All posts tagged "Open Ports"
-
 319Cyber Events
319Cyber EventsThe Pitfalls of Keeping Your Ports Wide Open
Based on security assessment results, penetration testers often recommend hiding an enterprise network’s ports behind a whitelist. However, corporate IT teams don’t...
-
 344Tutorials
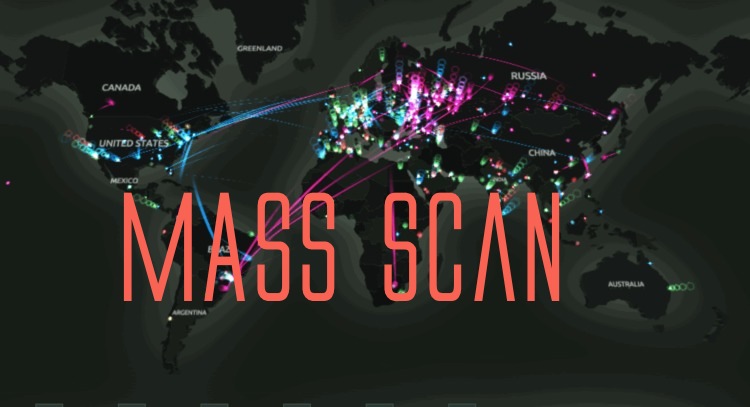
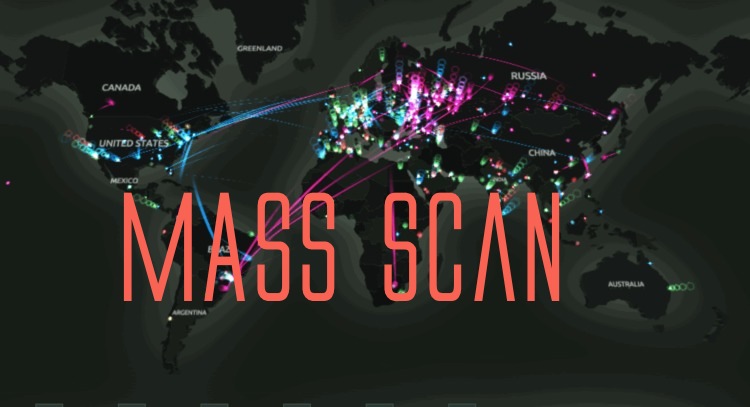
344TutorialsHow to Scan whole country IP Addresses in a while
In some phases of information gathering. Pentester do require to scan some of the IP addresses that are most commonly used. As...
-

 194Malware
194MalwareOpen Ports Create Backdoors in Millions of Smartphones
Mobile applications that open ports on Android smartphones are opening those phones to remote hacking, claims a team of researchers from the...






