All posts tagged "Penetration testing"
-

 295Malware
295MalwareLightNeuron, the backdoor designed especially for Microsoft Exchange
Reports of IICS web application penetration testing experts mentioned that a group of Russian cyber spies created one of the most advanced...
-

 261Malware
261MalwareFree Email Security Penetration Testing Tool to Check Organization’s Security against Advanced Threats
BitDam launches a free Email Security Penetration Testing tool to determine the organization’s security posture against advanced threats. The Email accounts are...
-

 454Pentest
454PentestWPScan – Penetration Testing Tool to Find The Security Vulnerabilities in Your WordPress Websites
WPScan is a WordPress security scan for detecting and reporting WordPress vulnerabilities. WordPress is a free online Open source content Managed system...
-
 298Vulnerabilities
298VulnerabilitiesOsmedeus – Fully Automated Offensive Security Tool for Reconnaissance & Vulnerability Scanning
Osmedeus is a fully automated tool that allows you to run the collection of awesome tools to reconnaissance and vulnerability scanning against...
-

 297News
297NewsPenetration Testing The Most Visible Component of Cyber Security
Amid all of the high-profile data breaches, of all sizes have been successfully targeted by hackers who employ a wide range of...
-

 345News
345News8 Easy Steps of Installing Kali Linux In Raspberry Pi
The humble Raspberry Pi, a single-board integrated computer based-on ARM architecture has become very influential in the field of enthusiast computing. With...
-
 1.7KRansomware
1.7KRansomwareSamSam Ransomware Hits Again VS Jackson County, Georgia
2017 was the Year of the Ransomware when WannaCry and its derivatives wreaked havoc to various computer installations with SMBv1 vulnerabilities. The...
-

 340News
340NewsThe Best 10 Linux Distro for Penetration Testing
If you are working as a security professional and interested in this specific field of knowledge, you must be known these top...
-
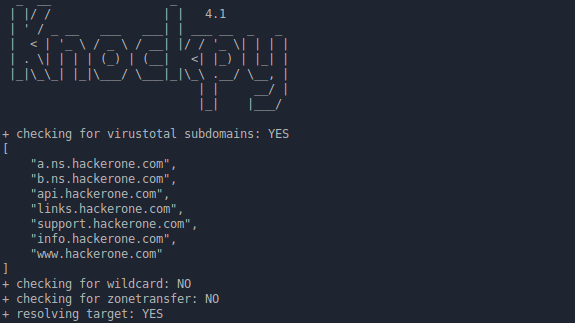
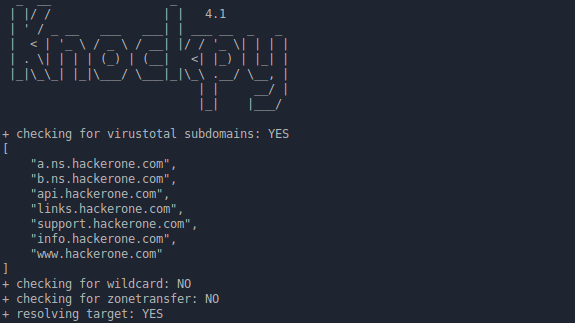 218Information Gathering
218Information GatheringKnock v.4.1.1 – Subdomain Scan
Knockpy is a python tool designed to enumerate subdomains on a target domain through a wordlist. It is designed to scan for...
-
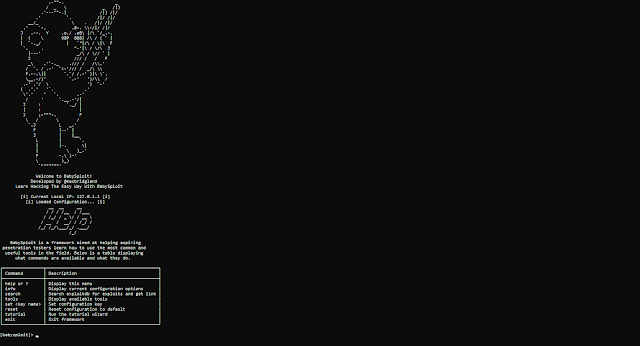
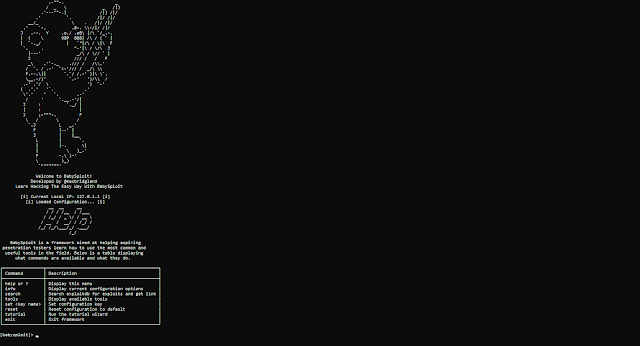 221Exploitation Tools
221Exploitation ToolsBabySploit – BabySploit Beginner Pentesting Framework
Tested on Kali Linux. Should work with all Debian based distros (and other ones if you have the right packages installed) BabySploit...
-

 167News
167News5 Things to Know For a Successful Pen Testing
Penetration testing (AKA Pen test) is an authorized deliberate hacking of a corporate network and computer infrastructure to determine its vulnerability. The...
-

