All posts tagged "IoT"
-

 243News
243NewsSafe Computing Tips For Common Computer User
Currently, most computers are connected to the network, and various information is exchanged beyond national borders. Mobile devices such as smartphones and...
-

 317Hacking Tools
317Hacking ToolsJapanese Government to “Pen Test” Citizen’s IoT Devices Ahead of Olympics
The Japanese Ministry of Internal Affairs and Communications revealed in a recent report that 2/3 of cyber attacks in 2016 were aimed...
-

 206Geek
206GeekMeet Aztarna, a tool to find vulnerable Internet connected robots
The company behind Aztarna is Alias Robotics, a cyber-security startup. Manufacturers and users of IoT robots should breathe a sigh of relief that...
-

 232News
232NewsJapan Will Hack Its Citizens’ IoT Devices To ‘Make Them Secure’
The Japanese government has passed a new law amendment that will allow officials to hack into citizen’s Internet of Things devices to...
-
 213News
213NewsHow To Order Xiaomi’s China-exclusive Products In India?
Chinese company Xiaomi has a plethora of categories to offer to the users. However, there are many products unavailable in India and users...
-

 245Data Security
245Data SecurityMalware can fully compromise building control systems
Enterprise security vendor ForeScout’s operational technology research unit has developed a PoC (Proof-of-Concept) malware that exposed the vulnerabilities in building automation systems (BAS)...
-

 366Data Security
366Data SecurityThousands of Internet connected hot tubs vulnerable to remote attacks
Weak security practices have rendered IoT devices vulnerable to hacking and all sorts of cyber-attacks. According to the research from a Buckinghamshire-based...
-

 3.4KData Security
3.4KData SecurityHow to protect your sensitive data
A critical data security trends in 2019 highlights show that protecting access to increasing volumes of sensitive data will be a challenge....
-

