All posts tagged "malware"
-
 313Data Security
313Data SecurityNew Trojan Turns Linux Devices into Botnet
New Linux Trojan turns infected Linux Devices and websites into P2P botnets and threatens users with DDoS and ransom! — This Trojan...
-

 97Cyber Crime
97Cyber Crime7 Cases When Victims Paid Ransom to stop cyber attacks
These cases include ransomware infection and DDoS attacks! Enjoy Everyone has been talking about the growing threat of ransomware and non-stop distributed...
-

 301News
301NewsDonald Trump Campaign Hacked; Targeted with Malware: Report
Republican and Democratic Networks’ Computer Systems were hacked — Attackers also hacked Donald Trump’s election campaign staff! The computer systems of Presidential candidate Donald...
-
 223Cyber Crime
223Cyber CrimeBeware; Hackers targeting Pokemon Go Users with Smishing Scam
Pokemon Go Game Inspiring one Scam After Another — After malware and RAT infected apps here comes Pokemon Go smishing (SMS Phishing) scam!...
-

 260Geek
260GeekScammers Used Google AdSense to Drop Malware on Android Devices
Google AdSense targeted by Malware mimicking as Login Pages of Popular Websites and Apps Keystroke logging malware has become the most dangerous...
-
 83Incidents
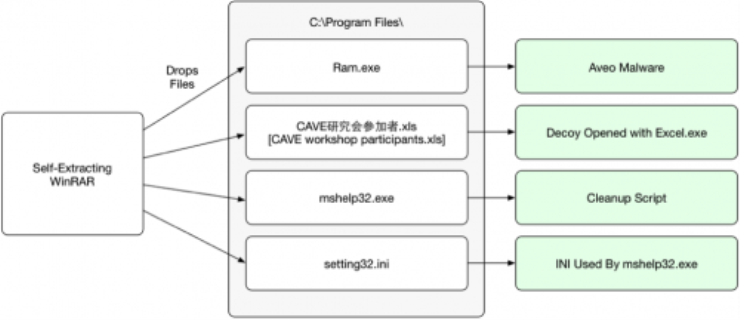
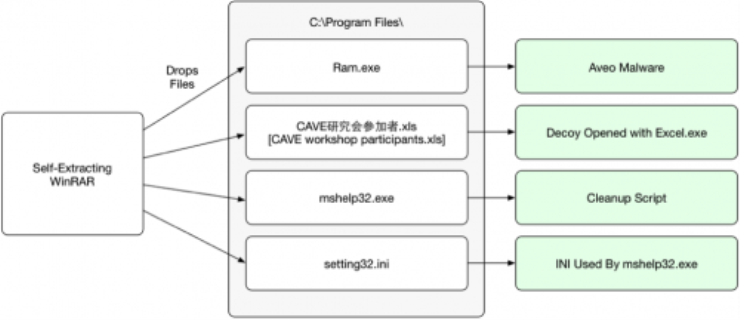
83IncidentsAveo Trojan Used in Attacks Against Japanese Users
Palo Alto Networks has identified a malware family known as ‘Aveo’ that is being used to target Japanese speaking users. The ‘Aveo’...
-

 304News
304NewsWikiLeaks Turkish AKP Email Dumps Contain Malware; Researcher
Last month Wikileaks published emails stolen from Turkish ruling party AKP — Now, a researcher has presented a report showing the AKP...
-
 364News
364NewsHackers Claim Stealing NSA Hacking Tools; Selling Them Online
Shadow Brokers hacking group is claiming that it hacked NSA’s Equation Group and stole a trove of hacking tools and exploits! Hackers are...
-

 173Malware
173MalwareResearchers Hide Malware Inside Digitally-Signed Files Without Breaking Hashes
New technique makes malware detection almost impossible. A team of security researchers from Deep Instinct have discovered a method of injecting malware inside...
-
 194Data Security
194Data SecurityResearchers crack open unusually advanced malware that hid for 5 years
Espionage platform with more than 50 modules was almost certainly state sponsored. Security experts have discovered a malware platform that’s so advanced in...
-

