All posts tagged "Nmap"
-
 447Exploitation Tools
447Exploitation ToolsPenta – Open Source All-In-One CLI Tool To Automate Pentesting
Penta is is Pentest automation tool using Python3. (Future!) It provides advanced features such as metasploit and nexpose to extract vuln...
-
 304Pentest
304PentestYuki Chan – Automated Penetration Testing and Auditing Tool – Detailed Explanation
Yuki Chan is an Automated Penetration Testing tool that will be auditing all standard security assessment for you. It is one of the...
-
 337Tutorials
337TutorialsHow to Scan whole country IP Addresses in a while
In some phases of information gathering. Pentester do require to scan some of the IP addresses that are most commonly used. As...
-
 315Tutorials
315TutorialsFind vulnerability of any target to hack
Scanning is the initial phase of pentesting. Security researchers/ pentesters are very well aware of this phase. This is the phase where...
-
 317Information Gathering
317Information GatheringBscan – An Asynchronous Target Enumeration Tool
Synopsisbscan is a command-line utility to perform active information gathering and service enumeration. At its core, bscan asynchronously spawns processes of well-known...
-
 333Tutorials
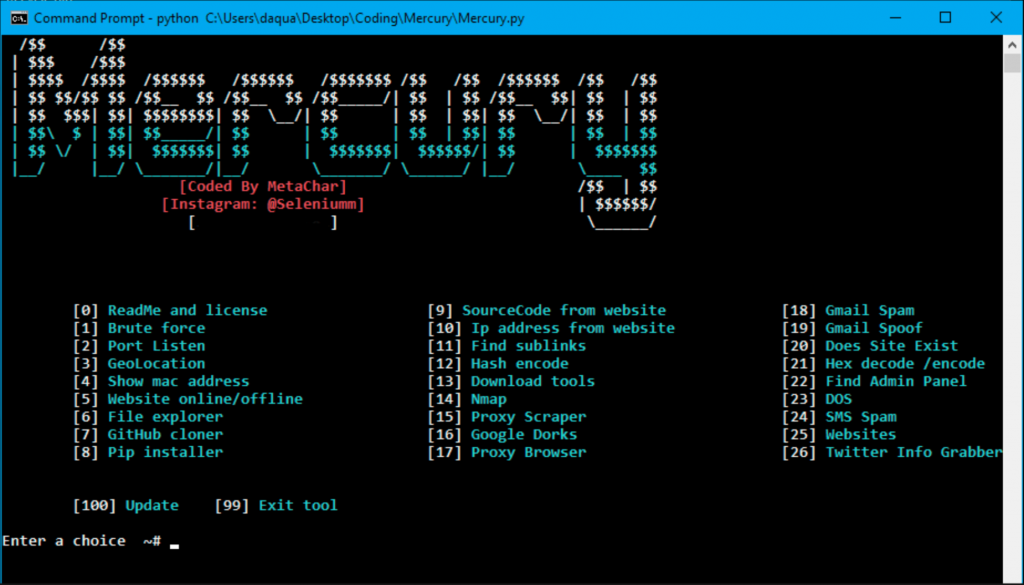
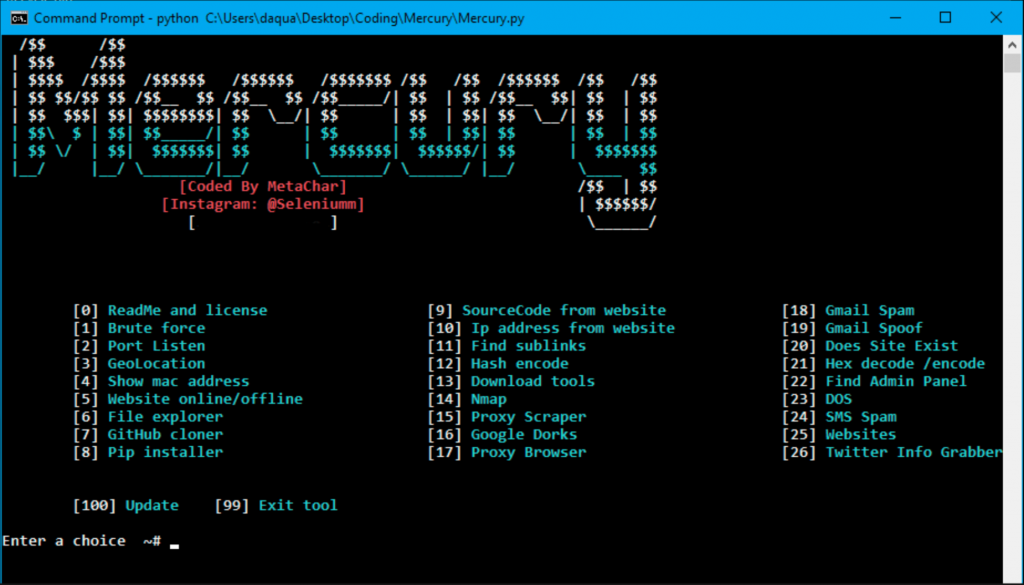
333TutorialsHack any website with All in One Tool
Internet is the hub of web applications. Many past developers has made numerous web applications to use internet more effectively. Internet has...
