All posts tagged "ransomware"
-
 201Ransomware
201RansomwareA New .NET Ransomware Shrug2 Encrypts Files Around 76 Different Extensions
Malware authors find easy to develop malware using the Microsoft .Net framework, some infamous ransomware like SamSam, Lime and now Shrug2 ransomware...
-

 265Ransomware
265RansomwareRansomware-as-a-Service – Princess Evolution Ransomware Advertised in Underground Forums
The new version of Princess Locker ransomware dubbed Princess Evolution advertised in dark web forums as a ransomware as a service (RaaS) and...
-

 330Cyber Crime
330Cyber CrimeIranian Hackers are Developing Ransomware to Secure Bitcoin
Cybersecurity experts have come up with the warning that Iranian Hackers, in the face of the economic issues that the country is...
-
 284Malware
284MalwareIphone chipmaker hit by massive ransomware attack
Factories crippled after WannaCry variant infected Windows 7 devices without protection Enterprise network security specialists from the International Institute of Cyber Security...
-

 131News
131NewsBitPaymer Malware made Mat-Su Alaska Gov’t to Reuse Typewriters
Electromagnetic pulse (EMP) attacks can render our advanced technology to recede as back to pre-industrial revolution stage. In other words, we in...
-

 286Malware
286MalwareNew AZORult Malware Spreading Via Office Documents Steals to Credentials & Launch Ransomware Attack
Threat actors behind AZORult malware released an updated version with improvements on both the stealer and the downloader functionalities. Within a day...
-
 221Ransomware
221RansomwareCyber Criminals Launch Hermes Ransomware Via Password Protected Word Documents
Cyber Criminals distributing Hermes Ransomware via dangerous malspam that contains Weaponized Password protected Word documents to encrypt the system files and lock the victim’s...
-

 311News
311NewsIT Security Pros Are Sure Feeling The Heat Of Modern Attacks
In this new digital landscape, IT security professionals are feeling the most heat, as they must constantly fret about looming cyberattacks and...
-

 399Data Security
399Data SecurityNew variant of Kronos banking trojan spotted using Tor network
WannaCry ransomware hero is facing charges in the United States for developing Kronos banking trojan. In August 2017, Marcus Hutchins (@MalwareTechBlog on Twitter) aka...
-

 138Cyber Crime
138Cyber Crime5 Reasons Why Businesses Are Failing IT 101
In today’s ever-changing technological landscape, cybercriminals have taken on the challenge of cybersecurity. Different forms of ransomware and crytojacking malware are their...
-

 191Ransomware
191RansomwareHackers Compromised Navi Mumbai Hospital Computers Sytems With Ransomware
Ransomware attack hits computer systems of Navi Mumbai Mahatma Gandhi Mission Hospital. The attack came into light on Sunday when a receptionist...
-

 195News
195NewsCyptojacking: the latest buzzword for Cybercriminals
Ransomware seems to have taken a back seat and not it’s Cryptojacking the latest arsenal for cybercriminals, and it has increased drastically over...
-

 267Malware
267MalwareProspective on the evolution of ransomware
This is a reflection exercise on the possible evolution of one of the most common information threats nowadays. Are ransomware threats the...
-

