All posts tagged "malware"
-
 3.0KMalware
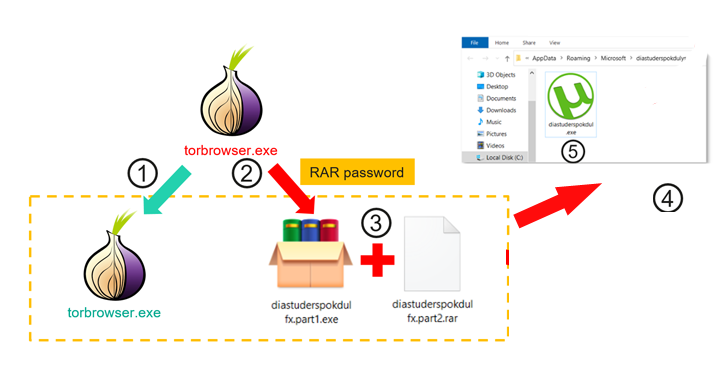
3.0KMalwareTrojanized TOR Browser Installers Spreading Crypto-Stealing Clipper Malware
Trojanized installers for the TOR anonymity browser are being used to target users in Russia and Eastern Europe with clipper malware designed...
-
 2.5KMalware
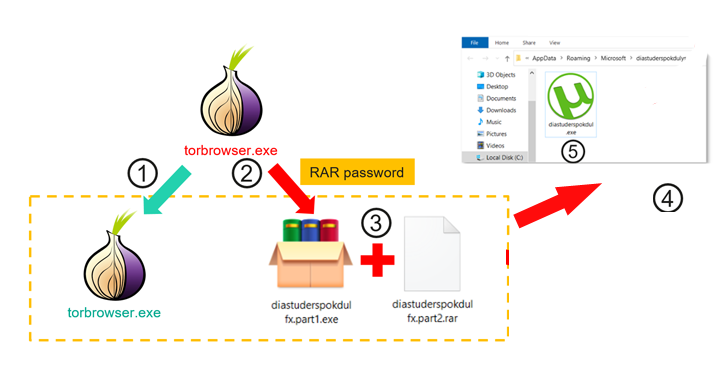
2.5KMalwareMicrosoft Introduces GPT-4 AI-Powered Security Copilot Tool to Empower Defenders
Microsoft on Tuesday unveiled Security Copilot in limited preview, marking its continued quest to embed AI-oriented features in an attempt to offer...
-
 4.5KMalware
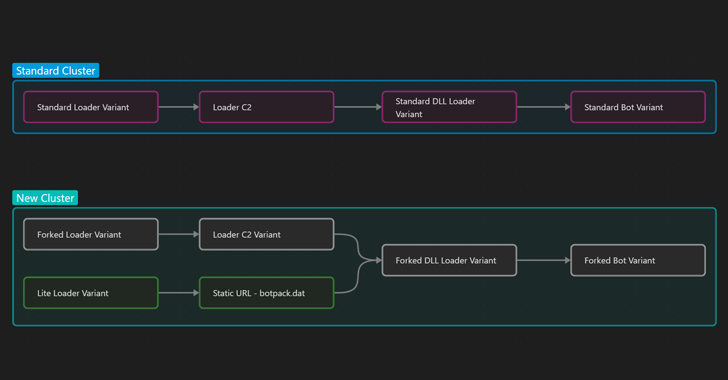
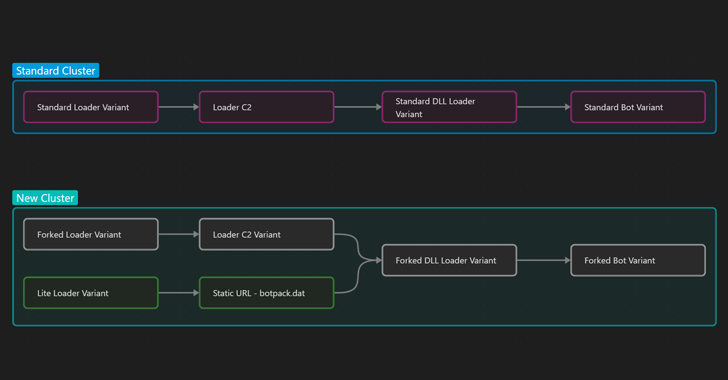
4.5KMalwareIcedID Malware Shifts Focus from Banking Fraud to Ransomware Delivery
Multiple threat actors have been observed using two new variants of the IcedID malware in the wild with more limited functionality that...