-
 328Information Gathering
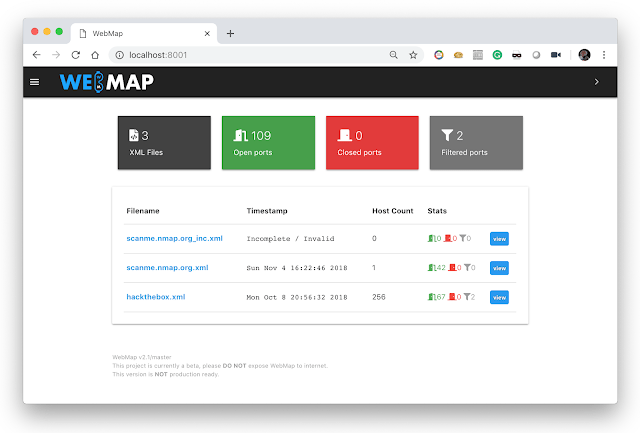
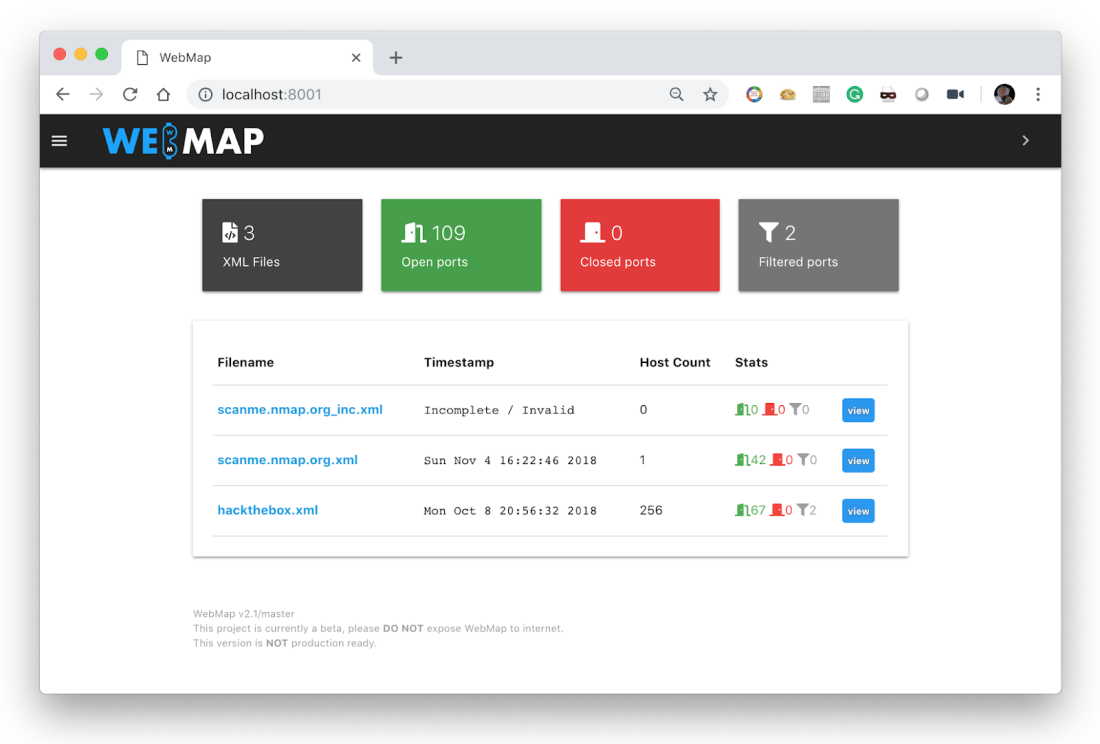
328Information GatheringWebMap – Nmap Web Dashboard And Reporting
A Web Dashbord for Nmap XML Report Usage You should use this with docker, just by sending this command: $ mkdir /tmp/webmap...