 192Ransomware
192RansomwareMagniber Ransomware Improves Its Obfuscation Techniques and Expands to Other Asian Countries
Magniber ransomware emerges again leveraging various obfuscation techniques and with refined source codes. The most famous and long-running browser exploitation toolkit Magnitude...
-
 250Hacked
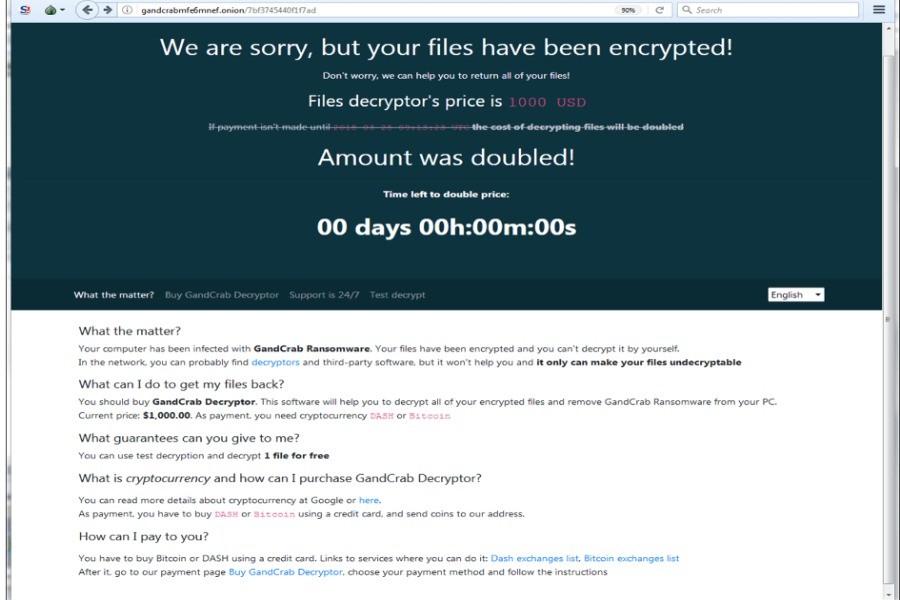
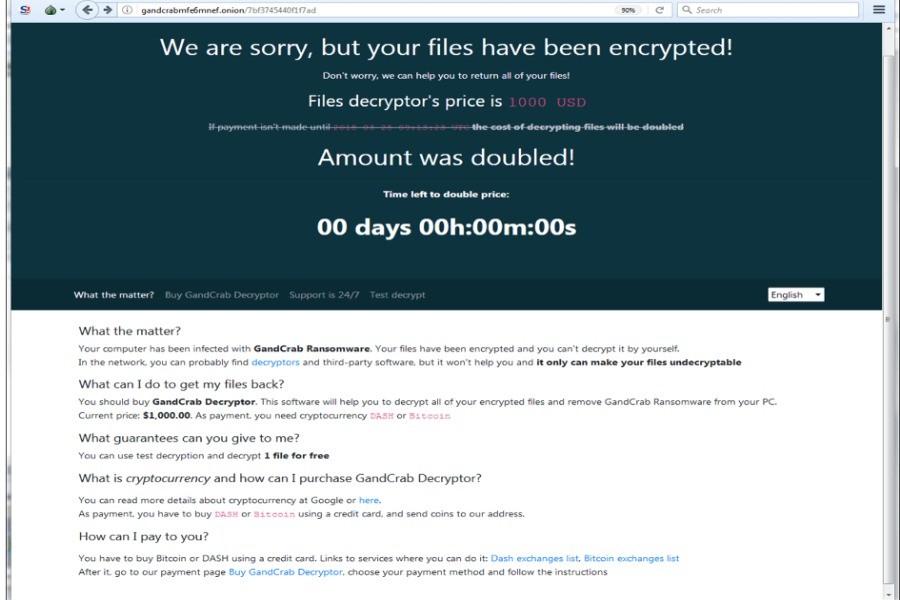
250HackedRewritten GandCrab Ransomware Targets SMB Vulnerabilities To Attack Faster
GandCrab ransomware, which has created a hullabaloo in the cybersecurity industry by constantly evolving, has yet again caused a commotion. The latest...
-
 286Ransomware
286RansomwareNew Version of GandCrab Ransomware Attack via Compromised Websites using SMB Exploit Spreader
The new version of GandCrab ransomware discovered that attack the target system using SMB exploit spreader through compromised websites that posed as...
-
 198Ransomware
198RansomwareHackers Distributing Malicious PDF that Perform both Ransomware and Crypto-Mining Attack
A newly discovered malicious PDF sample distributing Rakhni ransomware family and hackers now added new crypto-mining capabilities to infect victims to perform both...
-

 320Malware
320MalwareA virus that decides whether your computer will be attacked with cryptojacking or with ransomware
Pentest specialists discovered a malware piece that infects systems with ransomware cryptocurrency mining programs, depending on equipment specifications and configuration, to decide which...
-

 229News
229NewsHeighten End-User’s Responsibility with Fighting Phishing
Antimalware companies have made many innovations for many decades in order to keep individuals and enterprises secure from cyber risks. However, human...
-

 157News
157NewsEndpoint Security-Related Issues that Providers Encounter
Endpoint security is of critical importance to all kinds of organizations, big and small. As organizations all around the world get attacked...
-

 186News
186NewsFortinet Reflects On The Dangerous New Threatscape
Industry research supports the belief that cybercriminals are currently developing many new ways to boost their attack capabilities, on the network and...