-

 1.5KMalware
1.5KMalwareStealthy DBatLoader Malware Loader Spreading Remcos RAT and Formbook in Europe
A new phishing campaign has set its sights on European entities to distribute Remcos RAT and Formbook via a malware loader dubbed...
-
 882Malware
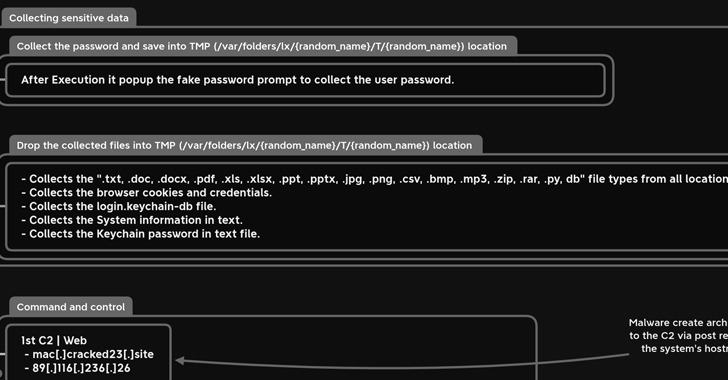
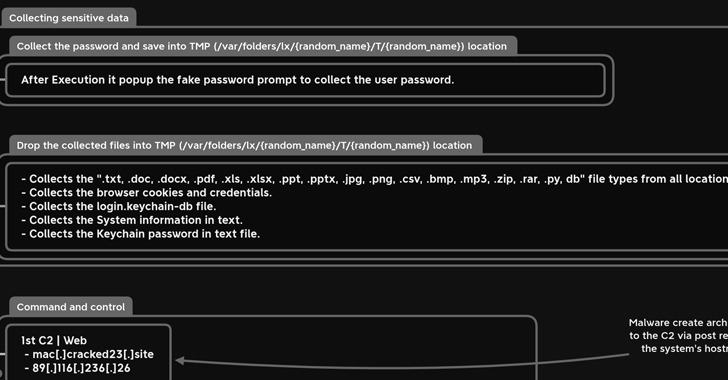
882MalwareNew MacStealer macOS Malware Steals iCloud Keychain Data and Passwords
A new information-stealing malware has set its sights on Apple’s macOS operating system to siphon sensitive information from compromised devices. Dubbed MacStealer,...
-

 1.9KMalware
1.9KMalwareMalicious Python Package Uses Unicode Trickery to Evade Detection and Steal Data
A malicious Python package on the Python Package Index (PyPI) repository has been found to use Unicode as a trick to evade...
-
 733Malware
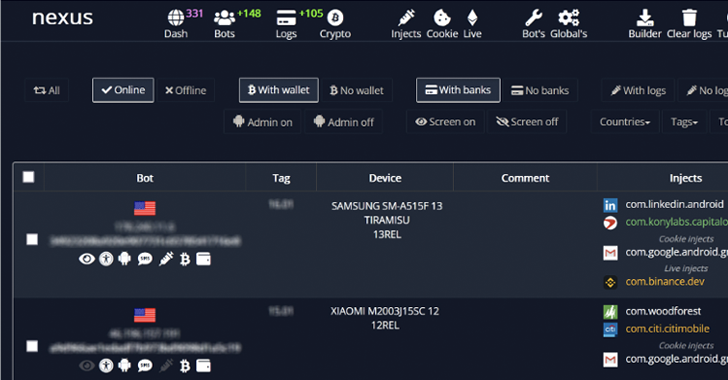
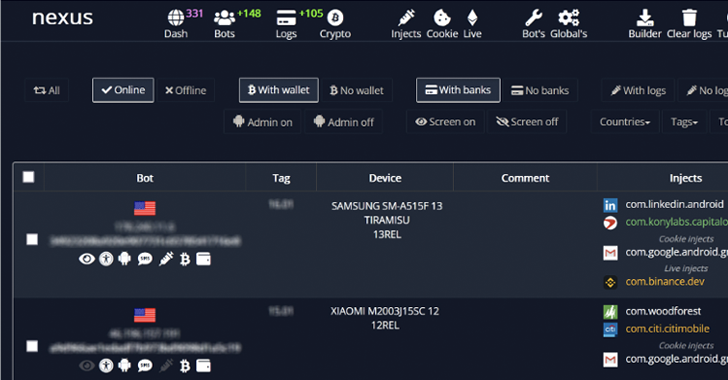
733MalwareNexus: A New Rising Android Banking Trojan Targeting 450 Financial Apps
An emerging Android banking trojan dubbed Nexus has already been adopted by several threat actors to target 450 financial applications and conduct...