 195Incidents
195IncidentsOracle-owned point-of-sale service suffers from malware attack
A Russian organized cybercrime group known for hacking into banks and retailers appears to have breached hundreds of computer systems at software giant...
-

 195Malware
195MalwareKazakhstan Government Uses Malware to Spy on Journalists and Political Activists
EFF exposes threat group operating for Kazakhstan regime. The Electronic Frontier Foundation (EFF) has released a report today named Operation Manul that details...
-

 186Incidents
186IncidentsHow hackers used this Trojan malware to spy on a territorial dispute
F-Secure researchers say parties involved in the South China Sea arbitration case were infected with the data-stealing NanHaiShu Trojan. Hackers have used...
-

 412Geek
412GeekBeware of Fake Android Prisma Apps Running Phishing, Malware Scam
Beware of fake Prisma photo editing app on Android store targeting users with phishing and malware scam! Prisma app for Android users was launched...
-
 74Incidents
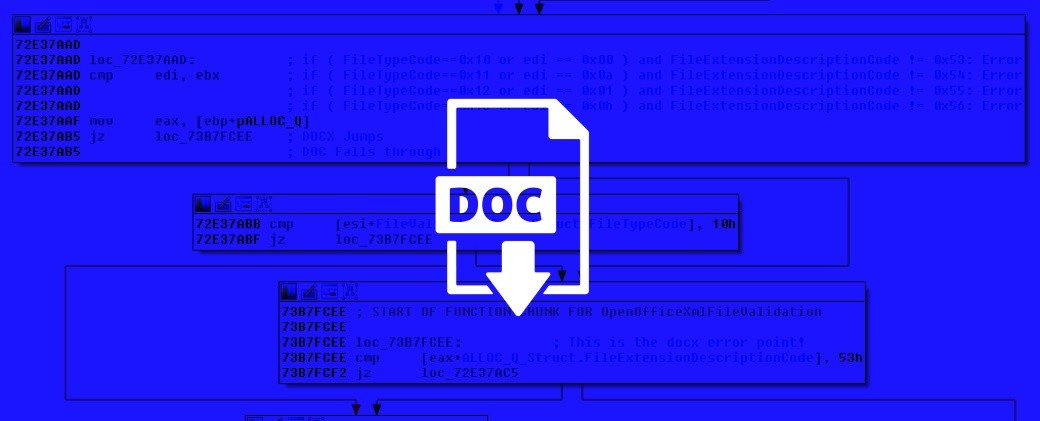
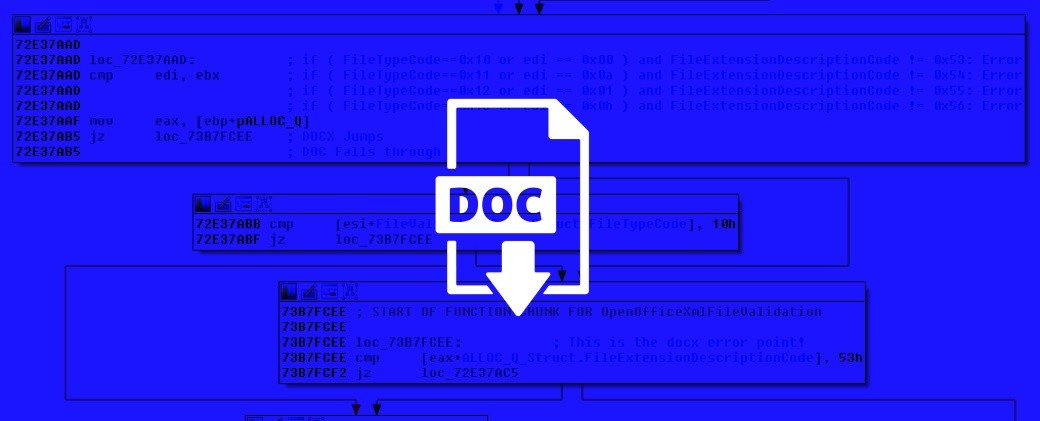
74IncidentsRenaming Office Files Is Enough to Disguise Macro Malware
Macros have been used since the mid 1990s to spread malware and infect systems. Increased user awareness of the need to disable...
-
 320Cyber Crime
320Cyber CrimeScammers Using Genuine PayPal Emails to Spread Banking Malware
Another day another PayPal scam — This time, it’s highly sophisticated and comes from a genuine PayPal email address! PayPal like other financial institutions...
-

