All posts tagged "malicious"
-

 2.8KMalware
2.8KMalwareFacebook Removes Accounts That Spread Malware to Thousands of People
Researchers have discovered the Facebook account network, which uses Libyan themes and information to spread malware to tens of thousands of people...
-

 1.7KMalware
1.7KMalwareAutomated Malware Analysis in the Cloud
Cybercriminals execute malware attacks using different attack vectors and using different methods. The number of malware strains is increasing in an unprecedented...
-

 3.5KMalware
3.5KMalwareFirefox Send Set To Reform The File Transfer Service Market
For decades, people are using email attachments in order to send files to their intended recipients. However, using emails as a channel...
-

 1.3KData Breach
1.3KData BreachAlmost A Thousand North Korean Defectors in South Korea, Victims Of Data Breach
North Koreans who defected to South Korea are trying to live their lives for the better after they left their original homes....
-

 229Malware
229MalwareMalicious hackers and their interest in bypassing CAPTCHA
Hackers are looking for ways to bypass this security measure The topic is being discussed in multiple hacking forums hosted on deep...
-

 370News
370NewsNew GhostDNS, DNS Changer Botnet Hijacked Over 1,00,000 Routers
Chinese researchers have discovered cyber widely spread the GhostDNS malicious campaign that has captured more than 100,000 home routers and changed their...
-

 222Malware
222MalwareMore than 20 million Chrome users installed fake malicious Ad Blockers
Ad Blockers hurt the earnings of a website at the same time it lets users browse the Internet without the hassle of...
-

 271Information Gathering
271Information GatheringipChecker – Check If A IP Is From Tor Or Is A Malicious Proxy
Tool to check if a given IP is a node tor or an open proxy. Why? Sometimes all your throttles are not...
-
 327Malware
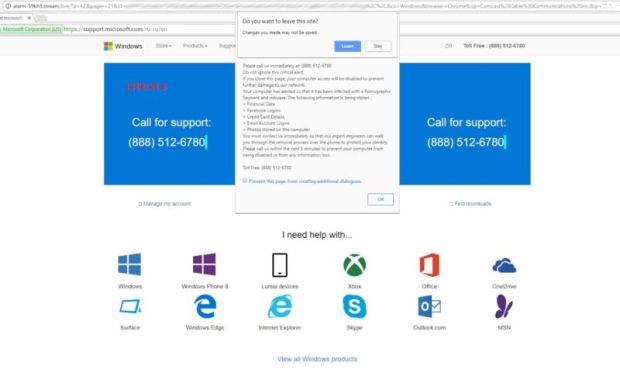
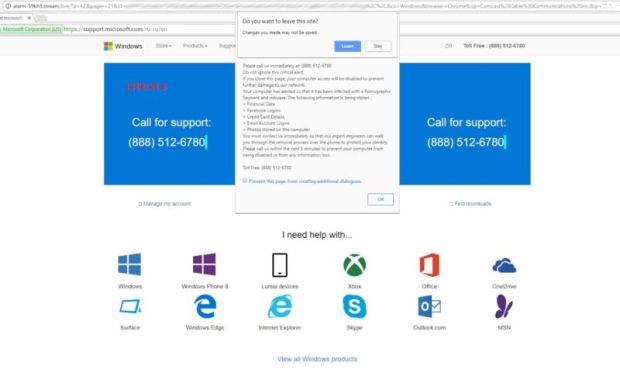
327MalwareHere’s why the epidemic of malicious ads grew so much worse last year
Forced redirects from Zirconium group push phony malware and fake Flash updates. Last year brought a surge of sketchy online ads to...
-
Articles
Google has Removed 60 Apps Containing Malicious Software from the Play Store
The malicious software uncovered pornographic ads and attempted to trick users into buying added services, according to Check Point. “We’ve eliminated the...
-

 152Vulnerabilities
152VulnerabilitiesSuspected Hack Attack Snagging Cell Phone Data Across D.C.
Malicious entity could be tracking phones of domestic, foreign officials. An unusual amount of highly suspicious cellphone activity in the Washington, D.C.,...
-
 206Incidents
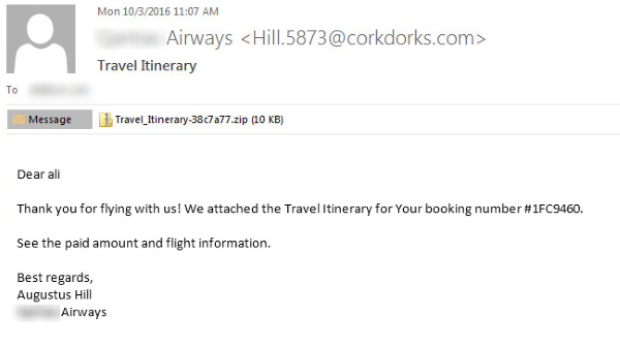
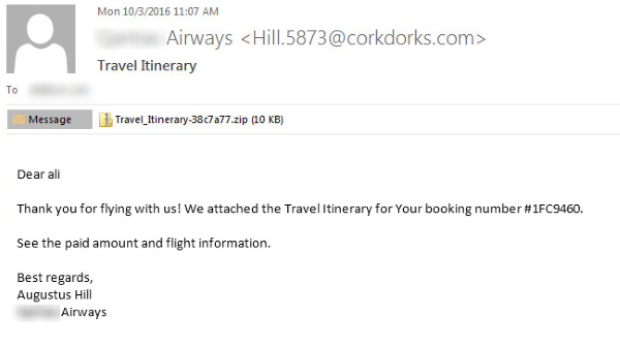
206IncidentsSurge of email attacks using malicious WSF attachments
Ransomware attack groups among the most frequent users of new tactic. Symantec has seen a major increase in the number of email-based...






