All posts tagged "ransomware"
-
 158Malware
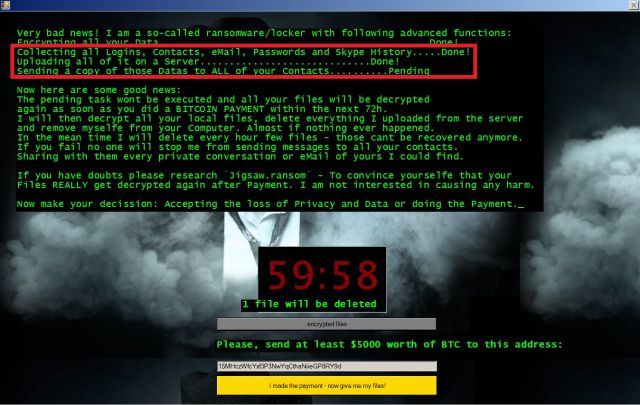
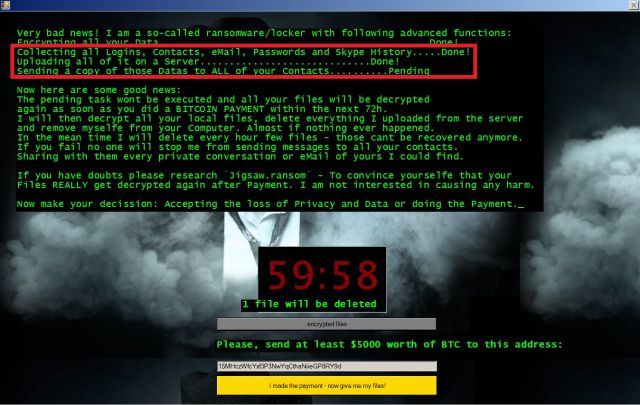
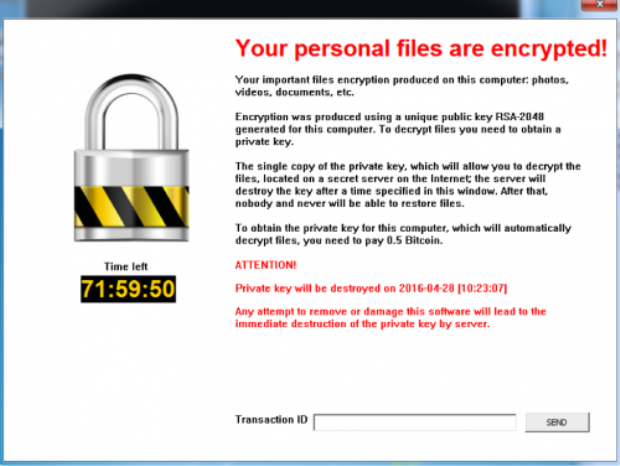
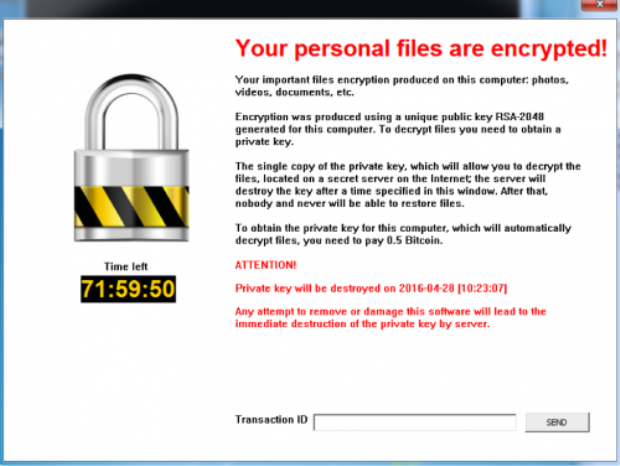
158MalwareMeet Jigsaw, the ransomware that taunts victims and offers live support
As data-encrypting malware proliferates, new entrants search for ways to stand out. The crypto ransomware racket is a booming business thatgenerates lots...
-
 90Data Security
90Data SecurityWhy Ransomware Works: Tactics and Routines Beyond Encryption
How do companies regardless of size and industry prepare for ransomware attacks? A recent study revealed that businesses are considering saving up Bitcoins,...
-

 154Malware
154MalwareRansomware dominates the threat landscape
Ransomware! Ransom Software! Encrypting Ransomware! AHHH! No doubt the last year exposed you to this term numerous times and I doubt any of...
-
 162Malware
162MalwareCryptXXX Ransomware Learns the Samba, Other New Tricks With Version 3.100
Proofpoint researchers have been tracking the rapid development of CryptXXX since they first discovered the ransomware in April [1]. In mid-May, the...
-