 178Data Security
178Data SecurityHow Illegal Streaming is Putting Your Security at Risk
There’s no such thing as a free ticket: How Illegal streaming is putting your security at risk It’s an expensive business being...
-
 114News
114NewsClash of Kings forum Breached; 1.6 Million Users’ Accounts Stolen
Another day another hack: Clash of Kings, one of the world’s most famous games on smartphones has its forum hacked, data stolen!...
-

 329Data Security
329Data SecurityHow to secure your cyber infrastructure from threats like ransomware?
The Internet is a great place to do business and cybercriminals are aware of that fact so how can you protect your networks,...
-
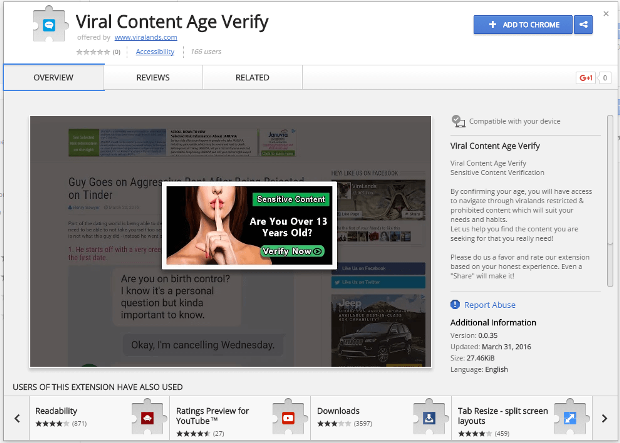
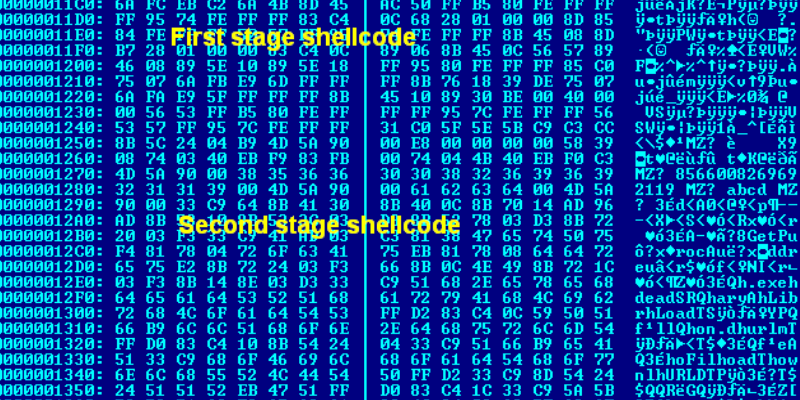
 144Data Security
144Data SecurityMalware in the browser: how you might get hacked by a Chrome extension
Increasingly, browsers are taking on a central role in our daily lives. With web apps for everything, we have placed our most...
-
 128Data Security
128Data SecurityCVE-2015-1641 and CVE-2015-2545 Are Today’s Most Popular Microsoft Word Exploits
Office exploit kits updates drop support for CVE-2012-0158. Two newer vulnerabilities targeting the Microsoft Office suite have become very popular in recent months,...






