All posts tagged "Kali Linux"
-
 322How To
322How ToSetup own PenTesting Environment (DVWA) on your Kali Linux
Setup own PenTesting Environment in your Kali Linux. Penetration game Tester now plays more than a few years ago, because the Internet...
-
 458How To
458How ToList of Metasploit Commands – The Cheatsheet
Metasploit was created by H. D. Moore in 2003 as a portable network tool that uses Perl. In 2007, the Metasploit Framework...
-
 275Cyber Attack
275Cyber AttackLinux PC Can Be Hacked Remotely With Malicious DNS Response
A critical loophole has been discovered in SystemD, the popular first character system and service manager for Linux operating systems, which can...
-

 293How To
293How ToHow theHarvester Tool Used For Information Gathering In Kali Linux
The purpose of this program is to collect emails, subdomains, hosts, employee names, open ports and banners from various public sources such...
-

 375How To
375How ToWhat Is Hydra Tool In Kali Linux And How Does It Work?
Hydra Tool is a password detection tool (cracking) that can be used in a wide range of situations, including authentication-based forms commonly...
-

 227Incidents
227IncidentsKali Linux 2017.1 is arrived, more power for password-cracking with cloud GPUs
Kali Linux 2017.1 rolling release was announced, the popular distro comes with a set of significant updates and features. The popular Kali Linux...
-

 295Geek
295GeekKali Linux 2017.1 Released With New Features | Download ISO Files And Torrents Here
Short Bytes: Offensive Security has updated the Kali Linux images with new features and changes. Termed Kali Linux 2017.1, this release comes...
-

 456How To
456How ToHack Someone’s Bluetooth And Other Wireless Tools Using Kali Linux
Blooover is performing the Bluebug attack(Bluetooth sniffer Linux). Whilst you intend to install the software, you have to be using a phone...
-

 137How To
137How TomitmAP – Simple Tool to Create a Fake AP and Sniff Data
mitmAP, is a simple python program to create a fake AP and sniff data SSLstrip2 for HSTS bypass Image capture with...
-

 271Hacked
271HackedKali Alternative: BackBox Linux 4.7 Arrives With Updated Hacking Tools
Short Bytes: The BackBox developers have released the latest version of their ethical hacking Linux distro, i.e., BackBox Linux 4.7. It comes with...
-

 111News
111NewsLinux Based Red Star OS of North Korea can be Hacked by just a Link
North Korea’s personal homegrown PC operating device redstar, it’s presupposed to be completely hacker proof and extra comfortable than foreign OS, like...
-

 224Data Security
224Data SecurityHacking WPA Enterprise with Kali Linux
Admittedly, that’s somewhat of a click-bait blog post title but bear with us, it’s for a good reason. Lots of work goes...
-

 189How To
189How Toneedle – An iOS Security Testing Framework
needle, is an open source, modular framework to streamline the process of conducting security assessments of iOS applications and acts as a central point...
-
How To
How To Spoof MAC Address Using Macchanger in Kali Linux
MAC address spoofing is a technique for temporarily changing your Media Access Control (MAC) address on a network device. A MAC Address...
-
 266How To
266How ToLalin – Hackpack & Kali Linux Tools
Lalin, remake of Lazykali by bradfreda with fixed bugs, new features and updated tools. Lain is compatible with the latest Kali Linux...
-
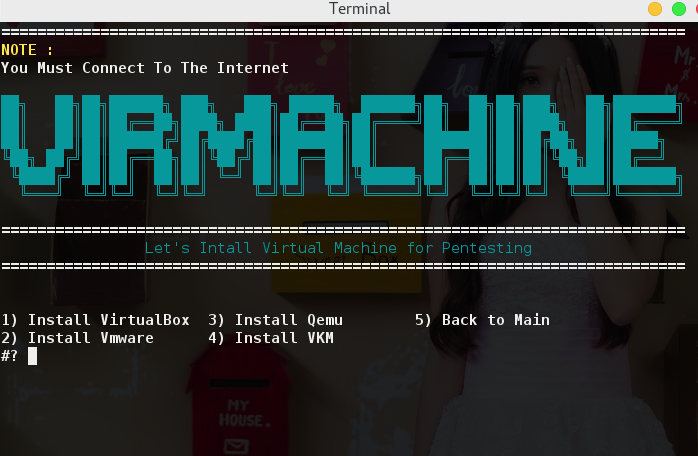
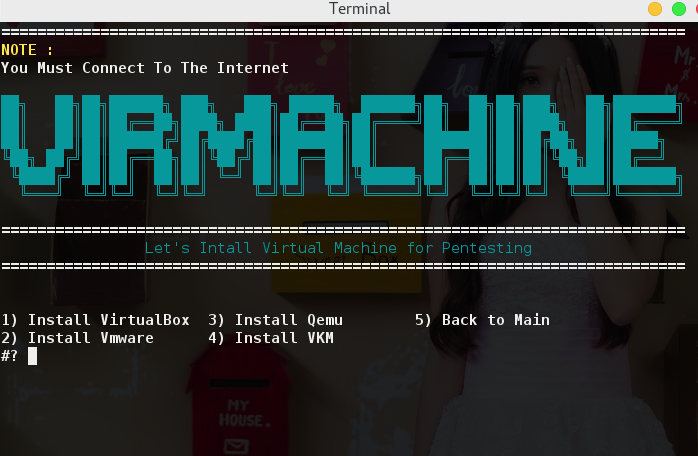
How To
How To Install VMware Tools In Kali Linux 2
Welcome back guys and today we will learn how to install official VMware Tools in Kali Linux 2.0 Sana. There are many articles online...
-
 204Geek
204GeekKali Linux 2016.2 Released — KDE, MATE, LXDE, Xfce, And e17 Flavors Available
Short Bytes: Developers of Kali Linux, one of the best ethical hacking distribution, have announced the second rolling release i.e. Kali Linux...
-

 401How To
401How ToHow To Install All Kali Linux Tools On Ubuntu Using “Katoolin” Script?
Short Bytes: Many Ubuntu Linux users are willing to use the tools of Kali Linux but they don’t want to install another...
-

 385News
385NewsCatalan Police Union Server Destroyed, Data Leaked Against Police Brutality
In an act of hacktivism, a hacker has leaked everything from the Catalan Police Union website — Reason: Police brutality! A couple of...
-

 275Hacked
275HackedKali Linux Rolling Release — Best Features That Make It The Best OS For Ethical Hackers
Image | Kali.org Short Bytes: Kali Linux, a hacker’s favorite operating system, is now available with first Rolling release. This release ensures...
-

 218Cyber Events
218Cyber Events8 Most Popular and Best Hacking Tools
The internet has as many downsides as well as upsides but it’s the lack of knowledge about dangers on users’ behalf makes...






