All posts tagged "Passwords"
-

 5.0KIncidents
5.0KIncidentsThis politician hacked the iCloud accounts of more than 100 women
A Dutch politician could be living his last days at large, as he is facing a sentence of up to three years...
-

 541Data Security
541Data SecurityHow to password protect and encrypt files and folders in Windows 10, no additional software needed
The main protection measure for files stored on a computer with Windows 10 operating system is the users’ password; however, data protection...
-

 352Hacked
352HackedThis Technique Claims To Make Passwords 14 Million% Tougher To Crack
Tide, an Australia-based non-profit organization has come up with a technique called ‘Splintering’ that claims to make usernames and passwords 14 million...
-
 492Hacked
492HackedMicrosoft: Multi-Factor Authentication Is 99.9% Effective Than Passwords
According to Microsoft, it witnesses around 300 million fake account sign-in attempts every day. Users can protect their account if they have...
-
 396Password
396PasswordCombolists-as-a-Service – Hackers Sell Stolen Passwords on underground Hacking Forums
Threat actors advertising a new Combolists-as-a-Service model to sell credentials on the underground hacking forums that enable account takeovers. Attackers employ several...
-

 303Data Security
303Data SecurityMicrosoft will remove password expiration policy; they think it’s useless
The technology giant Microsoft plans to eliminate the so-called password expiration policy, by which the company requests Windows users to change their...
-

 316Data Security
316Data SecurityMillions of Instagram users affected by Facebook security incident
According to cyber forensics course experts from the International Institute of Cyber Security (IICS), a security error in Facebook affected more users...
-

 376News
376NewsList Of World’s Most Hacked Passwords Is Here And It’s Embarrassing
We cannot stress enough on the fact that it is important to use passwords that aren’t easy to guess. Our online security...
-
 241Password
241PasswordMost Hacked Passwords – Top 100,000 Common Passwords that Already Known to Hackers
Password plays a vital role in securing your account, a common password is easy to remember, but it will be easier for...
-

 337News
337NewsFacebook Exposed Millions Of Instagram Passwords By Storing It In Plaintext
Just a month ago, Facebook admitted it had mistakenly exposed hundreds of millions of passwords by storing them in plaintext where employees...
-
 344Geek
344GeekFacebook stored 600m user passwords in plain text exposed to 20k employees
The company says it discovered the issue in January and there is no need to change passwords. The social media giant Facebook has revealed...
-

 232Data Breach
232Data BreachFacebook Stored Hundreds of Millions of Users Password in Plain Text
Facebook Stored their hundreds of millions of users password in plain text instead of masking it as a human-readable format. These millions...
-
 406Data Security
406Data SecurityOne of the most common and vulnerable passwords is ‘Ji32k7au4a83’
Experts explain why this combination of characters has been linked to multiple incidents of data breach According to network security and ethical...
-

