All posts tagged "Mac"
-

 218Malware
218MalwareBest way to Remove Malware on Mac, Including Other Unwanted Apps
Some Mac apps are so persistent that you can’t use traditional methods to remove them. Even if you do, there will always...
-
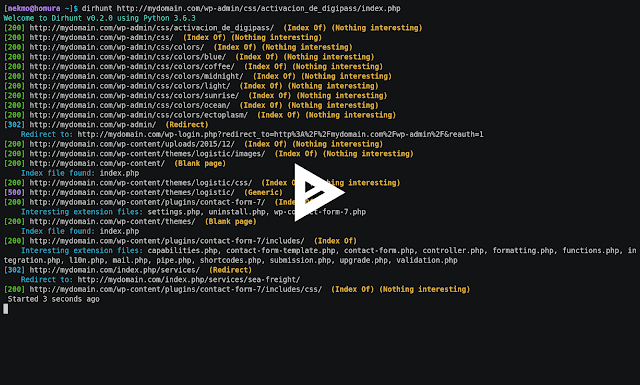
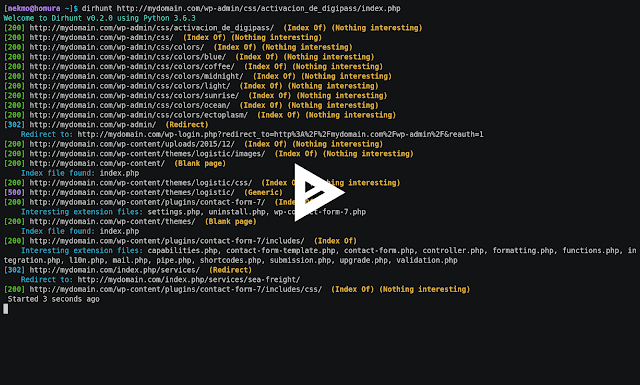 240Information Gathering
240Information GatheringDirhunt v0.6.0 – Find Web Directories Without Bruteforce
DEVELOPMENT BRANCH: The current branch is a development version. Go to the stable release by clicking on the master branch. Dirhunt is...
-
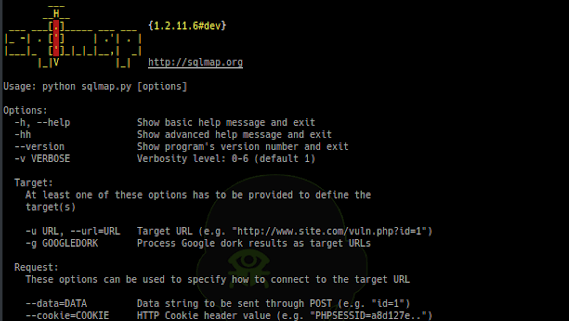
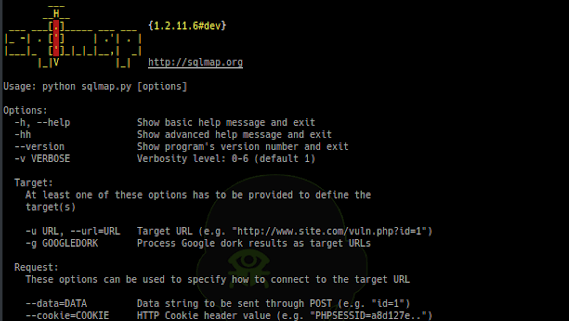 250Exploitation Tools
250Exploitation ToolsSQLMap v1.2.11 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over...
-

 240Geek
240GeekApple’s T2 Security Chip Is Currently Blocking Linux From Booting
Linux enthusiasts must be knowing that one can run Linux distributions on Apple’s older hardware, including the MacBook Air. The quality of...
-

 161Malware
161MalwareWidely Used Cryptocurrency App Launching 2 Different Powerful Backdoor on Mac Users
A cryptocurrency app, CoinTicker which is widely used in cryptocurrency industry pushing 2 different backdoors on Mac users to steal the cryptocurrency coins...
