All posts tagged "MITM"
-
 316Tutorials
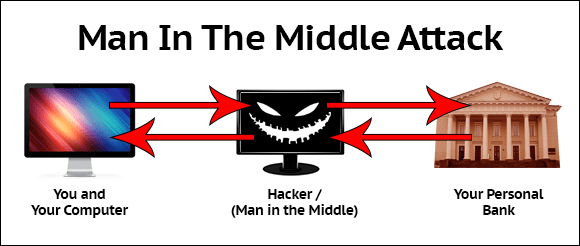
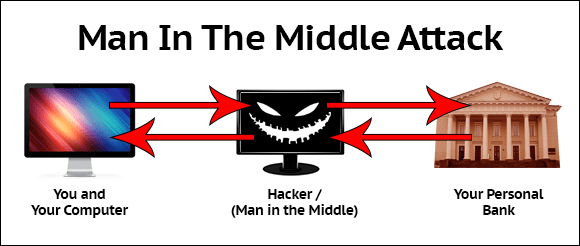
316TutorialsMonitor traffic using MITM (Man in the middle attack)
MITM INRO :- MITM (Man in the middle attack) is a another method where attacker’s sniff the running sessions in a network....
-

 323Data Security
323Data SecurityUpdate your devices: New Bluetooth flaw lets attackers monitor traffic
The Bluetooth flaw also opens door to a man-in-the-middle attack. The IT security researchers at Israel Institute of Technology have discovered a critical security vulnerability in...
-

 277Man-In-The-Middle
277Man-In-The-Middleratched – Transparent Man-in-the-Middle TLS Proxy
ratched is a Man-in-the-Middle (MitM) proxy that specifically intercepts TLS connections. It is intended to be used in conjunction with the Linux...
-
 272Man-In-The-Middle
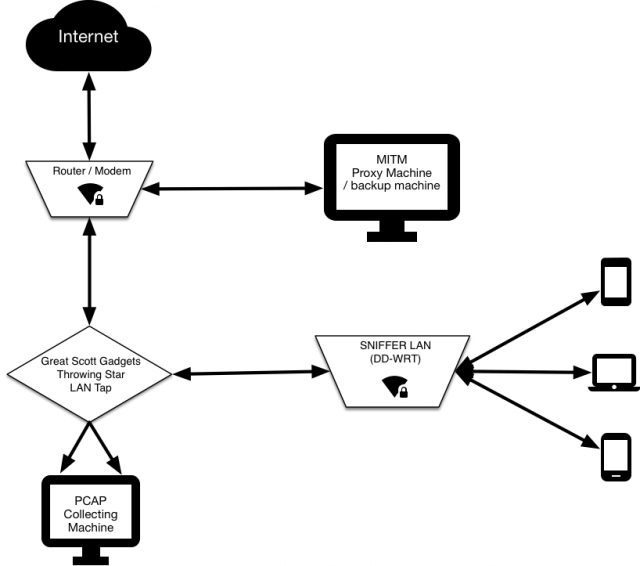
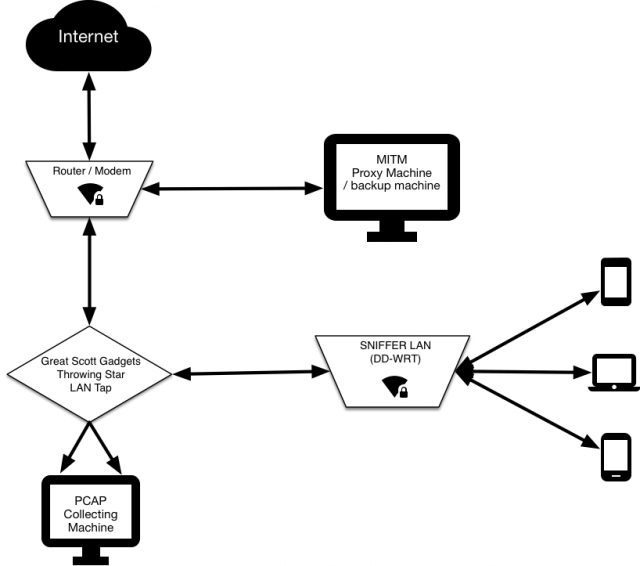
272Man-In-The-MiddleSNIFFlab – Create Your Own MITM Test Environment
Essentially it’s a WiFi hotspot that is continually collecting all the packets transmitted across it. All connected clients’ HTTPS communications are subjected...
-
 498How To
498How ToHow To Do Man in the Middle Attack in Kali Linux
Currently, in this tutorial, we are going to perform the man in the middle attack using Kali Linux. Man in the middle...
-

 223How To
223How ToSetting up Ettercap for Man in the Middle Attacks
PenTest Magazine describes a cyber-attack as the following: Man in the middle attacks (or MITMs) are no different. They’re extremely useful in...