-

 3.2KCyber Attack
3.2KCyber AttackOperation Soft Cell: Chinese Hackers Breach Middle East Telecom Providers
Telecommunication providers in the Middle East are the subject of new cyber attacks that commenced in the first quarter of 2023. The...
-
Malware
ScarCruft’s Evolving Arsenal: Researchers Reveal New Malware Distribution Techniques
The North Korean advanced persistent threat (APT) actor dubbed ScarCruft is using weaponized Microsoft Compiled HTML Help (CHM) files to download additional...
-
 1.6KMalware
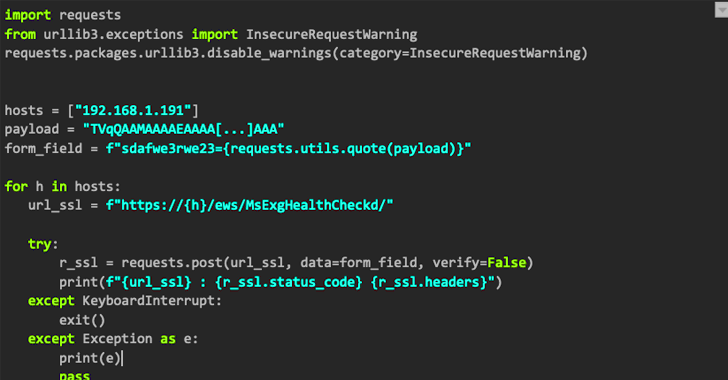
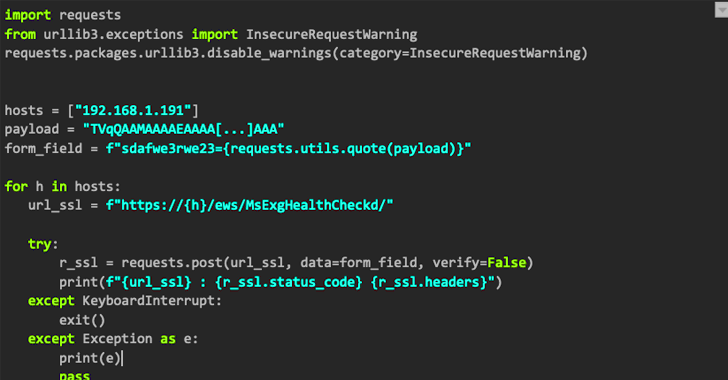
1.6KMalwareNAPLISTENER: New Malware in REF2924 Group’s Arsenal for Bypassing Detection
The threat group tracked as REF2924 has been observed deploying previously unseen malware in its attacks aimed at entities in South and...
-
 796Malware
796MalwareNew ShellBot DDoS Malware Variants Targeting Poorly Managed Linux Servers
Poorly managed Linux SSH servers are being targeted as part of a new campaign that deploys different variants of a malware called...
-
 4.4KMalware
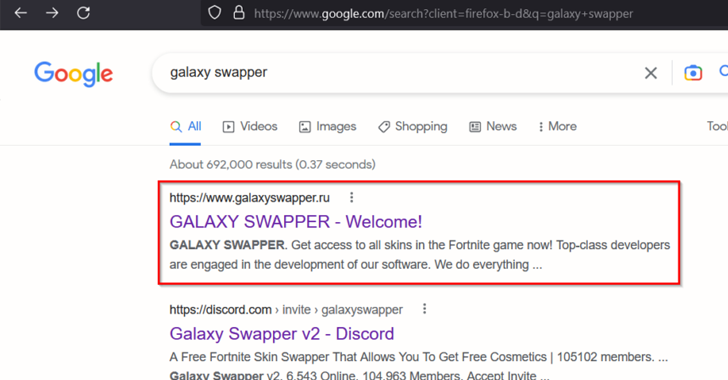
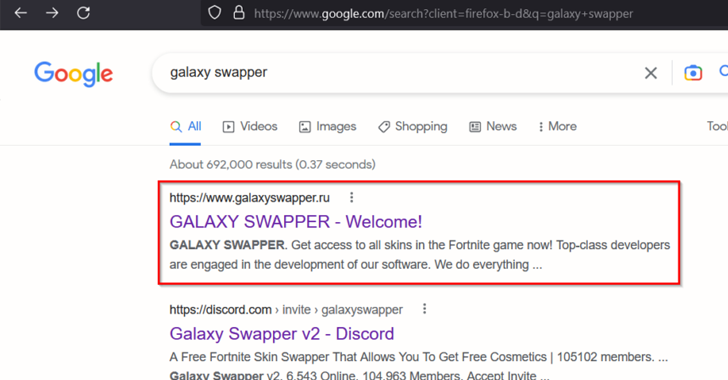
4.4KMalwareNew DotRunpeX Malware Delivers Multiple Malware Families via Malicious Ads
A new piece of malware dubbed dotRunpeX is being used to distribute numerous known malware families such as Agent Tesla, Ave Maria,...