-
 242Data Security
242Data SecurityWebMap – A web dashboard for Nmap XML report
Use You should use this with docker. According to digital forensics specialists from the International Institute of Cyber Security, all you have...
-
 322Exploitation Tools
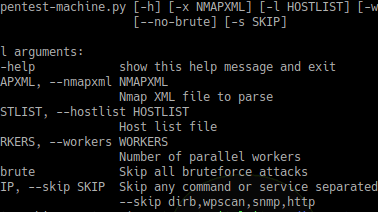
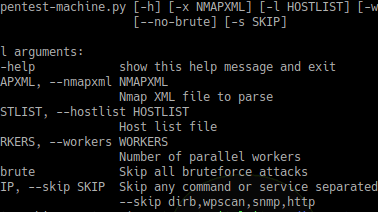
322Exploitation ToolsPentest-Machine – Automates Some Pentest Jobs Via Nmap Xml File
Automates some pentesting work via an nmap XML file. As soon as each command finishes it writes its output to the terminal...
-

 283How To
283How ToNmap-bootstrap-xsl Hack Creates Visually Appealing Nmap Scan Reports : Interview With Its Creator, Andreas Hontzia
As the title itself states, nmap-xsl-bootstrap, a brand-new utility or, better to say an Nmap hack, that helps in beautifying the regular...
-
 199Information Gathering
199Information GatheringNmap 7.70 Released With Better OS Detection, 9 new NSE scripts and Much More
Nmap (“Network Mapper”) is a free and open source utility for network discovery and security auditing. Many systems and network administrators also find...
-
 207Information Gathering
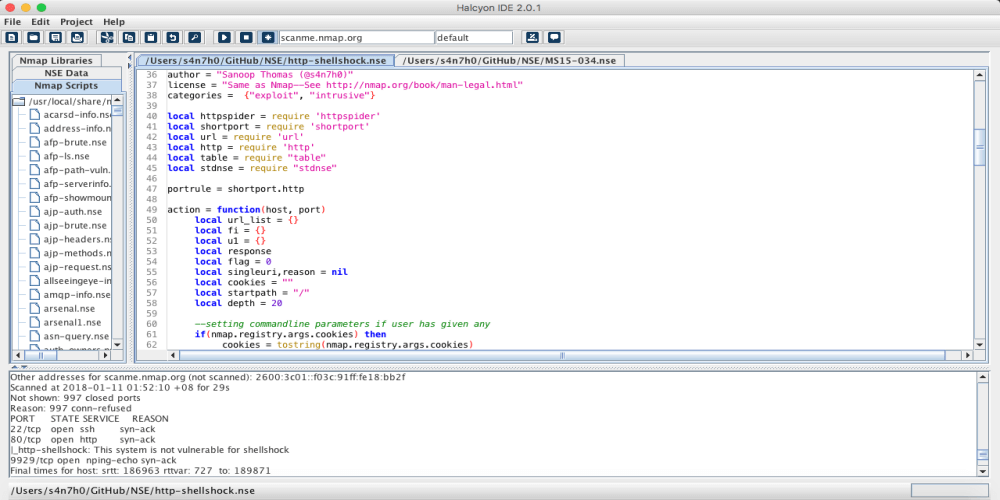
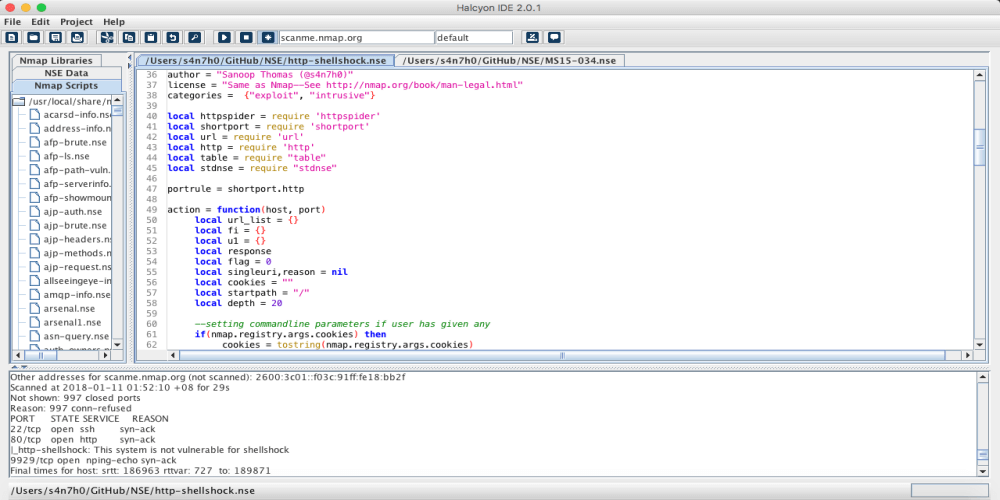
207Information GatheringHalcyon – NSE Nmap Script Development IDE
Halcyon IDE lets you quickly and easily develop scripts for performing advanced scans on applications and infrastructures with a range from recon to...
