All posts tagged "PROXYCHAINS"
-
 266Tutorials
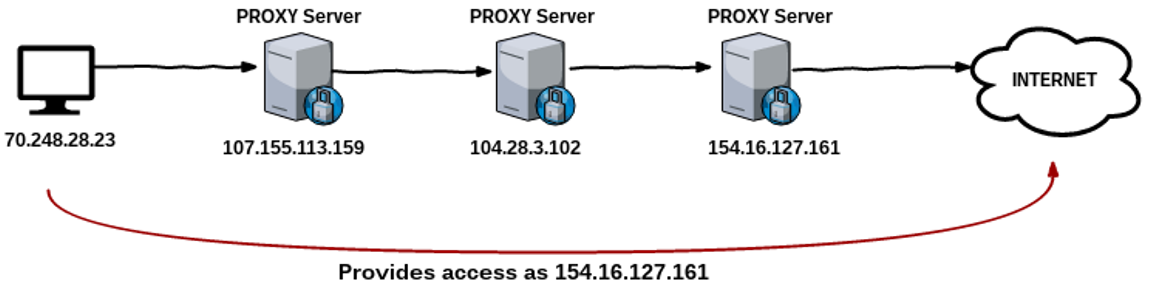
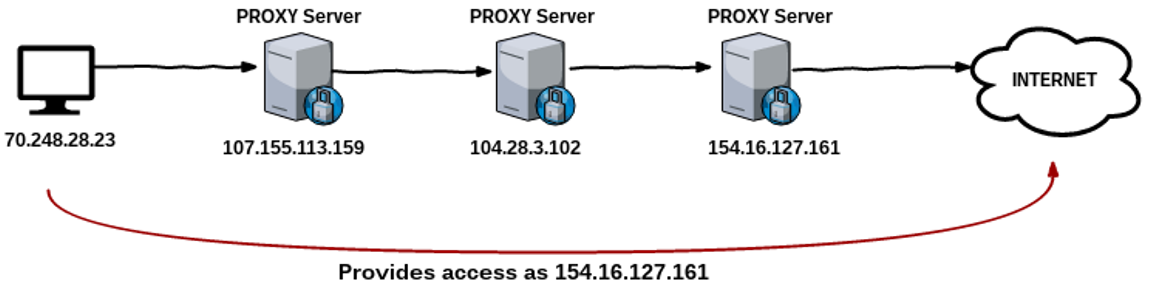
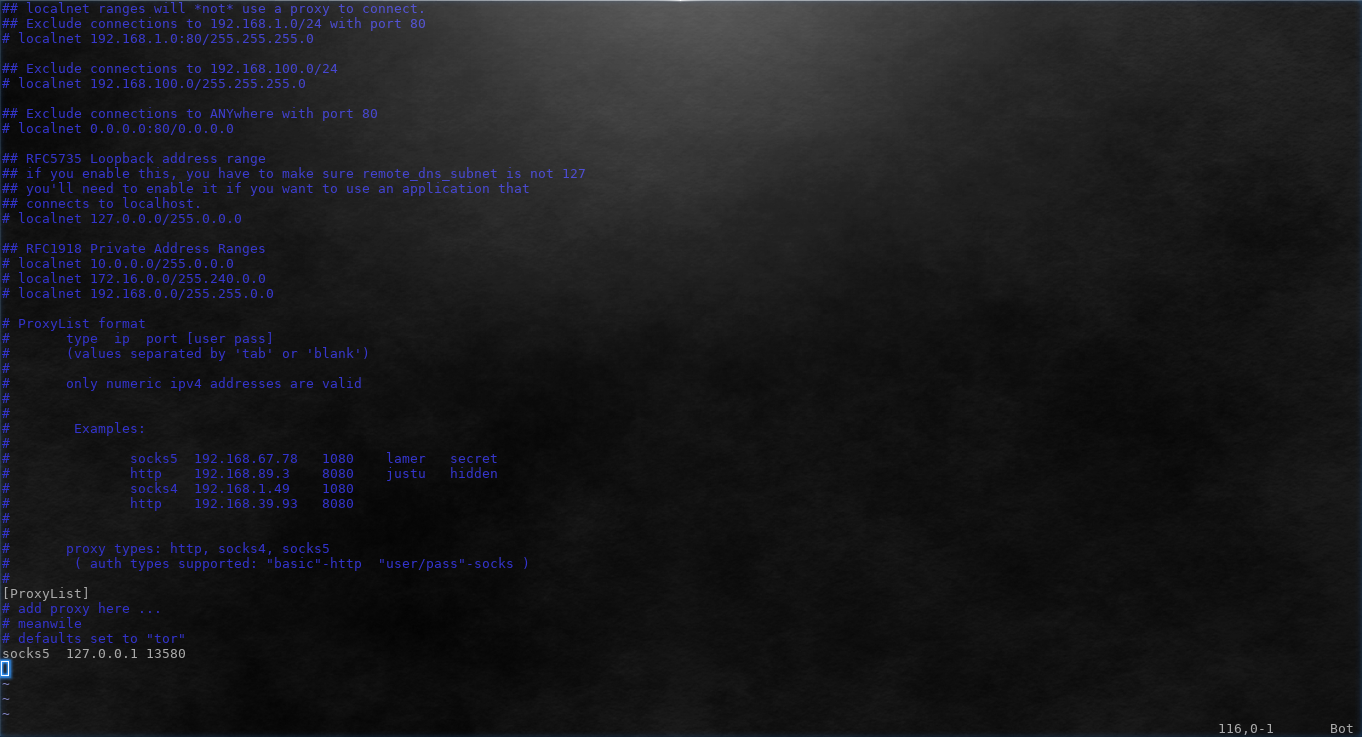
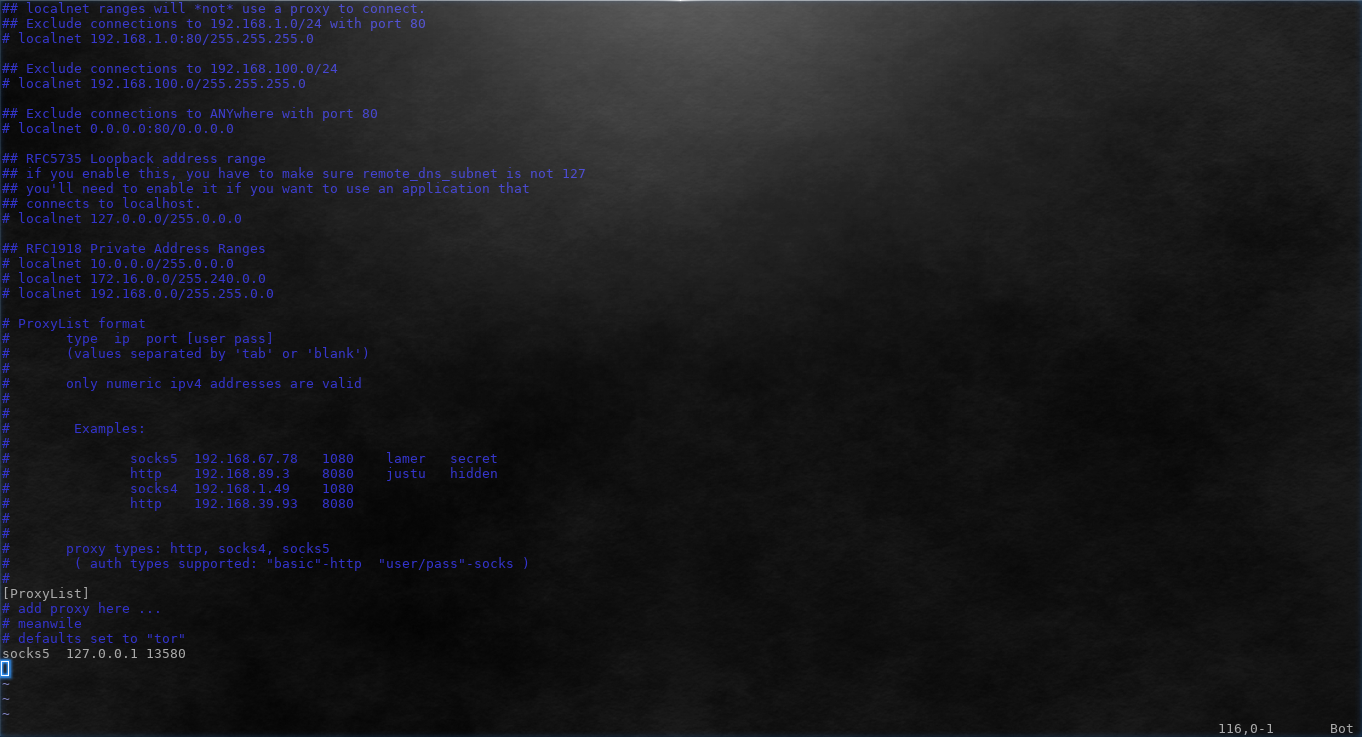
266TutorialsEVADE USING PROXYCHAINS
EVADE USING PROXYCHAINS:- Whenever attacker attacks in any network, all traffic of the attacker can be logged which can reveal the identity...
-
 324Anonymity
324AnonymityHow To Use Proxychains To Evade Detection in Kali Linux
The most important thing about doing penetration testing is anonymity, undetectable, or at least hard to be detected. The worst thing that...
-
 325Geek
325GeekHow to Use Proxychains to Run Applications Behind Proxy
Some applications do not support proxy by default. Other applications might support HTTP proxy but fail when using SOCKS. As Tor provides...






