All posts tagged "MitM attacks"
-

 282News
282NewsGoogle to Block Sign-ins from Embedded Browser Frameworks
In a bid to improve its phishing protections and to protect users from MITM attacks, Google has come up with a new...
-

 3.7KCyber Attack
3.7KCyber AttackMan-in-the-Middle (MITM) Attacks: An Introduction
What is a Man-in-the-Middle (MITM) Attacks – Definition MITM attack refers to the kind of cyberattack in which an attacker eavesdrops on...
-
 238Vulnerabilities
238VulnerabilitiesPerl devs fix an important flaw in DBD—MySQL that affects encryption between client and server
Perl development team solved a flaw in DBD—MySQL in some configurations that wasn’t enforcing encryption allowing an attacker to power MiTM attacks....
-

 209Cryptocurrency
209CryptocurrencyConfide App used by White House staffers Found Vulnerable for MITM attacks
Confide is an a encrypted texting application for Android and iOS, which used by staffers in White House for their secret communication. Security...
-
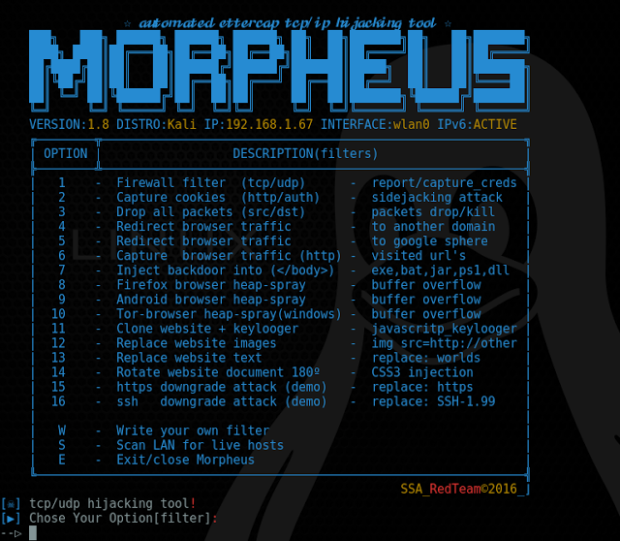
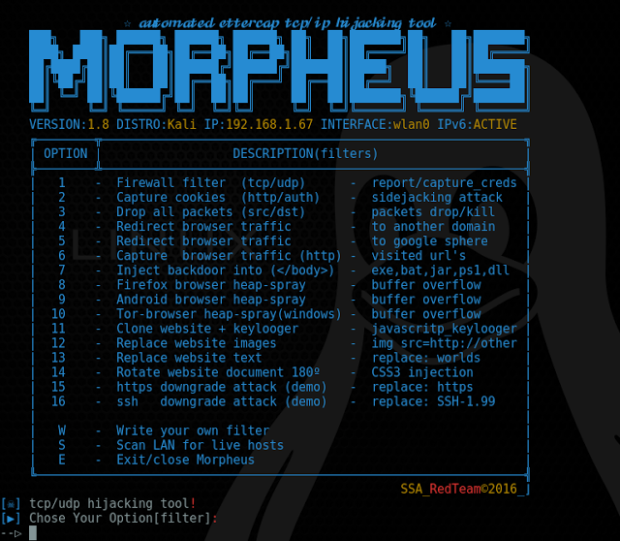 168Data Security
168Data SecurityAutomated Ettercap TCP/IP Hijacking Tool – Morpheus
Morpheus is a framework tool which automates TCP/UDP packet manipulation tasks by using etter filters to manipulate target requests/responses under MitM attacks...