-

 250Exploitation Tools
250Exploitation ToolsPasteJacker – Add PasteJacking To Web-Delivery Attacks
The main purpose of the tool is automating (PasteJacking/Clipboard poisoning/whatever you name it) attack with collecting all the known tricks used in...
-

 270Security Tools
270Security ToolsPython-Nubia – A Command-Line And Interactive Shell Framework
Nubia is a lightweight framework for building command-line applications with Python. It was originally designed for the “logdevice interactive shell (aka. ldshell)”...
-

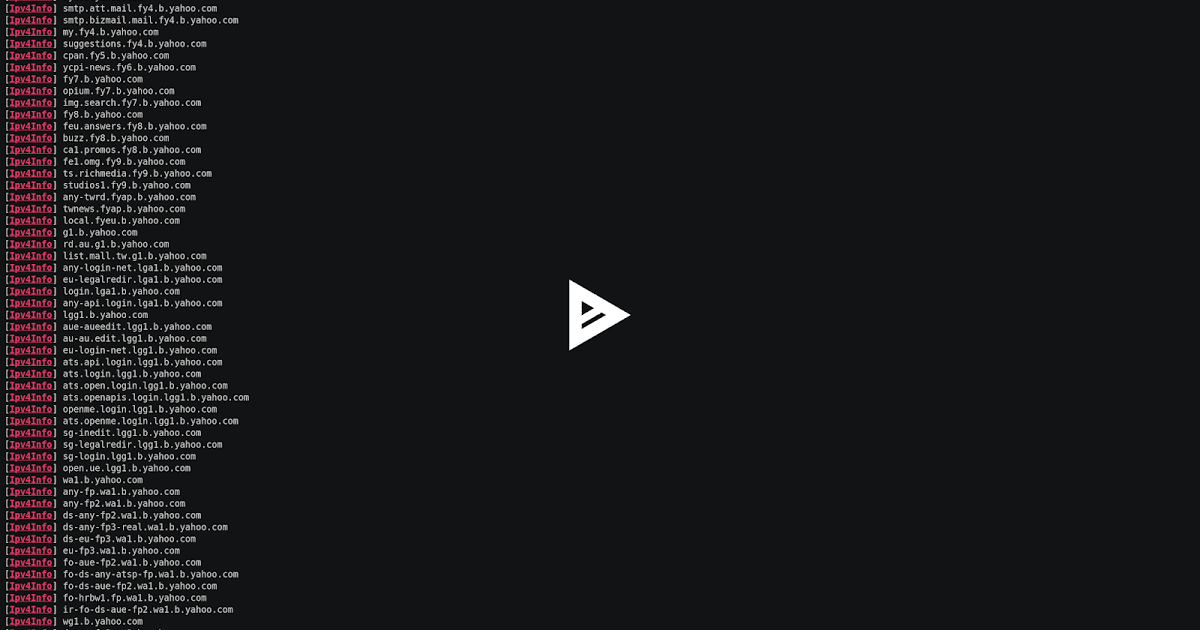
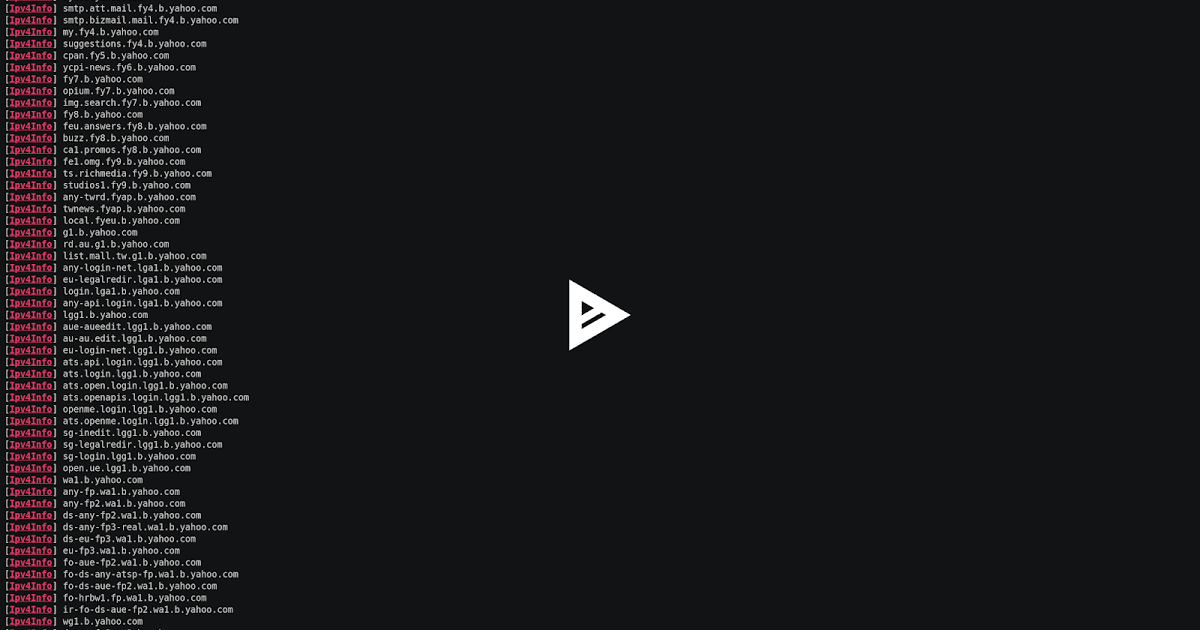
 319Information Gathering
