All posts tagged "malware"
-

 1.5KCyber Crime
1.5KCyber Crime9 apps with 6M installs stole Facebook logins of Android users
All 9 malicious apps were found on Google Play Store. In recent news, a research team of malware analysts from Dr. Web...
-
 1.4KGeek
1.4KGeekWindows Defender update caught removing zip, exe, source code files
Reportedly, the Windows Defender daily update flagged DeCSS DVD encryption software copy as a Trojan and quarantined it before deleting it after...
-

 4.4KCyber Crime
4.4KCyber CrimeColombia arrests suspect wanted by US over Gozi virus
The suspect, Mihai Ionut Paunescu, was already arrested by the Romanian authorities in December 2012 but managed to avoid extradition to the...
-

 3.7KData Security
3.7KData Security6 official Python repositories plagued with cryptomining malware
Researchers at security firm Sonatype have uncovered six malicious typosquatting packages in the official Python programming language’s PyPI repository, laced with cryptomining malware. Sonatype...
-

 4.5KCyber Events
4.5KCyber EventsCrippling attack on Iranian trains linked to Meteor file wiper malware
The Meteor file wiper malware is linked to a cyberattack that took place on July 9th, 2021 on the Iranian railway system...
-

 4.8KCyber Crime
4.8KCyber CrimeThe Threat of Ransomware on the Rise in 2021
As if we didn’t have enough threats on our plate to deal with. Did you know in 2018, ransomware attacks worldwide grew...
-
 3.8KNews
3.8KNewsDarkRadiation ransomware targeting RedHat, Debian Linux distributions
The newly discovered DarkRadiation ransomware chain is unlike any other ransomware family. Trend Micro cybersecurity researchers have shared findings of a newly identified ransomware...
-

 789Data Security
789Data SecurityNameless malware stole 26m login credentials from 3.25m computers
The total amount of data collected by the malware includes nearly 26 million login credentials holding 1.1 million unique email addresses, 2...
-
 3.2KCyber Crime
3.2KCyber CrimeThreat actors using Google Docs exploit to spread phishing links
Cybercriminals have started employing a new phishing attack that abuses the popularity of Google Drive and Docs to bypass security filters. In...
-

 1.4KNews
1.4KNewsWatch out Android users as Joker malware is back on Play Store
The researchers managed to identify and report the presence of Joker malware in 8 apps on Google Play Store. In the past...
-
 1.2KData Security
1.2KData SecurityNew malware blocks victims from visiting The Pirate Bay, illegal sites
Dubbed Vigilante by researchers; the malware prevents the system from those sites that redistribute pirated software/data. The IT security researchers at SophosLabs have...
-

 4.7KMalware
4.7KMalwareRussian Ransomware Group REvil Back Online After 2-Month Hiatus
The operators behind the REvil ransomware-as-a-service (RaaS) staged a surprise return after a two-month hiatus following the widely publicized attack on technology...
-

 2.7KMalware
2.7KMalware3 Ways to Secure SAP SuccessFactors and Stay Compliant
The work-from-anywhere economy has opened up the possibility for your human resources team to source the best talent from anywhere. To scale...
-
 5.0KMalware
5.0KMalwareNew 0-Day Attack Targeting Windows Users With Microsoft Office Documents
Microsoft on Tuesday warned of an actively exploited zero-day flaw impacting Internet Explorer that’s being used to hijack vulnerable Windows systems by...
-
 1.0KMalware
1.0KMalwareTraffic Exchange Networks Distributing Malware Disguised as Cracked Software
An ongoing campaign has been found to leverage a network of websites acting as a “dropper as a service” to deliver a...
-
 4.1KCyber Attack
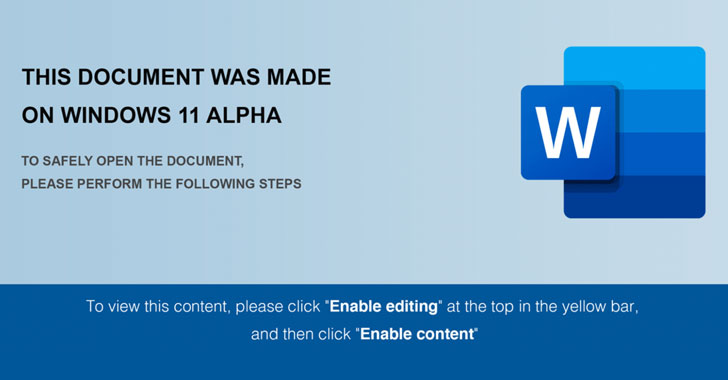
4.1KCyber AttackFIN7 Hackers Using Windows 11 Themed Documents to Drop Javascript Backdoor
A recent wave of spear-phishing campaigns leveraged weaponized Windows 11 Alpha-themed Word documents with Visual Basic macros to drop malicious payloads, including...
-
 4.9KMalware
4.9KMalwareChinese Authorities Arrest Hackers Behind Mozi IoT Botnet Attacks
The operators of the Mozi IoT botnet have been taken into custody by Chinese law enforcement authorities, nearly two years after the...
-
 5.2KMalware
5.2KMalwareCybercriminals Abusing Internet-Sharing Services to Monetize Malware Campaigns
Threat actors are capitalizing on the growing popularity of proxyware platforms like Honeygain and Nanowire to monetize their own malware campaigns, once...
-

 3.4KMalware
3.4KMalwareFIN8 APT Hackers Attacks Financial Institutions Using Sophisticated Backdoor
The security analysts from the cybersecurity firm Bitdefender have recently noted the new backdoor BADHATCH malware that was being used by the...
-
 812Malware
812MalwareResearchers Uncover FIN8’s New Backdoor Targeting Financial Institutions
A financially motivated threat actor notorious for setting its sights on retail, hospitality, and entertainment industries has been observed deploying a completely...
-

 4.7KCyber Attack
4.7KCyber AttackNew SideWalk Backdoor Targets U.S.-based Computer Retail Business
A computer retail company based in the U.S. was the target of a previously undiscovered implant called SideWalk as part of a...






