All posts tagged "Pwn2Own"
-
 1.5KVulnerabilities
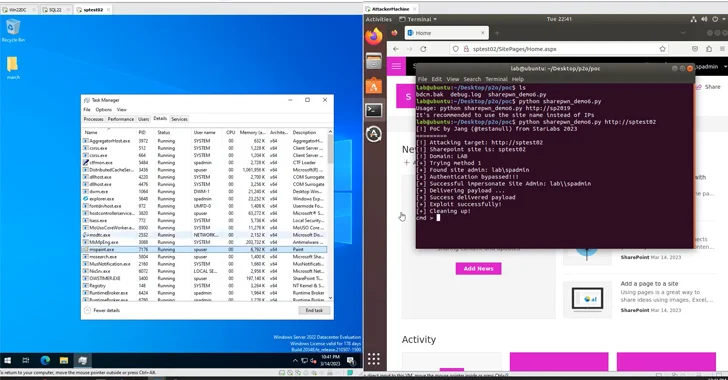
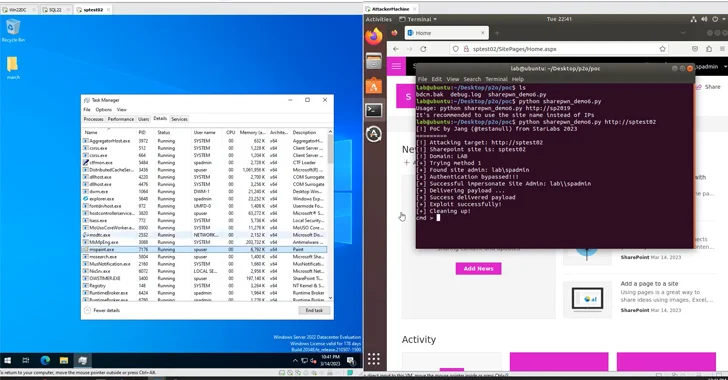
1.5KVulnerabilitiesAct Now: CISA Flags Active Exploitation of Microsoft SharePoint Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security vulnerability impacting Microsoft SharePoint Server to its Known Exploited...
-
 4.6KNews
4.6KNewsiPhone 13 Pro, Windows, Chrome, Linux and others pwned at Tianfu Cup
Tianfu Cup is the Chinese version of the Pwn2own in which hackers from Kunlun Lab managed to secure first place by hacking...
-

 4.7KNews
4.7KNewsChinese Hackers Win $382,500 For Hacking KVM On Ubuntu, Edge, Adobe Reader
In 2018, the Chinese government barred Chinese security researchers from participating in hacking contests in foreign countries in a bid to keep...
-
 2.3KData Security
2.3KData SecurityXiaomi, Amazon Echo, Sony & Samsung Smart TVs pwned at Pwn2Own
Hackathons happen to be an all-out favorite for the cybersecurity industry for their renewed sense of competing in real-time – testing your...
-
 261News
261NewsFirefox, Edge, Safari, And Tesla Hacked At Pwn2Own 2019
Earlier this week, Pwn2Own Vancouver 2019 kicked off with participants from all around the world. This year was the first time in...
-

 484Vulnerabilities
484VulnerabilitiesPwn2Own 2019 – Apple Safari, VirtualBox, VMware Hacked – Ethical Hackers Earned $240,000 by Submitting Zero-day’s
Trend Micro’s Zero Day Initiative (ZDI) vulnerability research contest Pwn2Own 2019 Successfully started its first-day contest and the team of researchers earned...
-

 378Data Security
378Data SecurityBug bounty: Hack Tesla Model 3 to win your own Model 3
Tesla is partnering with Pwn2Own’s bug bounty to identify vulnerabilities in its Model 3 car software. Electric car maker Tesla announced recently...
-

 275News
275NewsiPhone X, Xiaomi Mi 6 & Samsung Galaxy S9 hacked at Pwn2Own
White hat hackers and IT security researchers have once again proved their elite skills at Pwn2Own 2018 after exposing critical security vulnerabilities in products...
-

 279Vulnerabilities
279VulnerabilitiesThe Weak Bug – Exploiting a Heap Overflow in VMware
Introduction In march 2017, I took part in the pwn2own contest with team Chaitin Security Research Lab. The target I was focused on was...
-

 223Hacked
223HackedUbuntu Linux, Safari, Adobe Reader, And Edge Hacked At Pwn2Own 2017
Short Bytes: At the Trend Micro-sponsored Pwn2Own 2017 competition, the security researchers were able to hack many popular software and applications like Ubuntu,...