319Information GatheringCT-Exposer – An OSINT Tool That Discovers Sub-Domains By Searching Certificate Transparency Logs
Discover sub-domains by searching through Certificate Transparency logs. What is CT? Certificate Transparency (CT) is an experimental IETF standard. The goal of...
-
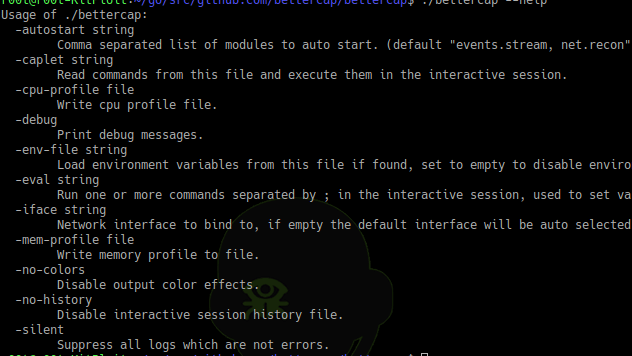
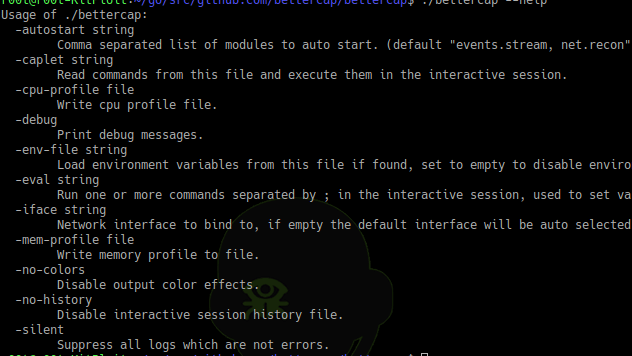 262Man-In-The-Middle
262Man-In-The-MiddleBetterCap v2.10 – The Swiss Army Knife For 802.11, BLE And Ethernet Networks Reconnaissance And MITM Attacks
bettercap is the Swiss Army knife for 802.11, BLE and Ethernet networks reconnaissance and attacks. How to Install A precompiled version is...