-
 3.9KMalware
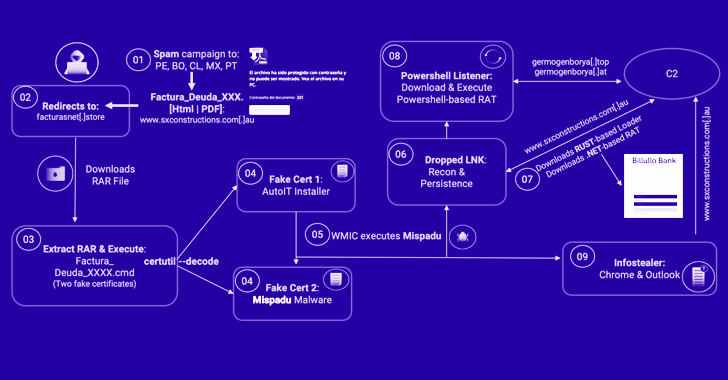
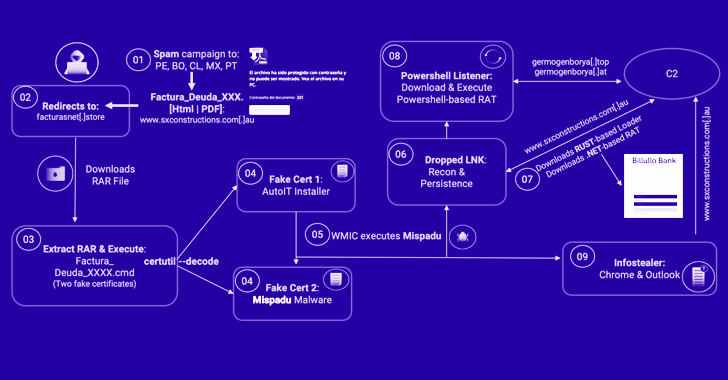
3.9KMalwareMispadu Banking Trojan Targets Latin America: 90,000+ Credentials Stolen
A banking trojan dubbed Mispadu has been linked to multiple spam campaigns targeting countries like Bolivia, Chile, Mexico, Peru, and Portugal with...
-
 3.0KMalware
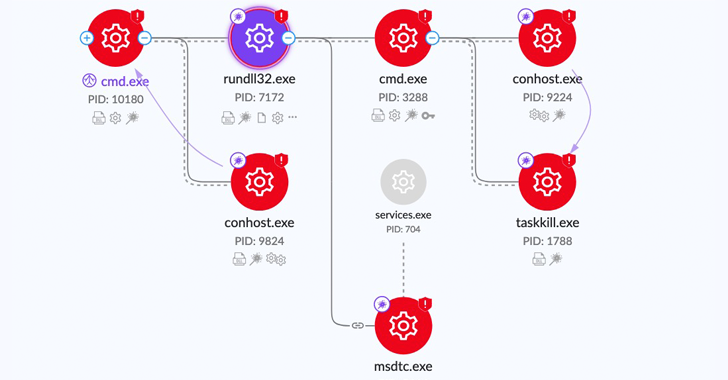
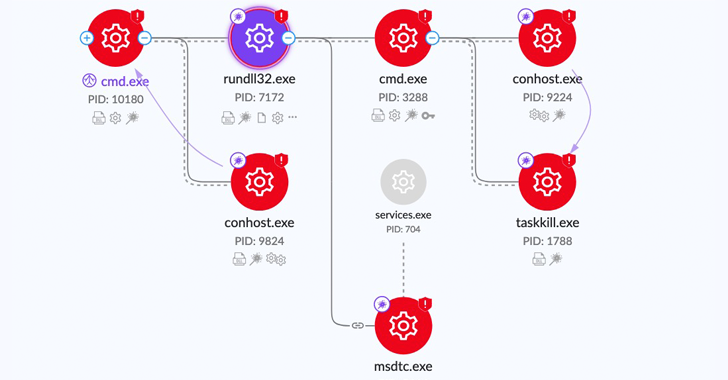
3.0KMalwareResearchers Shed Light on CatB Ransomware’s Evasion Techniques
The threat actors behind the CatB ransomware operation have been observed using a technique called DLL search order hijacking to evade detection...