 288Malware
288MalwareIoT malware grows over 200% during 2018
Several malware variants showed significant growth this year According to cybersecurity specialists from the International Institute of Cyber Security, the amount of...
-
 295News
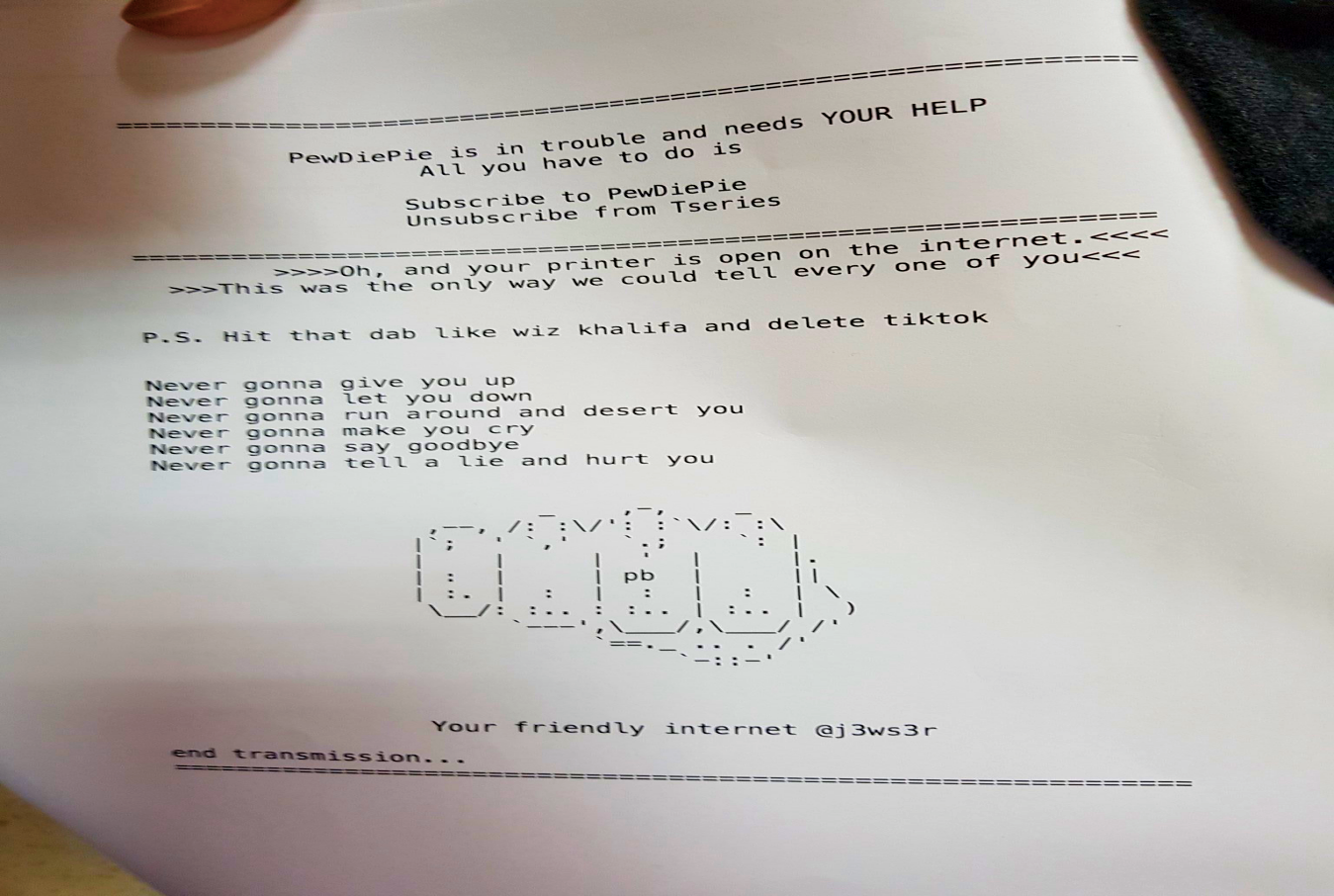
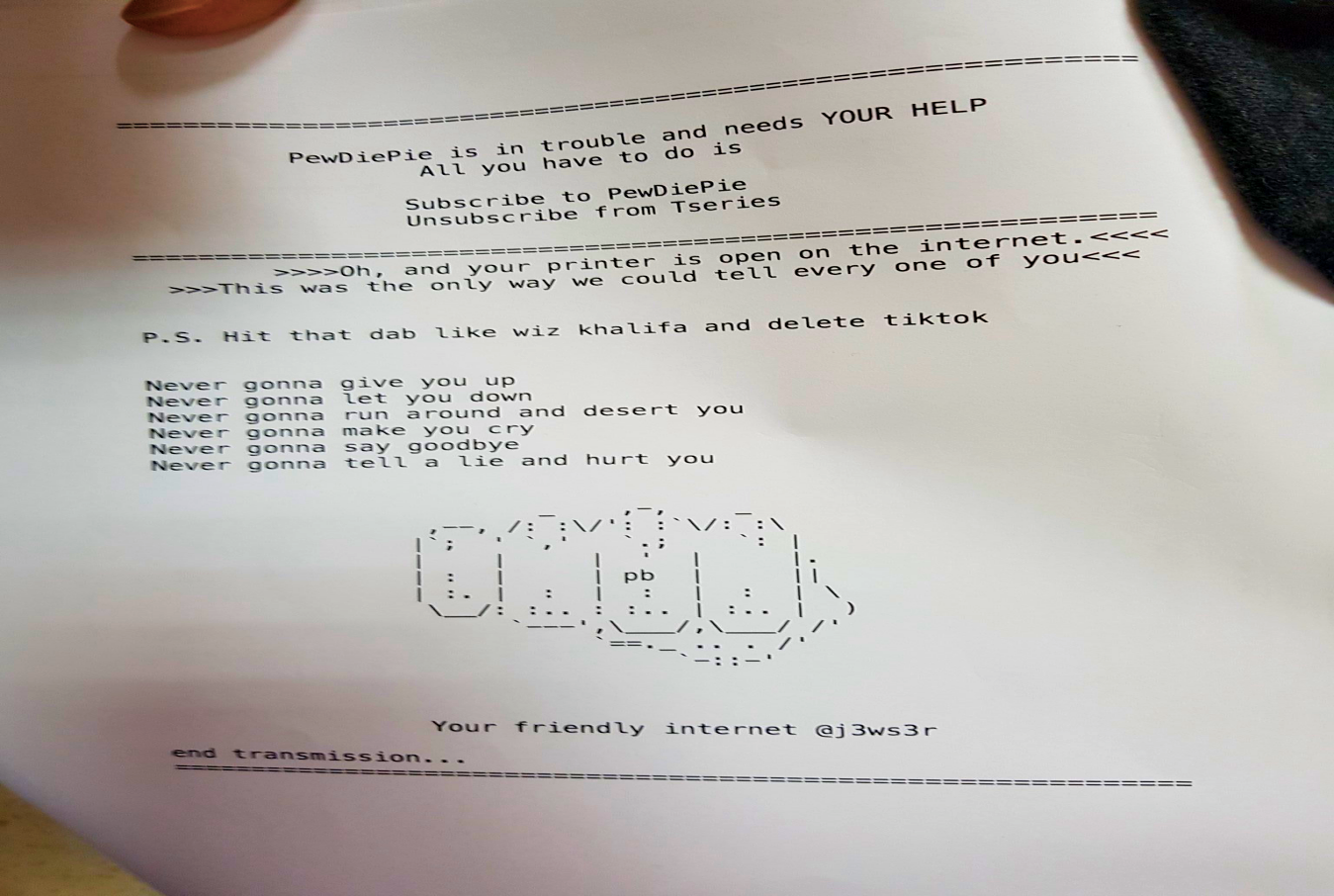
295NewsPewDiePie fan hacker compromise 100,000 printers
A couple of weeks ago, a hacker going by the online handle of TheHackerGiraffe hacked over 50,000 printers for the sake of promoting PewDiePie’s...
-
 353News
353NewsSomeone hacked 50,000 printers to promote PewDiePie YouTube channel
Nearly 50,000 printers across the globe were hacked by a hacker using the alias TheHackerGiraffe for the sake of promoting PewDiePie’s YouTube...
-
 285Infosec
285InfosecBeware – Dangerous IoT Attacks Leads Some One to Hack and Control Your Car
The Internet of Things (IoT), responsible for connecting unthinkable things, now offers the possibility of connecting vehicles to the internet. With this,...
-