-
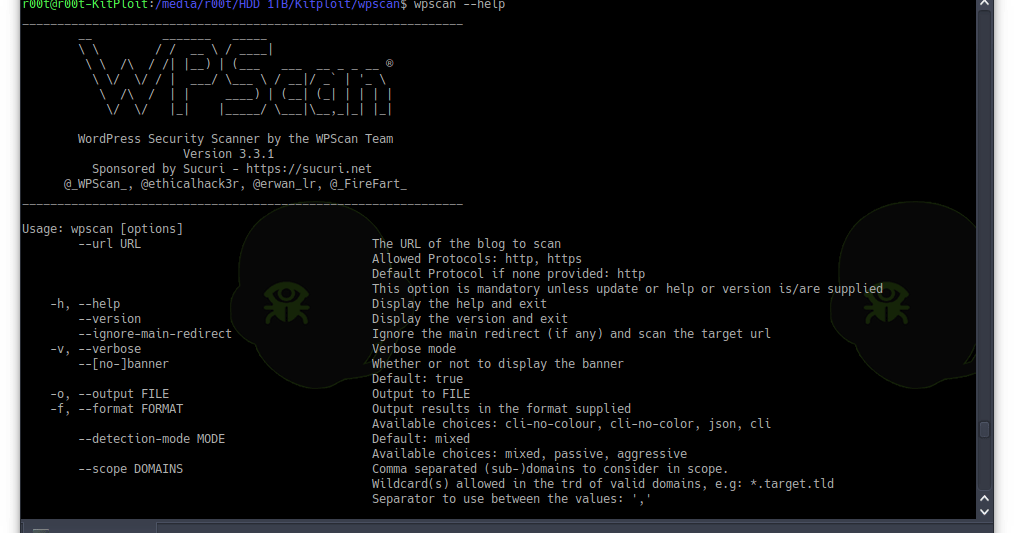
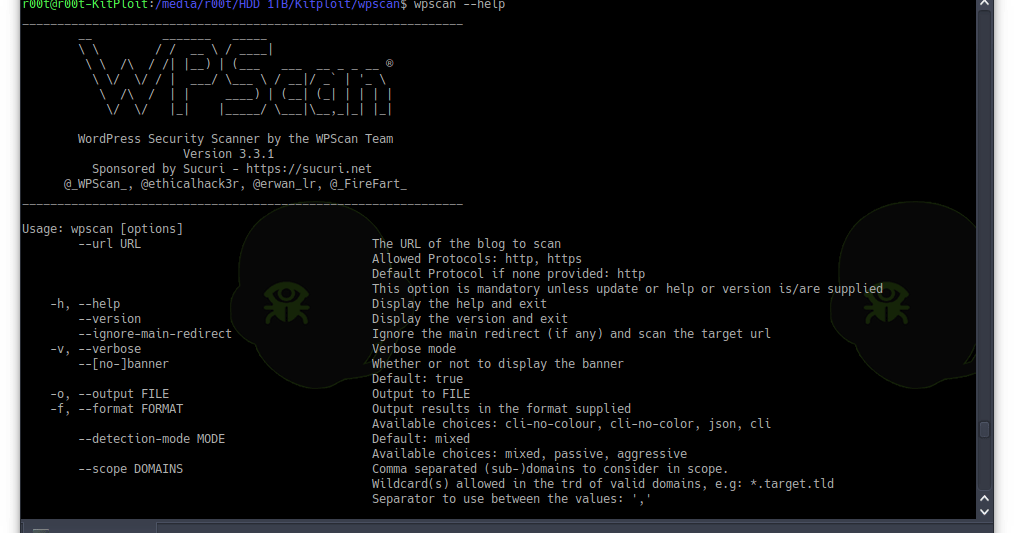 251Vulnerability Analysis
251Vulnerability AnalysisWPScan v3.3.1 – Black Box WordPress Vulnerability Scanner
WPScan is a free, for non-commercial use, black box WordPress vulnerability scanner written for security professionals and blog maintainers to test the...
