All posts tagged "ISP"
-
 393Malware
393MalwareChinese APT 10 Group Hacked Nearly 10 Telecom Networks and Stealing Users Call Records, PII, Credentials, Email Data and more
Infamous Chinese APT 10 hackers compromised over 10 Telecom networks around the world under the campaign called Operation Soft Cell and stealing various...
-
 334Mobile Security
334Mobile SecurityHackers Taping the Phone Network using SS7 Attacks to Steal Money From Bank Accounts
New research states that sophisticated hackers are now taping the Phone network by exploiting the SS7 protocol to steal money from the...
-

 309DDOS
309DDOSA New Massive DDoS Attack bit-and-Piece Pattern Targeting Internet Service Providers
Internet service providers hit with a new stealthy volumetric attack by injecting the malicious traffic with the legitimate traffic to evade detection....
-
 197Incidents
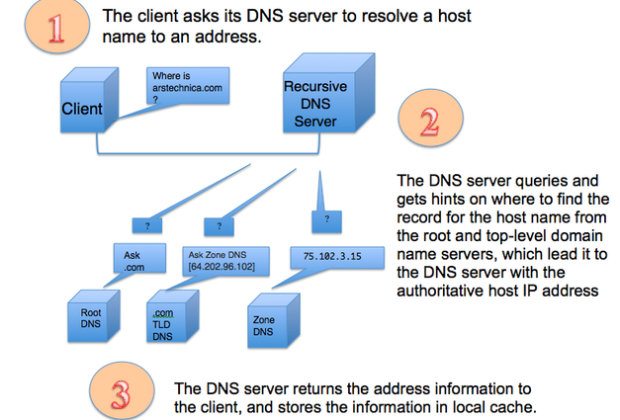
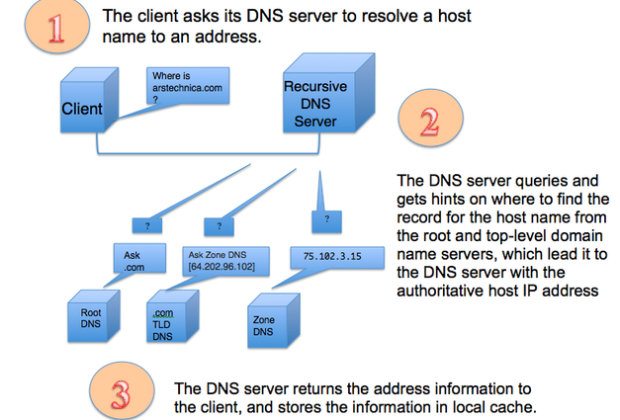
197IncidentsHow to keep your ISP’s nose out of your browser history with encrypted DNS
Using Cloudflare’s 1.1.1.1, other DNS services still requires some command-line know-how. The death of network neutrality and the loosening of regulations on how Internet...
-