 85Vulnerabilities
85VulnerabilitiesHACKERS FIND BUGS, EXTORT RANSOM AND CALL IT A PUBLIC SERVICE
Crooks breaking into enterprise networks are holding data they steal for ransom under the guise they are doing the company a favor...
-

 91Malware
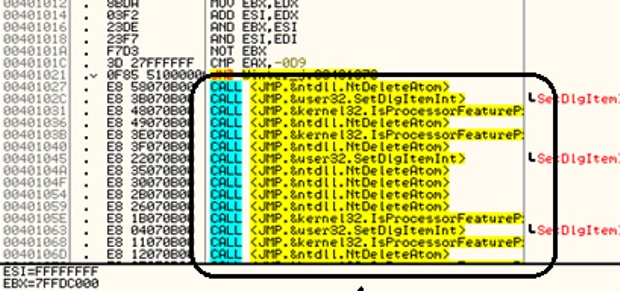
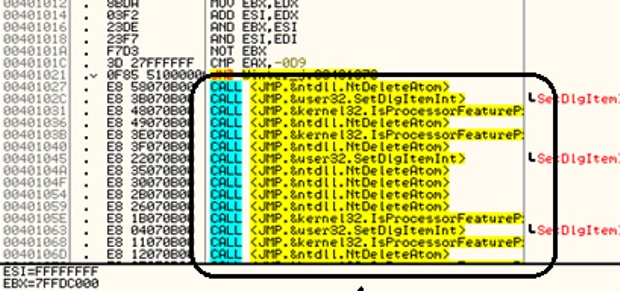
91MalwareDMA Locker 4.0 – Known Ransomware Preparing For A Massive Distribution
From the beginning of this year, we are observing rapid development of DMA Locker. First, the threat was too primitive to even...
-

 126Data Security
126Data SecurityScientists Find New Way to Generate Random Numbers, Encryption Could Get a Boost
University of Texas researchers find a way to merge two low-quality sources of random numbers into high-quality output. Two researchers from the...
-

 108Data Security
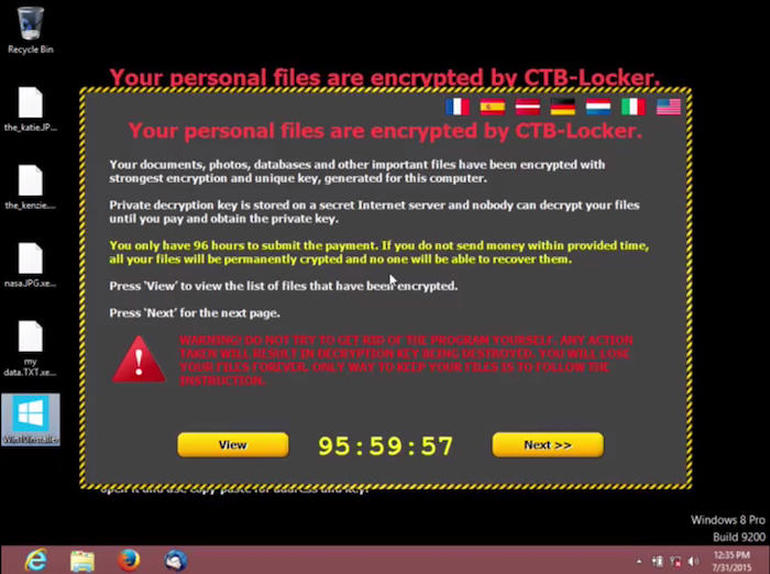
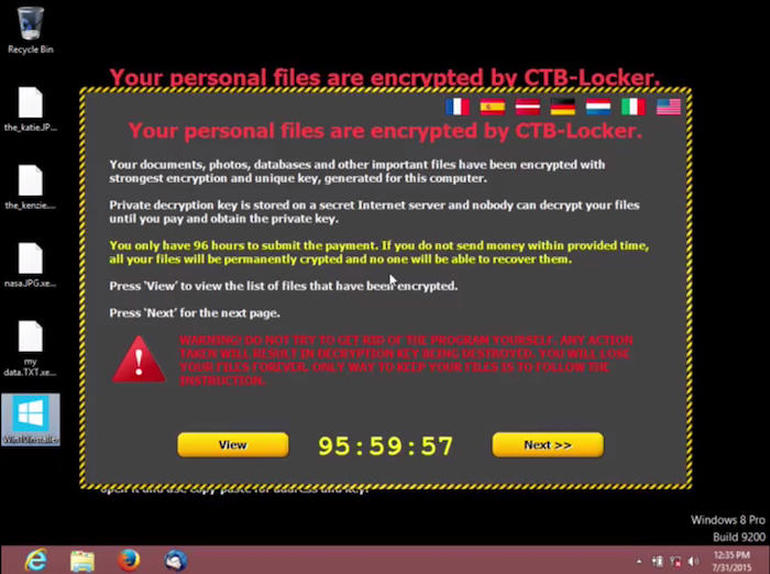
108Data Security4 Ways to Protect Against the Very Real Threat of Ransomware
RANSOMWARE IS A multi-million-dollar crime operation that strikes everyone from hospitals to police departments to online casinos. It’s such a profitable scheme...
-
 107Malware
107MalwareBucbi Ransomware Is Back With a Ukrainian Makeover
The Bucbi ransomware family, which dates back to early 2014, has received a significant update. In a recently observed attack, we also...
-