-
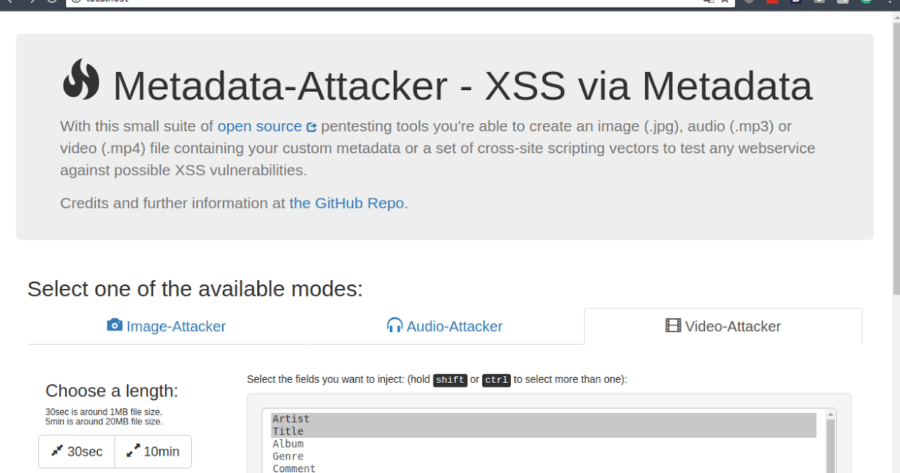
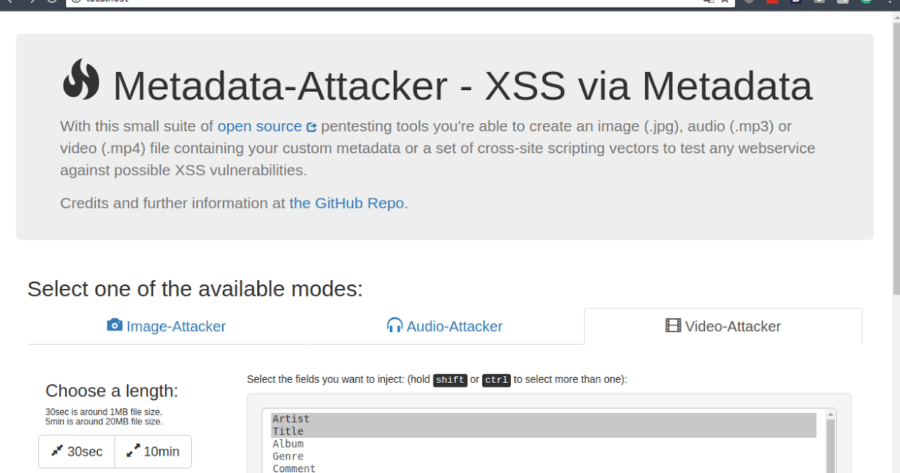 242Exploitation Tools
242Exploitation ToolsMetadata-Attacker – A Tool To Generate Media Files With Malicious Metadata
Metadata-Attacker or a set of cross-site scripting vectors to test any webservice against possible XSS vulnerabilities when displaying unfiltered meta datWith this...