 309Cyber Events
309Cyber EventsThe Pirate Bay suffers 40% traffic drop after domain ban in Netherlands
The Pirate Bay is in hot water once again – This time the reason is the Netherlands where authorities have blocked The...
-
 181Articles
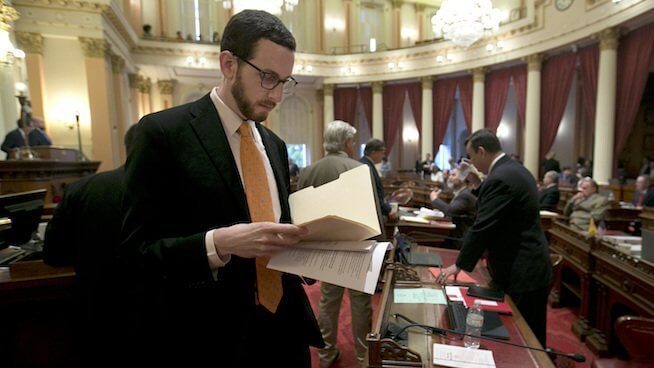
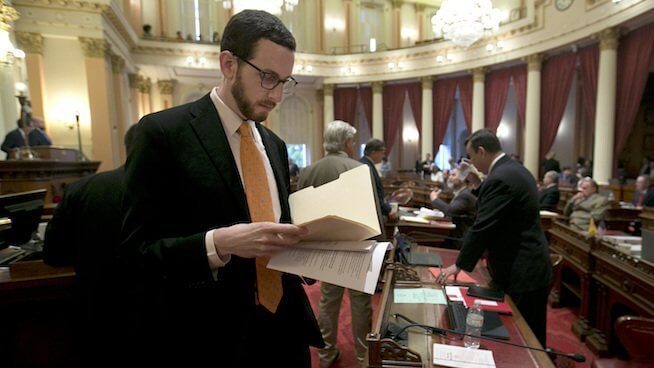
181ArticlesNew Bill has been announced by California to Protect Net Neutrality
As the FCC has attempted to abandon its role as the defender of a free and open Internet at the federal level,...
-
 190Security Tools
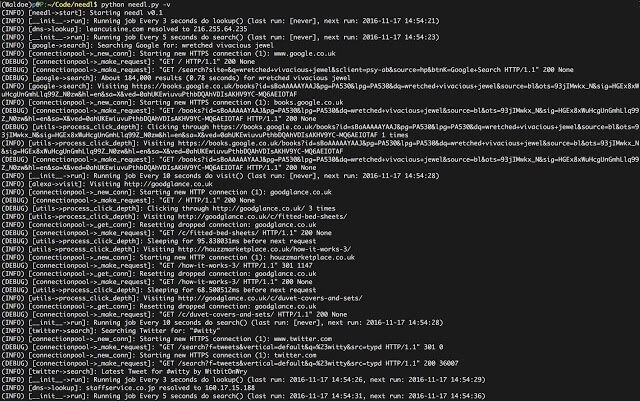
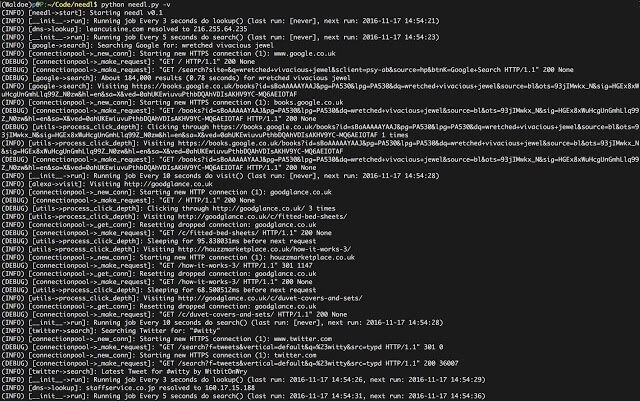
190Security ToolsNeedl – Take Back Your Privacy. Lose Yourself In The Haystack
Take back your privacy. Lose yourself in the haystack. Your ISP is most likely tracking your browsing habits and selling them to...
-

 167News
167NewsISPs Are Helping Hackers To Infect You With FinFisher Spyware
Are you sure that the version of WhatsApp or Skype or VLC Player installed on your device is legitimate? Security researchers have...
-

 273Data Security
273Data SecurityFlaws in ISP gateways let attackers remotely tap internet traffic
Defcon is the most important event for the DIY hacking community and this year too, the conference was held in the same...
-
 290Surveillance
290SurveillanceIXmaps Map reveals if your Internet traffic is being monitored by the NSA
A new interactive online tool named Internet Exchange Mapping (IXmaps) appeared earlier this week, and it shows if your data traffic passes...
-
 290Hacked
290HackedISPs Can Now Sell Your Web Browsing History Without Your Permission, US Senate Votes
Short Bytes: The US Senate has voted to discard the broadband privacy rules that would have forced the ISPs to seek consumers’...
-
 289Hacked
289HackedOnionDSL: Engineer Becomes Tor-based One Man ISP To Fight Against Mass Survelliance
Short Bytes: In order to oppose the advent of mass surveillance programs in the UK, an engineer named Gareth Llewelyn demonstrated his OnionDSL...