 220Data Breach
220Data BreachMassive Collection of 2.2 Billion Usernames and Passwords Circulated in Hacker Forums
A new collection of massive breached database freely distributed on hacker forums and torrents. The breached database contains a collection of 2.2...
-
 296Password Attacks
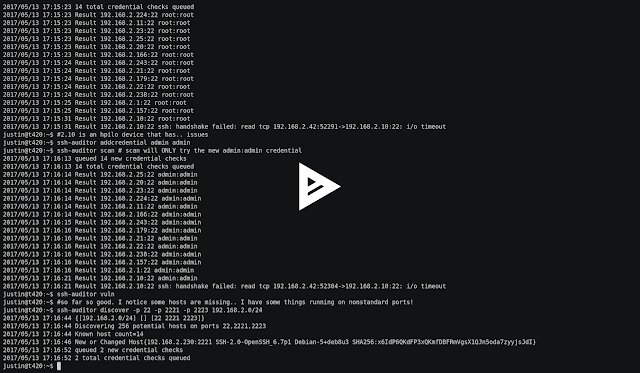
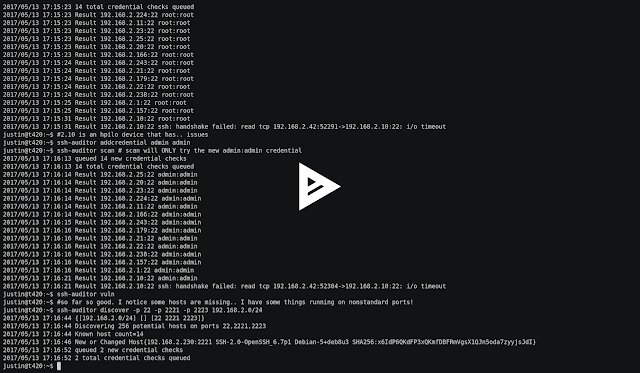
296Password AttacksSSH Auditor – The Best Way To Scan For Weak Ssh Passwords On Your Network
The Best Way To Scan For Weak Ssh Passwords On Your Network Features ssh-auditor will automatically: Re-check all known hosts as new...
-
 282Exploitation Tools
282Exploitation ToolsAutoRDPwn v4.5 – The Shadow Attack Framework
AutoRDPwn is a script created in Powershell and designed to automate the Shadow attack on Microsoft Windows computers. This vulnerability allows a...
-
 300Data Security
300Data SecurityCalifornia prohibits use of weak default passwords
Passwords like “admin” or “password” set by default will be illegal in 2020 The state of California has recently passed a law that establishes higher safety standards for any device connected...
-
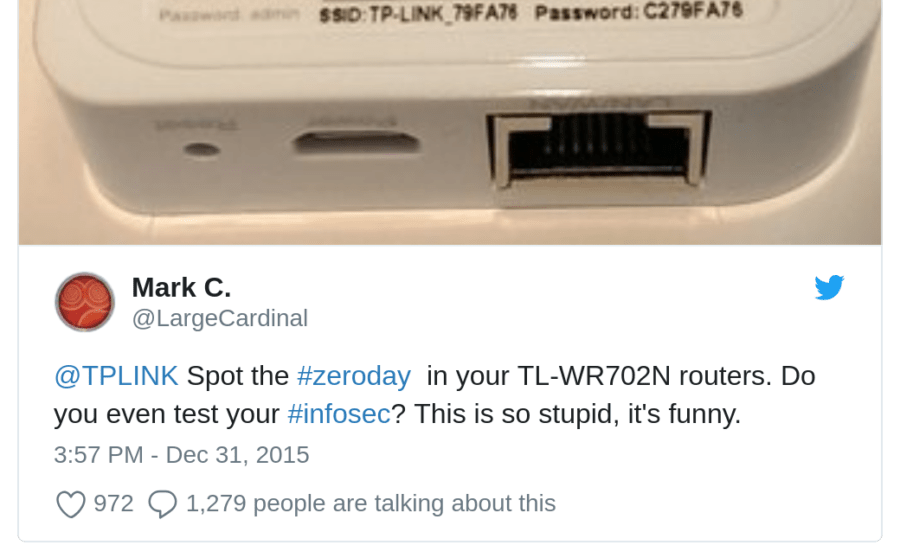
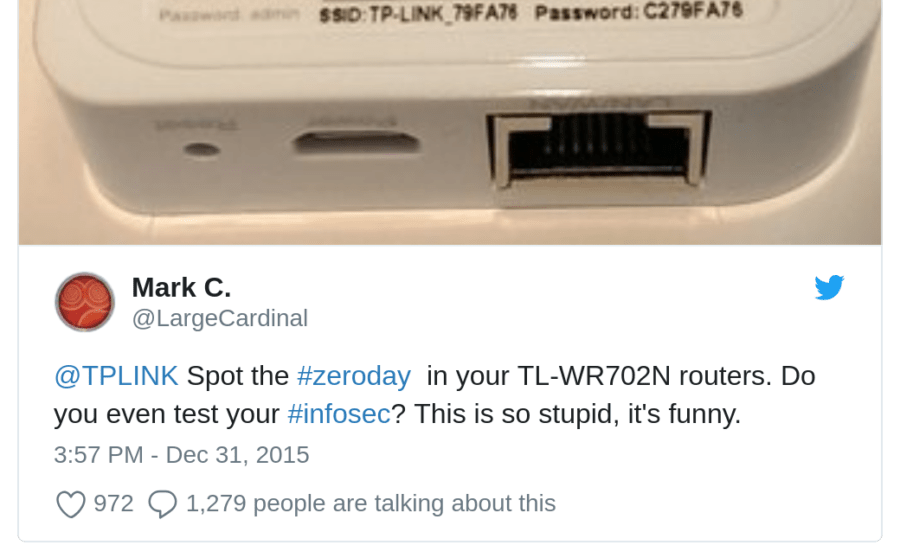 266Password Attacks
266Password AttacksTP-Link-defaults – Python Script For Trying Default Passwords For Some TP-Link Hotspots
Python script for trying default passwords for some TP-Link Hotspots Inspired by Usage usage: scan.py [-h] [-p] Python script for trying default...
-