-
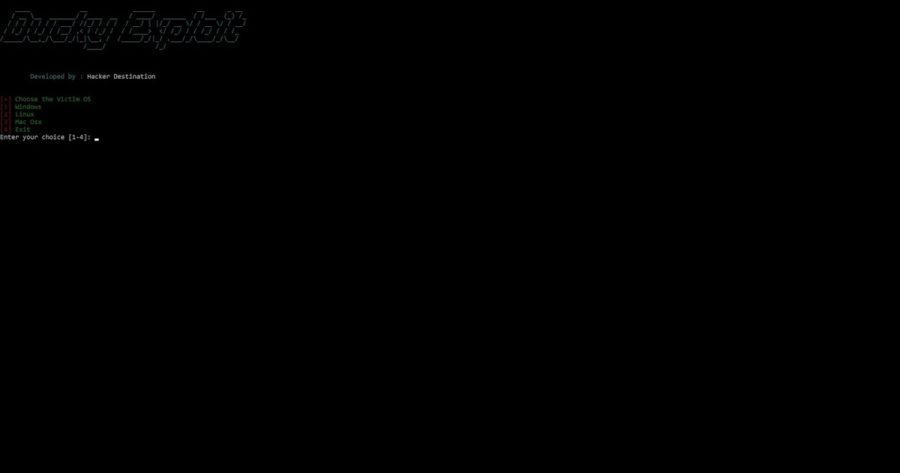
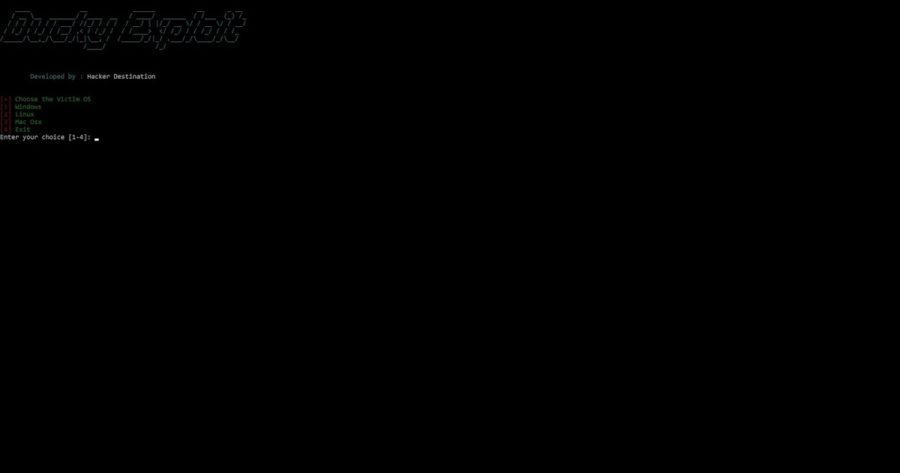 272Exploitation Tools
272Exploitation ToolsDucky-Exploit – Arduino Rubber Ducky Framework
Ducky Exploit is python framework which helps as to code Digispark as Rubber Ducky. This script has been tested on Kali Linux...
-

 345Malware
345MalwareLazarus Group launches Mac malware for the first time
The malware has been spread through a cryptocurrency exchange hack Lazarus Group, the North Korean hacker group responsible for the attack on Sony films...
-
 494Geek
494GeekYou can now run Windows 95 on your Mac, Linux and Windows 10 devices
The maximum RAM that Windows 95 consumes within Windows 10 is just 200 MB. We have seen hackers doing wonders like hacking PlayStation...
-
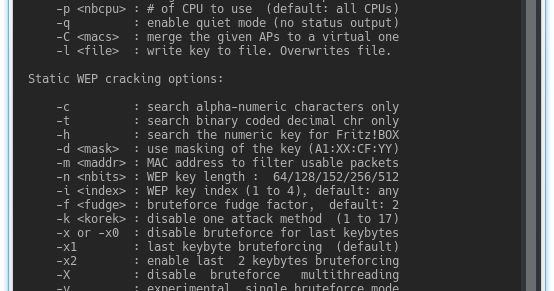
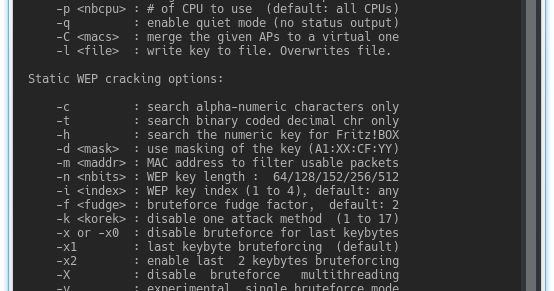 256Network Tools
256Network ToolsAircrack-ng 1.3 – Complete Suite Of Tools To Assess WiFi Network Security
Aircrack-ng is a complete suite of tools to assess WiFi network security. It focuses on different areas of WiFi security: Monitoring: Packet...