-

 1.2KMalware
1.2KMalwareEmotet Rises Again: Evades Macro Security via OneNote Attachments
The notorious Emotet malware, in its return after a short hiatus, is now being distributed via Microsoft OneNote email attachments in an...
-

 3.5KMalware
3.5KMalwareLockBit 3.0 Ransomware: Inside the Cyberthreat That’s Costing Millions
U.S. government agencies have released a joint cybersecurity advisory detailing the indicators of compromise (IoCs) and tactics, techniques, and procedures (TTPs) associated...
-

 3.0KMalware
3.0KMalwareFakeCalls Vishing Malware Targets South Korean Users via Popular Financial Apps
An Android voice phishing (aka vishing) malware campaign known as FakeCalls has reared its head once again to target South Korean users...
-
 2.2KMalware
2.2KMalwareA New Security Category Addresses Web-borne Threats
In the modern corporate IT environment, which relies on cloud connectivity, global connections and large volumes of data, the browser is now...
-
 2.4KMalware
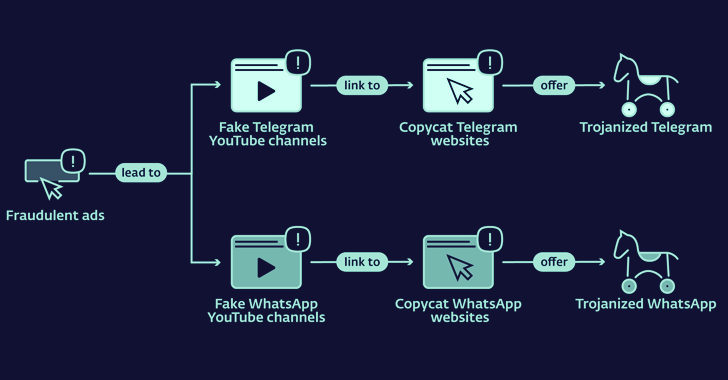
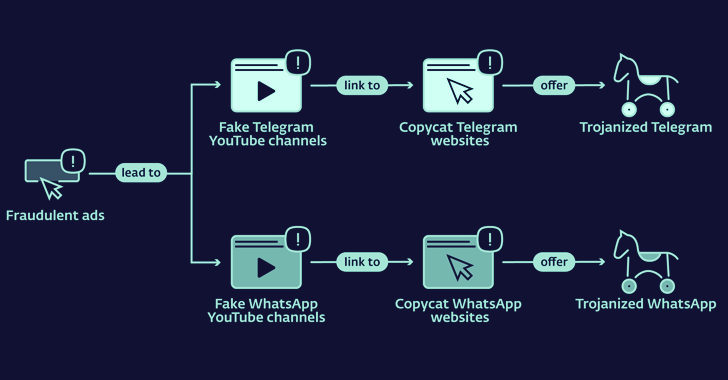
2.4KMalwareLookalike Telegram and WhatsApp Websites Distributing Cryptocurrency Stealing Malware
Copycat websites for instant messaging apps like Telegram and WhatApp are being used to distribute trojanized versions and infect Android and Windows...
-
 3.0KMalware
3.0KMalwareChinese and Russian Hackers Using SILKLOADER Malware to Evade Detection
Threat activity clusters affiliated with the Chinese and Russian cybercriminal ecosystems have been observed using a new piece of malware that’s designed...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesMicrosoft Rolls Out Patches for 80 New Security Flaws — Two Under Active Attack
Microsoft’s Patch Tuesday update for March 2023 is rolling out with remediations for a set of 80 security flaws, two of which...






