All posts tagged "IoT"
-

 333Pentest
333PentestMetasploit Can Be Directly Used For Hardware Penetration Testing Now
Security researchers and penetration testers have used the open source Metasploit Framework to probe for vulnerabilities, run exploits, and simulate real-world attacks...
-
Articles
Security Flaw in LG IoT Software Left Home Appliances Vulnerable
LG has updated its software after security researchers spotted a flaw that allowed them to gain control of devices like refrigerators, ovens,...
-

 268Hacked
268HackedIoTroop/Reaper: A Massive Botnet Cyberstorm Is Coming To Take Down The Internet
In 2016, Mirai botnet shook the cybersecurity world with massive DDoS attacks that took down popular websites, online services, and hosting providers....
-

 206DDOS
206DDOSOne Million Organisations hit in under a Month with a Massive IoT botnet
The Internet of Things or IoT refers to the vast network of connected devices or “things” connected to the Internet which can...
-

 191Articles
191ArticlesA New IoT Botnet Threatens to Take Down the Internet
Just a year after Mirai—biggest IoT-based malware that caused vast Internet outages by launching massive DDoS attacks—completed its first anniversary, security researchers...
-

 332Geek
332GeekGoogle Home Mini Secretly Recorded Conversations Due to “Flawed Touch Panel”
We often hear about smart home speakers eavesdropping on all the conversations inside the home because these are already equipped with the...
-
 235Geek
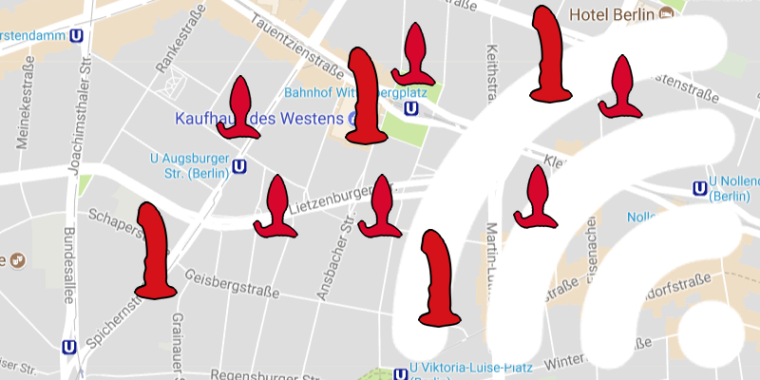
235GeekHackers can identify if you are using sex toys and exploit them
Smart Sex Toys Can Be Switched On/Off and Exploited Remotely – Thanks To A Vulnerability. Pen Test Partners (PTP) is a security...
-
 215News
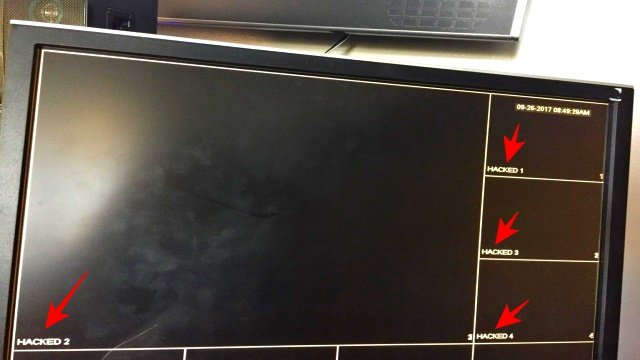
215NewsHikvision Security Cams Compromised to Display “HACKED”
If you own Hikvision security cameras you would have noticed the sudden change in the live feed display where the normal footages...
-

 338Geek
338GeekHackers Can Remotely Access Wireless Syringe Infusion Pump
Another day, another set of critical vulnerabilities in wireless medical devices – This time; high severity flaws identified in Smiths Medical Syringe...
-