-
 266Password Attacks
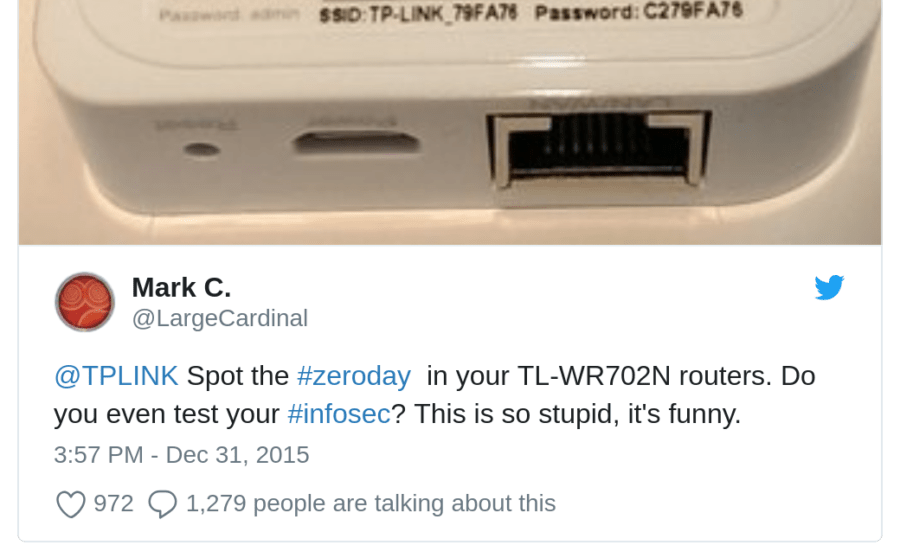
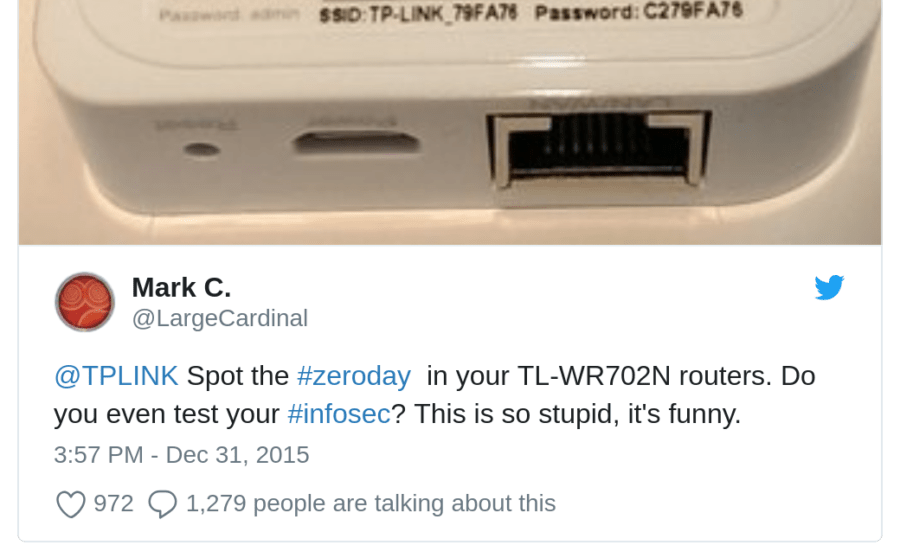
266Password AttacksTP-Link-defaults – Python Script For Trying Default Passwords For Some TP-Link Hotspots
Python script for trying default passwords for some TP-Link Hotspots Inspired by Usage usage: scan.py [-h] [-p] Python script for trying default...
-

 309Geek
309GeekTop 7 Most Popular and Best Cyber Forensics Tools
We often watch experts in movies using forensic tools for their investigations but what cyber forensic tools are used by experts? Well,...