 276News
276NewsWhy Penetration Testing is Important
For enterprises, encountering IT security vulnerabilities have become common incident around their enterprise networks and IT systems. These IT security vulnerabilities can...
-

 283News
283NewsConquering The Real Challenges Of GDPR Compliance
The General Data Protection Regulation became enforceable on May 25th, 2018, and since then, the risk of a cyber breach has become...
-
 363Data Security
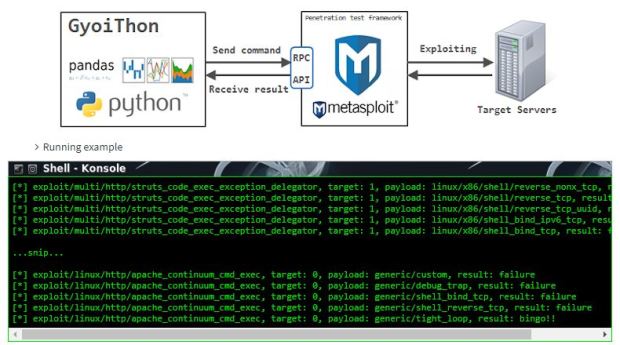
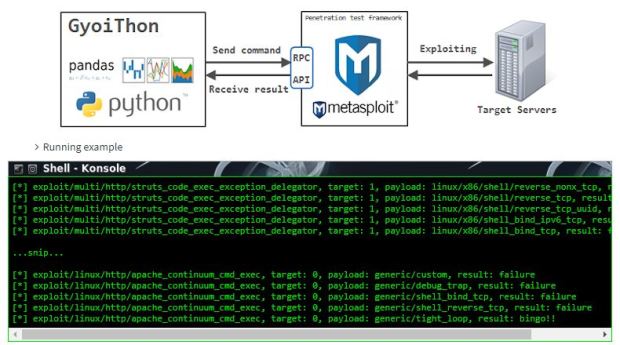
363Data SecurityGyoiThon: tool to make penetration testing with Machine Learning
According to information security experts, GyoiThon identifies the software installed on the web server as OS, Middleware, Framework, CMS, etc. Then, run valid exploits...
-

 319Pentest
319PentestExploit Pack V10.07 Released with More than 38.000+ Exploits Including Zero-Days
Exploit Pack is a well-integrated open source tool for conducting professional penetration tests. As like any other penetration testing tool it requires...
-
 216Data Security
216Data SecurityHow to do offensive Penetration Testing with Kali?
We will start with the preparation. We will need some basic skills. Even more important than being able to do research, time...
-

 218News
218NewsPenetration Testing – How it is Performed and Types
A penetration test, or pen-test, is an effort to measure the security of an IT infrastructure by safely attempting to exploit vulnerabilities....
-
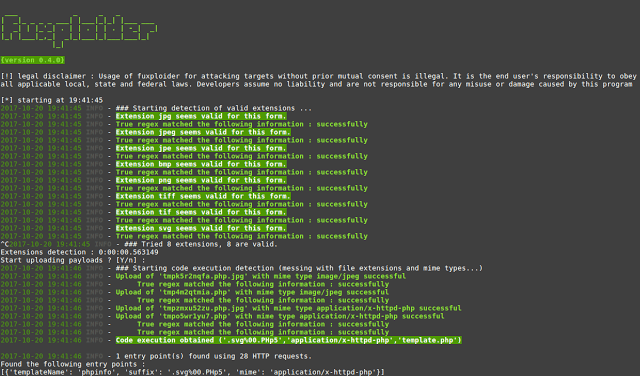
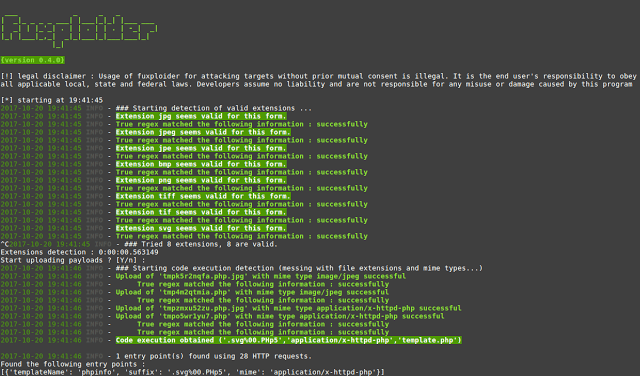 292Exploitation Tools
292Exploitation Toolsfuxploider – File Upload Vulnerability Scanner And Exploitation Tool
fuxploider is an open source penetration testing tool that automates the process of detecting and exploiting file upload forms flaws. This tool...
-
 200News
200NewsWeb Application Penetration Testing Checklist Overview
Penetration testing is the process of testing a software by trained security experts (aka penetration testers or ethical hackers) in order to...
-

 235Pentest
235PentestParrot Security OS New Released with a Collection of tools for Penetration Testing and Forensic Analysis
Parrot Security Operating System is a Penetration Testing & Forensics Distro dedicated to Ethical Hackers & Cyber Security Professionals. With the new...
-
 322How To
322How ToSetup own PenTesting Environment (DVWA) on your Kali Linux
Setup own PenTesting Environment in your Kali Linux. Penetration game Tester now plays more than a few years ago, because the Internet...






