All posts tagged "Network"
-

 4.5KData Security
4.5KData SecurityWhat Is Deep Packet Inspection and How Does It Work?
Also known as DPI, deep packet inspection is a kind of packet filtering that evaluates the data and header of a packet...
-

 265News
265NewsA Simple Look At An Efficient Enterprise MDR
In general, corporate security policies define the information assets needed to continue corporate activities. Detecting threats to this information asset is the...
-
 3.9KDDOS
3.9KDDOSHow Companies Fight DDoS Attacks?
The threat of DDoS (Denial-of-Service) attacks that send massive processing demands from multiple Internet-connected devices (be it a PC, a smartphone, a...
-

 2.8KCyber Attack
2.8KCyber AttackYet Again! Cyber Attack on Toyota Car Maker
Once again Toyota Motor Corporation reported its second data breach. The first attack was in February, and it’s not clear whether the...
-

 240News
240NewsImplementing Operational Security, The Process and Best Practices
procedural security is what we call operational security (OPSEC), it is kind of risk management process that encourages admin to monitor operations...
-

 302News
302NewsUnderstanding VPN through open systems interconnection model
VPN is a wonderful thing that you all have probably heard about. I assume it was something like this: “Using a VPN...
-

 243News
243NewsSafe Computing Tips For Common Computer User
Currently, most computers are connected to the network, and various information is exchanged beyond national borders. Mobile devices such as smartphones and...
-

 321News
321NewsSecure Web Gateway Mechanics Made Simple
What is a Secure Web Gateway (SWG)? For the perspective of a typical Joe or Jill of today’s computing, Secure Web Gateway...
-

 3.4KMalware
3.4KMalwareAPT32 Malware’s Use Of New Downloader Critical To Its Propagation Success
APT32 malware has been covered here in Hackercombat recently, and we are set to update you of the latest findings from Palo...
-
 319Information Gathering
319Information GatheringBscan – An Asynchronous Target Enumeration Tool
Synopsisbscan is a command-line utility to perform active information gathering and service enumeration. At its core, bscan asynchronously spawns processes of well-known...
-
 249Network Tools
249Network ToolsNETworkManager – A Powerful Tool For Managing Networks And Troubleshoot Network Problems!
A powerful tool for managing networks and troubleshoot network problems! Features Network Interface – Information, Configure IP-Scanner Port-Scanner Ping Traceroute DNS Lookup...
-
 224Data Security
224Data SecurityHackers can use fax machines to infect a network
You may want to think twice before providing an enterprise fax number to a stranger Many companies still provide their fax number...
-
 333Incidents
333IncidentsNew Spectre attack enables secrets to be leaked over a network
It’s no longer necessary to run attacker code on the victim system. When the Spectre and Meltdown attacks were disclosed earlier this year, the...
-
 371Network Tools
371Network ToolsNETworkManager – A Powerful Tool For Managing Networks And Troubleshoot Network Problems
A powerful tool for managing networks and troubleshoot network problems! Features Network Interface – Information, Configure IP-Scanner Port-Scanner Ping Traceroute DNS Lookup...
-

