All posts tagged "malicious code"
-

 5.2KCyber Attack
5.2KCyber AttackAdvanced Persistent Threat: What You Need to Know
Today, criminal organizations no longer attack corporations and businesses physically with weapons. Instead, they use computers and malware, aiming to steal vital...
-

 401Malware
401MalwareClipsa, The Multi-talented Crypto Asset Thieving Malware
Here in hackercombat.com, we have covered stories about bank trojans on a fairly regular basis. Blackhat hackers are after people’s money, profit...
-

 274Hacked
274HackedPopular JavaScript Library Infected By Malicious Code To Steal Cryptocurrency
A malicious code has infected Event-stream JavaScript library with the intention of stealing cryptocurrency from digital wallets. The popular JavaScript library is...
-

 197Data Security
197Data SecurityFeature to attach video to Word files could be used to send malicious code
Hackers could abuse a feature that allows you to attach a video directly to a Word document for the victim to download...
-
 194Malware
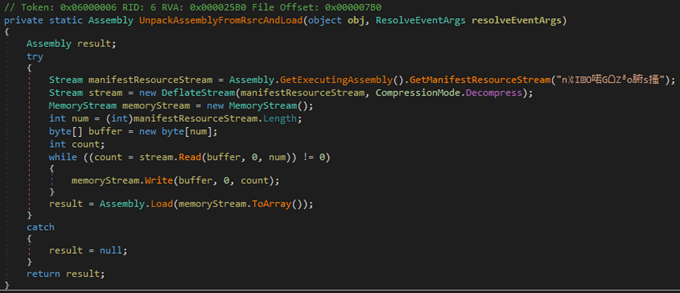
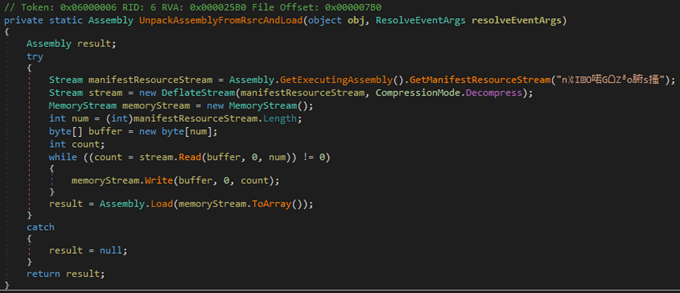
194MalwareUsing legitimate tools to hide malicious code
The authors of malware use various techniques to circumvent defensive mechanisms and conceal harmful activity. One of them is the practice of...
-
 247Incidents
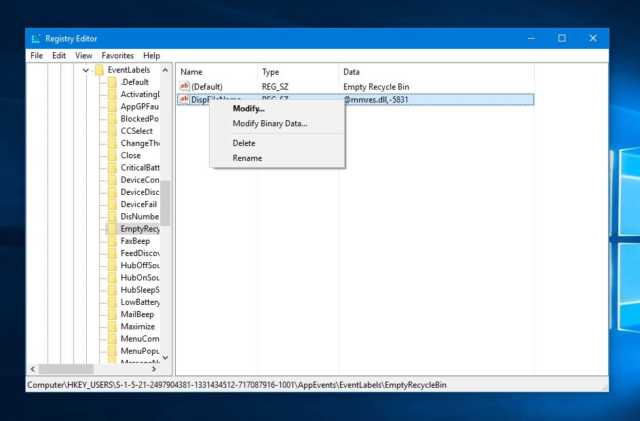
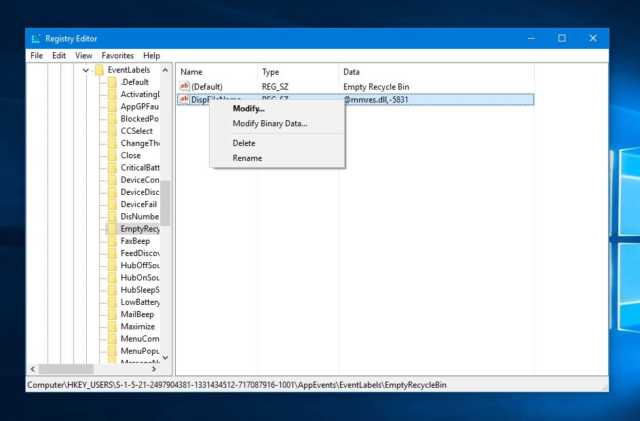
247IncidentsSimple Registry Hacks Bypass Windows Digital Signature, Opening Gates For Malicious Code
Windows Digital Signature check is a mechanism included in Microsoft Windows to make sure that the software or driver you’re trying to...
-

 183Data Security
183Data SecurityWidely used WebEx plugin for Chrome will execute attack code—patch now!
Publicly known “magic string” lets any site run malicious code, no questions asked. The Chrome browser extension for Cisco Systems WebEx communications...
-
 149Incidents
149IncidentsEC Council Website Hacked and used to serve malicious code
Researchers at Fox-IT warn that the website of security certification provider EC Council has been compromised to host the malicious Angler Exploit...