-

 294Geek
294GeekCryptocurrency users on Discord & Slack hit by MacOS malware
Hackers are using a new MacOS malware aimed at cryptocurrency investors on Discord and Slack group chat communities. The malware was initially...
-
 255Wireless Attacks
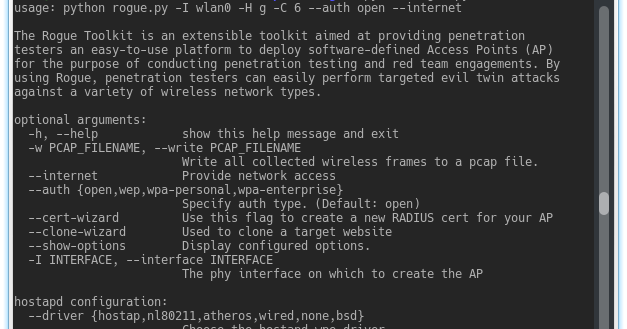
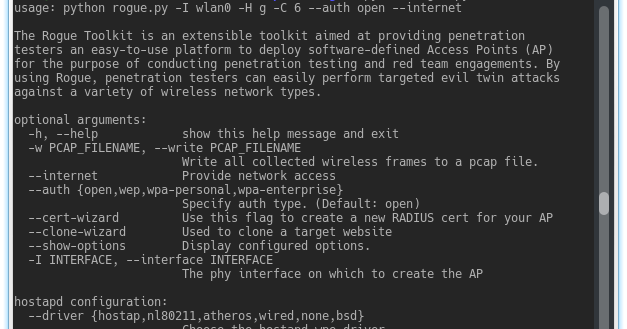
255Wireless AttacksThe Rogue Toolkit – An Extensible Toolkit Aimed At Providing Penetration Testers An Easy-To-Use Platform To Deploy Access Points
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP)...
-
 330Information Gathering
330Information GatheringSubFinder – A Subdomain Discovery Tool That Discovers Valid Subdomains For Websites
SubFinder is a subdomain discovery tool that discovers valid subdomains for websites by using passive online sources. It has a simple modular...
-
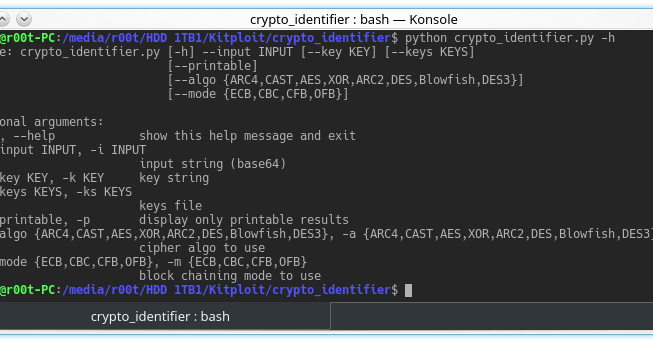
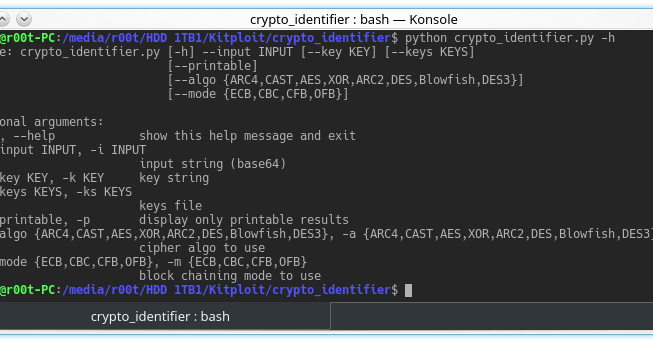 273Cryptography and Encryption
273Cryptography and EncryptionCrypto Identifier – Tool To Uncipher Data Using Multiple Algorithms And Block Chaining Modes
Crypto tool for pentest and ctf : try to uncipher data using multiple algorithms and block chaining modes. Usefull for a quick...