 313Password Attacks
313Password AttacksRedLogin – SSH Brute-force Tools
Red Login: SSH Brute-force Tools. Features: High speed and precision CLI ( Console based ) Run the arbitrary command after the attack is successful (...
-
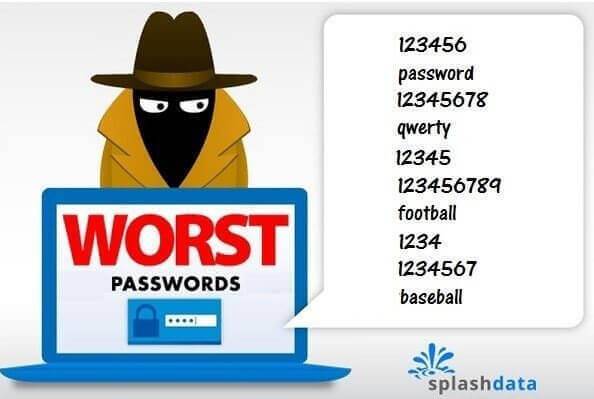
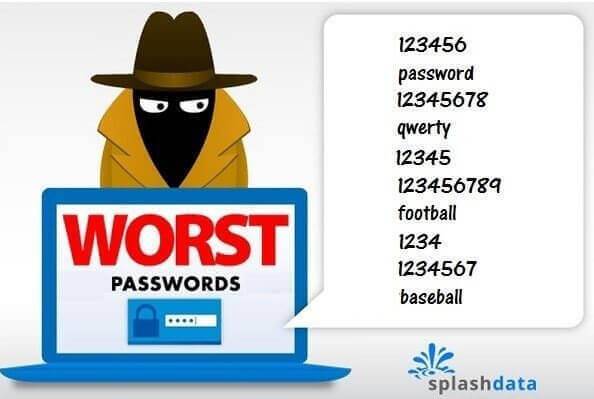 281Articles
281ArticlesMost Common Password found in Every Data Dump is “123456”
While becoming “123456” as your phrase is quite bad, the other phrases found on a list of Top 100 Worst Passwords of...
-
 281Exploitation Tools
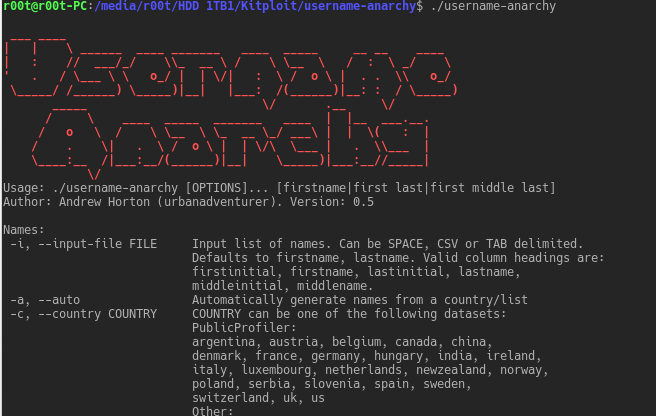
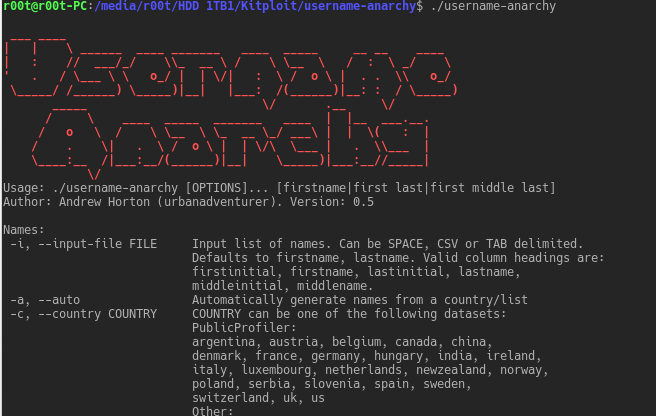
281Exploitation ToolsUsername Anarchy – Username Tools For Penetration Testing
Tools for generating usernames when penetration testing. Usernames are half the password brute force problem. This is useful for user account/password brute...






