All posts tagged "Network"
-

 150Incidents
150IncidentsFive Inmates Built Two PCs and Hacked a Prison From Within
Five inmates from the Marion Correctional Institution (MCI) built two computers from spare parts, hid them in the ceiling of a training...
-

 228How To
228How ToYour Wi-Fi Is Slow Because Of Your Neighbour, Here Is How To Fix It
Short Bytes: You can reduce the wireless interference for your network by selecting the least congested channel. You can do so on...
-

 189Vulnerabilities
189VulnerabilitiesRTM: Stealthy group targeting remote banking system
Today, we have released a white paper on RTM, a cybercrime group that has been relentlessly targeting businesses in Russia and neighboring...
-
 155Incidents
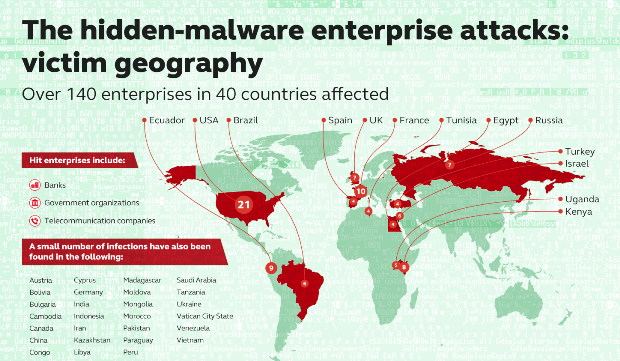
155IncidentsFileless attacks against enterprise networks
During incident response, a team of security specialists needs to follow the artefacts that attackers have left in the network. Artefacts are...
-
 101Data Security
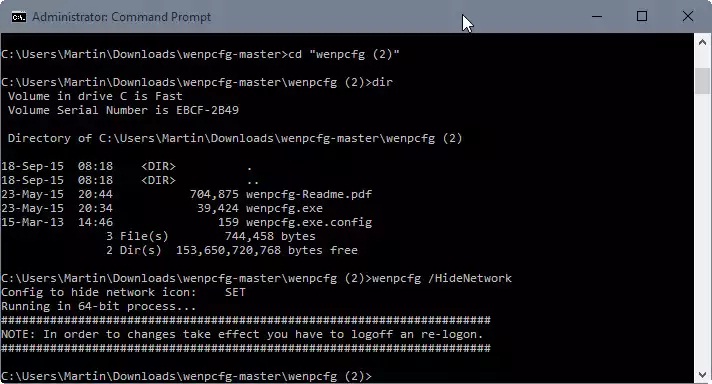
101Data SecurityRemove Libraries, Network, Homegroup and other links from File Explorer
When you open File Explorer in Windows 10, the system’s default file browsing and management tool, you will notice immediately that it...
-
 173How To
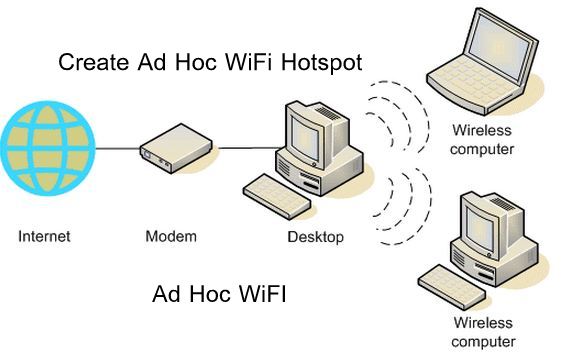
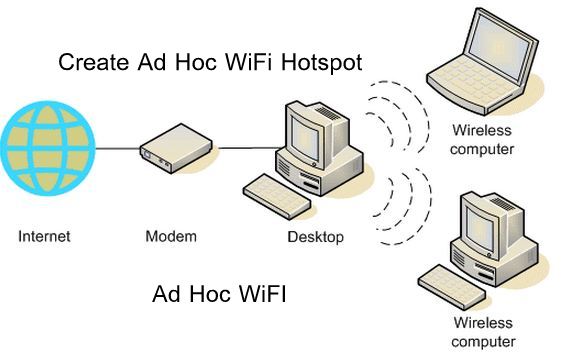
173How ToHow to Connect to Ad Hoc WiFi Network in Windows 8.1
Having Windows 8.1 and then connecting to a wireless network, sometimes it may create some problems. Well I use Ubuntu most of...
-

 289Data Security
289Data SecurityVulnerability in Blu-ray Players allow hackers to penetrate your network
Unsuspected Blu-Ray Players Vulnerabilities Present Open passage to Cybercriminals. A team of security researchers at NCC Group analyzed different Blu-ray players and...