 189Cyber Crime
189Cyber CrimeSophos: Cybercrime is a For-Profit Undertaking, Just Like Any Typical “Business”
The real world is a jungle; it is really is still the survival of the fittest even after hundreds of thousands of...
-

 235Data Security
235Data SecurityShoddy security of popular smartwatch lets hackers access your child’s location
Smartwatches are generally considered safe to keep track of your kids when they are outside the home. However, there is a scary...
-

 319Data Security
319Data SecurityVulnerability in Drone giant DJI exposed users’ photos & other sensitive data
Researchers at security firm CheckPoint identified a vulnerability in the website and apps of the popular consumer drone manufacturer DJI. The vulnerability...
-

 318Data Security
318Data SecurityCalifornia governor signs IoT cybersecurity bill
California Capitol Dome with Moon This law will establish a cybersecurity standard for IoT manufacturers Jerry Brown, Governor of California, signed last...
-
 288Data Security
288Data SecurityMeet GhostDNS: The dangerous malware behind IoT botnet targeting banks
Security researchers at NetLab, a sub-division of the Chinese cybersecurity firm Qihoo 360, have discovered a new, wide-scale, and very active malware...
-

 330Cyber Crime
330Cyber CrimeAir-conditioned apocalypse: A blackout scenario involving smart climate control devices
Science fiction movies often depict various situations related to cybercriminals’ activity. These can include predicaments where threat actors disrupt the transportation system...
-

 276Data Security
276Data SecurityResearchers demonstrate how to unlock Tesla wireless key fobs in 2 seconds
Vulnerabilities and security flaws in vehicle security systems aren’t as surprising for us as it is that even the most renowned car...
-

 392Geek
392GeekApple Watch saves one more life by notifying user about his unusual heart rate
Who doesn’t like elegant watches, especially those who can literally save your life like the Apple Watch, right? Last time when we talked...
-

 356News
356NewsNew Mirai Botnet Variant Now Infects Vulnerable IoT Devices Near You
Right after the smartphone and tablet revolution that disrupted the laptop market considerably, the next big thing is the proliferation of IoT...