 277Data Security
277Data SecurityQuick look your right eyes and ears while using public WiFi network
Research has revealed that public WiFi networks are more dangerous than one might realize. They can be like ripe fruit for hackers....
-
 260Network Tools
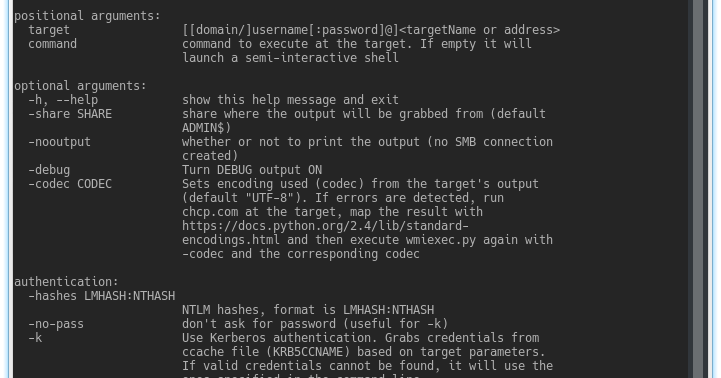
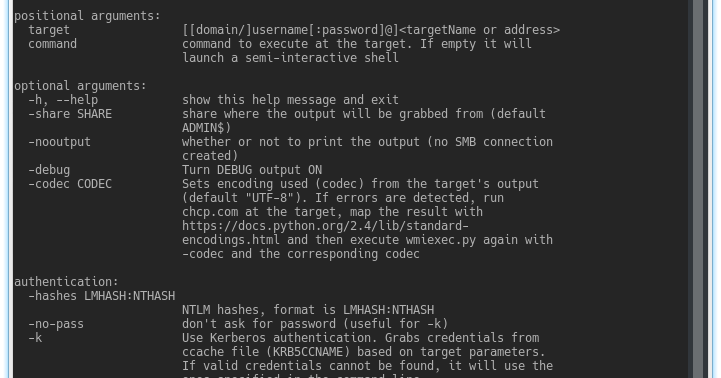
260Network ToolsImpacket – Collection Of Python Classes For Working With Network Protocols
Impacket is a collection of Python classes for working with network protocols. Impacket is focused on providing low-level programmatic access to the...
-
 234Security Tools
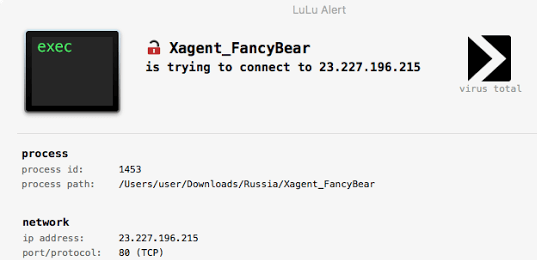
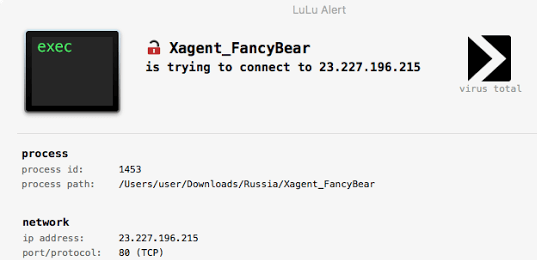
234Security ToolsLuLu – macOS Firewall That Aims To Block Unauthorized (Outgoing) Network Traffic
LuLu is the free open-source macOS firewall that aims to block unauthorized (outgoing) network traffic, unless explicitly approved by the user: Full...
-
 230Information Gathering
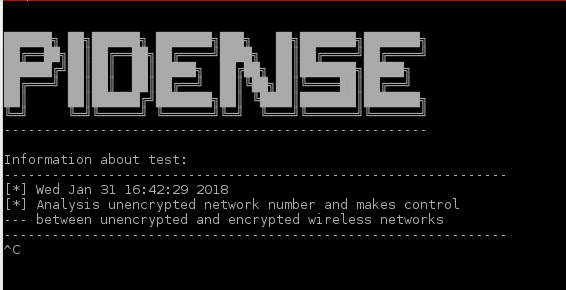
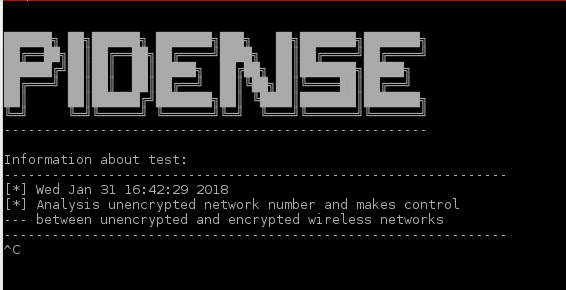
230Information GatheringPiDense – Monitor Illegal Wireless Network Activities (Fake Access Points)
Monitor illegal wireless network activities. Similar SSID broadcasts Same SSID broadcasts Calculates unencrypted wireless networks density Watches SSID broadcasts at the blacklist. Capabilities...
-

 267Information Gathering
267Information GatheringSPARTA – Network Infrastructure Penetration Testing
SPARTA is a python GUI application which simplifies network infrastructure penetration testing by aiding the penetration tester in the scanning and enumeration...
-

 245Network Tools
245Network ToolsDNSCAP – DNS Traffic Capture
dnscap is a network capture utility designed specifically for DNS traffic. It produces binary data in pcap(3) and other format. This utility is similar to tcpdump(1),...
-
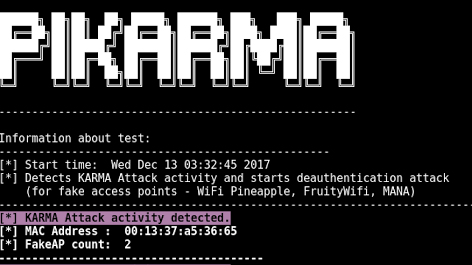
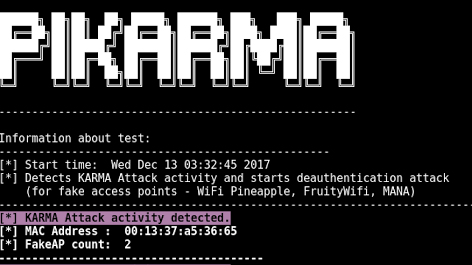 255Wireless Attacks
255Wireless AttacksPiKarma – Detects Wireless Network Attacks
Detects wireless network attacks performed by KARMA module (fake AP). Starts deauthentication attack (for fake access points) Working Principle for PiKarma Collects...