 318Geek
318GeekCritical vulnerability lets hackers play with safety system of modern cars
According to the latest research from a collaborative team of researchers from Linklayer Labs, Politecnico di Milano and Trend Micro’s Forward-looking Threat...
-
 312News
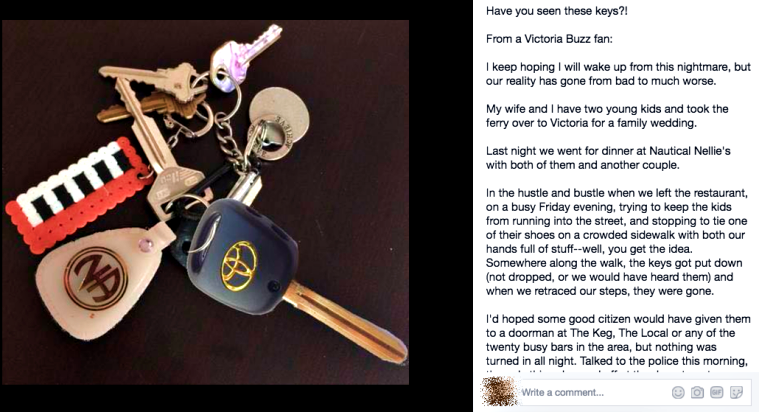
312NewsHacker unlocks vehicle for family who’d lost keys months ago
Our world is full of good and bad people and same applies for hackers. Where there are hackers eager to use their...
-

 240Data Security
240Data SecuritySelf-Driving Cars Can Be Tricked Into Misreading Street Signs
We know that this is the age of smart gadgets and self-operational machines. However, the cons associated with such devices easily surpass...
-

 171Data Security
171Data SecurityA Dangerous Vulnerability in Solar Panels can Cause Power Outage
Willem Westerhof, a cybersecurity researcher at Dutch security firm ITsec, has identified a serious vulnerability in an essential component of solar panels,...
-

 356Data Security
356Data SecurityAmazon Echo Can Be Hacked to act as a Surveillance device
Taking over an IoT (Internet of Things) device is nothing new for hackers, but since users have become increasingly dependent on smart devices,...
-

 355News
355NewsWatch: Hackers take over Tesla Model X; control brakes and doors
The hackers from Keen Security Labs, a part of Chinese Internet giant Tencent Holdings discovered some critical security flaws in Tesla Model X “holiday show” easter...
-

 176News
176NewsWatch: Researcher hacking, unlocking a smart gun with $15 magnets
A $1500 smart gun developed with the main objective of reducing gun crime has an inherent security flaw, which is so huge...
-
 282Geek
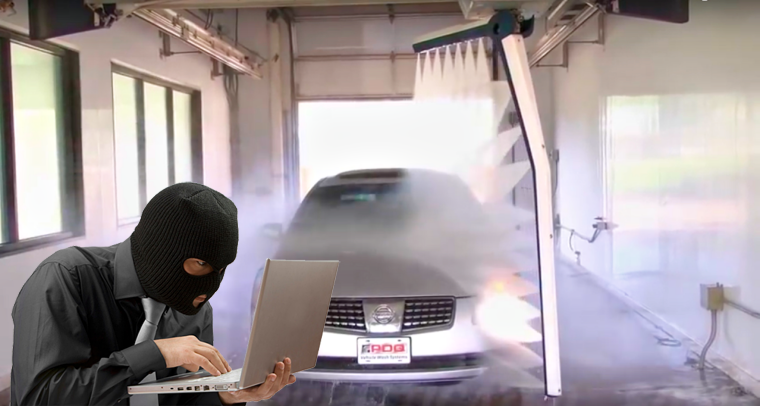
282GeekHackers can take over Car Wash, trap you and smash your vehicle
It is understandable to receive Internet of Things (IoT) related warnings like vulnerable public WiFi or charging spots that can be hacked...
-
 284News
284NewsCasino Becomes Victim of Data Hack—courtesy Fish Tank
It is a fact that the soaring number of internet-connected devices has made it easier for cyber-criminals to fulfill their malicious objectives...
-

 177Geek
177GeekRemotely Controllable Hoverboards Latest Target of Hackers
Without a doubt, hoverboards are the latest fad. Hoverboards are indeed very useful as these aren’t only easy to use but make...
-
 229Malware
229MalwareSambaCry Vulnerability used in Deploying Payloads Targeting IoT devices Particularly NAS
Attackers using the SambaCry vulnerability to target older versions of Samba(3.5.0) to upload and execute the malicious payload. SambaCry Vulnerability(CVE-2017-7494) have the...
-

 244Vulnerabilities
244VulnerabilitiesMillions of IoT Devices Infected with “Devil’s Ivy” Remote Code Execution Vulnerability Including Internet Connected Cameras
A New Vulnerability called “Devil’s Ivy” Discovered that infected Tens of Millions of IoT Devices which leads to Remotely Execute the code...






