All posts tagged "Malware analysis tools"
-

 423Malware
423MalwareA Complete Malware Analysis Tutorials, Cheatsheet & Tools list for Security Professionals
Analysing the malware to breakdown its function and infection routine is a kind of tough job. here we describing the complete Malware...
-
 576Infosec
576InfosecMost Important Security Tools and Resources For Security Researcher and Malware Analyst
Security Professionals always need to learn many tools, techniques, and concepts to analyze sophisticated Threats and current cyber attacks. Hex Editors HxD...
-

 1.7KMalware
1.7KMalwareAutomated Malware Analysis in the Cloud
Cybercriminals execute malware attacks using different attack vectors and using different methods. The number of malware strains is increasing in an unprecedented...
-

 294Infosec
294InfosecFLASHMINGO – Free Threat Intelligence Tool for Malware Analysts’ to Analyse Flash Exploits
FireEye released a Free automated analysis tool FLASHMINGO, which enables malware analysts to detect suspicious flash samples and to investigate them. The...
-

 418Malware
418MalwareBest Ways to Remove Trojans, Malware and Viruses From Your Android Phone
According to MalwareBytes’s 2019 State of Malware Report, Trojans and crypto miners are the dominate malware threats of 2019. Android phones may...
-

 326Malware Analysis
326Malware AnalysisMalware Analysis Tools and Cheat list
A large number of computer intrusions involve some form of malicious software (malware), which finds its way to the victim’s workstation or...
-
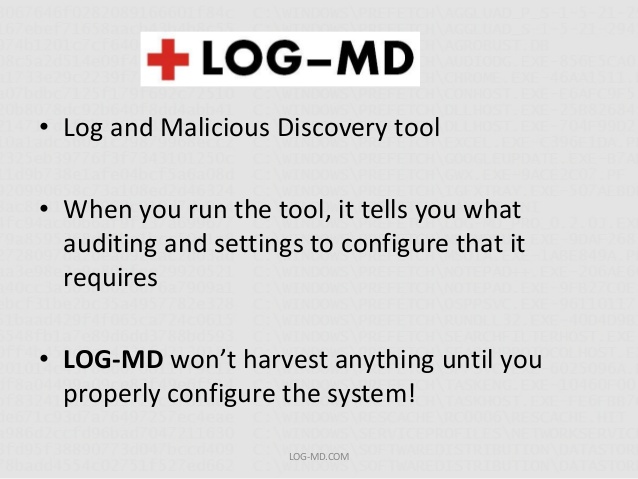
 238Hack Tools
238Hack ToolsLOG-MD – Log Malicious Detection tool
LOG-MD was designed for Windows based systems to audit log and advanced audit policy settings and guide users to enable and configure...






