All posts tagged "Infosec"
-

 161Data Security
161Data SecurityBig Data and Cybersecurity: Opportunity or Threat?
Suppose you write for a living. You write articles and blog posts for a number of clients. In the course of that...
-

 325News
325NewsHackers can manipulate Police body cam footages
Kiss goodbye to crucial evidence. Body cameras used by the law enforcement nowadays have already remained controversial but no one has, so...
-

 338Data Security
338Data SecurityHP Bug Bounty Program: Hack HP Printers & Earn Up To $10,000
HP Discloses its Bug Bounty Program and Here’s What You Need To Know. The Palo Alto Calif. based HP Inc., has disclosed...
-
 354Video Tutorials
354Video TutorialsHow to Generate a PHP Backdoor using Weevely – Kali Linux
Weevely is a web shell designed for post-exploitation purposes that can be extended over the network at runtime. Upload weevely PHP agent...
-

 402Data Security
402Data SecurityHow to Teach Your Employees About Cybersecurity
In the modern world, threats to security are no longer just physical. In fact, cybersecurity has now become one of the most...
-

 409Cyber Crime
409Cyber CrimeEx-employee stole secrets of Israeli spyware firm for dark web deals
Israeli authorities have arrested a 38-year-old man for allegedly stealing secrets of the NSO Group, a Herzliya-based firm that specializes in developing spyware and...
-

 468News
468NewsWiFi hacker: 10 best Android & Desktop WiFi hacking apps free download
Hacking is no more the specialty of experts and professionals only. With the emergence of user-friendly hacking tools, the art can be...
-

 307News
307NewsHacker access critical code of British cell operator EE
EE, a British mobile network giant owned by BT Group has been accused of leaving a critical code repository on an open-source tool protected...
-
 459Data Security
459Data SecurityFirewalls: What They Are & Why You Need Them
There are some phrases that you hear bandied about, and you think that you know what they are. You have a basic...
-
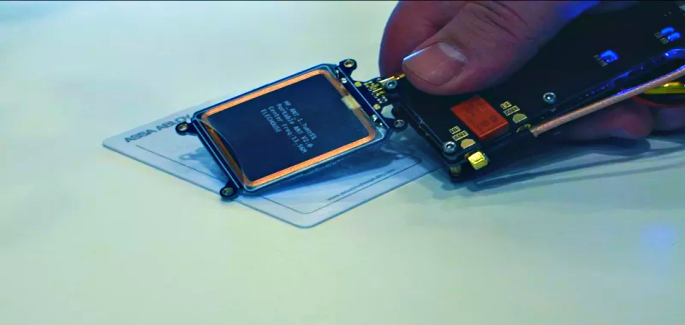
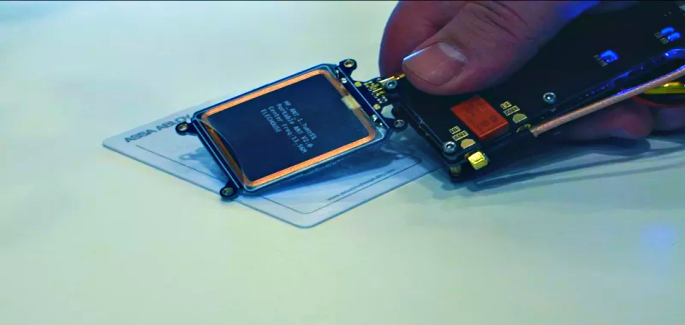 211News
211NewsMaster Key Hack Exploits Flaw in Key System to Unlock Hotel Rooms
The master key hack has the capability of unlocking not hundreds or thousands but millions of hotel rooms, claim F-Secure security researchers....
-

 258Data Security
258Data SecurityAll Nintendo Switch Consoles Contain Unpatchable Chip-Level Flaw
Nintendo Switch has fans across the world; the gaming console has garnered success worldwide and has remained in high demand since it...
-

 170Data Security
170Data SecurityHackers find life-threatening vulnerabilities in Austrian ski lift control unit
Serious Vulnerabilities Identified in Austrian Ski Lifts Control System Can Disrupt its Operations- Researchers Claim. The impact of last year’s hack attack...
-

 319Data Security
319Data SecurityMedicine pumps & Pacemaker threat as Dr’s simulate hacked overdose
Doctors Demonstrate Dangers of Hacked Medicine Pumps By Simulating Emergency Overdose. The key points explored at the ongoing RSA 2018 included situations...
-

 174Data Security
174Data SecuritySecurity Trends to Watch Out for in 2018
There are many threats in the world, meaning business owners, as well as homeowners, have to be vigilant in their security systems...
-

 173News
173NewsHackers attack Casino’s fish tank thermometer to obtain sensitive data
The Internet of Things (IoT) has transformed the way we use everyday objects such as appliances, thermometers, and even lighting. However, despite...
-

 145News
145NewsWebsite security firm Sucuri hit by large scale volumetric DDoS attacks
Another day, another series of DDoS attacks – This time Sucuri and its customers have been hit by a series of attacks...
-

 270Data Security
270Data SecurityHackers can takeover & control emergency alarm system with a $35 radio
Researcher Identifies Emergency Alert Systems Vulnerable to Exploitation Due to SirenJack Flaw – Critical Military and State Infrastructure at Risk of Attacks by Malicious Hackers. ...
-

 232Geek
232GeekIntel removes remote keyboard app for Android rather than fixing its flaws
Critical Flaws in Intel’s Remote Keyboard App for Android Lead to its Discontinuation. As is the norm with security researchers, when bugs...
-

 228Data Security
228Data SecurityCyber security developments: Keeping safe and up to date
Cyber security is the backbone of any online businesses – Here are some quick tips to keep yourself informed about the latest...
-

 262Geek
262GeekFlawed Meltdown patch by Microsoft makes Windows more vulnerable
Microsoft’s January patch was released amidst claims of addressing the risks associated with attacks like Spectre and Meltdown to Windows-based systems. However,...
-

 340Data Security
340Data SecurityHackers can Send Fake Emergency Alerts by Exploiting 4G LTE Protocol Flaws
Researchers at the Purdue University and the University of Iowa, USA, have managed to break the key 4G LTE protocols for generation...