 111Data Security
111Data SecurityAlphaLocker Is the Most Professional Ransomware Kit to Date
.. but security researchers already cracked it According to security experts from Cylance, in the underground world of ransomware peddlers, there’s no ransomware...
-
 127Malware
127MalwareRansomware is now the biggest cybersecurity threat
Simple attacks plus user willingness to pay ransoms to get their files back means ransomware is on the rise, warn Kaspersky researchers....
-

 113Malware
113Malware“I’m with Stupid” Locky network gets hacked and dissed
A few months ago, we reported on a white hack against Dridex where the malicious payload was removed and an Avira antivirus...
-
 89Malware
89MalwareNew CryptMix Ransomware Promises to Give Money to a Children’s Charity
CryptMix is a mashup of CryptXXX and CryptoWall. A new type of ransomware created and distributed by a group of crooks calling themselves...
-

 110Incidents
110IncidentsBWL Electric and Water Utility shut down by ransomware
The Lansing Board of Water & Light (BWL) utility has had to shut down systems, phone lines in response to a ransomware-based...
-

 183Data Security
183Data SecurityRansomware Explosion Continues: CryptFlle2, BrLock and MM Locker Discovered
Ransomware makes headlines when hospitals are taken offline or police departments pay cybercriminals to decrypt their files. Established threat actors have also...
-

 143Malware
143MalwareToy Maker Maisto Unwittingly Serves Up CryptXXX Ransomware
The website of popular American brand Maisto, known for miniature and radio-controlled toy vehicles, was caught pushing the Angler exploit kit eventually leading to ransomware...
-
 157Data Security
157Data SecurityRegsvr32 can be used to install Ransomware through Jscript Installers
A security researcher named Casey Smith published an article last week where he detailed how the Windows Regsvr32.exe command could be used to bypass AppLocker...
-
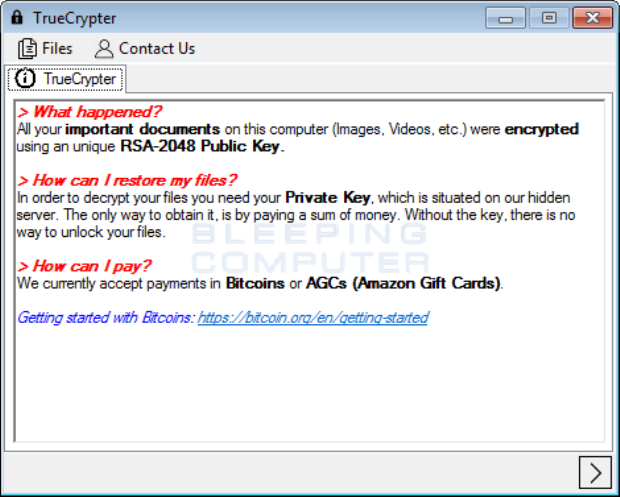
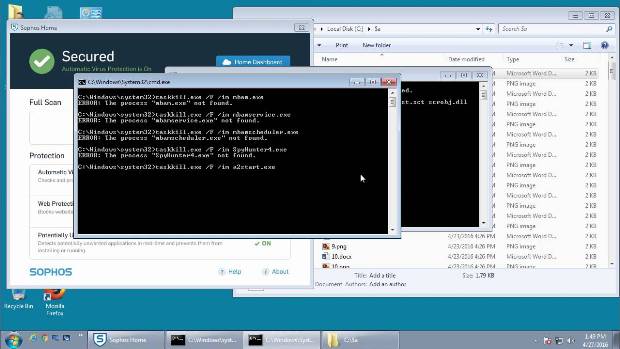
 197Data Security
197Data SecurityTrueCrypter Ransomware accepts payment in Bitcoins or Amazon Gift Card
Yesterday, a new ransomware called TrueCrypter was discovered by AVG malware analyst Jakub Kroustek. This ransomware encrypts your data using AES-256 encryption and then...
-

