All posts tagged "IT Security"
-

 431Malware
431MalwareBlack Basta Ransomware May Have Exploited MS Windows Zero-Day Flaw
Threat actors linked to the Black Basta ransomware may have exploited a recently disclosed privilege escalation flaw in the Microsoft Windows Error...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesProof-of-Concept Exploit Released for Progress Software OpenEdge Vulnerability
Technical specifics and a proof-of-concept (PoC) exploit have been made available for a recently disclosed critical security flaw in Progress Software OpenEdge...
-

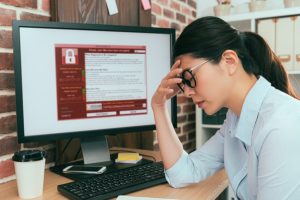
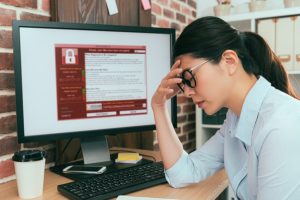
 702Malware
702MalwareAre We Ready to Give Up on Security Awareness Training?
Some of you have already started budgeting for 2024 and allocating funds to security areas within your organization. It is safe to...
-

 1.3KCyber Attack
1.3KCyber AttackVietnam: Cyber Attacks For 1st Half-2019 More Than Doubled
When it comes to cyber-attack and digital security issues, we often report incidents happening in the United States, Europe, and other first-world...
-

 3.5KData Breach
3.5KData Breach36TB Data Breach: The Culprit, Lenovo’s Obsolete Iomega NAS
The probability that Lenovo has earned the infamous record for becoming a subject of the world’s biggest data breach in history is...
-

 324News
324NewsDigital Transformation and Implementation of Information Security
Security has been a major concern for everyone recently, especially for companies that use technology as the main component of their service...
-

 3.6KPrivacy
3.6KPrivacyDefining Role-Based Access Control, or RBAC
Role-Based Access Control, or what is simply known as RBAC, provides the ability to restrict access to certain systems based on the...
-

 310News
310NewsNew Hybrid Computing, Same Security Concerns
Pulse Secure, with the cooperation of IDG Connect has released its 2019 State of Enterprise Secure Access research paper, detailing how cloud...
-

 682Data Breach
682Data BreachCathay Pacific 2014 Breach Fully Disclosed By Hong Kong
The Hong Kong Special Administrative Region in China, through its Privacy Commissioner, Stephen Kai-yi Wong has publicly disclosed a report containing more...
-

 247News
247NewsIT Security Sensitivity In The Financial Sector
IT Security’s importance is absolute, regardless of whether the corporate decision makers agree or not. It is the foundation where company’s survivability...
-

 272News
272NewsVictoria’s Public Health System “Highly Vulnerable”: Report
Victoria’s public health system is “highly vulnerable” to a Singapore-like data breach, according to a recent report. As per an auditor general...
-

 309News
309NewsOur Long Collective Struggle To Secure Enterprise Email
Email is the oldest service on the Internet, launched in the 1970’s, it is older than the WWW or the World Wide...
-

 3.4KCyber Attack
3.4KCyber AttackThe Sad State of New Zealand’s Cyber Attack Readiness
The New Zealand Financial Innovation & Technology Association (FinTechNZ), a financial-technology organization has exposed the alarming situation of companies based on New...
-

 258News
258NewsWipro, the Indian IT Service Giant Attacked By Phishing
IT Services giant, Wipro Ltd which is headquartered in India has become the latest victim of spear phishing. According to the initial...
-

 287News
287NewsThe IT Acronyms and What They Stand For
Here are the IT Security acronyms that you will like to know what it stands for in technology world. IT Security A...
-

 297News
297NewsPhishing Attack In EyeSouth Breached 24000 Patient Records
Hackers see the healthcare industry as a lucrative target for hackers, why we say so is because we have seen this happening...
-

 333News
333NewsVulnerable Legacy Systems Used By Banks, Need A Careful Review
The legacy-dependence of the financial sector is very evident, many banks are still using legacy hardware and software to perform their day-to-day...
-

 321News
321NewsFederal Websites Shutdown Due to Expired Security certificates
The public in the United States will no longer be able to access several Federal websites due to their expired HTTPS certificates....
-
 4.2KCryptocurrency
4.2KCryptocurrencyThe Nasty Operation of KingMiner Monero Cryptomining Trojan
2018 is becoming the year of cryptomining malware, a subtle virus compared to the very loud ransomware which dominated the 2017 malware...
-

 279News
279NewsPractical Policies That Help Increase Corporate Security
Companies today have largely accepted that technology is here to stay, and not embracing it is not in the table. The white...
-

 237News
237NewsSteps to Prevent Negative Economic Impact of Human Error
Human error has a lot to do with increased cybersecurity risks for any organization today, large or small. Even with reliable and...






