute Arbitrary Commands
Multiple Vulnerabilities found in IBM QRadar chained together allows a remote attacker to bypass authentication and to execute arbitrary commands with root...
-

 322Data Security
322Data SecurityIBM improves its security and prohibits the use of USB drives throughout the company
IBM recently banned all removable storage, throughout the company; this is a new policy that aims to avoid financial and reputational damage...
-

 348Data Security
348Data SecurityTrickBot Variant Steals Bitcoin by Hijacking Cryptocurrency Transactions
Another day, another malware – This time TrickBot’s variant is stealing Bitcoin by hacking cryptocurrency transactions. TrickBot malware, which emerged in late...
-
Vulnerability Analysis
unCaptcha – Low Resource Defeat of reCaptcha’s Audio Challenge
Across the Internet, hundreds of thousands of sites rely on Google’s reCaptcha system for defense against bots (in fact, Devpost uses reCaptcha...
-
 452Vulnerabilities
452Vulnerabilities6 Critical RCE and Buffer Overflow Vulnerabilities in IBM Informix Dynamic Server and Informix Open Admin Tool
IBM Informix Dynamic Server and Informix Open Admin Tool contains 6 Critical Vulnerabilities including RCE and a Buffer overflow in HEAP. IBM Informix...
-

 359Data Security
359Data SecurityIBM Sent Off USB Sticks Infected with Malware
A new warning has been issued by IBM and the situation seems to be rather serious. According to the firm, there are...
-
 285Geek
285GeekBig Tech Companies Announce OpenCAPI Consortium To Develop Open Hardware For Servers
Short Bytes: OpenCAPI is a consortium formed by tech leaders AMD, Google, IBM, Micron, and Mellanox which aims to provide an open...