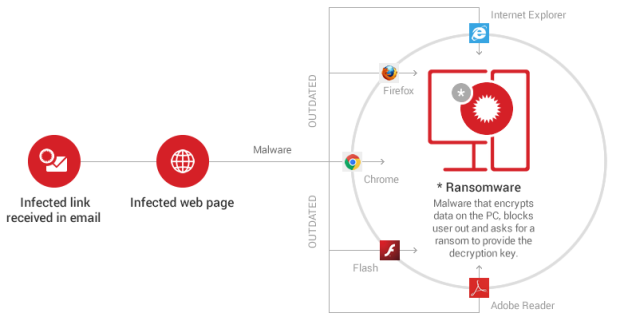
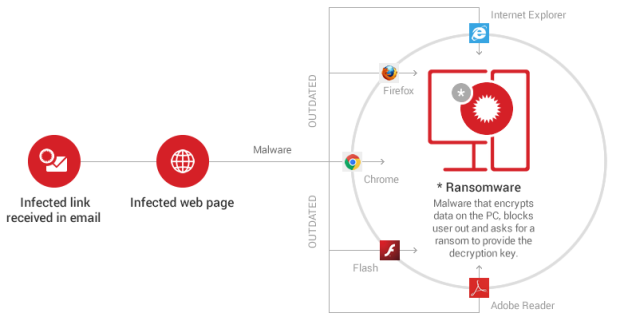
 177Vulnerabilities
177VulnerabilitiesActive drive-by exploits critical Android bugs, care of Hacking Team
Hostile JavaScript delivered through ads installs ransomware on older Android phones. An ongoing drive-by attack is forcing ransomware onto Android smartphones by exploiting...
-
 160Malware
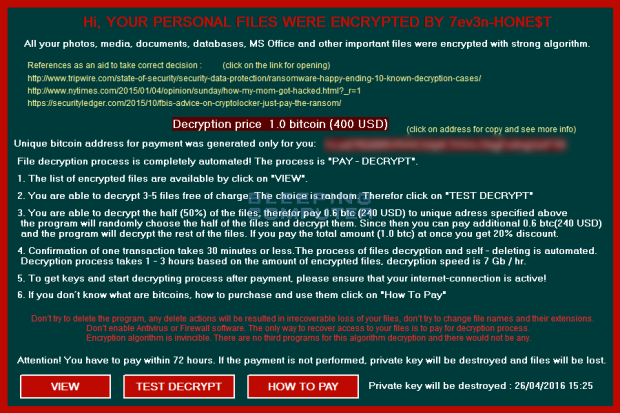
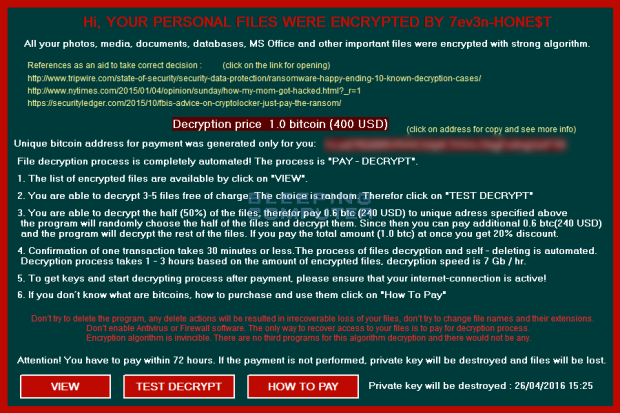
160MalwareThe 7ev3n-HONE$T ransomware encrypts and renames your files to R5A
A security researcher named Mosh has discovered a new variant of the 7ev3n Ransomware, which has rebranded itself as 7ev3n-HONE$T. This ransomware will encrypt your...
-

 123Vulnerabilities
123VulnerabilitiesHacker Promises To Kill Apple Mac Ransomware Before It Becomes A Nightmare — UPDATED
Ransomware has become the scourge of the web in recent months. Hospitals thrust back into the non-digital age, their files locked up...