-
 208Exploitation Tools
208Exploitation ToolsBruteSpray v1.6.0 – Brute-Forcing from Nmap output (Automatically attempts default creds on found services)
BruteSpray takes nmap GNMAP/XML output and automatically brute-forces services with default credentials using Medusa. BruteSpray can even find non-standard ports by using...
-

 215How To
215How ToSimple Tools for Collecting Information During Pen-Testing
Collecting information is a useful tool in any situation. For a penetration tester, information gathering is not only useful but necessary. When...
-
 211How To
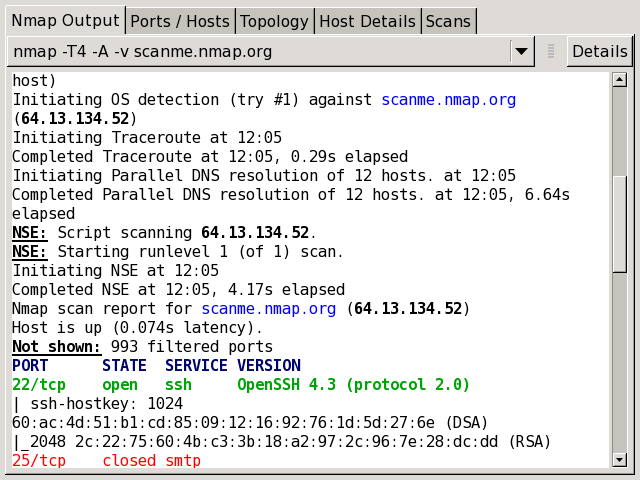
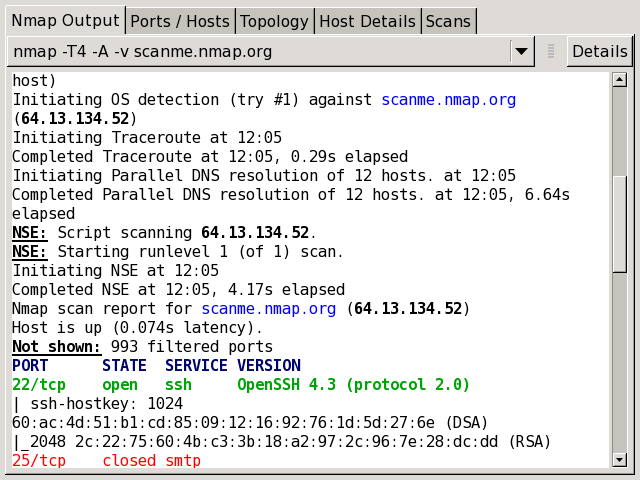
211How ToHow to Perform Open Port Scanning and OS Detection Using Nmap
Today in this tutorial we will have a look at how we can use Nmap (Which stands for Network Mapper )in Kali...
-

 232How To
232How ToHow to Use Zenmap – Nmap Network Scanning Tool in Windows
Running Nmap on Windows is not as difficult or problematic as it was in the past. Nmap is supported on Windows 7...
-
How To
How to Scan Live Hosts With Nmap
Live hosts detection is a very important tool for every penetration tester and ethical hacking. In this tutorial we are going to...
-
How To
How to Scan for Heartbleed bug using Nmap on Kali Linux
In this tutorial we will be scanning a target for the well known Heartbleed SSL Bug using the popular Nmap tool on Kali Linux. The...






